- Apr 17, 2011
- 9,224
Zscaler researchers make an interesting point about fake antiviruses, also known as scareware. Despite the fact that they've been around for several years, many security solutions are still incapable of blocking these threats.
Researchers highlight the fact that, overall, scareware has remained the same as it was a few years ago. The names of the bogus applications may have changed, but other than that, they're pretty much the same.
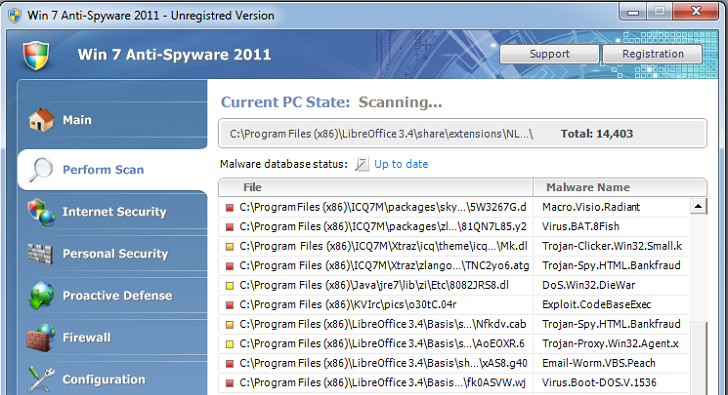
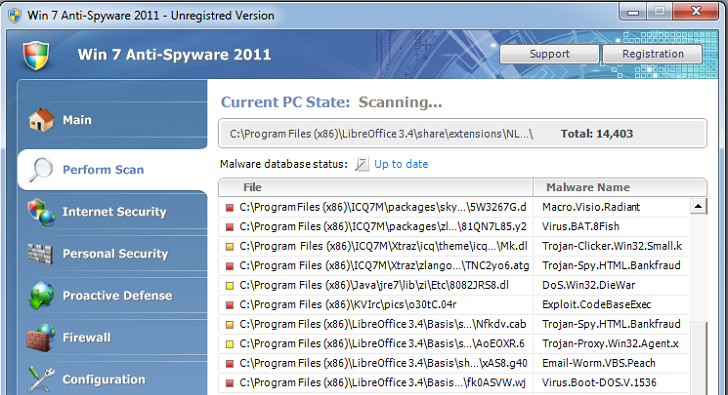
A perfect example is the Win 7 Anti-Spyware 2011 (click here) piece of scareware which we detailed a few days ago.
The threat is undetected by most security applications, and when it finds itself on a computer, it starts causing serious damage.
It disables the firewall, the legitimate antivirus application, disables all security warnings and it creates registry entries to ensure that it has full control over the infected device.
Furthermore, it wraps any executable run by the user, so when any application is run, the scareware steps into play, alerting the victim about all sorts of Trojans and Worms that can be allegedly cleaned only by registering the bogus antivirus.
While performing our tests, we've managed to remove the scareware in approximately two hours, but for a regular user the task would not be easy.
Source
Researchers highlight the fact that, overall, scareware has remained the same as it was a few years ago. The names of the bogus applications may have changed, but other than that, they're pretty much the same.
A perfect example is the Win 7 Anti-Spyware 2011 (click here) piece of scareware which we detailed a few days ago.
The threat is undetected by most security applications, and when it finds itself on a computer, it starts causing serious damage.
It disables the firewall, the legitimate antivirus application, disables all security warnings and it creates registry entries to ensure that it has full control over the infected device.
Furthermore, it wraps any executable run by the user, so when any application is run, the scareware steps into play, alerting the victim about all sorts of Trojans and Worms that can be allegedly cleaned only by registering the bogus antivirus.
While performing our tests, we've managed to remove the scareware in approximately two hours, but for a regular user the task would not be easy.
Source

