Microsoft introduced a new range of devices called Secured-core PCs which come with built-in protection against firmware attacks that have been increasingly used by state-sponsored hacking groups.
The APT28 cyber-espionage group (also tracked as Sednit, Fancy Bear, Strontium, and Sofacy), for instance, used a
Unified Extensible Firmware Interface (UEFI) rootkit dubbed LoJax as part of its 2018 operations.
This gave the attackers persistence on the compromised computers not only against operating system reinstallation but also against attempts of replacing the hard drives on infected machines.
These devices are designed specifically for industries like financial services, government, and healthcare, and for workers that handle highly-sensitive IP, customer or personal data, including PII as these are higher-value targets for nation-state attackers," says Microsoft.
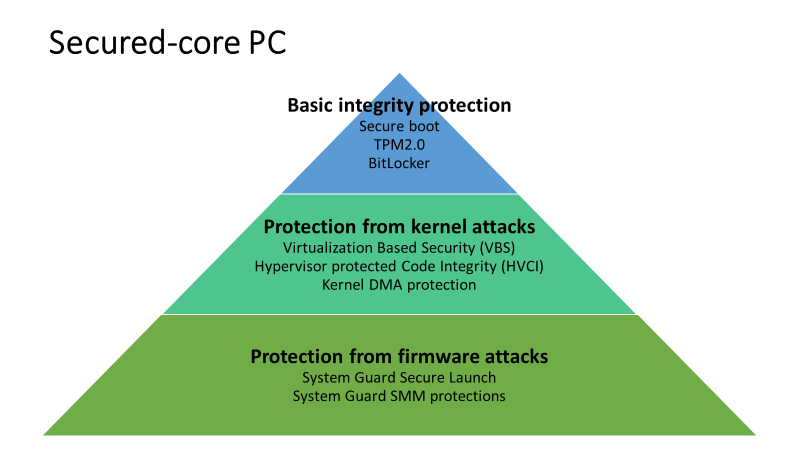
Layers of built-in protection
This new type of secured devices is designed to closely meet an array of software and hardware requirements that will "apply the security best practices of isolation and minimal trust to the firmware layer, or the device core, that underpins the Windows operating system."
Given the deep integration between the hardware, firmware, operating system, and identity features built-in, organized as layers designed to prevent attackers from successfully compromising the system, Secured-core PCs protect from increasing risks of targeted attacks and highly advanced threats out of the box.
"These devices, created in partnership with our OEM and silicon partners, meet a specific set of device requirements that apply the security best practices of isolation and minimal trust to the firmware layer, or the device core, that underpins the Windows operating system," Microsoft adds.
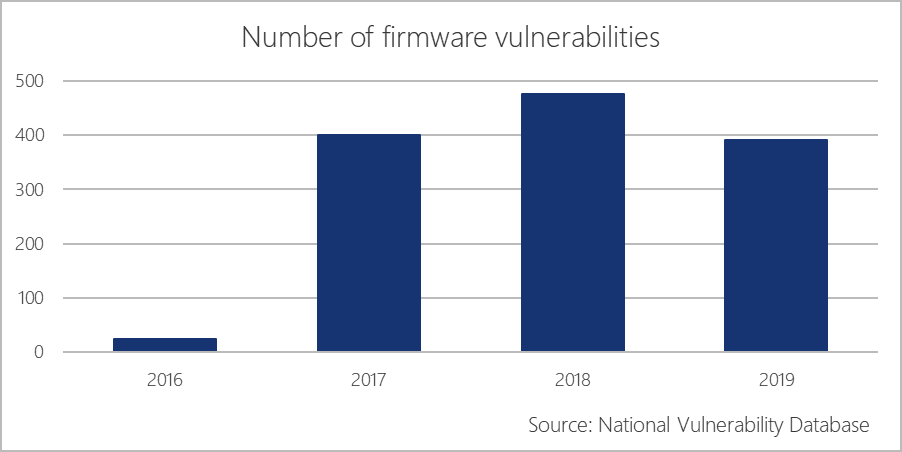
Secured-core PCs come as a solution for the number of increasing firmware vulnerabilities that attackers can exploit to bypass a Windows machine's Secure Boot and the lack of visibility at the firmware level present in today's endpoint security solutions.
To protect Secured-core PC users against it, Microsoft and its OEM partners introduced the following array of built-in requirements:
•
Loading Windows securely: Enabled with Hypervisor Enforced Integrity, a Secured-core PC only starts executables signed by known and approved authorities. Also, the hypervisor sets and enforces permissions to prevent malware from attempting to modify the memory and made executable
•
Firmware protection: System Guard Secure Launch uses the CPU to validate the device to boot securely, preventing advanced firmware attacks
•
Identity protection: Windows Hello allows you to sign-in without a password, Credential Guard leverages VBS to prevent identity attacks
•
Secure, hardware-isolated operating environment: Uses the Trusted Platform Module 2.0 and a modern CPU with dynamic root of trust measurement
(DRTM) to boot up your PC securely and minimizes firmware vulnerabilities
These provisions allow Secured-core PCs to boot securely, protect themselves from firmware vulnerabilities, shield their operating system from attacks, prevent unauthorized access, and secure their users' identity and domain credentials.
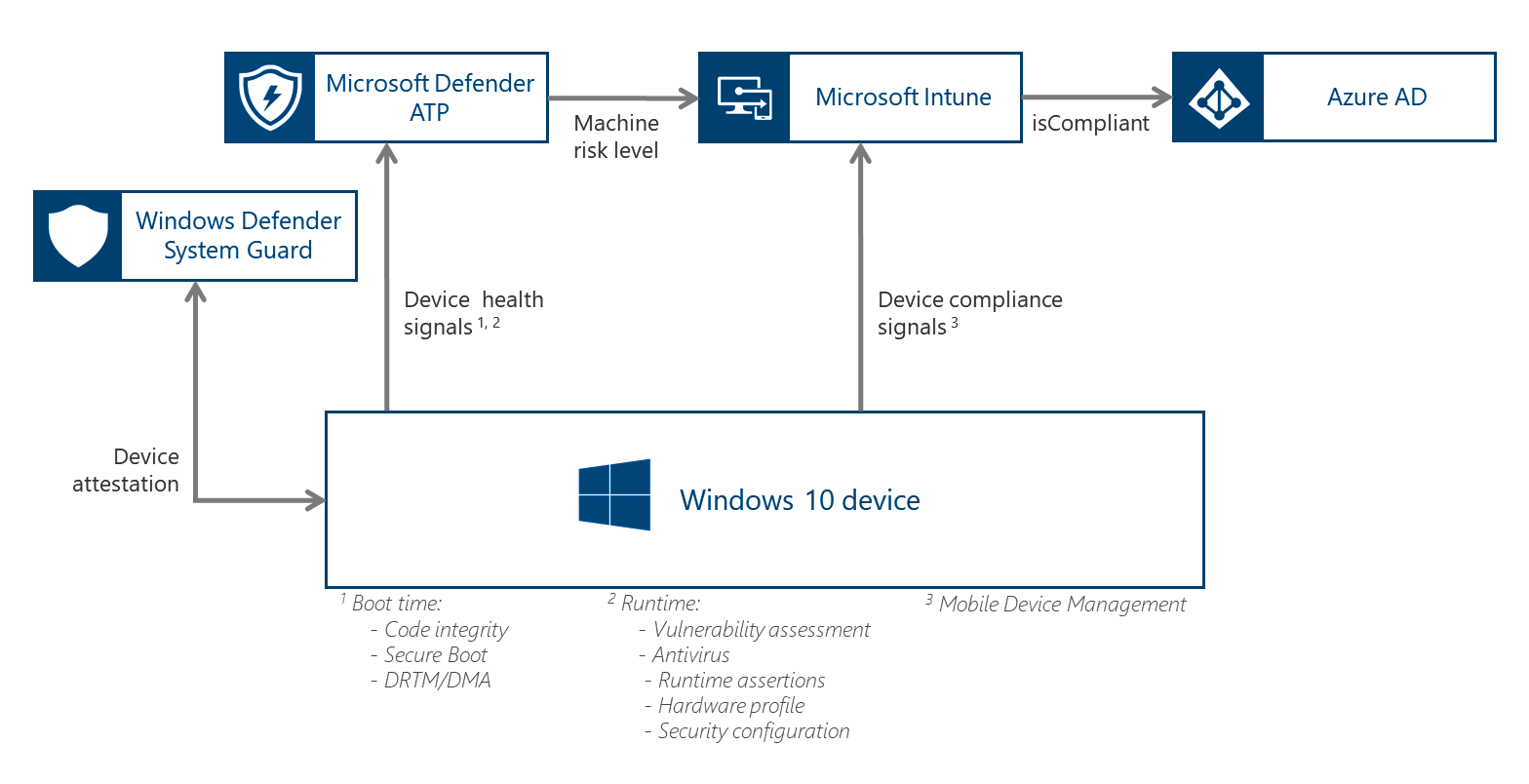
Windows Defender System Guard is a key requirement
"Using new hardware capabilities from AMD, Intel, and Qualcomm,
Windows Defender now implements System Guard Secure Launch as a key Secured-core PC device requirement to protect the boot process from firmware attacks," says Microsoft.
"System Guard uses the Dynamic Root of Trust for Measurement (DRTM) capabilities that are built into the latest silicon from AMD, Intel, and ARM to enable the system to leverage firmware to start the hardware and then shortly after re-initialize the system into a trusted state by using the OS boot loader and processor capabilities to send the system down a well-known and verifiable code path."
According to Microsoft's announcement, all Secured-core PCs will come with the necessary operating system and hardware support for Windows Defender System Guard's capabilities.
The rest of the link:
Microsoft introduced a new range of devices called Secured-core PCs which come with built-in protection against firmware attacks that have been increasingly used by state-sponsored hacking groups.

www.bleepingcomputer.com

 www.engadget.com
www.engadget.com