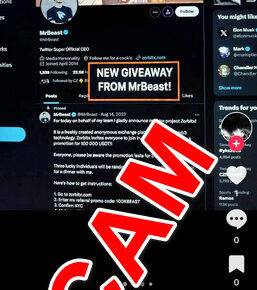
Scams have become increasingly prevalent in the digital age, with scammers constantly devising new methods to deceive unsuspecting individuals. One such scam that has gained traction on social media platforms, particularly Facebook, is the ‘Type WINNER Letter By Letter’ HP Laptop Giveaway scam. This article aims to shed light on this scam, how it works, what to do if you have fallen victim, and provide valuable insights to protect yourself from falling prey to similar scams.

What is the ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook Scam?
The ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook scam is a fraudulent scheme that lures users into believing they have won a brand new HP laptop. The scam typically starts with a post or message on Facebook claiming that the user can win the laptop by typing the word “WINNER” letter by letter in the comments section. The scammers often use enticing images and persuasive language to make the offer seem legitimate.
Once users start commenting with the letters, scammers take advantage of the engagement to increase the visibility of their post. This tactic aims to attract more victims and create a sense of urgency, as users see others participating and believe they have a genuine chance of winning.
How Does the Scam Work?
The ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook scam operates by exploiting users’ desire for freebies and their trust in social media platforms. Here is a step-by-step breakdown of how the scam typically unfolds:
- Scammers create a post or message on Facebook, often using a fake account or impersonating a well-known brand or influencer.
- The post claims that users can win an HP laptop by typing the word “WINNER” letter by letter in the comments section.
- Users start commenting with the letters, increasing the engagement and visibility of the post.
- Scammers may ask users to perform additional actions, such as sharing the post or liking their page, to further spread the scam.
- Once the post gains enough traction, scammers may redirect users to external websites or ask for personal information, such as email addresses or phone numbers.
- In some cases, scammers may request payment for shipping fees or other associated costs, claiming it is necessary to receive the prize.
- Victims who provide personal information or make payments may become targets for identity theft or financial fraud.
What to Do If You Have Fallen Victim?
If you have fallen victim to the ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook scam, it is crucial to take immediate action to protect yourself and minimize the potential damage. Here are the steps you should follow:
- Report the scam: Report the fraudulent post or message to Facebook by clicking on the three dots in the top-right corner of the post and selecting “Report post” or “Report message.”
- Remove your comments: Delete your comments from the scam post to prevent further engagement and minimize the visibility of the scam.
- Scan your device: Run a scan with a reputable antivirus software, such as Malwarebytes Free, to check for any malware or viruses that may have been downloaded unknowingly.
- Monitor your accounts: Keep a close eye on your bank accounts, credit cards, and other online accounts for any suspicious activity. If you notice any unauthorized transactions, contact your financial institution immediately.
- Change your passwords: Change the passwords for your social media accounts, email, and any other accounts that may have been compromised.
- Be cautious of future scams: Learn from the experience and be vigilant when encountering similar offers or giveaways on social media platforms. Remember that legitimate giveaways rarely require users to perform specific actions or provide personal information.
Technical Details and Statistics
While specific technical details about the ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook scam may vary, scammers often employ social engineering techniques to manipulate users into participating. By leveraging users’ desire for freebies and the fear of missing out, scammers create a sense of urgency and exploit their trust in social media platforms.
According to a report by the Better Business Bureau, Facebook scams have been on the rise, with an estimated 1.3 million reported incidents in 2022 alone. The report also highlights that scammers are becoming increasingly sophisticated, making it more challenging for users to identify and avoid falling victim to such scams.
Summary
The ‘Type WINNER Letter By Letter’ HP Laptop Giveaway Facebook scam preys on users’ desire for freebies and their trust in social media platforms. By creating an illusion of a legitimate giveaway, scammers manipulate users into engaging with their posts and potentially falling victim to identity theft or financial fraud.
To protect yourself from falling prey to similar scams, it is essential to remain cautious and skeptical of offers that seem too good to be true. Remember to report scams, remove your engagement, scan your device for malware, monitor your accounts, change your passwords, and stay vigilant for future scams.
By staying informed and taking proactive measures, you can safeguard yourself and help create a safer online environment for everyone.