You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- Sep 12, 2015
- 617
Hand down CIS. Best free prevention and lock down security software ever, but this software is for advanced users only that knows what they are doing because by tweaking you can make CIS outperform other antiviruses easily.
- Jun 21, 2014
- 1,044
CIS require knowledge, AVG doesn't.
I voted CIS because I know how to set it and it has the best protection out there. AVG is for average user
I voted CIS because I know how to set it and it has the best protection out there. AVG is for average user
- Jun 9, 2013
- 6,720
- Jul 6, 2015
- 737
- Jan 27, 2013
- 661
You cannot go wrong with comodo.It beats AVG hands down.Comodo is a great complete security suite and all for free.
I
illumination
Thread author
I think a proclaimed advanced user that uses Virtualbox should test both these products in it and decided for themselves. Level of knowledge would be a key factor here deciding between these two products.
Above you ask for user friendliness and user interface, these are two things generally not associated with CIS, although advanced users would have no trouble learning..
Above you ask for user friendliness and user interface, these are two things generally not associated with CIS, although advanced users would have no trouble learning..
- Feb 22, 2013
- 451
I choose Comodo Internet Security, as compared to AVG, it is more effective and profesional product.
- Mar 15, 2011
- 13,070
Its like the comparison for here is totally different where one is not an IS.
But to be frankly, the actual components as an edge for Comodo than AVG however its up to the user on the requirements cause when more features included then time management increase that may affect your productive tasks.
But to be frankly, the actual components as an edge for Comodo than AVG however its up to the user on the requirements cause when more features included then time management increase that may affect your productive tasks.
- Oct 30, 2015
- 1,251
Maybe I should asked this: how much time are you wiling to spend to configure the security program? 
It could be a key question to determine one which of the two is preferable.
It could be a key question to determine one which of the two is preferable.
L
LabZero
Thread author
What characterizes AVG is simplicity for normal use, for all users.
An experienced user can install CIS that offers excellent features but that must be managed and set with knowledge, for example behavioral blocking in interactive mode and this applies to other advanced security configurations.
It is possible to specify the blocking policy stating what behaviors are considered legit and which are not. Whenever a program launches a request to the operating system, behavioral blocking intercepts the request, check the policy, and decide whether to block the request.
This setting gives some false positives and has an impact on productivity because block, in the same way, legitimate apps and malicious one. Also there are few users who fully understand the implication of specific blocks, for example, file access, but how can a average/basic user know which and how many good programs can access to system files and which are effective malicious software?
Expert users analyze entire classes of malicious codes and analyzed their behavior in order to define what are the behaviors they want to block. This causes potentially harmful behaviors may be allowed in some cases while in others should be blocked. For example an expert might know that 80% of malicious code first tries to change the autostart registry entries before access to system files, so he can define a behavior to block what occurs when a code attempts to access system files after making a change to the registry. This leaves less room for false positives that might be generated by legitimate programs.
Knowledge and stay safe.
An experienced user can install CIS that offers excellent features but that must be managed and set with knowledge, for example behavioral blocking in interactive mode and this applies to other advanced security configurations.
It is possible to specify the blocking policy stating what behaviors are considered legit and which are not. Whenever a program launches a request to the operating system, behavioral blocking intercepts the request, check the policy, and decide whether to block the request.
This setting gives some false positives and has an impact on productivity because block, in the same way, legitimate apps and malicious one. Also there are few users who fully understand the implication of specific blocks, for example, file access, but how can a average/basic user know which and how many good programs can access to system files and which are effective malicious software?
Expert users analyze entire classes of malicious codes and analyzed their behavior in order to define what are the behaviors they want to block. This causes potentially harmful behaviors may be allowed in some cases while in others should be blocked. For example an expert might know that 80% of malicious code first tries to change the autostart registry entries before access to system files, so he can define a behavior to block what occurs when a code attempts to access system files after making a change to the registry. This leaves less room for false positives that might be generated by legitimate programs.
Knowledge and stay safe.
C
CySecy825
Thread author
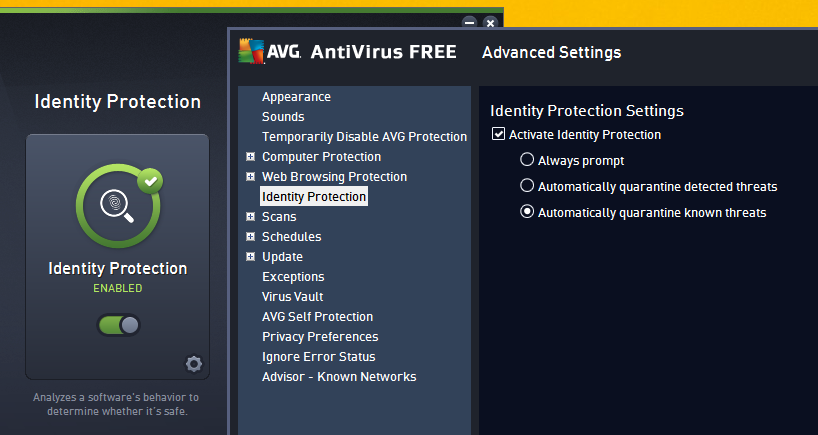
How about Avg Identify Protection is it good ?
for zero day threats compared to CIS BB or hips
for zero day threats compared to CIS BB or hips
- Jan 8, 2011
- 22,361
Update: There are better choices than AVG Free. They used to be good, but the overall experience of AVG 2016 has been more intrusive than expected. Where to start..
I installed AVG Free Antivirus, but ended up with AVG PC Tune Up and Web Tune Up. Bloatware Everywhere.
Don't forget their new Privacy Policy to sell your data.
AVG ID Protection is it's Behavioural Guard, I remember testing it years ago, when it was a standalone tool. It will compliment the real-time protection.
From their non-updated help pages:
I installed AVG Free Antivirus, but ended up with AVG PC Tune Up and Web Tune Up. Bloatware Everywhere.
Don't forget their new Privacy Policy to sell your data.
How about Avg Identify Protection is it good ?
for zero day threats compared to CIS BB or hips
AVG ID Protection is it's Behavioural Guard, I remember testing it years ago, when it was a standalone tool. It will compliment the real-time protection.
AVG Identity Protection™
Analyzes a software’s behavior in real-time to determine if it’s safe. This feature helps protect you against 0-day threats and malicious programs that could steal your passwords, bank account details, and other digital valuables.
From their non-updated help pages:
AVG Identity Protection uses a technology called behavioral analysis to make sure all the programs running on your PC are operating the way they should. If it spots something suspicious that could indicate an attempted identity theft attack, it shuts that activity down, preventing any possible theft from happening. It doesn’t matter whether you’re running AVG software or security software from another vendor; identity protection runs alongside all popular programs to keep you safer when they’re online.
Source - AVG | AVG Identity Protection for Windows
Last edited:
- Nov 18, 2015
- 104
my vote goes to avg because can cure much better an already infected pc and its easy to use...comodo is for advanced users who propably dont need an av to protect their pc
- Jan 14, 2015
- 1,761
voted other: avast free and Fortinet, simply because they offer decent protection and are user friendly and resource friendly compared to AVG and Comodo. AVG and Comodo have their short comings. Not to say avast and Fortinet dont, but overall, those are in my opinion superior. Sure, Comodo offers stellar zero day protection, if you like to configure left right and center and spend time with every aspect of the configuration in order not to "break" anything.
- Nov 18, 2015
- 104
you can try 360 TS its easy and very goodOk but can someone help me choose antivirus ???
its need to be Light and silent av but ok detection and free. i have panda but VERY SLOW SCAN Speed and i heard bad things so i removed it
Thanks for helping
C
CySecy825
Thread author
I Maybe try fortinet but it doesn,t have BB
what is their protection for zero-day threats
and 360 Ts its good but what i see its bloated
and heurestic block steam game updates : (
but i try fortinet did i need comodo firewall combo for it because if it doesn,t have behavior analysis or any kinds of zero day protection
THANKS
what is their protection for zero-day threats
and 360 Ts its good but what i see its bloated
and heurestic block steam game updates : (
but i try fortinet did i need comodo firewall combo for it because if it doesn,t have behavior analysis or any kinds of zero day protection
THANKS
- Jan 8, 2011
- 22,361
Similar threads
App Review
Huorong Internet Security Antivirus Review
- Replies
- 5
- Views
- 736
- Replies
- 1
- Views
- 337
- Replies
- 11
- Views
- 922
