Gandalf_The_Grey
Level 76
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
- Apr 24, 2016
- 6,593
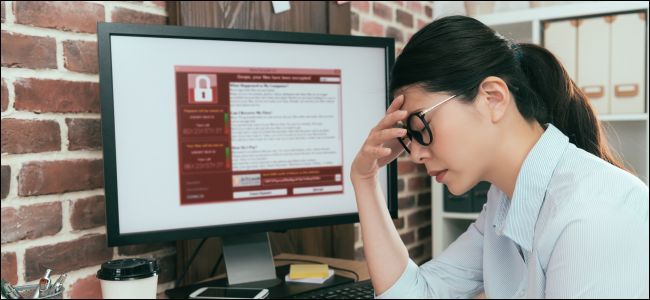
Maastricht University (UM) announced that almost all of its Windows systems have been encrypted by ransomware following a cyber-attack that took place on Monday, December 23.
UM is a university from the Netherlands with over 18,000 students, 4,400 employees, and 70,000 alumni, UM being placed in the top 500 universities in the world by five ranking tables in the last two years.
"Maastricht University (UM) has been hit by a serious cyber attack," the university announced on Christmas Eve, December 24.
"Almost all Windows systems have been affected and it is particularly difficult to use e-mail services. UM is currently working on a solution."
It is currently unknown if scientific data was also accessed or exfiltrated by the attackers during the attack, prior to the systems getting encrypted with the yet unnamed ransomware strain.
Read the rest of this story by Bleeping Computer here:

 www.bleepingcomputer.com
Website of the university:
www.bleepingcomputer.com
Website of the university:
 www.maastrichtuniversity.nl
www.maastrichtuniversity.nl
UM is a university from the Netherlands with over 18,000 students, 4,400 employees, and 70,000 alumni, UM being placed in the top 500 universities in the world by five ranking tables in the last two years.
"Maastricht University (UM) has been hit by a serious cyber attack," the university announced on Christmas Eve, December 24.
"Almost all Windows systems have been affected and it is particularly difficult to use e-mail services. UM is currently working on a solution."
It is currently unknown if scientific data was also accessed or exfiltrated by the attackers during the attack, prior to the systems getting encrypted with the yet unnamed ransomware strain.
Read the rest of this story by Bleeping Computer here:

Ransomware Hits Maastricht University, All Systems Taken Down
Maastricht University (UM) announced that almost all of its Windows systems have been encrypted by ransomware following a cyber-attack that took place on Monday, December 23.