A Google security researcher has found and helped patch a severe vulnerability in Keeper, a password manager application that Microsoft has been bundling with some Windows 10 distributions this year.
"I've heard of Keeper, I remember filing a bug
a while ago about how they were injecting privileged UI into pages,"
said Tavis Ormandy, the Google security researcher who discovered the recent vulnerability.
"I checked and, they're doing the same thing again with this version," the expert added, referring to the
Keeper app bundled with some Windows 10 versions.
"I think I'm being generous considering this a new issue that qualifies for a ninety day disclosure, as I literally just changed the selectors and the same attack works. Nevertheless, this is a complete compromise of Keeper security, allowing any website to steal any password," Ormandy added.
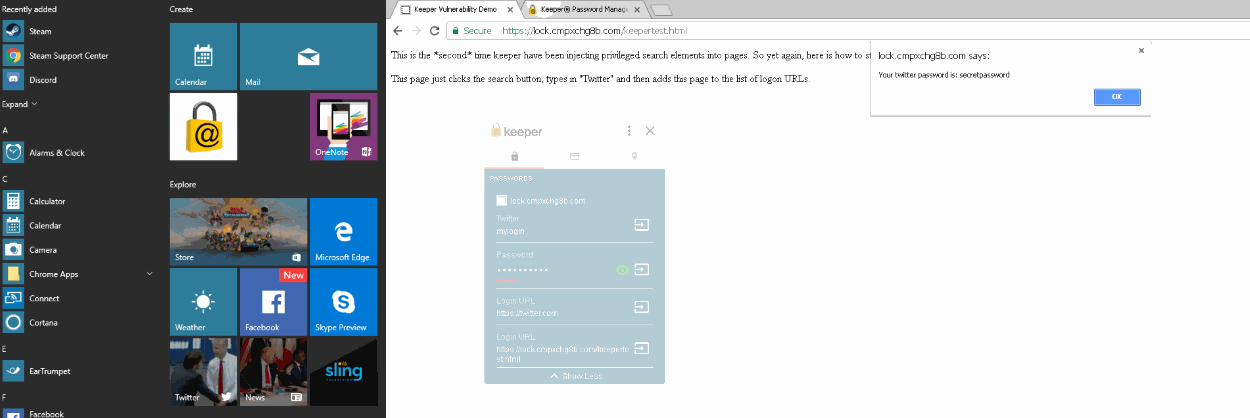
To prove his point, the expert also created a
demo page where Keeper users can see the vulnerability in action.