L
LabZero
Thread author
Crypto-ransomware is one of the latest trends in the world of malware. Encrypting and holding files to ransom provides a way to extort money from victims, but a new example takes things one step further.
Chimera not only locks users out of their files until a ransom is paid, but also threatens to release unencrypted copies of the files online if payment is not made. Security company Trend Micro says this is the first instance of this type of threat. Interestingly, Chimera also seems to be part of an affiliate program.
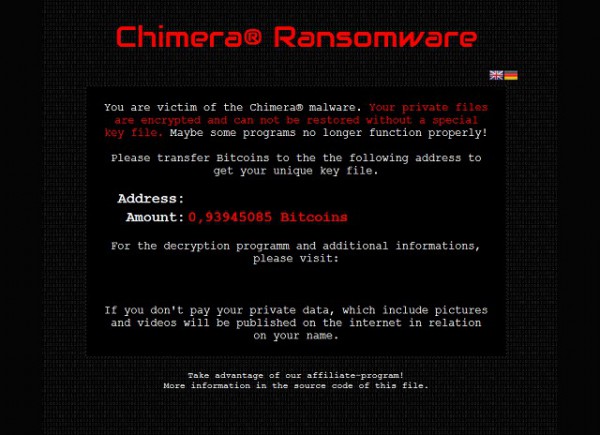
Infected systems display a warning informing victims that their data will be inaccessible until they cough up the ransom. The incentive that said files will be leaked to the internet is an extra encouragement, particularly for anyone with content they would rather not be associated with. Victims are told:
If you don’t pay your private data, which include pictures and videos will be published on the internet in relation to your name.
In addition to trying to extort money from people, Chimera also acts as a recruitment campaign. The warning screen that lets people know that their computer is infected includes a footnote:
Take advantage of our affiliate-program! More information in the source code of this file.
As Trend Micro notes, this "is clearly a way to sift out people with technical skills". The security firm has examined the source code and determined that it does contain contact details and Bitcoin information for payment. There is also a decryption tool which checks to see whether a Bitcoin payment has been made before freeing up files.
Chimera is being described as Ransonware as a Service (RaaS) because of its recruitment drive component, and this could be the direction in which future ransomware is heading.

