- Sep 5, 2017
- 1,168
Hello everybody
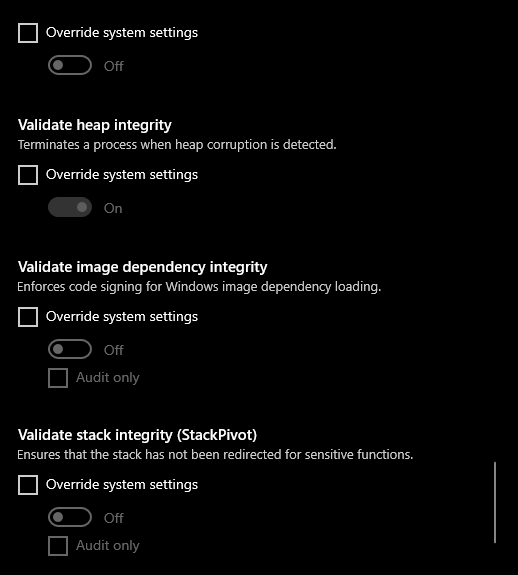
i just come found by coincidence option for exploit protection built in my windows 10 (honestly i don't know it is exist as i depend mainly on Emsisof as animalware and don't get close to windows security center as there is no any red alert notification )
)
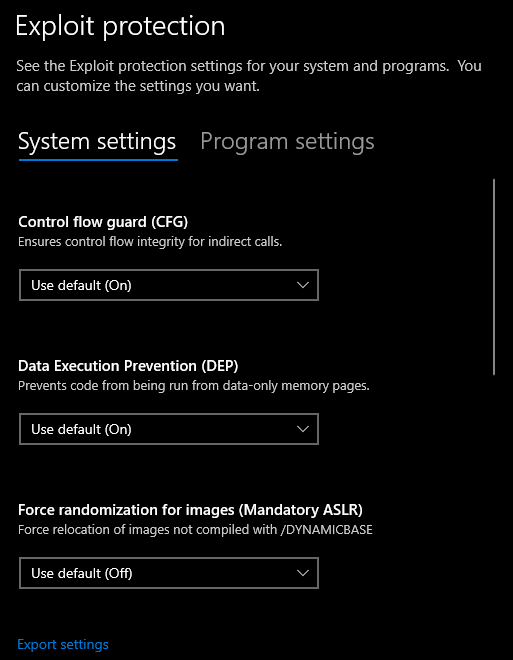
anybody can give me a hint about how to adjust it and the meaning of each setting
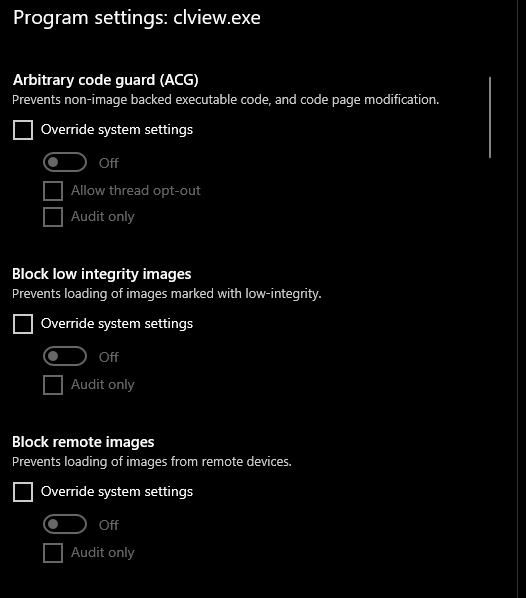
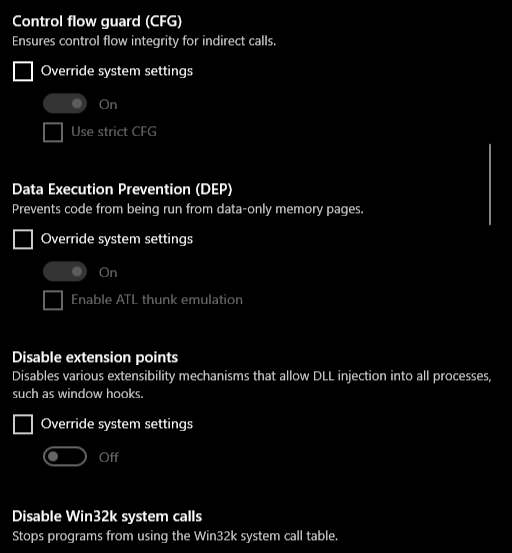
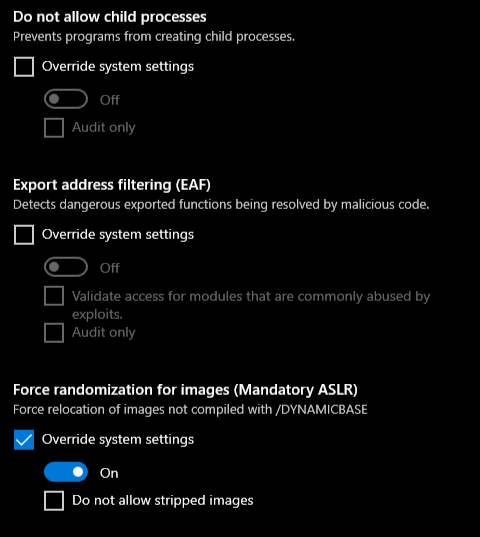
Note:by default all system setting is enabled however i want to add some programs to program settings
Edit:many settings in program settings as added in spoiler part
i just come found by coincidence option for exploit protection built in my windows 10 (honestly i don't know it is exist as i depend mainly on Emsisof as animalware and don't get close to windows security center as there is no any red alert notification
anybody can give me a hint about how to adjust it and the meaning of each setting
Note:by default all system setting is enabled however i want to add some programs to program settings
Edit:many settings in program settings as added in spoiler part
Last edited:




