If your computer is locked, and you are seeing a “Your computer has been blocked” notification that pretends to be from the PRS for Music, then your computer is infected with a piece of malware known as Trojan Kovter.
How did the “PRS for Music” virus got on my computer?
The PRS for Music virus is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission of knowledge.
Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the PRS for Music virus.
The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software.
The PRS for Music virus is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
What is the “PRS for Music” ransomware?
The PRS for Music virus is part of the Troj/Kovter Ransomware family of computer infections that target computers in United Kingdom.
When installed the PRS for Music virus will display a bogus notification that pretends to be from PRS for Music, and states that your computer has been blocked due to it being involved with the distribution of pornographic material, SPAM and copyrighted content.
The PRS for Music virus will lock you out of your computer and applications, so whenever you’ll try to log on into your Windows operating system or Safe Mode with Networking, it will display instead a lock screen asking you to pay a non-existing fine of £50 in the form of an Ukash or Paysafecard voucher. The malware’s authors prefer these payment services because transactions made through them cannot be reversed and are hard to trace.
Furthermore, to make this alert seem more authentic, this virus also has the ability to access your installed webcam, so that the bogus PRS for Music notification shows what is happening in the room.
Am I infected with the “PRS for Music” virus?
If your computer is infected with the PRS for Music ransomware, this infection will display a localized webpage that covers the entire desktop of the infected computer and demands payment for the supposed possession of illicit material. The message displayed by this ransomware infection can be localized depending on the user’s location, with text written in the appropriate language.
Here is the text for the PRS for Music scam:
Illegally downloaded music pieces (pirated) have been located on your computer.
By downloading, those music pieces were reproduced, thereby involving a criminal offense under Section 106 of the Copyright Act.The downloading of copyrighted songs via the Internet or music-sharing networks is illegal and is in accordance with Section 106 of the Copyright Act subject to a fine or imprisonment for a penalty of up to 3 years.
Furthermore, possession of illegally downloaded music pieces is punishable under Section 184 paragraph 3 of the Criminal Code and may also lead to the confiscation of the computer, with which the files were downloaded.You can be clearly identified by resolving your IP address and the associated hostname.
The pirated material has been encrypted and was moved to a protected folder to prevent further damage.
To unlock your computer and to avoid other legal consequences, you are obligated to pay a release fee of £50. Payable through our payment partner Paysafecard. After successful payment, your computer will automatically unlock.
Failure to adhere to this request could involve criminal charges and possible imprisonment.
To perform the payment, enter the acquired Paysafecard code in the designated payment box and press the “Submit” button.
The PRS for MUSIC is legitimized by law – and is in close contact with the legislators and the Metropolitan Police.
Cyber criminals often updated the design of this lock screen, however you should always keep in mind that the PRS for Music will never lock down your computer or monitor your online activities.
The PRS for Music lock screen is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you send a 100 Euro Ukash or Paysafecard voucher to these cyber criminals, and if you have, you can should request a refund, stating that you are the victim of a computer virus and scam.
How to remove the “PRS for Music ” virus (Removal Guide)
This page is a comprehensive guide, which will remove the PRS for Music infection from your your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
The PRS for Music will start automatically when you login to your computer and display its screenlocker so that you are unable to access your computer, therefore we will need to remove this infection by using any of the below methods:
OPTION 1: Remove PRS for Music virus with with HitmanPro Kickstart
OPTION 2: Remove PRS for Music lock screen virus with System Restore
OPTION 3: Remove PRS for Music virus with Kaspersky Rescue Disk
OPTION 1: Remove PRS for Music virus with HitmanPro Kickstart
HitmanPro.Kickstart is the solution against police ransomware and other persistent malware that has taken your computer hostage or prevents normal computer use.
As the PRS for Music ransomware infection has locked you out of your computer, we will need to create a bootable USB drive that contains the HitmanPro Kickstart program.
We will then boot your computer using this bootable USB drive and use it to clean the infection so that you are able to access Windows normally again.
To perform this step, you will also need a USB drive, which will have all of its data erased and will then be formatted. Therefore, only use a USB drive that does not contain any important data.
- Using a “clean” (non-infected) computer, please download HitmanPro Kickstart from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a download page in a new web page from where you can download HitmanPro Kickstart) - Once HitmanPro Kickstart has been downloaded, please insert the USB flash drive that you would like to erase and use for the installation of HitmanPro Kickstart. Then double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows).
To create a bootable HitmanPro USB drive, please follow the instructions from this video:
- Now, remove the HitmanPro Kickstart USB drive and insert it into the computer infected with the PRS for Music virus.
- Once you have inserted the HitmanPro Kickstart USB drive, turn off the infected computer and then turn it on. As soon as you power it on, look for text on the screen that tells you how to access the boot menu.
The keys that are commonly associated with enabling the boot menu are F10, F11 or F12. - Once you determine the proper key (usually the F11 key) that you need to press to access the Boot Menu, restart your computer again and start immediately tapping that key. Next, please perform a scan with HitmanPro Kickstart as shown in the video below.
- HitmanPro will now reboot your computer and Windows should start normally.Then please download Malwarebytes Anti-Malware and HitmanPro, and scan your computer for any left over infections as seen below.
OPTION 2: Remove PRS for Music lock screen virus with System Restore
System Restore helps you restore your computer’s system files to an earlier point in time. It’s a way to undo system changes to your computer without affecting your personal files, such as e‑mail, documents, or photos.
Because the PRS for Music virus will not allow you to start the computer in Windows regular mode, we will need to start System Restore from the Safe Mode with Command Prompt mode.
STEP 1: Restore Windows to a previous state using System Restore
- Reboot your computer into Safe Mode with Command Prompt. To do this, turn your computer off and then back on and immediately when you see anything on the screen, start tapping the F8 key on your keyboard.
If you are using Windows 8, the trick is to hold the Shift button and gently tap the F8 key repeatedly, this will sometimes boot you into the new advanced “recovery mode”, where you can choose to see advanced repair options. On the next screen, you will need to click on the Troubleshoot option, then select Advanced Options and select Windows Start-up Settings. Click on the Restart button, and you should now be able to see the Advanced Boot Options screen. - Using the arrow keys on your keyboard, select Safe Mode with Command Prompt and press Enter on your keyboard.
- At the command prompt, type rstrui.exe, and then press ENTER.
Alternatively, if you are using Windows Vista, 7 and 8, you can type: C:\windows\system32\rstrui.exe , and press Enter. And if you are a Windows XP user, type C:\windows\system32\restore\rstrui.exe, then press Enter. - System Restore should start, and you will display also a list of restore points. Try using a restore point created just before the date and time the PRS for Music lock screen virus has infected your computer.
- When System Restore has completed its task, start your computer in Windows regular mode, and perform a scan with Malwarebytes Anti-Malware and HitmanPro, as seen in the next step.
STEP 2: Remove PRS for Music virus with Malwarebytes Anti-Malware Free
- You can download Malwarebytes Anti-Malware Free from the below link, then double-click on the icon named mbam-setup.exe to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process, then at the last screen click on the Finish button.
- On the Scanner tab, select Perform quick scan, and then click on the Scan button to start searching for the PRS for Music malicious files.
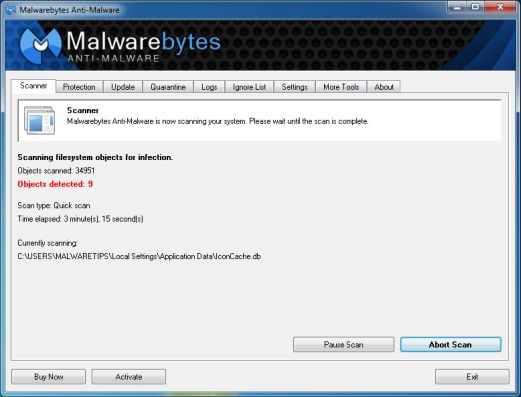
- Malwarebytes’ Anti-Malware will now start scanning your computer for PRS for Music virus as shown below.
- When the Malwarebytes Anti-Malware scan has finished, click on the Show Results button.
- You will now be presented with a screen showing you the computer infections that Malwarebytes Anti-Malware has detected. Make sure that everything is Checked (ticked), then click on the Remove Selected button.
STEP 3: Double-check for the PRS for Music virus with HitmanPro
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a web page from where you can download HitmanPro) - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the Next button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for PRS for Music malicious files.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove PRS for Music virus.
- Click on the Activate free license button to begin the free 30 days trial, and remove all the malicious files from your computer.
OPTION 3: Remove PRS for Music virus with Kaspersky Rescue Disk
If any of the above methods did not clean your infected computer, we can use a Kaspersky Rescue Disk Bootable to clean the Windows registry and to perform a system scan to remove the PRS for Music virus.
To create a bootable Kaspersky Rescue Disk, we will need the following items:
- A clean (non-infected) computer with Internet access
- A blank DVD or CD
- A computer with a DVD or CD burner
STEP 1: Download and create a bootable Kaspersky Rescue Disk CD
- You can download Kaspersky Rescue Disk utility from link below:
KASPERSKY RESCUE DISK DOWNLOAD LINK (This link will automatically download Kaspersky Rescue Disk kav_rescue_10.iso on your computer.) - To create the bootable rescue disk, we will need to use the ImgBurn program. You can download ImgBurn from the below link, then install this program.
IMGBURN DOWNLOAD LINK (This link will open a new page from where you can download the ImgBurn program) - Insert your blank DVD or CD in your burner, then start ImgBurn and click on the Write image file to disc button.
- Under Source click on the Browse for file button, then navigate to the location where you previously saved the Kaspersky Rescue Disk utility (kav_rescue_10.iso), then click on the Write button.
That’s it, ImgBurn will now begin writing your bootable Kaspersky Rescue Disk.
STEP 2: Start your computer using the Kaspersky Rescue Disk
- Once you’ve got the Kasperky Rescue Disk in hand, insert it into the infected computer, and turn off and then turn it on again.
- As soon as you power it on, you will see a screen that tells you to press any key to enter the menu, so please tap any key to boot your machine from the Kaspersky Rescue Disk.
- In the next screen, you will need to chose a language, then you click on Kaspersky Rescue Disk. Graphic Mode and press ENTER, to start the Kaspersky Rescue Disk.
STEP 3: Scan your system with Kaspersky Rescue Disk
- Within a few short seconds you should see the full working environment, with the Kaspersky Rescue Disk screen front and center as shown below.
- Switch tabs over to the My Update Center, and then click the Start update button to load the latest anti-virus definitions. Please be patience while this process its completed.
- Switch back over to the Objects Scan tab, select the drives you want to scan, and then click the Start Objects Scan button.
- When Kaspersky Antivirus will detect the PRS for Music virus, you’ll be prompted to select an action. When this happens, please select Quarantine or Delete to remove this infection from your computer.
- When the antivirus scan has completed, you can restart back into Windows regular mode, by clicking on the Kaspersky Start button
(lower left corner), and selecting Restart.
Once your computer will start in Windows regular more, download Malwarebytes Anti-Malware and HitmanPro, and scan your computer for any left over infections.
Your computer should now be free of the PRS for Music infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future, and perform regular computer scans with HitmanPro.
If you are still experiencing problems while trying to remove PRS for Music Ukash virus from your machine, please start a new thread in our Malware Removal Assistance forum.

![Windows Boot Menu screens [Image: Windows Boot Menu screens]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/windows-boot-manager.jpg)
![Windows F8 key [Image: F8 key]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/F8-key.jpg.png)
![Advanced Boot Options screen [Image: Starting computer in Safe Mode with Command Prompt]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Safe-Mode-with-Command-Prompt.jpg)
![rstrui.exe command in Safe Mode with Command Prompt [Image: Start System Restore to remove lock screen virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/system-restore-command.jpg)
![Restore your computer's system files to an earlier point in time [Image: Restore settings to remove ransomware]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/system-restore.jpg)
![Malwarebytes Anti-Malware installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Malwarebytes Anti-Malwar removing PRS for Music virus [Image: Malwarebytes Anti-Malwar removing PRS for Music virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)




![HitmanPro free 30 days trial [Image: HitmanPro 30 days activation button]](http://malwaretips.com/blogs/wp-content/uploads/2012/11/hitmanpro-activation.jpg)
![Creating Kaspersky Rescue Disk bootable CD [Image: Bootable Kaspersky Rescue CD]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/creating-bootable-kaspersky-rescue-disk.jpg)
![Starting infected computer from Kaspersky Rescue Disk [Image: Starting infected computer from Kaspersky Rescue Disk]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-boot.png)
![Kaspersky Rescue Disk Graphic Mode screen [Image: Kaspersky Rescue Disk Graphic Mode screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-graphic-mode.png)
![Kaspersky Rescue Disk scanner [Image: Kaspersky Rescue Disk scanner]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk.jpg)
![Updating Kaspersky Rescue Disk antivirus definitions [Image: Updating Kaspersky Rescue Disk antivirus definitions]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-update.jpg)
![Kaspersky Rescue Disk scan [Image: Kaspersky Rescue Disk scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-scan.jpg)
![Kaspersky Rescue Disk when detecting malware [Image: Kaspersky Rescue Disk prompt]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Kaspersky-Rescue-Disk-alarm.png)








HI,
Thanks for the advice, however I’m having to do this the manual way, and when I get to the shell entry in regedit it already points to explorer, so nothing to change there.
I randomly found the virus file on my desk top while in command prompt explorer and deleted it as well as checking my startup but its still there. Any more suggestions?
Thanks.
Hello Colin,
Did you create a Kaspersky bootable disk?
Thanks again for holding my hand during this process but I have something else that won’t let me start the removal of the virus.
When I turn on my pc it goes to a black screen that says “Boot selection pop up menu has been selected” Pressing F8 isn’t possible as it goes directly to this.
The only option I have is to press F1 to setup.
I tried it many times and nothing happened. I even left my PC so I could make lunch and it just says setup getting ready (Something like that).
Sorry for bugging you so much but I can’t even find info on how to go passed this bit before I can fix my PC.
Did you try to create a Kapersky Bootable Disk??
This required the disc again?
Oh haha I threw it away.. I’ll make another one then and try again tomorrow.
What Anti-Virus/Anti-Malware should I use in future?
I actually bought one when my PC got that PRS for music Ransomware.
Here is how you can remove this infection , without using a bootable disk :
STEP 1 : Start your computer in Safe Mode with Command Prompt
STEP 2: Remove the malicious registry key and file
The Windows Explorer will open, do not close this window.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\ and search on the list to the right for an registry entry named Shell.
In our case, the malicious file is running from the Desktop and it’s called “contacts.exe”, but the cyber crimanls may have changed the file name in your case so it might have a different name.
Next perform a scan with Malwarebytes Anti-Malware Free
[hr]
As for what security product to use ,you should really start a thread in our Security Configuration forum as you need to build a layerd security config: http://malwaretips.com/Forum-Security-Configuration-Wizard
McAfee is the worst!! :)
As a quick answer :
Free – Avast 7 Free version or COMODO Internet Security
Paid : Norton Internet Security 2012 or Avast Internet Security 7
Good luck! B-)
When I turn on my pc it goes to a black screen that says “Boot selection pop up menu has been selected” Pressing F8 isn’t possible as it goes directly to this.
The only option I have is to press F1 to setup.
Pressing F8 has no effect as this screen comes on instantly.
I want to be able to do it but I have one more hurdle:
http://www.youtube.com/watch?v=WADh3QuB1c8&feature=youtu.be
I really appreciate the help you’ve given so far
Step 3 , instead of asking to press any key when I use kapersky via usb it takes me to Grub> command prompt,any idea what to do next
Did you configure your PC to boot from the USB? – http://support.kaspersky.com/faq/?qid=208286083
thanks for responding , yes i did,it boots from the USB ,but takes me to Grub command prompt
I have also tried,AVG,Bit defender and Avira rescue CDs all from USB but unfortunately these cant fix the issue
Did you try to manually remove this infection???
STEP 1 : Start your computer in Safe Mode with Command Prompt
STEP 2: Remove the malicious registry key and file
The Windows Explorer will open, do not close this window.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\ and search on the list to the right for an registry entry named Shell.
In our case, the malicious file is running from the Desktop and it’s called “contacts.exe”, but the cyber crimanls may have changed the file name in your case so it might have a different name.
Next perform a scan with Malwarebytes Anti-Malware Free
Hi, I got it to work, I copied GRUB EL TORITO to the GRUB folder and it worked , thanks
Thanks for such a quick and detailed response.
What I need to ask before I try this is when I type in some of this stuff will I have to type Windows xp or XP?
I really don’t know if upper or lower case letters will make a difference.
Thanks so far though!
Use lowercase…doesn;t really matter but use lowercase:P
Good luck!
Hi there,
I got this virus not too long ago and followed these tips but for some reason it went wrong.
The windowsunlocker option was not present on my Kaspersky. So instead I scanned and removed/quarantined as advised.
The program then crashed and when I turned my PC on again it stayed on a black page again and the Kaspersky was not able to start again.
Is there anything else I can do as I have a lot of files that I do not have anywhere else?
Appreciate any help.
Thanks!
Hello,
Try this and then report back for further instructions :
STEP 1 : Start your computer in Safe Mode with Command Prompt
STEP 2: Remove the malicious registry key and file
The Windows Explorer will open, do not close this window.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\ and search on the list to the right for an registry entry named Shell.
In our case, the malicious file is running from the Desktop and it’s called “contacts.exe”, but the cyber crimanls may have changed the file name in your case so it might have a different name.
Wrote this guide : http://malwaretips.com/blogs/remove-police-trojan/ : you can follow any of the 3 methods to get rid of the virus!!