Vista Defender is a computer virus,which pretends to be a legitimate security program and claims that malware has been detected on your computer,however if you try to remove these infections,it will state that you need to buy this product before being able to do so.
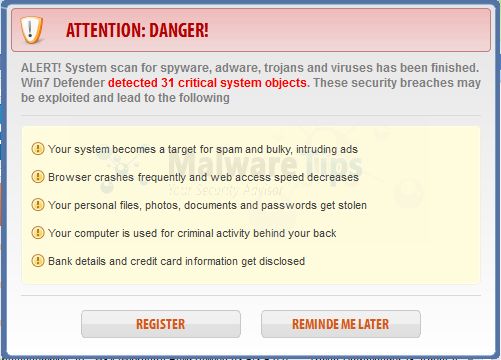
Apart from the bogus scan results,Vista Defender will display other fake security alerts that are designed to think that your data is at risk or that your computer is severely infected.These messages include:
System Security Alert
Vulnerabilities found
Background scan for security breaches was finished. Serious issues were detected. Safeguard your system against exploits, malware and viruses right now by activating Proactive Defense.
System Security Alert
Unknown program is scanning your system registry right now! Identity theft detected.
In reality, none of the reported issues are real, and are only used to scare you into buying Vista Defender and stealing your personal financial information.
As part of its self-defense mechanism,Vista Defender has disabled the Windows system utilities, including the Windows Task Manager and Registry Editor,and will block you from running certain programs that could lead to its removal.
Further more,this rogue antivirus has modified your Windows files associations and now,whenever you are trying to any programs that have a .exe extension ,Vista Defender it will display a bogus notification in which will report that the file is infected,in an attempt to scare you.The text of this alert is:
Vista Defender Firewall Alert
Firefox.exe is infected with Trojan-Clicker.Js.Agent.op. Private data can be stolen by third parties, including credit card details and passwords.
If your computer is infected with Vista Defender,then you are seeing this screens:
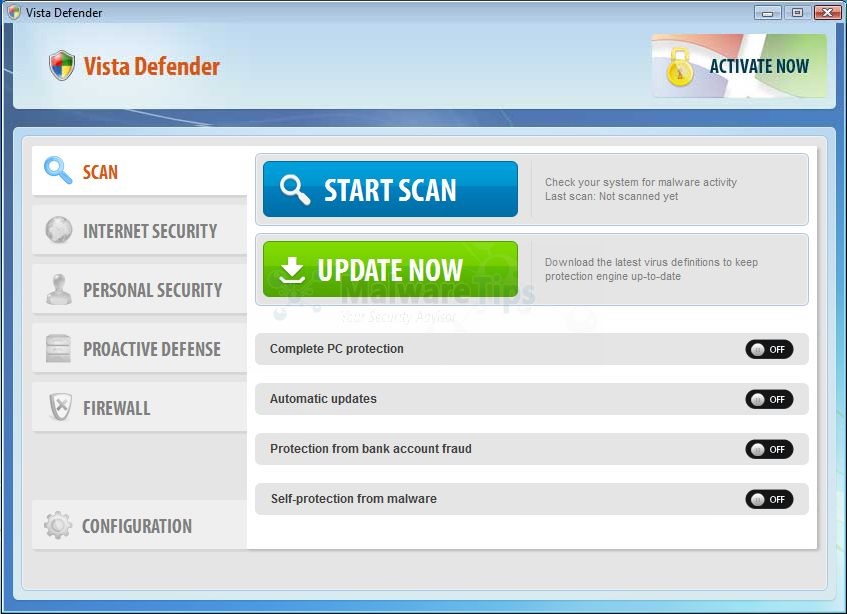
Vista Defender is a scam and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you buy this rogue security software as this could lead to identity theft,and if you have, you should contact your bank and dispute the charge stating that the program is a scam and a computer virus.
Vista Defender – Virus Removal Instructions
STEP 1 : Start your computer in Safe Mode with Networking
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
- Press and hold the F8 key as your computer restarts.Please keep in mind that you need to press the F8 key before the Windows start-up logo appears.
Note: With some computers, if you press and hold a key as the computer is booting you will get a stuck key message. If this occurs, instead of pressing and holding the “F8 key”, tap the “F8 key” continuously until you get the Advanced Boot Options screen. - On the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
![Safe Mode with Networking screen [Image: Safemode.jpg]](//malwaretips.com/images/removalguide/safemode.jpg)
STEP 2: Repair your Windows Registry from Vista Defender malicious changes.
Vista Defender has changed your Windows registry settings so that when you try to run a executable file,it will instead launch the infection rather than the desired program.
Some variants of this virus will not allow your to open your web browser,so you’ll need to download this registry fix on a clean computer and then transfer the program to the infected computer. You can transfer the files via a CD/DVD, external drive, or USB flash drive.
Alternatively,on the infected computer, right click on the Internet Explorer’s icon or any other browser’s icon, and select Run As or Run as Administrator.This should allow your browser to open where you can then download this registry fix from the below link and save it to a folder that your infected account can access.
- Download the registryfix.reg file to fix the malicious registry changes from Win 7 Defender.
REGISTRYFIX.REG DOWNLOAD LINK (This link will automatically download the registry fix called registryfix.reg) - Double-click on registryfix.reg file to run it. Click “Yes” for Registry Editor prompt window,then click OK.
![Remove Vista Defender (Removal Instructions) 2 [Image: fix registry]](//malwaretips.com/blogs/wp-content/uploads/2011/12/registry.png)
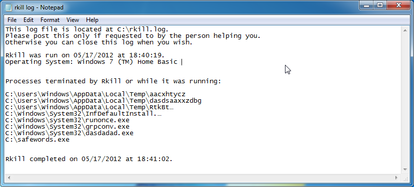
STEP 3: Run RKill to terminate known malware processes associated with Win 7 Defender.
RKill is a program that will attempt to terminate all malicious processes associated with Win 7 Defender,so that we will be able to perform the next step without being interrupted by this malicious software.
Some variants of this virus will not allow your to open your web browser,so you’ll need to download RKill on a clean computer and then transfer the program to the infected computer. You can transfer the files via a CD/DVD, external drive, or USB flash drive.
Alternatively,on the infected computer, right click on the Internet Explorer’s icon or any other browser’s icon, and select Run As or Run as Administrator.This should allow your browser to open where you can then download Rkill from the below link and save it to a folder that your infected account can access.
- While your computer is in Safe Mode with Networking ,please download the latest official version of RKill.Please note that we will use a renamed version of RKILL so that Vista Defender won’t block this utility from running.
RKILL DOWNLOAD LINK (This link will automatically download RKILL renamed as iExplore.exe) - Double-click on the iExplore.exe icon in order to automatically attempt to stop any processes associated with Win 7 Defender.
![RKILL ICON [Image: run-rkill-1.png]](//malwaretips.com/images/removalguide/rkill1.png)
- RKill will now start working in the background, please be patient while the program looks for various malware programs and tries to terminate them.
![RKILL Command prompt [Image: run-rkill-2.png]](//malwaretips.com/images/removalguide/rkill2.png)
IF you are having problems starting or running RKill, you can download any other renamed versions of RKill from here. - When Rkill has completed its task, it will generate a log. You can then proceed with the rest of the guide.
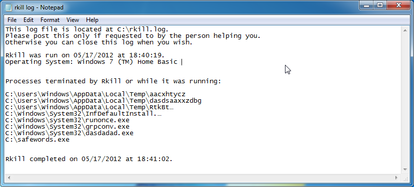
WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.
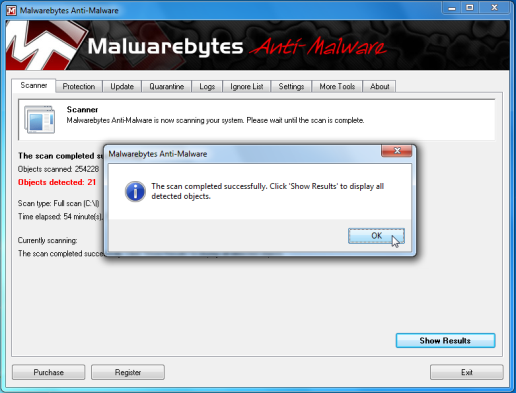
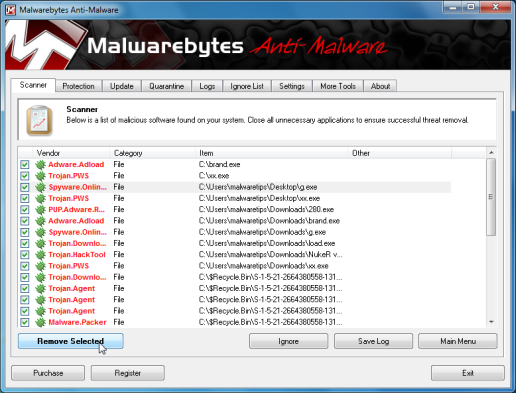
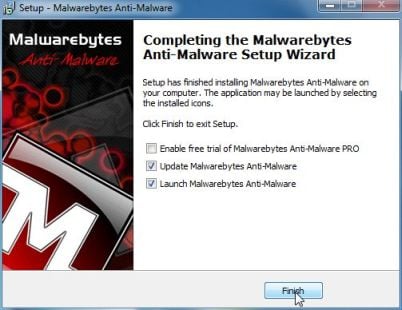
STEP 4: Remove Vista Defender malicious files with Malwarebytes Anti-Malware FREE
Malwarebytes Anti-Malware is a powerfull on-demand scanner which will remove Vista Defender malicious files from your computer.
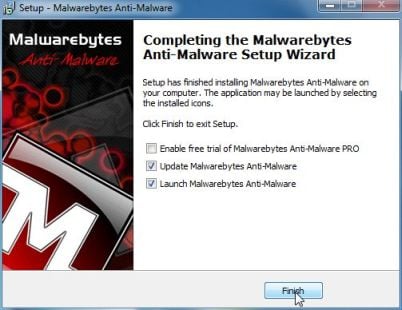
- You can download Malwarebytes Anti-Malware Free from the below link,then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
DO NOT make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked,then click on the Finish button.
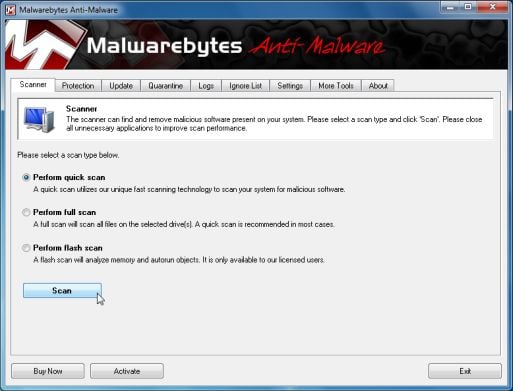
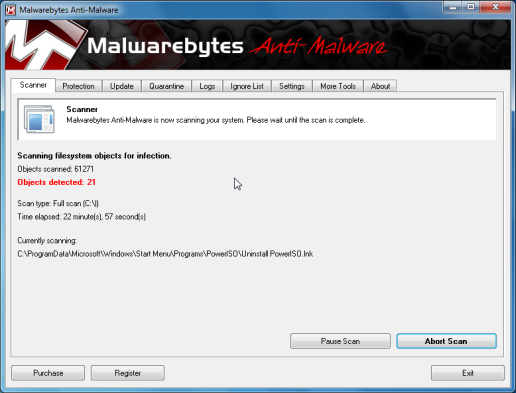
- On the Scanner tab,select Perform quick scan and then click on the Scan button to start scanning your computer.
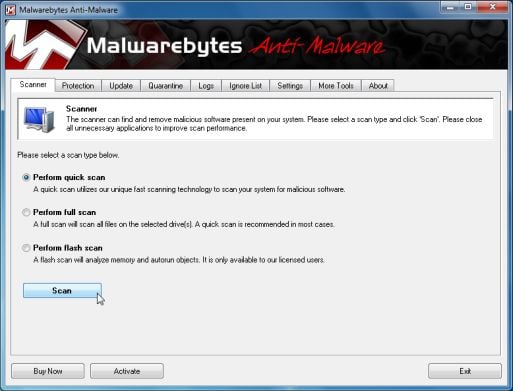
- Malwarebytes’ Anti-Malware will now start scanning your computer for Vista Defender malicious files as shown below.
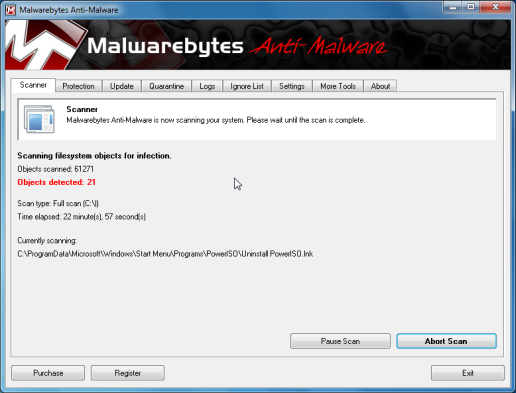
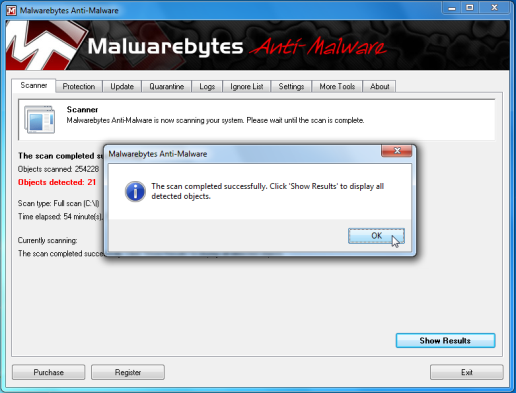
- When the Malwarebytes scan will be completed,click on Show Result.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
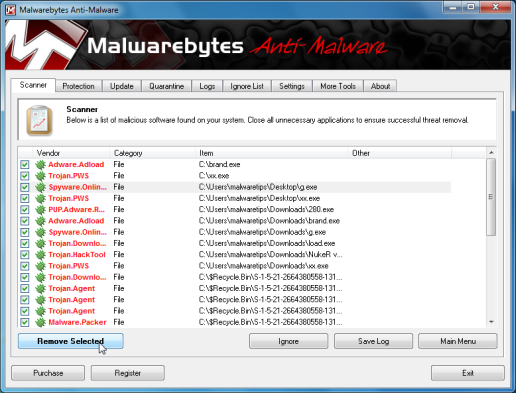
- After your computer will restart in Normal mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
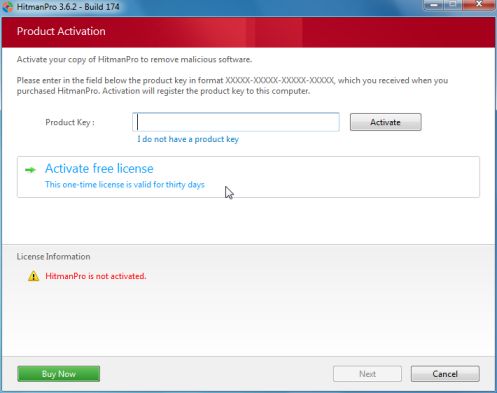
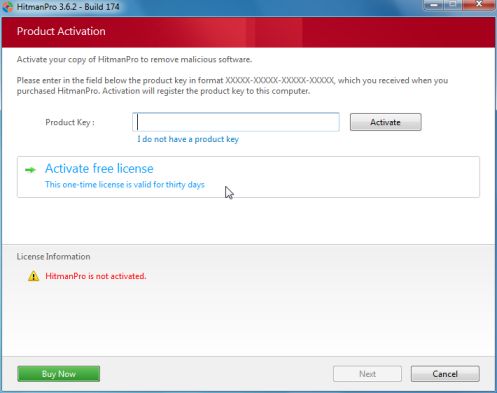
STEP 5: Remove Vista Defender rootkit with HitmanPro
In some cases,Vista Defender will also install a rootkit on victims computer.To remove this rootkit we will use HitmanPro.
- Download HitmanPro from the below link,then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.


- HitmanPro will start scanning your computer for Vista Defender malicious files as seen in the image below.

- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.

- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
That’s it, Vista Defender should be completely removed from your computer!
We strongly recommend that you build up your malware defenses by starting a new thread in Security Configuration Wizard forum and keep installed on your machine all the on-demand scanners that we’ve used in this article to perform regular scans with them.



![Safe Mode with Networking screen [Image: Safemode.jpg]](http://malwaretips.com/images/removalguide/safemode.jpg)
![Remove Vista Defender (Removal Instructions) 2 [Image: fix registry]](http://malwaretips.com/blogs/wp-content/uploads/2011/12/registry.png)
![RKILL ICON [Image: run-rkill-1.png]](http://malwaretips.com/images/removalguide/rkill1.png)
![RKILL Command prompt [Image: run-rkill-2.png]](http://malwaretips.com/images/removalguide/rkill2.png)