- May 16, 2013
- 844
Telegram Messenger is a communication app that allows you to create encrypted chats and phone calls with other users over the Internet. This program describes itself as being a secure and private communication app, but a researcher has shown that in its default configuration it would allow a user's IP address to be leaked when making call.
This is caused by a default setting in Telegram, which causes voice calls to be made over P2P. When using P2P to initiate Telegram calls, though, the IP address of the person you are speaking with will appear in the Telegram console logs. Not all versions include a console log. For example, Windows does not display a console log in our tests, while the Linux version does.
The Telegram app does indicate that users can prevent their IP address from being revealed by changing the setting at Settings -> Private and Security -> Voice Calls -> Peer-To-Peer to Never or Nobody. Doing this will cause the user's calls to be routed through Telegram's servers, which would then hide the IP address, but at the cost of having a slight decrease in audio quality.
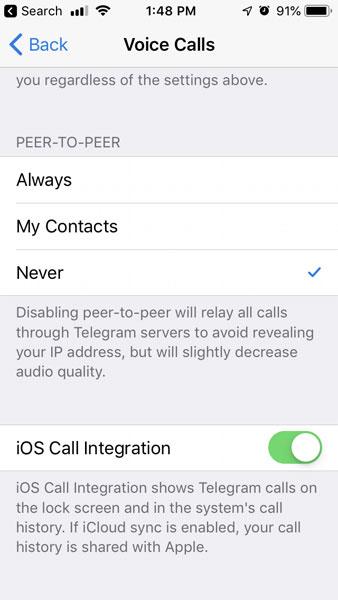
P2P Settings in Telegram for iOS
The problem is that while you are able to disable P2P calls and the associated IP address leak in iOS and Android, security researcher Dhiraj has discovered that the official Telegram for Desktop (tdesktop) and Telegram Messenger for Windows applications did not offer the ability to disable P2P calls.
This meant that these user's IP addresses would be leaked whenever they used Telegram to make a call. You can see an example of an IP address being leaked in the console for Telegram for Desktop on Ubuntu.
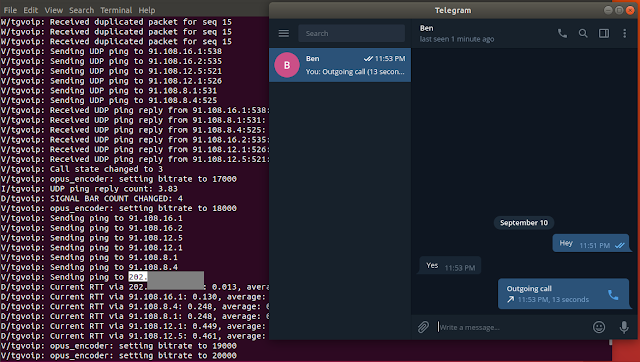
IP address leak in Telegram console log
In conversations with Dhiraj, the researcher shared a Proof of Concept video with BleepingComputer that illustrated how the IP addresses were leaked.
"If you see in my video PoC there are 3 IP's that leak: 1. Telegram server IP (That's Ok) 2. Your own IP (Even that's okay too) 3. End user IP (That's not okay)" Dhiraj explained.
This is caused by a default setting in Telegram, which causes voice calls to be made over P2P. When using P2P to initiate Telegram calls, though, the IP address of the person you are speaking with will appear in the Telegram console logs. Not all versions include a console log. For example, Windows does not display a console log in our tests, while the Linux version does.
The Telegram app does indicate that users can prevent their IP address from being revealed by changing the setting at Settings -> Private and Security -> Voice Calls -> Peer-To-Peer to Never or Nobody. Doing this will cause the user's calls to be routed through Telegram's servers, which would then hide the IP address, but at the cost of having a slight decrease in audio quality.
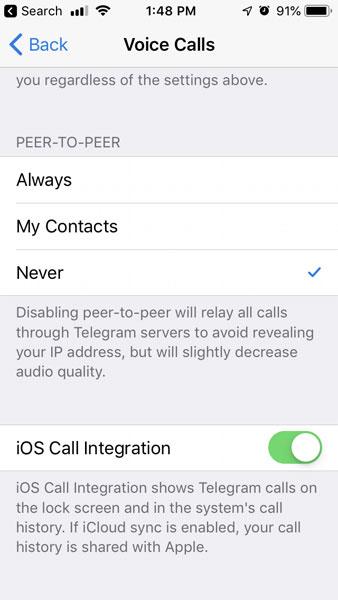
P2P Settings in Telegram for iOS
The problem is that while you are able to disable P2P calls and the associated IP address leak in iOS and Android, security researcher Dhiraj has discovered that the official Telegram for Desktop (tdesktop) and Telegram Messenger for Windows applications did not offer the ability to disable P2P calls.
This meant that these user's IP addresses would be leaked whenever they used Telegram to make a call. You can see an example of an IP address being leaked in the console for Telegram for Desktop on Ubuntu.
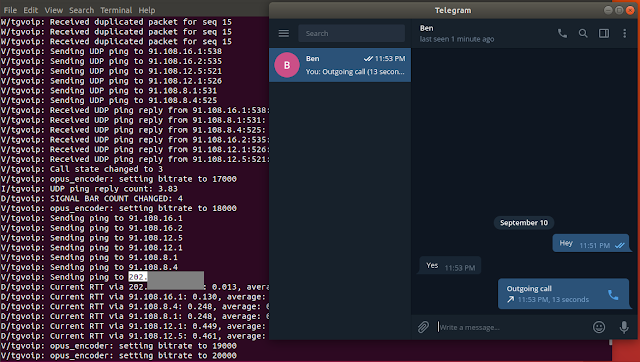
IP address leak in Telegram console log
In conversations with Dhiraj, the researcher shared a Proof of Concept video with BleepingComputer that illustrated how the IP addresses were leaked.
"If you see in my video PoC there are 3 IP's that leak: 1. Telegram server IP (That's Ok) 2. Your own IP (Even that's okay too) 3. End user IP (That's not okay)" Dhiraj explained.
