silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,172
Qualcomm and MediaTek Wi-Fi chips were found to have been impacted by new variants of the KrØØk information disclosure vulnerability discovered by ESET researchers Robert Lipovský and Štefan Svorenčík. [...]
Lipovský and Svorenčík discovered new KrØØk variants that have also impacted systems Qualcomm and MediaTek radios used in vehicles, navigation systems, watches, laptops, smartphones, routers, and other devices.
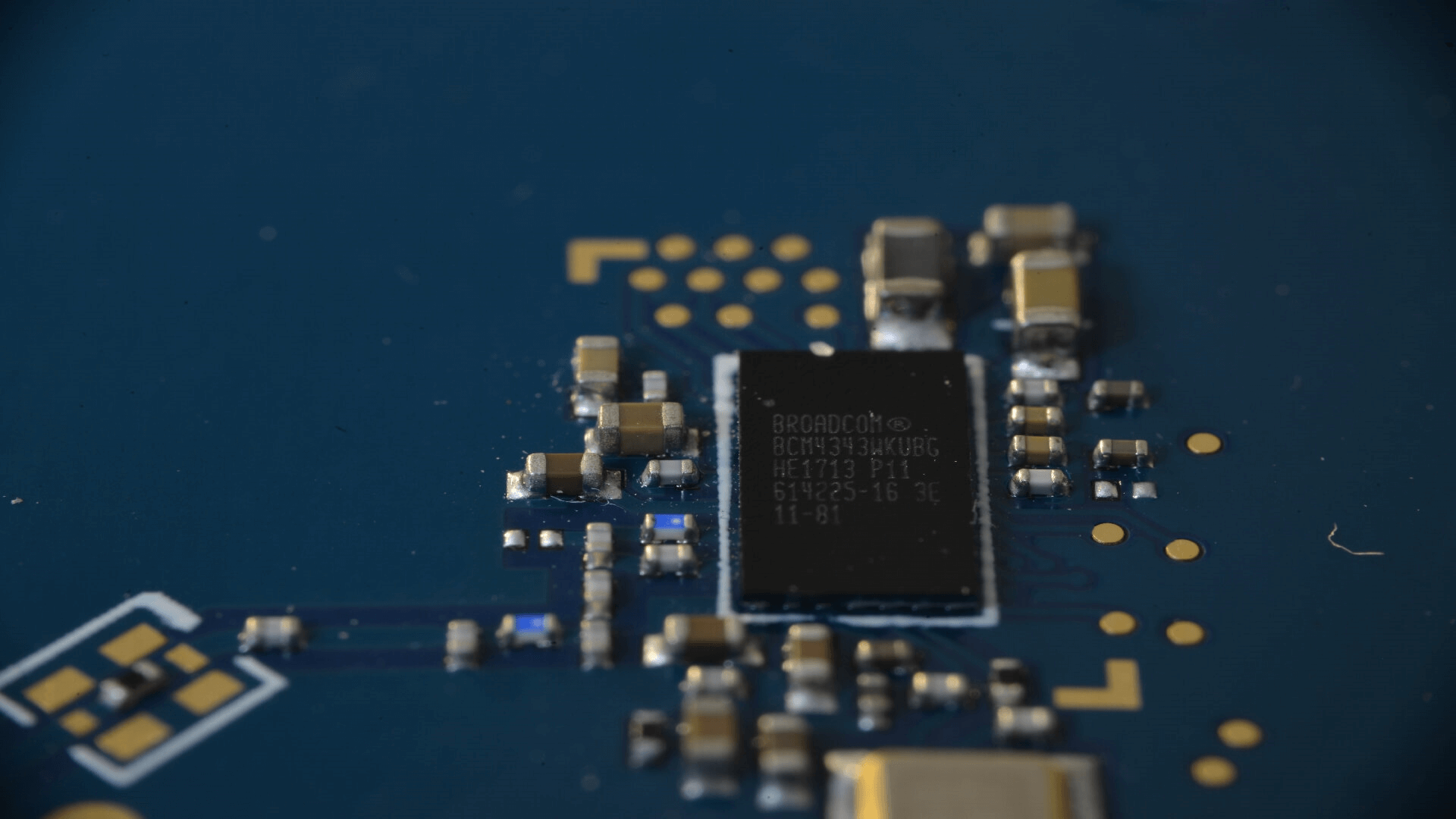
"One of the chips we looked at aside from those from Broadcom and Cypress was by Qualcomm," the researchers explain in a report published today and shared with BleepingComputer earlier this week.
"The vulnerability we discovered (which was assigned CVE-2020-3702) was also triggerable by a disassociation and led to undesirable disclosure of data by transmitting unencrypted data in the place of encrypted data frames – much like with KrØØk."
"We also observed the manifestation of a similar vulnerability (i.e. lack of encryption) on some Wi-Fi chips by MediaTek," including the ASUS RT-AC52U route and the Microsoft Azure Sphere development kit that utilizes the MT3620 microcontroller also used in smart home, commercial, and industrial solutions.