Gandalf_The_Grey
Level 76
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
- Apr 24, 2016
- 6,586
Read the full report here:Q3 has seen a massive 82% rise in the number of new botnet command and controllers (C&Cs) identified by our research team. They have observed an explosion in the use of backdoor malware with nefarious operators hiding behind FastFlux. In turn, this has caused several new countries and service providers to be listed in our Top 20 charts. Welcome to the Spamhaus Botnet Threat Update Q3 2021.
FastFlux emerging again
After analyzing this quarter’s statistics, it is evident that FastFlux is once again rising in popularity. Here’s a quick FastFlux refresher, including a deeper dive into how cybercriminals use it to make their infrastructure resilient against takedowns.
What makes FastFl to cybercriminals?
All FastFlux networks that are currently in business can be rented as a service on the dark web. This makes life easy for botnet operators. All they have to do is register domains required for the botnet C&Cs and point them to the FastFlux operator’s service. FastFlux takes care of the rest, ensuring that the A records rapidly change.
Number of botnet C&Cs observed, Q3 2021
In Q3 2021, Spamhaus Malware Labs identified 2,656 botnet C&Cs compared to 1,462 in Q2 2021. This was an 82% increase quarter on quarter! The monthly average increased from 487 per month in Q2 to 885 botnet C&Cs per month in Q3.
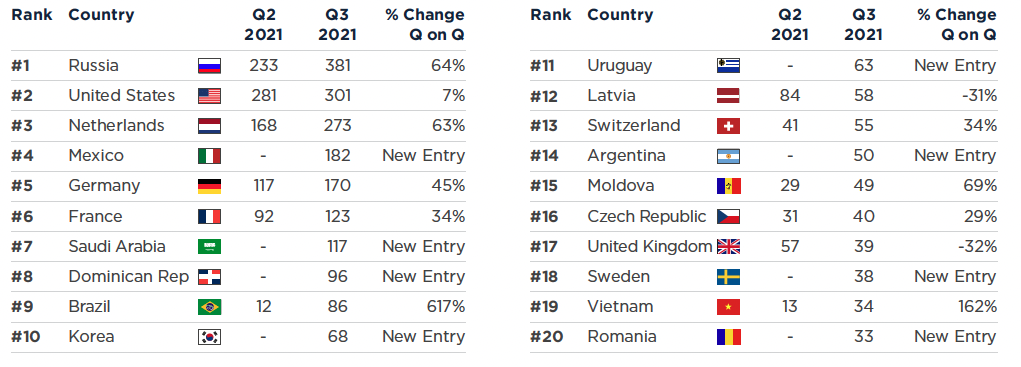
Geolocation of botnet C&Cs, Q3 2021
Given FastFlux’s influence over the past quarter, it isn’t surprising that there’s a clear pattern to the newcomers entering the chart for Q3 2021. Many of the countries joining the charts were responsible for hosting a large percentage of TeamBot, and FluBot botnet C&C servers - utilizing Fastflux - and fit the profile of countries with extensive internet coverage but less security-focused.
Significant increases in Russia
The number of botnet C&Cs located in Russia has dramatically risen. This is the second increase quarter on quarter that Russia has experienced:
Therefore, it comes as no surprise that in Q3 Russia overtook the United States for the #1 spot.
- Q1 to Q2 – 19% increase
- Q2 to Q3 – 64% increase
Continued increases across Europe
The trend that started in Q2 continued in Q3. Once again, there was an uptick in the number of botnet C&C servers hosted in various European countries, including the Netherlands (+63%), Germany (+45%), France (+34%), and Switzerland (+34%).
Botnet C&C | Botnet Threat Update Q3 2021 | Quarterly Report
Q3 has seen a massive 82% rise in the number of new botnet command and controllers (C&Cs) identified by our research team.
www.spamhaus.org
