When it comes to computer processes and files, it’s important to understand their purpose and whether they pose any risks to your system. One such file that often raises questions is srvany.exe. In this article, we will delve into what srvany.exe is, whether you should remove it, and whether it is considered malware or not.

What is srvany.exe?
Srvany.exe is an executable file that stands for “Service Any”. It is a part of the Windows operating system and is used to run any executable as a service. Services in Windows are background processes that run without any user interaction and provide various functionalities to the system.
Srvany.exe allows you to convert any program or script into a service, enabling it to run in the background even when no user is logged in. This can be useful for running applications that require continuous operation, such as server software or monitoring tools.
Should I remove srvany.exe?
Whether or not you should remove srvany.exe depends on your specific needs and usage of the Windows operating system. Here are a few factors to consider:
1. Legitimate Use:
If you have intentionally installed a program or script that utilizes srvany.exe to run as a service, removing srvany.exe may cause that program or script to stop functioning correctly. It is important to identify the purpose of the service and determine if it is necessary for your system’s functionality.
2. Suspicious Behavior:
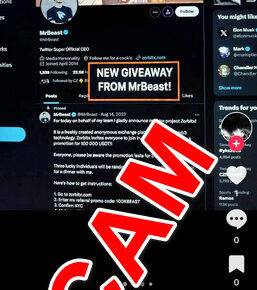
If you notice any suspicious behavior or performance issues on your system, it is recommended to investigate further. Malware or other malicious programs may disguise themselves as srvany.exe to evade detection. Running a thorough antivirus scan, such as Malwarebytes Free, can help identify and remove any potential threats.
3. Unnecessary Services:
Windows services consume system resources, and having unnecessary services running can impact performance. If you have identified a service that is no longer needed or is causing issues, you can consider removing it. However, it is crucial to exercise caution and ensure that you are not removing a legitimate service that is essential for your system’s operation.
Is srvany.exe malware?
Srvany.exe itself is not considered malware. It is a legitimate Windows component that serves a specific purpose. However, as mentioned earlier, malicious programs may disguise themselves as srvany.exe to avoid detection. Therefore, it is essential to verify the integrity of the file and investigate any suspicious behavior.
One way to determine if srvany.exe is legitimate is by checking its file location. The legitimate srvany.exe file is typically located in the “C:WindowsSystem32” folder. If you find srvany.exe in a different location or notice any unusual behavior associated with it, it is advisable to run a thorough antivirus scan using a reputable security software like Malwarebytes Free.
Summary
Srvany.exe is a legitimate Windows component that allows you to run any executable as a service. Whether or not you should remove it depends on your specific needs and usage of the Windows operating system. If you have intentionally installed a program or script that utilizes srvany.exe, removing it may cause that program or script to stop functioning correctly. However, if you notice any suspicious behavior or performance issues, it is recommended to investigate further and run a thorough antivirus scan using a reputable security software like Malwarebytes Free to identify and remove any potential threats.
Remember, it is crucial to exercise caution when dealing with system files and processes. Always verify the integrity of files, investigate any suspicious behavior, and seek professional assistance if needed.