silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,165
Full report by researchers from Sophos: Maze attackers adopt Ragnar Locker virtual machine technique[...] While performing an incident response for one of their customers, Sophos discovered Maze had attempted to deploy their ransomware twice but were blocked by Sophos' Intercept X feature.
For the first two attempts, the Maze attacker attempted to launch various ransomware executables using scheduled tasks named 'Windows Update Security,' or 'Windows Update Security Patches,' or 'Google Chrome Security Update.'
After the two failed attacks, Sophos' Peter Mackenzie told BleepingComputer that the Maze threat actors tried a tactic previously used by the Ragnar Locker ransomware.
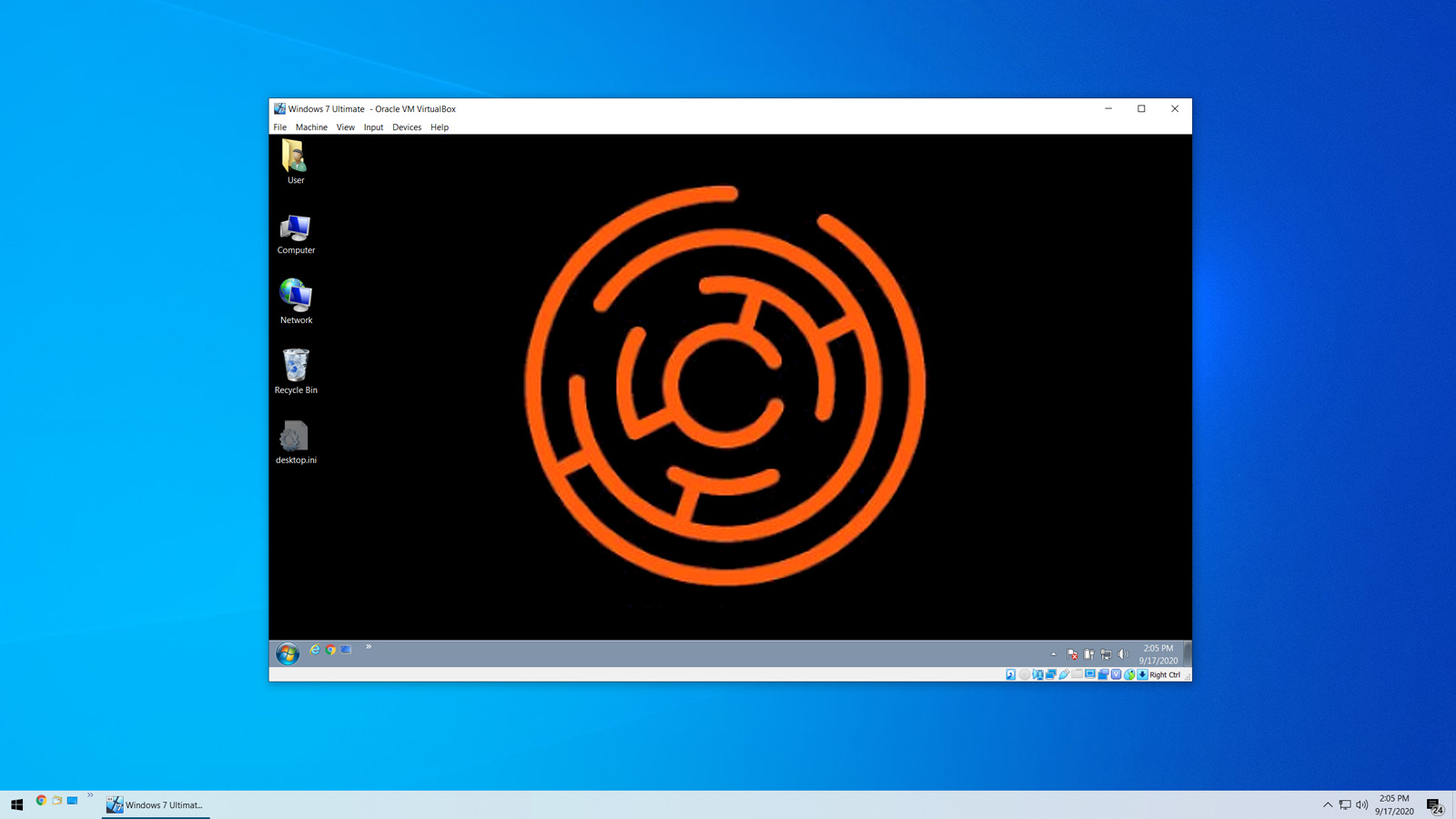
In their third attack, Maze deployed an MSI file that installed the VirtualBox VM software on the server along with a customized Windows 7 virtual machine. [...]
Last edited: