Gandalf_The_Grey
Level 76
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Well-known
- Apr 24, 2016
- 6,593
Read the full story here at How-To Geek:Back in the 1990s, many IBM PC-compatible machines included cylinder locks on their cases right next to the Turbo and Reset buttons. What did these locks do, and why were they there? Let’s find out!
The Land Before Passwords
In the early 1980s, IBM PC-compatible computers were largely single-task, single-user machines that ran MS-DOS, which didn’t include built-in password protection. Anyone who sat down in front of your PC could boot it up and access all your data.
Like today, PCs often ran server software or intensive tasks that could take a long time to complete. If you had to step away, you, of course, didn’t want someone to come along and press a key that interrupted the process, right? Today, you’d simply lock your PC with a password, but back then, that wasn’t an option.
This is where the keyboard lock (or “keylock,” as IBM called it) came in.
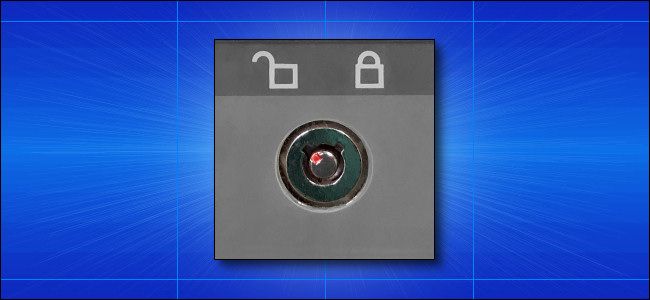
A keyboard lock on a 386-class generic PC from the early ’90s. Photo Benj Edwards
From about 1984 through the mid-to-late ’90s, many modular PC computer cases included a small tubular pin-tumbler lock on the front panel. It was usually located near the Turbo and Reset buttons.
When engaged (and if wired properly—PC builders sometimes skipped this step), these locks would prevent the keyboard from being used. You could type all you wanted, but the PC wouldn’t listen.
On some systems, this key switch also prevented a PC from booting when it was locked, resulting in a “302-System Unit Keylock is Locked” error.
The Origin of the Keyboard Lock
Ancestors of the keyboard lock can be traced back to IBM servers and mainframes, which predated the company’s PCs. A physical lock was a security measure to prevent unauthorized use.
For PC compatibles, the keyboard lock originated on the IBM Personal Computer AT, an expensive 286-based machine released in 1984. IBM initially aimed the $4,000-$6,700 machine (about $10,000-$16,800 today) at small business professionals, but its new features soon became the de facto standard for PC compatibles.
When IBM included a cylinder lock on the front of the PC AT, clone makers followed, introducing their own keyboard locks on AT-compatible machines. They added the lock both to include features that were on par with IBM’s and also to maintain compatibility with its systems. Compatibility was a key selling point for PC clones at that time.
For the IBM PC AT, the lock on the front of the case not only disabled the keyboard and interrupted the boot process, but it also moved an internal metal flange. This prevented the computer’s metal case from being opened.
In the many IBM PC clones that followed, only high-end machines tended to copy the case-locking feature. On most other PCs, the lock simply disabled the keyboard.
The Twilight of the Keyboard Lock
As cool as it was to have a PC case with a lock, few people actually used it. As the PC clone market increasingly became a cutthroat commodity business, with slimmer and slimmer margins, PC manufacturers began to trim away features. They especially targeted legacy features few people used, like the keyboard lock and Turbo button.
Keyboard locks really fell out of favor in the mid-’90s. Passwords arrived in modern multiuser, multitasking operating systems, like Windows NT, Novell NetWare, Linux, and (to some extent) Windows 95. The latter mostly used passwords to save personal preferences, though, rather than for security.
Who needs an expensive hardware lock when the software has one?
BIOS passwords also became a common feature for PC clones in the mid-’90s. There was now a software-based way to prevent people from booting a computer.
With operating system passwords and BIOS passwords widely available, the keyboard lock didn’t seem as useful anymore. It finally disappeared around the mid-to-late ’90s. The latest PC clone we’ve seen with a keyboard lock hails from 1996.
Why Did '90s PCs Have Keyhole Locks, and What Did They Do?
In the early 1990s, many PCs had a mysterious lock on their cases. What the heck was it for?

