silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,176
Threat actors behind an ongoing worldwide mobile banking fraud campaign were able to steal millions from multiple US and EU banks, needing just a few days for each attack.
To do that, the attackers used huge emulator farms that helped them access thousands of hacked accounts (compromised after phishing or malware attacks) using spoofed mobile devices.
While emulators are not malicious tools, the group behind this campaign used them for malicious purposes emulating compromised devices or setting up what looked like new devices picked up by the compromised accounts' owners.
For setting up the emulated devices, the attackers used a dedicated tool capable of feeding device specs from a database of previously compromised devices, matching each of the spoofed devices with the account holder's banking credentials.
The mobile emulator farm was even able to spoof a compromised device's GPS location using virtual private network (VPN) services to hide the malicious activity from the bank.
Read more below: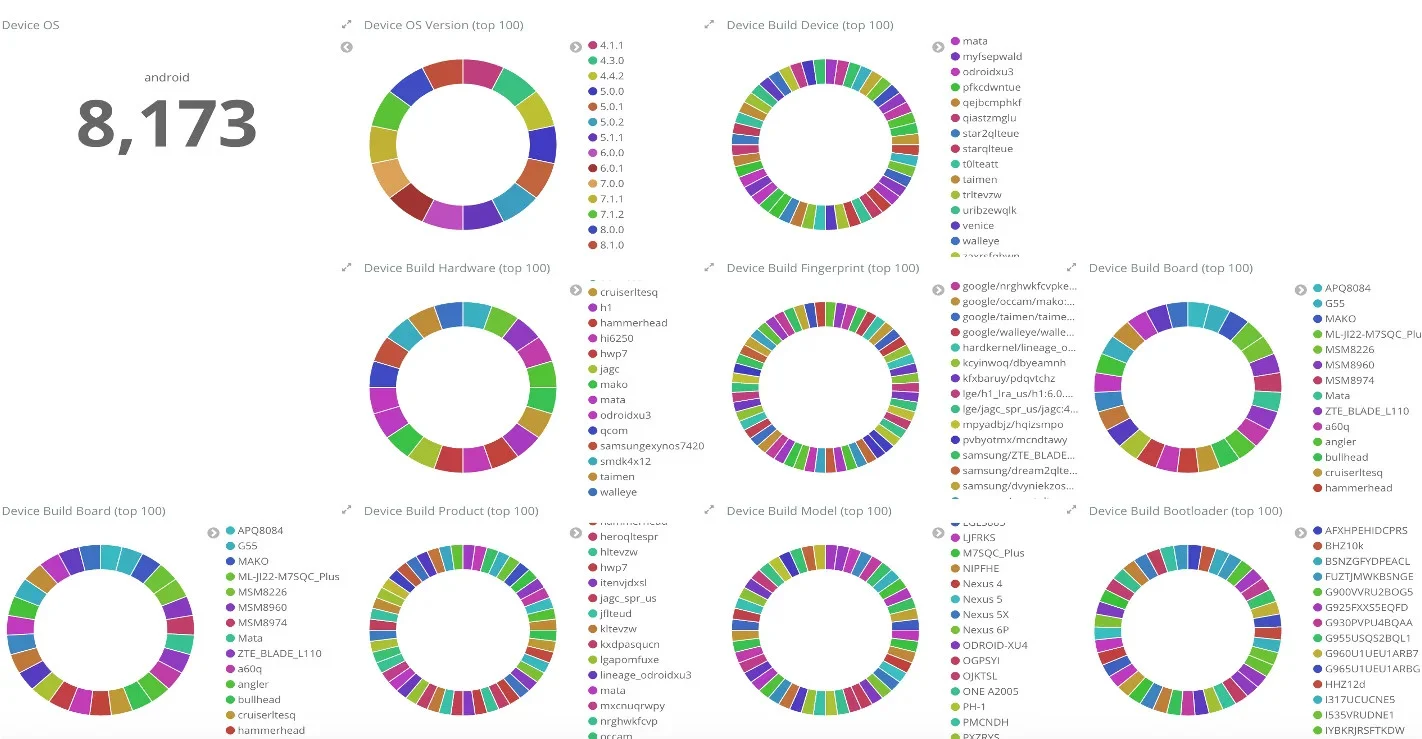
Data slices from emulator used to spoof over 8,000 devices (IBM Trusteer)

Emulated mobile devices used to steal millions from US, EU banks
Threat actors behind an ongoing worldwide mobile banking fraud campaign were able to steal millions from multiple US and EU banks, needing just a few days for each attack.
Full report below by researchers:

IBM Trusteer Exposes Massive Fraud Operation Facilitated by Evil Mobile Emulator Farms
A major mobile emulator fraud operation broke into bank accounts, IBM Security Trusteer found. Explore the attack and how IBM's team caught it.
 securityintelligence.com
securityintelligence.com
