- Apr 25, 2013
- 5,355
The emails of a new TorrentLocker campaign use Domain-based Message Authentication, Reporting and Conformance (DMARC) to avoid detection and collect data.
Cyber criminals are continuously improving the technique to spread malicious code and avoid detection systems. Recently security experts at Trend Micro noticed an improvement in the evasion techniques implemented by malware authors to spread the ransomware TorrentLocker.
The bad actors spread the malware through spam emails containing a link to the malware, in the last months the spammed messages were crafted to evade spam filters. A new analysis conducted by Trend Micro revealed that criminals behind TorrentLocker ransomware are using emails that are designed to pass spam filters and also collect information. The new TorrentLocker campaign reached the peak in December 2014, it has had a temporary decline in January to raise again in February.
Basically, a spam email could be authorized by the Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). The SPF allows recipients to verify that an incoming message from a domain is being sent from a host included in a list of IP addresses, authorized by that domain’s owner, published in the domain’s DNS records.
The new wave of malicious messages spreading the TorrentLocker use Domain-based Message Authentication, Reporting and Conformance (DMARC), that implemented both SPF and DKIM, but that sends also reports to email senders.
Using the DMARC authentication, the spammers could collect precious information about the status of their spam campaign as explained by the experts at Trend Micro in a blog post.
The cyber criminals could analyze the information related to email that are detected by spam filters along with information present in the DMARC report, including ISP data, contact details, IP addresses, mailbox provider name and SPF and DKIM authentication results.
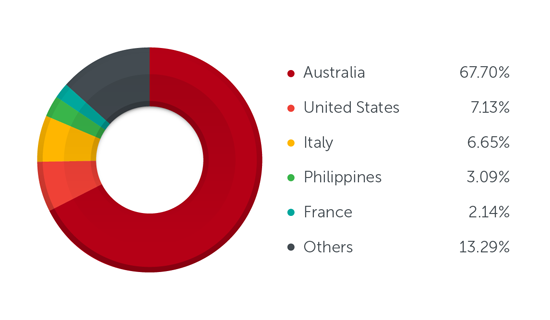
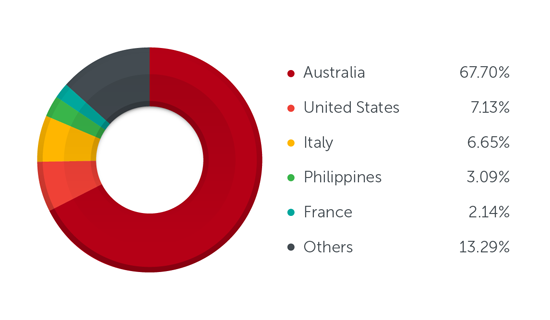
The new TorrentLocker campaign hit prevalently Australia, US and Italy
Be sharp and remain cautious when receive unsolicited emails, avoid clicking links or opening attachments.
Cyber criminals are continuously improving the technique to spread malicious code and avoid detection systems. Recently security experts at Trend Micro noticed an improvement in the evasion techniques implemented by malware authors to spread the ransomware TorrentLocker.
The bad actors spread the malware through spam emails containing a link to the malware, in the last months the spammed messages were crafted to evade spam filters. A new analysis conducted by Trend Micro revealed that criminals behind TorrentLocker ransomware are using emails that are designed to pass spam filters and also collect information. The new TorrentLocker campaign reached the peak in December 2014, it has had a temporary decline in January to raise again in February.
Basically, a spam email could be authorized by the Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM). The SPF allows recipients to verify that an incoming message from a domain is being sent from a host included in a list of IP addresses, authorized by that domain’s owner, published in the domain’s DNS records.
The new wave of malicious messages spreading the TorrentLocker use Domain-based Message Authentication, Reporting and Conformance (DMARC), that implemented both SPF and DKIM, but that sends also reports to email senders.
Using the DMARC authentication, the spammers could collect precious information about the status of their spam campaign as explained by the experts at Trend Micro in a blog post.
- Collect statistics about messages using their domain from DMARC receivers
- See how much of this traffic is passing/failing email authentication checks
- Request that messages using their domain that fail authentication be quarantined or rejected
- Receive data extracted from failed messages such as header information and URIs from the message body, if the receiver provides this service
The cyber criminals could analyze the information related to email that are detected by spam filters along with information present in the DMARC report, including ISP data, contact details, IP addresses, mailbox provider name and SPF and DKIM authentication results.
The new TorrentLocker campaign hit prevalently Australia, US and Italy
Be sharp and remain cautious when receive unsolicited emails, avoid clicking links or opening attachments.
