- Jan 24, 2011
- 9,378
A patching utility against crypto-malware Operation Global III (OG3) has been created, to prevent users from paying the ransom and free their files in a simple and efficient manner.
The tool, developed by malware researcher Nathan Scott, takes advantage of the fact that the authors of the threat did not do too good of a job and actually left the decryption keys within easy reach.
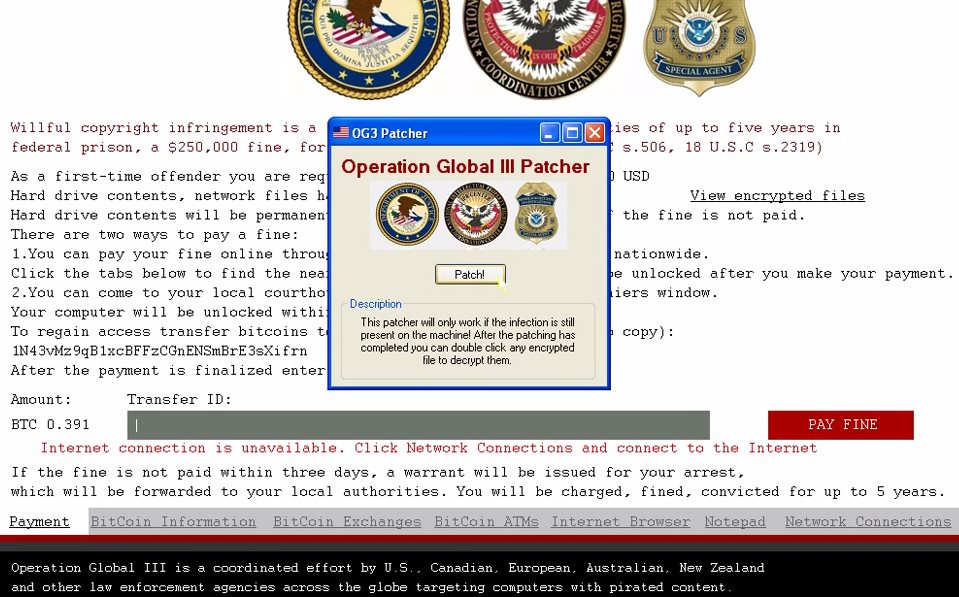
In a video published on YouTube (available below), Scott says that after the file encryption finishes, a lock screen showing the ransomware message is enabled.
OG3 is not the work of professionals
The text is a combination of police scareware and crypto-malware because the communication claims to be from law enforcement as a result of copyright infringement. The victim is informed that the penalties for the alleged offense are five years in a federal prison and a $250,000 / €202,000 fine.
However, since no previous misconduct has been recorded, a $250 / €202 fine, payable in bitcoin digital currency, would settle the matter. The victim is also informed that all the files available on the storage unit have been encrypted.
An analysis of the affected data showed the researcher that the decryption keys were present inside each encrypted file. From this to creating an automated tool that reversed the process was just a step.
The cybercriminals did their best to make sure that the affected user had no other choice but to pay the “fine” and locked the display to the ransom message; but they failed to do a proper job as the simple use of the Alt+Tab key combination allows switching to opened apps, giving the opportunity to download the patch and launch it.
Read more: http://news.softpedia.com/news/Decr...pto-Malware-Operation-Global-III-467052.shtml