Solved Malware appears to be google redirect, but am still having odd messages from Malwarebytes
- Thread starter Wade
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- Apr 24, 2014
- 3,395
Helllo,
My name is Argus and and I will be helping you with your computer problems.
Before we begin, please note the following:
 Scan with Farbar Recovery Scan Tool
Scan with Farbar Recovery Scan Tool
Please download Farbar Recovery Scan Tool and save it to your desktop.
Note: You need to run the version compatibale with your system. If you are not sure which version applies to your system download both of them and try to run them.
Only one of them will run on your system, that will be the right version.
My name is Argus and and I will be helping you with your computer problems.
Before we begin, please note the following:
- I will working be on your Malware issues, this may or may not, solve other issues you have with your machine.
- The logs can take some time to research, so please be patient with me.
- Stay with the topic until I tell you that your system is clean. Missing symptoms does not mean that everything is okay.
- Instructions that I give are for your system only!
- Please do not run any tools until requested ! The reason for this is so I know what is going on with the machine at any time. Some programs can interfere with others and hamper the recovery process.
- Please perform all steps in the order received. If you can't understand something don't hesitate to ask.
- Again I would like to remind you to make no further changes to your computer unless I direct you to do so. I will not help you if you do not follow my instructions.

Please download Farbar Recovery Scan Tool and save it to your desktop.
Note: You need to run the version compatibale with your system. If you are not sure which version applies to your system download both of them and try to run them.
Only one of them will run on your system, that will be the right version.
- Double-click to run it. When the tool opens click Yes to disclaimer.
- Press Scan button.
- It will make a log (FRST.txt) in the same directory the tool is run. Please attach it to your reply.
- The first time the tool is run, it makes also another log (Addition.txt). Please attach it to your reply.
- Apr 24, 2014
- 3,395
You need to exit MalwareBytes in your tray area. Right click and select Exit.
Download
 Malwarebytes Anti-Rootkit to your desktop.
Malwarebytes Anti-Rootkit to your desktop.
Download
- Double-click the icon to start the tool.
- It will ask you where to extract it, then it will start.
- Warning! Malwarebytes Anti-Rootkit needs to be run from an account with administrator rights.
- Click in the introduction screen "next" to continue.
- Click in the following screen "Update" to obtain the latest malware definitions.
- Once the update is complete select "Next" and click "Scan".
- When the scan is finished and no malware has been found select "Exit".
- If malware was detected, make sure to check all the items and click "Cleanup". Reboot your computer.
- Open the MBAR folder and paste the content of the following files in your next reply:
- "mbar-log-{date} (xx-xx-xx).txt"
- "system-log.txt"
- Mar 17, 2015
- 14
- Apr 24, 2014
- 3,395
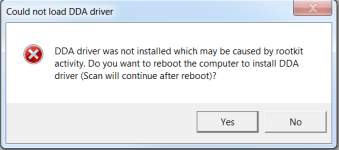
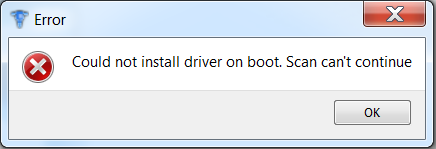
DDA stands for Direct Disk Access, and is required for rootkit scanning. Malwarebytes Anti-Rootkit needs this driver installed in order to be able to detect and remove most rootkits and is needed for it to function properly on any operating system. It's possible that another process is blocking it from doing so, such as your antivirus or third party firewall if you use one.
- Apr 24, 2014
- 3,395
Disable AVG and download new MBAR. Run the scan again.
Disable AVG
http://www.bleepingcomputer.com/forums/topic114351.html
Disable AVG
http://www.bleepingcomputer.com/forums/topic114351.html
- Apr 24, 2014
- 3,395

Once again we shall use FRST for additional checks. Re-run FRST/FRST64 the same way:
- Copy explorer.exe into the Search: field in FRST then click the Search Files button.
- FRST will search your computer for files and when finished it will produce a log Search.txt in the same directory the tool is run.
- Please attach it to your reply.
- Apr 24, 2014
- 3,395

Both files, FRST and fixlist.txt have to be in the same location or the fix will not work!
- Right-click on
icon and select
 Run as Administrator to start the tool.
Run as Administrator to start the tool.
(XP users click run after receipt of Windows Security Warning - Open File). - Press the Fix button just once and wait.
- If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run.
- When finished FRST will generate a log on the Desktop, called Fixlog.txt.
Please attach it to your reply.
Attachments
- Mar 17, 2015
- 14
Had a bunch more in the last few hours. 2-3 of each of these.
Malicious Website Protection, IP, 93.170.129.114, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 212.117.179.52, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 193.138.246.122, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 217.23.187.192, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 93.170.129.114, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 212.117.179.52, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 193.138.246.122, 6881, Outbound, C:\Windows\explorer.exe
Malicious Website Protection, IP, 217.23.187.192, 6881, Outbound, C:\Windows\explorer.exe
Similar threads
- Locked
- Replies
- 7
- Views
- 508
-
- Locked
- Replies
- 6
- Views
- 945