silversurfer
Level 85
Thread author
Verified
Honorary Member
Top Poster
Content Creator
Malware Hunter
Well-known
- Aug 17, 2014
- 10,151
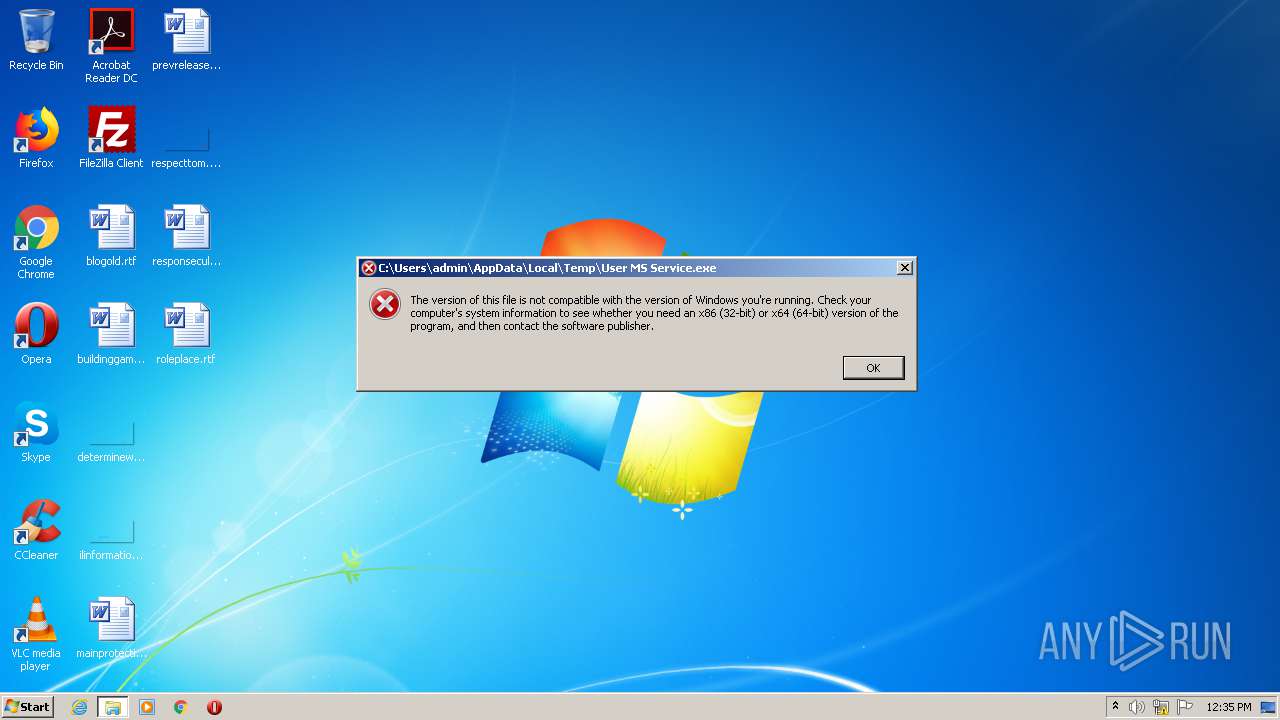
Read more: XDSpy cyber-espionage group operated discretely for nine yearsResearchers at ESET today published details about a threat actor that has been operating for at least nine years, yet their activity attracted almost no public attention.
Going largely unnoticed for this long is a rare occurrence these days as malicious campaigns from long-standing adversaries overlap at one point or give sufficient clues for researchers to determine that the same actor is behind them.
At the Virus Bulletin 2020 security conference today, ESET provided details about the victims and operations of a newly discovered advanced persistent threat (APT) named XDSpy, after the main malware downloader used in attacks.
ESET malware researchers Matthieu Faou and Francis Labelle say that the group has been running cyber-espionage campaigns since at least 2011.
XDSpy’s main interest is in the Eastern Europe and Balkans regions (Belarus, Moldova, Russia, Serbia, and Ukraine), targeting primarily government agencies (military, Ministries of Foreign Affairs), although private companies are also among its victims.