silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,154
Microsoft has fixed today a Windows kernel zero-day vulnerability exploited in the wild as part of targeted attacks and publicly disclosed by Project Zero, Google's 0day bug-hunting team, last month.
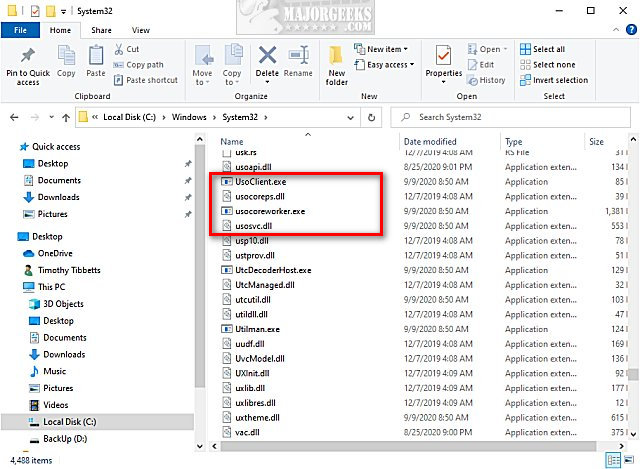
According to Project Zero researchers Mateusz Jurczyk and Sergei Glazunov who discovered it, the security flaw currently tracked as CVE-2020-17087 is a pool-based buffer overflow found in the Windows Kernel Cryptography Driver (cng.sys).
"The bug resides in the cng!CfgAdtpFormatPropertyBlock function and is caused by a 16-bit integer truncation issue," the researchers explained.
Microsoft tagged the bug with a CVSS:3.0 severity rating of 7.8/10 saying that it can be exploited by local attackers with low privileges for privilege escalation (including sandbox escape) in low complexity attacks not requiring user interaction.
CVE-2020-17087 affects desktop systems running Windows 7 or later and servers running Windows Server 2008 and higher.
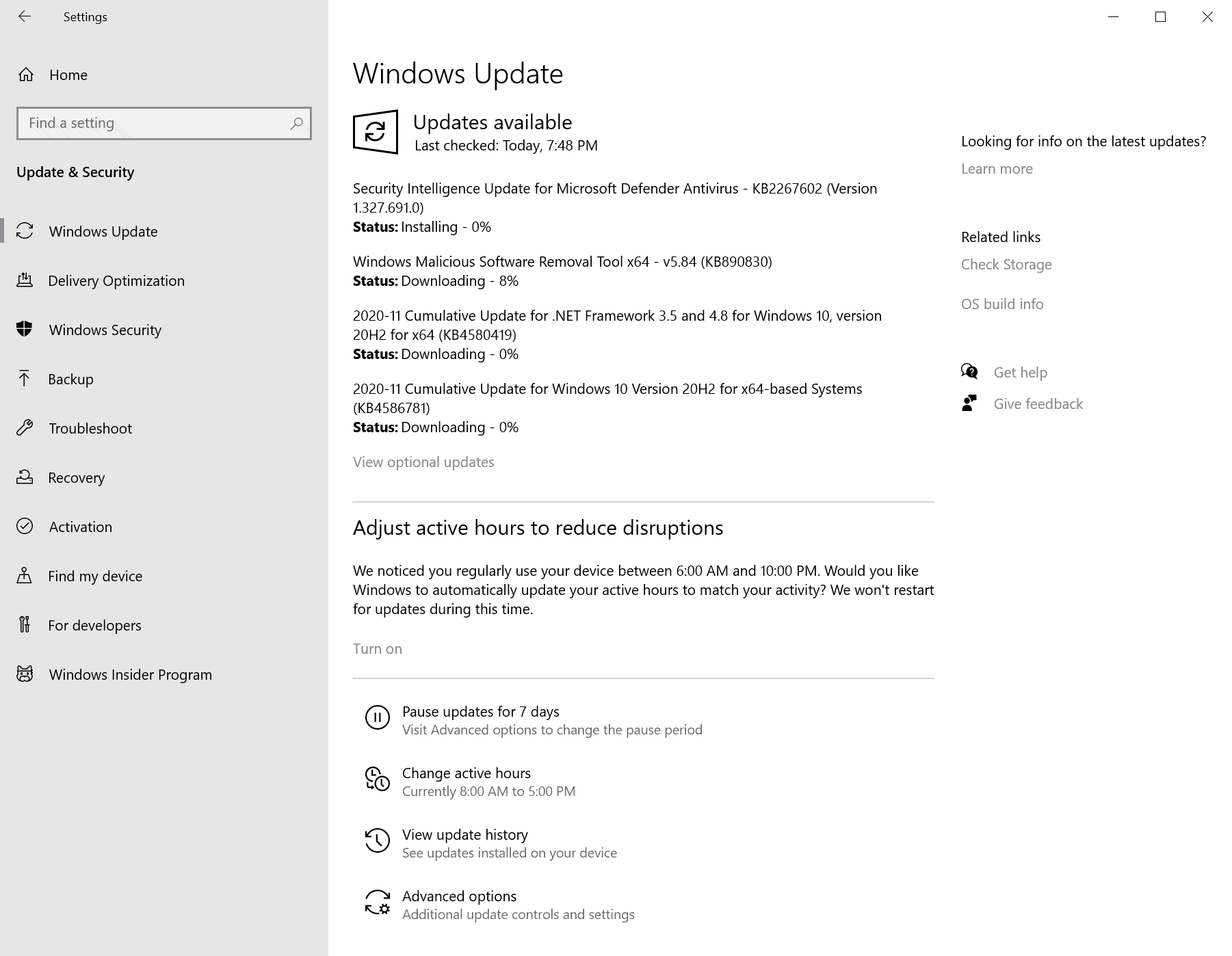
Security updates for all impacted Windows platforms are available on Microsoft's MSRC (Microsoft Security Response Center) portal.

Microsoft fixes Windows zero-day disclosed by Google last month
Microsoft has fixed today a Windows kernel zero-day vulnerability exploited in the wild as part of targeted attacks and publicly disclosed by Project Zero, Google's 0day bug-hunting team, last month.