Malware Defender 2015 is a computer virus, which masquerades as genuine security software, while actually reporting non-existent malware threats in order to scare the user into purchasing “Malware Defender 2015”.

- What is Malware Defender 2015?
- How did Malware Defender 2015 virus got on my computer?
- Am I infected with Malware Defender 2015 virus?
- How to remove Malware Defender 2015 virus (Removal Guide)
- STEP 1 : Start your computer in Safe Mode with Networking
- STEP 2: Run RKill to terminate Malware Defender 2015 malicious processes
- STEP 3: Remove Malware Defender 2015 virus with Malwarebytes Anti-Malware FREE
- STEP 4: Remove Malware Defender 2015 infection with HitmanPro

What is Malware Defender 2015?
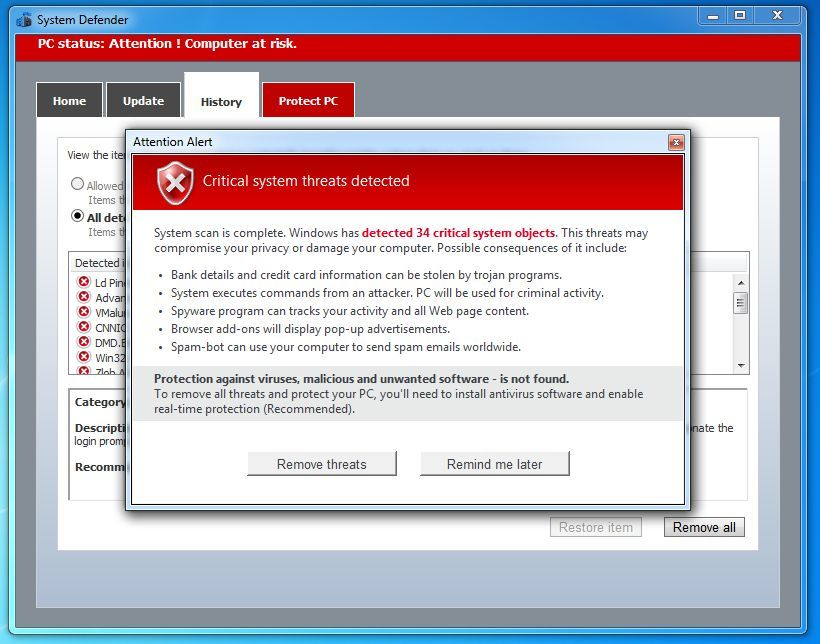
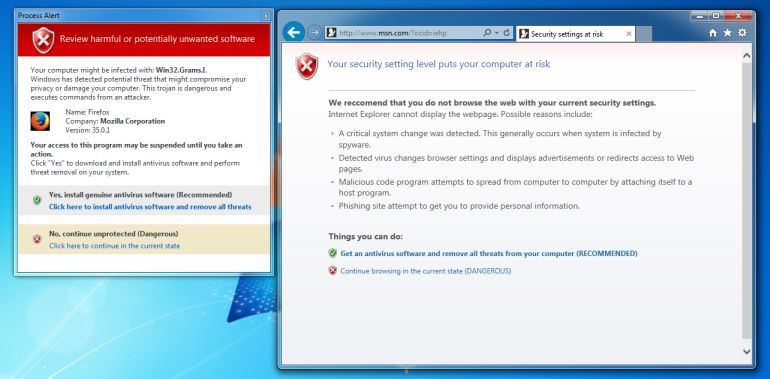
Malware Defender 2015 is classified as a rogue because it pretends to be an anti-virus program, but will instead displays bogus scan results, report non-existing computer infections, and does not allow you to run your normal applications.
In this case, not only is Malware Defender 2015 going to disrupt your system, it’s going to try and trick you into making a purchase using your credit card.
Malware Defender 2015 appears in the form of a fake Windows warning on your computer system that reads you have a specific number of viruses on your computer (usually in the hundreds) and that this software has detected those viruses. To get rid of them you must purchase the full-version of Malware Defender 2015. It’s important to remember that by purchasing the “claimed full version to remove the viruses” you will be submitting your personal information to unscrupulous persons and may also end up being a victim of credit card or identity fraud or theft.
To protect itself from being removed, Malware Defender 2015 will also terminate any application you try to run on your computer. It does this to protect itself from being removed by legitimate security programs and to scare you into thinking your programs are infected. When this infection terminates a program it will display a message similar to the following:
PC status: Potentially unprotected
Potential threat was detected!
View the items that were detected as potentially harmful and the actions that you took on them:
Downloader.JS.Snall.fi
Category: High
Description: This Trojan downloads other files via the Internet and launches them for execution on the victim machine. This program is an HTML page which contains Java Script scenarios. It is 1432 bytes in size.
How did Malware Defender 2015 virus got on my computer?
Malware Defender 2015 is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this rogue antivirus without your permission.
Another method used to propagate Malware Defender 2015 is spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the Malware Defender 2015 virus.
The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software.
The Malware Defender 2015 infection is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
Am I infected with Malware Defender 2015 virus?
Some examples of the interface, fake alerts, fake scanning results, and pop-ups displayed by Malware Defender 2015 virus are shown below:
How to remove Malware Defender 2015 virus (Removal Guide)
This page is a comprehensive guide, which will remove the Malware Defender 2015 infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Start your computer in Safe Mode with Networking
STEP 2: Run RKill to terminate Malware Defender 2015 malicious processes
STEP 3: Remove Malware Defender 2015 virus with Malwarebytes Anti-Malware Free
STEP 4: Remove Malware Defender 2015 infection with HitmanPro
STEP 1 : Start your computer in Safe Mode with Networking
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
- When the computer starts you will see your computer’s hardware being listed. When you see this information start to gently tap the F8 key repeatedly until you are presented with the Windows XP, Vista or 7 Advanced Boot Options.
![Windows F8 key [Image: F8 key]](//malwaretips.com/blogs/wp-content/uploads/2013/06/F8-key.jpg.png)
If you are using Windows 8, press the Windows key + C, and then click Settings. Click Power, hold down Shift on your keyboard and click Restart, then click on Troubleshoot and select Advanced options. In the Advanced Options screen, select Startup Settings, then click on Restart. - If you are using Windows XP, Vista or 7 in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
![Safe Mode with Networking screen [Image: Safemode.jpg]](//malwaretips.com/images/removalguide/safemode.jpg)
If you are using Windows 8, press 5 on your keyboard to Enable Safe Mode with Networking.If you are having issues starting Windows 8 in Safe Mode with Networking, you can follow this “How to start Windows 8 in Safe Mode with Networking” guide.Windows will start in Safe Mode with Networking.
STEP 2: Run RKill to terminate Malware Defender 2015 malicious processes
RKill is a program that will attempt to terminate all malicious processes associated with Malware Defender 2015 infection, so that we will be able to perform the next step without being interrupted by this malicious software.
Because this utility will only stop Malware Defender 2015 running process, and does not delete any files, after running it you should not reboot your computer as any malware processes that are configured to start automatically will just be started again.
- While your computer is in Safe Mode with Networking ,please download the latest official version of RKill.Please note that we will use a renamed version of RKILL so that Proven Antivirus Protection won’t block this utility from running.
RKILL DOWNLOAD LINK (This link will automatically download RKILL renamed as iExplore.exe) - Double click on iExplore.exe to start RKill and stop any processes associated with Malware Defender 2015.
![Rkill renamed to iExplore.exe [Image: RKILL Program]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-run-as-admin.jpg)
- RKill will now start working in the background, please be patient while the program looks for Malware Defender 2015 malicious process and tries to end them.
![RKill while killing Malware Defender 2015 malicious process [Image: RKILL stoping malware]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-program.jpg)
- When the Rkill utility has completed its task, it will generate a log. Do not reboot your computer after running RKill as the malware programs will start again.
![RKill Log [Image: RKill Report]](//malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-report.jpg)
STEP 3: Remove Malware Defender 2015 virus with Malwarebytes Anti-Malware FREE
Malwarebytes Anti-Malware Free uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.
It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Anti-Malware Free) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup-consumer-2.00.xx” to start the installation of Malwarebytes Anti-Malware.
![Malwarebytes Anti-Malware setup program [Image: Malwarebytes Anti-Malware setup program]](//malwaretips.com/blogs/wp-content/uploads/2014/02/Malwarebytes-Anti-Malware-Setup.jpg)
 You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation. - When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
![Malwarebytes Anti-Malware Setup Wizard [Image: Malwarebytes Anti-Malware Setup Wizard]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-installation.jpg)
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
![Malwarebytes Anti-Malware Final Setup Screen [Image: Malwarebytes Anti-Malware Final Setup Screen]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-final-screen.jpg)
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the “Fix Now” button.
![Remove Malware Defender 2015 virus (Removal Guide) 2 [Image: Click on the Fix Now button to start a scan]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-fix-now.jpg)
Alternatively, you can click on the “Scan” tab and select “Threat Scan“, then click on the “Scan Now” button.
![Malwarebytes Anti-Malware Threat Scan [Image: Malwarebytes Anti-Malware Threat Scan]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-threat-scan-option.jpg)
- Malwarebytes Anti-Malware will now check for updates, and if there are any, you will need to click on the “Update Now” button.
![Click on Update Now to update Malwarebytes Anti-Malware [Image: Click on Update Now to update Malwarebytes Anti-Malware]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-update-now.jpg)
- Malwarebytes Anti-Malware will now start scanning your computer for the Malware Defender 2015 virus. When Malwarebytes Anti-Malware is scanning it will look like the image below.
![Malwarebytes Anti-Malware while performing a scan [Image: Malwarebytes Anti-Malware while performing a scan]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-scan.jpg)
- When the scan has completed, you will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Quarantine All” button, and then click on the “Apply Now” button.
![Remove the malware that Malwarebytes Anti-Malware has detected [Image: Remove the malware that Malwarebytes Anti-Malware has found]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-potential-threat-detected.jpg)
Please note that the infections found may be different than what is shown in the image. - Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
![Malwarebytes Anti-Malware asking to reboot your computer [Image: Malwarebytes Anti-Malware while removing viruses]](//malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-remove-virus.jpg)
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another “Threat Scan” scan to verify that there are no remaining threats
STEP 4: Remove Malware Defender 2015 infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti-virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
![HitmanPro startup screen (Click Next) [Image: HitmanPro start-up screen]](//malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-install.jpg)
Click on the “Next” button, to install HitmanPro on your computer.
![HitmanPro installation options (Click Next) [Image: HitmanPro setup options]](//malwaretips.com/blogs/wp-content/uploads/2014/03/hitmapro-start-scan.jpg)
- HitmanPro will now begin to scan your computer for Malware Defender 2015 malicious files.
![HitmanPro scanning for Malware Defender 2015 [Image: HitmanPro scanning for malware]](//malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scanning.jpg)
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove Malware Defender 2015 virus.
![HitmanPro scan results (Click Next) [Image: HitmanPro scan results]](//malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scan-results.jpg)
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
![Click on the Activate free license button [Image: HitmanPro Activate Free License]](//malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-activation.jpg)

![Windows F8 key [Image: F8 key]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/F8-key.jpg.png)
![Safe Mode with Networking screen [Image: Safemode.jpg]](http://malwaretips.com/images/removalguide/safemode.jpg)
![Rkill renamed to iExplore.exe [Image: RKILL Program]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-run-as-admin.jpg)
![RKill while killing Malware Defender 2015 malicious process [Image: RKILL stoping malware]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-program.jpg)
![RKill Log [Image: RKill Report]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/rkill-report.jpg)
![Malwarebytes Anti-Malware setup program [Image: Malwarebytes Anti-Malware setup program]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/Malwarebytes-Anti-Malware-Setup.jpg)
![Malwarebytes Anti-Malware Setup Wizard [Image: Malwarebytes Anti-Malware Setup Wizard]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-installation.jpg)
![Malwarebytes Anti-Malware Final Setup Screen [Image: Malwarebytes Anti-Malware Final Setup Screen]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-final-screen.jpg)
![Remove Malware Defender 2015 virus (Removal Guide) 2 [Image: Click on the Fix Now button to start a scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-fix-now.jpg)
![Malwarebytes Anti-Malware Threat Scan [Image: Malwarebytes Anti-Malware Threat Scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-threat-scan-option.jpg)
![Click on Update Now to update Malwarebytes Anti-Malware [Image: Click on Update Now to update Malwarebytes Anti-Malware]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-update-now.jpg)
![Malwarebytes Anti-Malware while performing a scan [Image: Malwarebytes Anti-Malware while performing a scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-scan.jpg)
![Remove the malware that Malwarebytes Anti-Malware has detected [Image: Remove the malware that Malwarebytes Anti-Malware has found]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-potential-threat-detected.jpg)
![Malwarebytes Anti-Malware asking to reboot your computer [Image: Malwarebytes Anti-Malware while removing viruses]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-remove-virus.jpg)
![HitmanPro startup screen (Click Next) [Image: HitmanPro start-up screen]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-install.jpg)
![HitmanPro installation options (Click Next) [Image: HitmanPro setup options]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmapro-start-scan.jpg)
![HitmanPro scanning for Malware Defender 2015 [Image: HitmanPro scanning for malware]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scanning.jpg)
![HitmanPro scan results (Click Next) [Image: HitmanPro scan results]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scan-results.jpg)
![Click on the Activate free license button [Image: HitmanPro Activate Free License]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-activation.jpg)