Entrusted Toolbar is a browser hijacker, which is promoted via other free downloads, and once installed it will add the Entrusted Community Toolbar, change your browser homepage to search.conduit.com, and set your default search engine to Entrusted Customized Web Search.
![Entrusted Toolbar [Image: Entrusted Toolbar virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar.jpg)
The Entrusted Customized Web Search will display advertisements and sponsored links in your search results, and may collect search terms from your search queries. The Entrusted Toolbar infection is used to boost advertising revenue, as in the use of blackhat SEO, to inflate a site’s page ranking in search results.
The Entrusted Toolbar it’s technically not a virus, but it does exhibit plenty of malicious traits, such as rootkit capabilities to hook deep into the operating system, browser hijacking, and in general just interfering with the user experience. The industry generally refers to it as a “PUP,” or potentially unwanted program.
Entrusted Toolbar got on your computer after you have installed a freeware software (video recording/streaming, download-managers or PDF creators) that had bundled into their installation this browser hijacker. This browser hijacker is also bundled within the custom installer on many download sites (examples: CNET, Brothersoft or Softonic), so if you have downloaded a software from these websites, chances are that Entrusted was installed during the software setup process.
For example, when you install Entrusted Player, you will also agree to change your browser homepage to search.conduit.com, set your default search engine to Entrusted Customized Web Search, and install the Entrusted Toolbar.
However when you uninstall Entrusted Player from your computer, your web browser’s default settings will not be restored. This means that you’ll have to remove Entrusted Toolbar and search.conduit.com from your favorite web browser manually.
You should always pay attention when installing software because often, a software installer includes optional installs, such as this Entrusted Toolbar. Be very careful what you agree to install.
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
Entrusted Toolbar – Virus Removal Guide
This page is a comprehensive guide, which will remove Entrusted Toolbar from your Internet Explorer, Firefox and Google Chrome.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Uninstall Entrusted Toolbar programs from your computer
STEP 2: Remove Entrusted Toolbar from your web browser
STEP 3: Remove Entrusted Toolbar hijacker with AdwCleaner and Junkware Removal Tool
STEP 4: Remove Entrusted Toolbar malicious files with Malwarebytes and HitmanPro
STEP 1 : Uninstall Entrusted Toolbar program from your computer
- To uninstall Entrusted Toolbar from your computer, click the Start button, then select Control Panel, and click on Uninstall a program.
If you are using Windows 8, simply drag your mouse pointer to the right edge of the screen, select Search from the list and search for “control panel“. Or you can right-click on a bottom left hot corner (formerly known as the Start button) and select Control Panel from there, then select Uninstall a program.
![Click on Uninstall a program [Image: Uninstall a program]](//malwaretips.com/blogs/wp-content/uploads/2013/03/uninstall-a-program-windows.jpg)
- When the Add/Remove Programs or the Uninstall a Program screen is displayed, scroll through the list of currently installed programs and uninstall Search Protect by conduit, Entrusted Toolbar and any other recently installed or unknown programs from your computer.
![Uninstall Entrusted Toolbar from Windows [Image: Uninstall Entrusted Toolbar from Windows]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-unistall.jpg)
Depending on what program has installed the Entrusted Toolbar, the above program may have a different name or not be installed on your computer. If you cannot find any unwanted or unknown programs on your machine, then you can proceed with the next step.
STEP 2 : Remove Entrusted Toolbar from your web browser
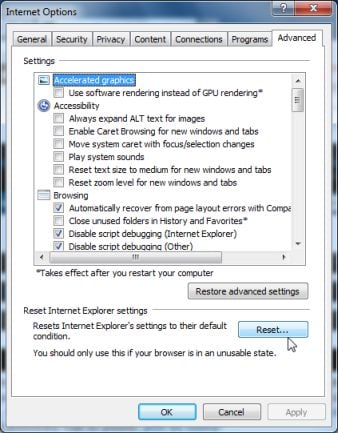
Remove Entrusted Toolbar from Internet Explorer 8, 9 and 10
- Open Internet Explorer, click on the gear icon
![How to remove Entrusted Toolbar (Uninstall Guide) 2 [Image: icongear.jpg]](//malwaretips.com/images/removalguide/icongear.jpg) (Tools for Windows XP users) at the top (far right), then click again on Internet Options.
(Tools for Windows XP users) at the top (far right), then click again on Internet Options.

- In the Internet Options dialog box, click on the Advanced tab, then click on the Reset button.
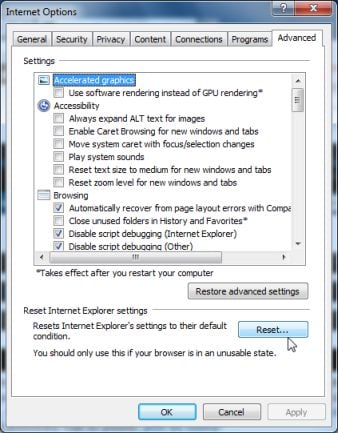
- In the Reset Internet Explorer settings section, check the Delete personal settings box, then click on Reset.
- When Internet Explorer finishes resetting, click Close in the confirmation dialogue box and then click OK.
- Close and open Internet Explorer.
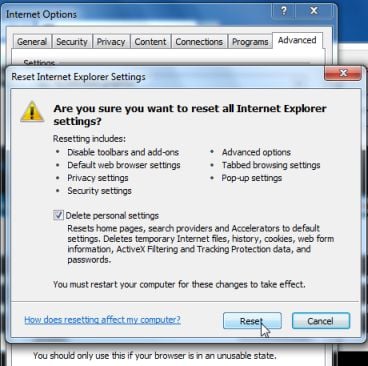
Remove Entrusted Toolbar from Mozilla Firefox
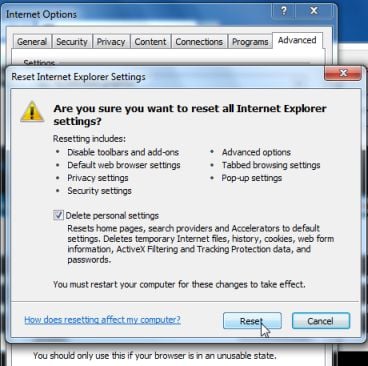
- Remove Entrusted Toolbar extensions from Firefox.
At the top of the Firefox window, click the orange Firefox button, then select Add-ons.
Select the Extensions tab, then remove Entrusted 10.16.4.19 and any other unknown extensions from Mozilla Firefox.
![Entrusted Toolbar Firefox extension [Image: Entrusted Toolbar Firefox extension]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-Firefox-extension.jpg)
- Reset your default search engine and home page from Entrusted Customized Web Search to their default.
To reset your search engine and homepage to their default, we will use the SearchReset extension.This add-on is very simple: on installation, it backs up and then resets your search preferences and home page to their default values, and then uninstalls itself. This affects the search bar, URL bar searches, and the home page.
You can download SearchReset from the below link, and then we will just need to install it to revert Firefox to its default settings.
SEARCHRESET DOWNLOAD LINK (This link will open another web page from where you can download the SearchReset Firefox extension)
![Install SearchReset extension to restore Firefox to its default settings [Image: SearchReset extension]](//malwaretips.com/blogs/wp-content/uploads/2013/03/searchreset-firefox-extension.jpg)
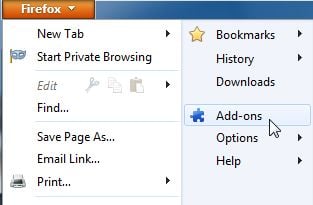
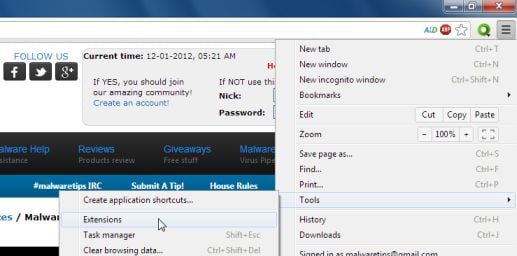
Remove Entrusted Toolbar from Google Chrome
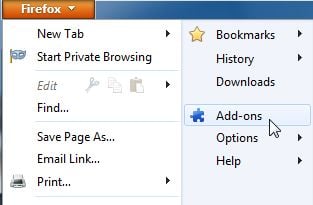
- Remove Entrusted Toolbar extensions from Google Chrome.
Click the Chrome menu button on the browser toolbar, select Tools and then click on Extensions.
button on the browser toolbar, select Tools and then click on Extensions.
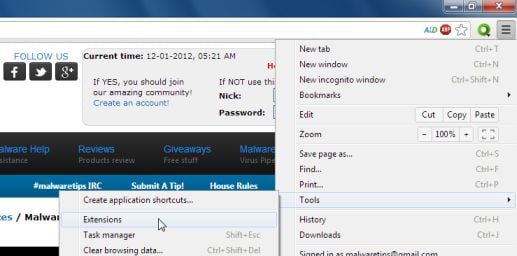
In the Extensions tab, remove Entrusted 10.16.70.1 and any other unknown extensions by clicking the trash can![Remove an extension from Chrome [Image: Remove an extension from Chrome]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Trash-Can-Chrome.png) icon.
icon.
Basically, if you have not installed an extension, you should remove it from your web browser.
![Entrusted Toolbar Chrome extension [Image: Entrusted Toolbar Chrome extension]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-Chrome-extension.jpg)
- Set Google Chrome default search engine from Entrusted Customized Web Search to Google.
Click the Chrome menu button, then select Settings and click on Manage search engines in the Search section.
button, then select Settings and click on Manage search engines in the Search section.
In the Search Engines dialog that appears, select Google and click the Make Default button that appears in the row.
![Entrusted Customized Web Search Chrome hijack [Image: Entrusted Customized Web Search Chrome hijack]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-Customized-Web-Search-Chrome.jpg)
Search for Conduit in the Search Engines list, and click the X button that appears at the end of the row.
![Entrusted Customized Web Search Chrome removal [Image: Entrusted Customized Web Search Chrome removal]](//malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-Customized-Web-Search-Chrome-removal.jpg)
- Change Google Chrome homepage from search.conduit.com to its default.
Conduit has modified your Google settings to open their webpage whenever you start your browser, so we will need to revert this change.
Click the Chrome menu button, then select Settings and click on One the New Tab page in the On Startup section.
button, then select Settings and click on One the New Tab page in the On Startup section.
![Change Google Chrome homepage to its default [Image: Change Google Chrome homepage to its default]](//malwaretips.com/blogs/wp-content/uploads/2013/06/Chrome-default-page.jpg)
STEP 3: Remove Entrusted Toolbar hijacker from your computer
To remove all the Entrusted Toolbar registry keys, files and folders from your computer, we will need to run a scan with the AdwCleaner and Junkware Removal Tool utilities.
Remove Entrusted Toolbar with AdwCleaner
The AdwCleaner utility will scan your computer for Entrusted Toolbar malicious files and registry keys, that may have been installed on your computer without your knowledge.
- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
![AdwCleaner Icon [Image: AdwCleaner Icon]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-icon.jpg)
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Search button as shown below.
![Click on Search to scan for Entrusted Toolbar [Image: AdwCleaner scanning for Entrusted Toolbar]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-scan.jpg)
The program will now start to search for Entrusted Toolbar malicious files that may be installed on your computer. When it has finished it will display a notepad screen that contains a log file of all the Entrusted extensions, files, and registry keys that have been detected. - To remove the Entrusted Toolbar malicious files that were detected in the previous step, please click on the Delete button on the AdwCleaner screen.
![Click on Delete to remove Entrusted Toolbar virus [Image: Adwcleaner removing Entrusted Toolbar]](//malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-virus-removal.jpg)
AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK button.
Remove Entrusted Toolbar hijack with Junkware Removal Tool
Junkware Removal Tool is a powerful utility, which will remove Entrusted Toolbar virus from Internet Explorer, Firefox or Google Chrome.
- You can download the Junkware Removal Tool utility from the below link:
JUNKWARE REMOVAL TOOL DOWNLOAD LINK (This link will automatically download the Junkware Removal Tool utility on your computer) - Once Junkware Removal Tool has finished downloading, please double-click on the JRT.exe icon as seen below.
![Double-click on the Junkware Removal Tool utility [Image: Junkware Removal Tool]](//malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-icon.jpg)
If Windows prompts you as to whether or not you wish to run Junkware Removal Tool, please allow it to run. - Junkware Removal Tool will now start, and at the Command Prompt, you’ll need to press any key to perform a scan for the Entrusted Toolbar.
![Junkware Removal Tool scanning for Entrusted Toolbar [Image: Junkware Removal Tool scanning for Entrusted Toolbar virus]](//malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
Please be patient as this can take a while to complete (up to 10 minutes) depending on your system’s specifications. - When the scan Junkware Removal Tool will be completed, this utility will display a log with the malicious files and registry keys that were removed from your computer.
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](//malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)
STEP 4: Remove Entrusted Toolbar virus from your computer
Remove Entrusted Toolbar virus with Malwarebytes Anti-Malware Free
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the Entrusted Toolbar malicious files.
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
- Malwarebytes’ Anti-Malware will now start scanning your computer for Entrusted Toolbar as shown below.
![Malwarebytes Anti-Malware scanning for Entrusted Toolbar [Image: Malwarebytes Anti-Malware scanning for Entrusted Toolbar virus]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
![Malwarebytes Anti-Malwar removing Entrusted Toolbar [Image: Malwarebytes Anti-Malware removing Entrusted Toolbar]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
Double-check for the Entrusted Toolbar infection with HitmanPro
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.

Click on the Next button, to install HitmanPro on your computer.

- HitmanPro will now begin to scan your computer for Entrusted Toolbar malicious files.

- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove Entrusted Toolbar adware.

- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](//malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
Your computer should now be free of the Entrusted Toolbar infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove Entrusted Toolbar from your machine, please start a new thread in our Malware Removal Assistance forum.

![How to remove Entrusted Toolbar (Uninstall Guide) 1 [Image: Entrusted Toolbar virus]](https://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar.jpg)
![Click on Uninstall a program [Image: Uninstall a program]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/uninstall-a-program-windows.jpg)
![Uninstall Entrusted Toolbar from Windows [Image: Uninstall Entrusted Toolbar from Windows]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-unistall.jpg)

![Entrusted Toolbar Firefox extension [Image: Entrusted Toolbar Firefox extension]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-Firefox-extension.jpg)
![Install SearchReset extension to restore Firefox to its default settings [Image: SearchReset extension]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/searchreset-firefox-extension.jpg)
![Entrusted Toolbar Chrome extension [Image: Entrusted Toolbar Chrome extension]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-toolbar-Chrome-extension.jpg)
![Entrusted Customized Web Search Chrome hijack [Image: Entrusted Customized Web Search Chrome hijack]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-Customized-Web-Search-Chrome.jpg)
![Entrusted Customized Web Search Chrome removal [Image: Entrusted Customized Web Search Chrome removal]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Entrusted-Customized-Web-Search-Chrome-removal.jpg)
![Change Google Chrome homepage to its default [Image: Change Google Chrome homepage to its default]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Chrome-default-page.jpg)
![Click on Search to scan for Entrusted Toolbar [Image: AdwCleaner scanning for Entrusted Toolbar]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-scan.jpg)
![Click on Delete to remove Entrusted Toolbar virus [Image: Adwcleaner removing Entrusted Toolbar]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/adwcleaner-virus-removal.jpg)
![Junkware Removal Tool scanning for Entrusted Toolbar [Image: Junkware Removal Tool scanning for Entrusted Toolbar virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes Anti-Malware scanning for Entrusted Toolbar [Image: Malwarebytes Anti-Malware scanning for Entrusted Toolbar virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Malwarebytes Anti-Malwar removing Entrusted Toolbar [Image: Malwarebytes Anti-Malware removing Entrusted Toolbar]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)

