- Jul 27, 2015
- 5,459
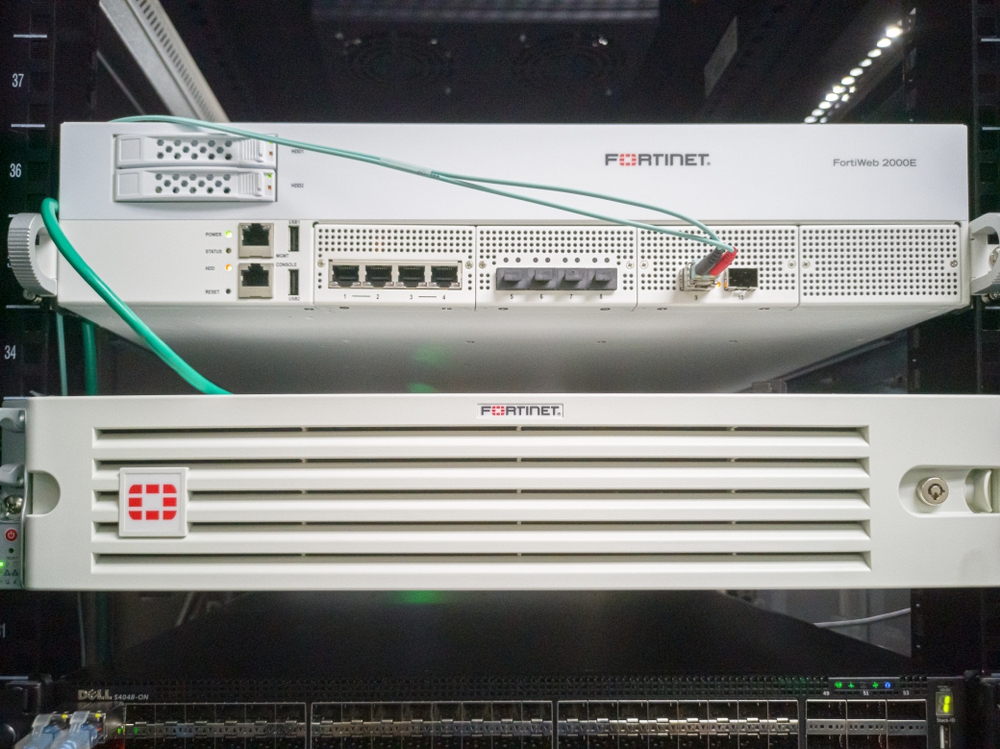
After privately warning customers last week that they need to patch or mitigate CVE-2022-40684, a critical vulnerability affecting FortiOS, FortiProxy, and FortiSwitchManager, Fortinet has finally confirmed that it “is aware of an instance where this vulnerability was exploited.”
But their advice to organizations to immediately check their systems for a specific indicator of compromise makes it sound like they believe more widespread attacks have happened or are happening.
CVE-2022-40684 is an authentication bypass vulnerability on vulnerable devices’ administrative interface that can be triggered by sending a specially crafted HTTP(S) requests. It affects :
Successful exploitation may allow attackers with access to the management interface to perform administrator operations and to, essentially, take control of the device. The patch has already been reverse-engineered by security researchers
- FortiOS versions: 7.2.1, 7.2.0, 7.0.6, 7.0.5, 7.0.4, 7.0.3, 7.0.2, 7.0.1, 7.0.0
- FortiProxy versions: 7.2.0, 7.0.6, 7.0.5, 7.0.4, 7.0.3, 7.0.2, 7.0.1, 7.0.0
- FortiSwitchManager versions: 7.2.0, 7.0.0

Auth bypass bug in FortiOS, FortiProxy is exploited in the wild (CVE-2022-40684) - Help Net Security
A critical vulnerability (CVE-2022-40684) affecting FortiOS, FortiProxy, and FortiSwitchManager is being exploited by attackers.
 www.helpnetsecurity.com
www.helpnetsecurity.com