silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,172
Since January 2020, a mysterious threat actor has been adding servers to the Tor network in order to perform SSL stripping attacks on users accessing cryptocurrency-related sites through the Tor Browser.
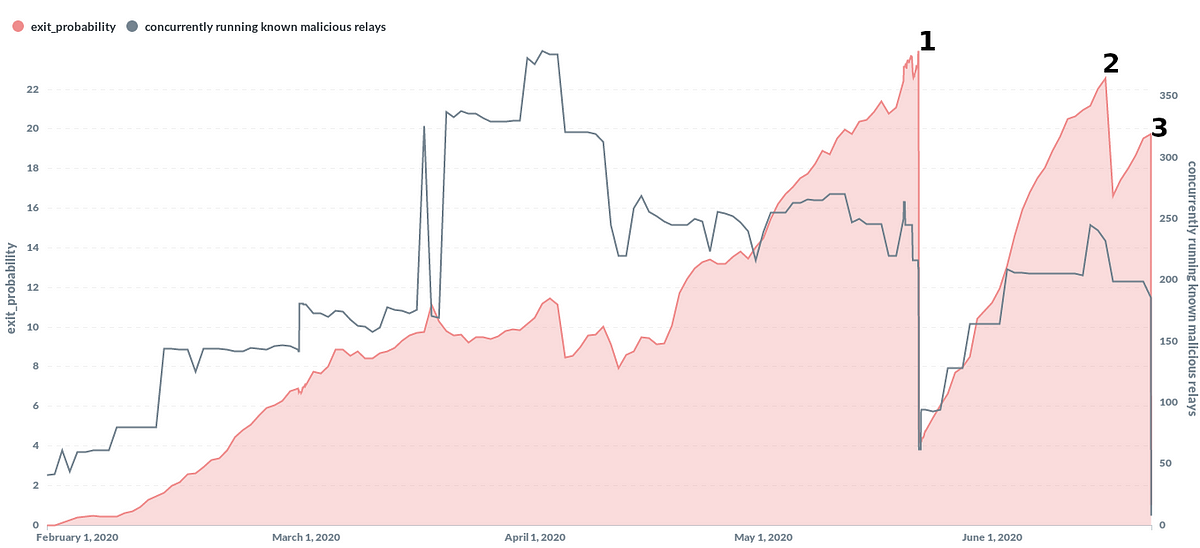
The group has been so prodigious and persistent in their attacks, that by May 2020, they ran a quarter of all Tor exit relays — the servers through which user traffic leaves the Tor network and accesses the public internet.
According to a report published on Sunday by an independent security researcher and Tor server operator known as Nusenu, the group managed 380 malicious Tor exit relays at its peak, before the Tor team made the first of three interventions to cull this network.
"The full extend[sic] of their operations is unknown, but one motivation appears to be plain and simple: profit," Nusenu wrote over the weekend.
The researcher says the group is performing " person-in-the-middle attacks on Tor users by manipulating traffic as it flows through their exit relays," and that they are specifically targeting users accessing cryptocurrency-related websites using the Tor software or Tor Browser.
The goal of the person-in-the-middle attack is to execute "SSL stripping" attacks by downgrading the user's web traffic from HTTPS URLs to less secure HTTP alternatives.