When it comes to managing databases, Microsoft SQL Server is one of the most popular and widely used options. It provides a robust and reliable platform for storing and retrieving data, making it an essential tool for many businesses and organizations. However, as with any software, there are various components and features that come with SQL Server, and one of them is the VSS Writer.

What is the Microsoft SQL Server VSS Writer?
The Microsoft SQL Server VSS Writer is a component of SQL Server that is responsible for creating and managing shadow copies of SQL Server databases. Shadow copies, also known as Volume Shadow Copies or VSS snapshots, are point-in-time copies of data that can be used for backup and restore operations.
The VSS Writer works in conjunction with the Volume Shadow Copy Service (VSS) provided by the Windows operating system. It ensures that the database remains in a consistent state during the backup process by temporarily suspending write operations and creating a snapshot of the database. This snapshot can then be used to create a backup without affecting the ongoing operations of the database.
Should I Remove the Microsoft SQL Server VSS Writer?
The decision to remove the Microsoft SQL Server VSS Writer depends on your specific requirements and the backup strategy you have in place. Here are a few factors to consider:
1. Backup and Restore Strategy
If you rely on SQL Server’s built-in backup and restore functionality or use third-party backup software that utilizes VSS snapshots, removing the VSS Writer may disrupt your backup strategy. The VSS Writer plays a crucial role in creating consistent backups, and removing it may result in incomplete or inconsistent backups.
2. Database Consistency
The VSS Writer ensures that the database remains in a consistent state during the backup process. Removing the VSS Writer may lead to potential data corruption or loss if backups are taken while the database is actively being written to. It is essential to consider the impact on data integrity before deciding to remove the VSS Writer.
3. Performance Considerations
While the VSS Writer does introduce some overhead during the backup process, it is generally well-optimized and designed to minimize the impact on the database’s performance. Removing the VSS Writer may result in the need for alternative backup methods that could potentially have a more significant impact on the database’s performance.
4. Compliance and Regulatory Requirements
Many industries have specific compliance and regulatory requirements for data backup and retention. Removing the VSS Writer may result in non-compliance with these requirements, as it is a widely accepted method for creating consistent backups.
How to Remove the Microsoft SQL Server VSS Writer?
If, after careful consideration, you have determined that removing the Microsoft SQL Server VSS Writer is necessary for your specific use case, here are the steps to do so:
- Open the “Services” application by searching for “services.msc” in the Windows Start menu.
- Scroll down and locate the “SQL Server VSS Writer” service.
- Right-click on the service and select “Properties.”
- In the “Properties” window, change the “Startup type” to “Disabled.”
- Click “Apply” and then “OK” to save the changes.
After disabling the SQL Server VSS Writer service, it will no longer be active, and VSS snapshots will not be created during the backup process. However, it is crucial to have an alternative backup strategy in place to ensure data integrity and compliance.
Conclusion
The Microsoft SQL Server VSS Writer is an essential component for creating consistent backups of SQL Server databases. While there may be specific scenarios where removing the VSS Writer is necessary, it is generally recommended to keep it enabled to ensure data integrity, compliance with regulatory requirements, and a reliable backup and restore strategy.
Before making any changes to the VSS Writer, carefully evaluate your backup requirements, consider the potential impact on data consistency and performance, and ensure compliance with industry regulations. If you are unsure about the best course of action, consult with a database administrator or IT professional to determine the most suitable backup strategy for your specific needs.
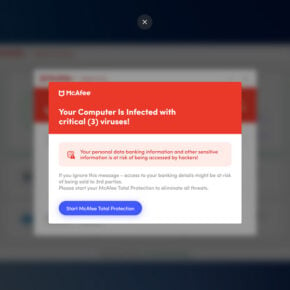
Remember, if you suspect any malware or security threats on your system, it is always recommended to scan your computer using reliable antivirus software. Consider using Malwarebytes Free to ensure the safety and security of your data.