Securebit Technologies Free Antivirus is a computer virus, which pretends to be a legitimate security program and claims that malware has been detected on your computer. If you try to remove these infections, Securebit Technologies will state that you need to buy its premium version before being able to do so.
Securebit Technologies targets users browsing Internet websites, and rely on social engineering to deliver its payload.
On infected or hacked websites users are prompted by a pop-up window that has been carefully crafted to resemble a legitimate security warning. These pop-up windows typically alert a user of a computer infection, and then prompt the user to download and install Securebit Technologies to resolve the apparent issue.
Some of the infections may have come from users downloading an infected codec file when they were trying to watch a video online, or users who receive a spam email and open an infected email attachment.
Once installed, Securebit Technologies will display fake security alerts that are designed to think that your data is at risk or that your computer is severely infected.These messages include:
Warning: Unable to clean all files.
Contact customer service for complete cleaning.
USA/Canada Toll Free: 1-800-862-2015Free Antivirus
Infected files have been detected on your PC.
36 Infected files found.
It is recommended that you run a full scan and clean your PC.
For Support Call 1-800-862-2015 (Toll Free US/Canada)This computer is potentially infected.
Antivirus has blocked some features of windows.
Please contact support for removal and clean up.WINDOWS HAS STOPPED WORKING
Symptoms:
When working in Windows, you may receive the following error
Windows has stopped working. Windows is restarting
Additionally, you may notice the screen flicker just before or after the error message appears.
Cause:
This issue can be caused due to any the following issues:
You may be using outdated or corrupted hardware drivers
System files on your PC may be corrupt or mismatched with other files
You may have a Virus or Malware infection on your PC
Some applications or services running on your PC may be causing Windows to stop working
Resolution
To resolve this issue you need to determine what is causing Windows to stop working, try the troubleshooting steps below to help determine the issue.
Scan your PC for Virus or Malware infections
Start your PC in Safe Mode to check for start-up issues
Start your PC is Clean Boot environment and troubleshoot the issue
If problem persist, contact support confer. Toll Free 1(800) 862 2015Antivirus
Infected files have been detected on your PC.
5 Infected files found.
It is recommended that you run a full scan and clean your PC.
For Support Call 1-800-862-2015 (Toll Free US/Canada)24/7 Virus Removal Helpline
USA 1-800-862-2015
UK 0-800-883-0862
If your computer is infected with Securebit Technologies virus, then you are seeing the following screens:
Securebit Technologies is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you buy this rogue security software as this could lead to identity theft,and if you have, you should contact your bank and dispute the charge stating that the program is a scam and a computer virus.
Securebit Technologies – Virus Removal Guide
STEP 1: Remove Securebit Technologies malicious files with Malwarebytes Anti-Malware
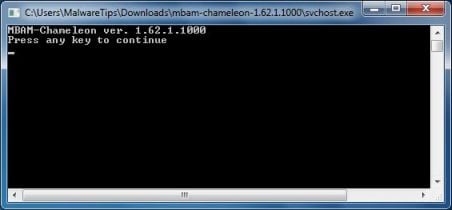
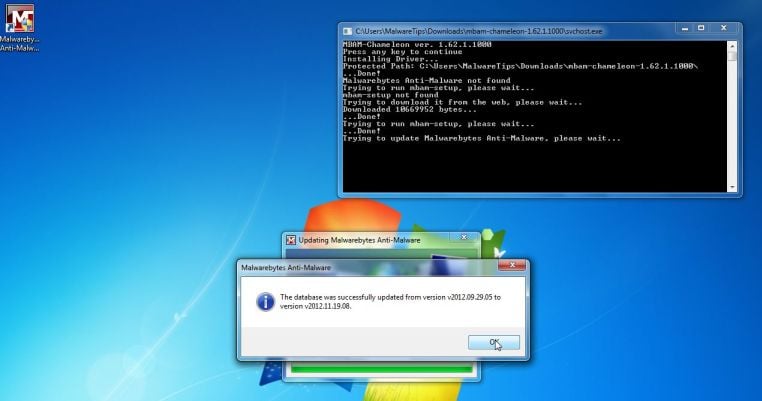
Malwarebytes Chameleon technologies will allow us to install and run a Malwarebytes Anti-Malware scan without being blocked by Securebit Technologies.
- Download Malwarebytes Chameleon from the below link, and extract it to a folder in a convenient location.
MALWAREBYTES CHAMELEON DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Chameleon)
- Make certain that your infected computer is connected to the internet and then open the Malwarebytes Chameleon folder, and double-click on the svchost.exe file.
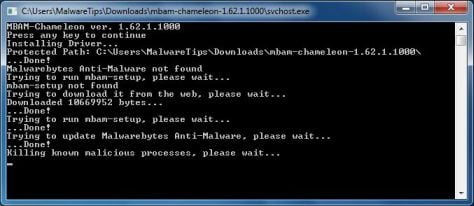
IF Malwarebytes Anti-Malware will not start, double-click on the other renamed files until you find one will work, which will be indicated by a black DOS/command prompt window. - Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
- Once it has done this, it will update Malwarebytes Anti-Malware, and you’ll need to click OK when it says that the database was updated successfully.
- Malwarebytes Anti-Malware will now attempt to kill all the malicious process associated with Securebit Technologies.Please keep in mind that this process can take up to 10 minutes, so please be patient.
- Next, Malwarebytes Anti-Malware will automatically open and perform a Quick scan for Securebit Technologies malicious files as shown below.
- Upon completion of the scan, click on Show Result
- You will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected.
Make sure that everything is Checked (ticked),then click on the Remove Selected button.
- After your computer restarts, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
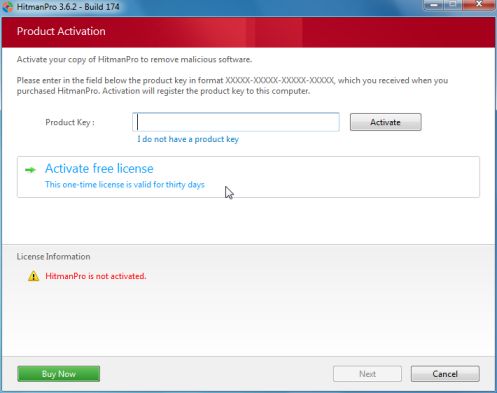
STEP 2: Remove Securebit Technologies rootkit with HitmanPro
In some cases,Securebit Technologies will also install a rootkit on victims computer.To remove this rootkit we will use HitmanPro.
- Download HitmanPro from the below link,then double-click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for Securebit Technologies malicious files as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.
- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
![Securebit Technologies virus [Image: Securebit Free Antivirus virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/04/securebit-technologies-virus.jpg)
![Windows has stopped working alert [Image: Windows has stopped working virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/04/windows-has-stopped-working-virus.jpg)
![Extract Malwarebytes Chameleon utility [Image: Extract Malwarebytes Chameleon utility]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-zip.jpg)
![Double click on svchost.exe [Image: Double click on svchost.exe]](http://malwaretips.com/blogs/wp-content/uploads/2013/02/malwarebytes-chameleon-svchost.jpg)
![Malwarebytes Anti-Malware scanning for Securebit Technologies [Image: Malwarebytes Anti-Malware scanning for Securebit Technologies]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of Securebit Technologies [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)