If your computer is locked, and you are seeing a “El ordenador se ha bloqueado y todos sus datos se cifran” notification from FBI Cybercrime Division , then your computer is infected with a piece of malware known as Trojan Reveton.
The “El ordenador se ha bloqueado y todos sus datos se cifran” virus is distributed through several means. Malicious websites, or legitimate websites that have been compromised, may drop this trojan onto a compromised computer. This drive-by-download often happens surreptitiously. Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software.
The “El ordenador se ha bloqueado y todos sus datos se cifran” virus is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
Once installed on your computer, the “El ordenador se ha bloqueado y todos sus datos se cifran” MoneyPak virus will display a bogus notification that pretends to be from the FBI Cybercrime Division, and states that your computer has been blocked due to it being involved with the distribution of pornographic material, SPAM and copyrighted content.
The “El ordenador se ha bloqueado y todos sus datos se cifran” virus will lock you out of your computer and applications, so whenever you’ll try to log on into your Windows operating system or Safe Mode with Networking, it will display instead a lock screen asking you to pay a non-existing fine of 200 Euro in the form of a MoneyPak code.
Furthermore, to make this alert seem more authentic, this virus also has the ability to access your installed webcam, so that the bogus “El ordenador se ha bloqueado y todos sus datos se cifran” notification shows what is happening in the room.
The “El ordenador se ha bloqueado y todos sus datos se cifran” virus locks the computer and, depending on the user’s current location, displays a localized webpage that covers the entire desktop of the infected computer and demands payment for the supposed possession of illicit material.
Cyber criminals often updated the design of this lock screen, however you should always keep in mind that FBI Cybercrime Division will never lock down your computer or monitor your online activities.
The message displayed by the threat can be localized depending on the user’s location, with text written in the appropriate language.
FBI Cybercrime Division
ADVERTENCIA! El ordenador se ha bloqueado y todos sus datos se cifran!
Su computadora ha sido bloqueado y todos sus archivos estaban cifrados. Motivo: violación de la ley. Las posibles violaciones se describen a continuación: Titulo 17 &; DERECHOS DE AUTOR, Capitulo 10, Subcapitulo B ,CONTROLES DE COPIA
(a) Prohibición de Importación. Fabricación y Distribución – Ninguna persona podrá importar, fabricar o distribuir cualquier dispositivo de grabación digital de audio o interfaz de audio digital. dispositivo que no se ajusta a-(1) Sistema de gestión de copia en serie, (2) un sistema que tiene las mismas características funcionales que el sistema de gestión de copia en serie y exige que los derechos de autor y la información de estado de generación de forma precisa enviada, recibida, y actuar en consecuencia entre los dispositivos que utilizan el método del sistema de regulación de copia en serie y los dispositivos que utilizan el Sistema de gestión de copia en serie, o (3) cualquier otro sistema certificado por el Secretario de Comercio que prohibe la copia no autorizada de serie. Titulo 18 DELITOS Y PROCEDIMIENTO PENAL ‘Mulo 18 Parte Ir Capitulo 117 r§2427 La inclusión de los delitos relacionados con la pornografía infantil en la definición de la actividad sexual por la que puede ser cualquier persona acusada de un delito penal Titulo > 18 i Parte Ir Capítulo 110 > §2258C La inclusión de los delitos relacionados con la pornografía infantil en la definición de la actividad sexual por la que puede ser cualquier persona acusada de un delito penal (a) Elementos—. (1) En general — El Centro Nacional para Niños Desaparecidos y Explotados puede proporcionar elementos relacionados con cualquier imagen de pornografía infantil aparente de un niño identificado a un proveedor de servicios de comunicación electrónica o de un proveedor de servicios de computación remota para el único y el propósito exclusivo de permitir que el proveedor de servicios de comunicación electrónica o el proveedor de servicios informáticos a distancia para detenerlo transmisión de otro tipo de imágenes. (2)— Inclusiones. Los elementos autorizados en el párrafo (1) puede incluir valores de has u otros identificadores únicos asociados con una imagen específica, ubicación de Internet de imágenes, y otros elementos tecnológicos queso pueden utilizar para identificar y detenerlo transmisión de pornografía infantil. (3) Exclusión —. Los elementos autorizados en virtud del párrafo (1) no puede incluir las imágenes reales. (b) El uso por las proveedores de servicios de comunicaciones electrónicas y los proveedores de servicios remotos Informática —. Cualquier proveedor de servicios de comunicación electrónica o el proveedor de servicio de computación remoto que recibe los elementos relativas a cualquier imagen de pornografía infantil aparente de un niño identificado por el Centro Nacional para Niños Desaparecidos y Explotados en esta sección puede utilizar dicha información únicamente para los fines descritas en esta sección, siempre que dicho uso no liberará a ese proveedor de servicios de comunicación electrónica o el proveedor de servicios informáticos a distancia de sus obligaciones de presentar informes bajo la sección 2258A.
(c) Limitaciones — Nada en las subvenciones. [1] (a) o (b) requiere que los proveedores de servicios de comunicaciones electrónicas o remotas proveedores de servicios informáticos que reciben los elementos relativos a cualquier imagen de pornografía infantil aparente de un niño identificado por el Centro Nacional para Menores Desaparecidos y Explotados Los niños a utilizar los elementos para detener la transmisión ulterior de las imágenes. (d) Provisión de elementos a la policía — El Centro Nacional para Niños Desaparecidos y Explotados pondrá a disposición Federal. Estatal y las autoridades locales involucradas en la investigación de delitos de pornografía infantil elementos, incluidos los valores hash, en relación con cualquier niño aparente imagen de pornografía a un niño identificado informó el Centro Nacional para Menores Desaparecidos y Explotado& (e) El uso por aplicación de la ley — Cualquier federal, estatal o agencia de policía local que recibe los elementos relativos a cualquier imagen de pornografía infantil aparente de un niño identificado por el Centro Nacional para Menores Desaparecidos y Explotados en virtud del articulo [1] (d) Puede utilizar estos elementos sólo en el ejercicio de las funciones oficiales de esa agencia para investigar los delitos de pornografía infantil. Titulo 18 r Parte Ir Capitulo 110 r § 2252A § 2252A – Ciertas actividades relacionadas con el material que constituya o contenga pornografía infantil Titulo 26 r Subtítulo F » Capítulo 78, Subcapitulo A, §7612 Procedimientos especiales para las citaciones para el software de la computadora Para desbloquear el ordenador, debe pagar una multa dentro de 24 horas y el código de cupón para una entrada siguiente formulario. Tendrá un máximo de 24 horas para comprobar el código de cupón y descifrar los datos.
The “El ordenador se ha bloqueado y todos sus datos se cifran” lock screen is a scam, and you should ignore any alerts that this malicious software might generate.
Under no circumstance should you send any Ukash code to these cyber criminals, and if you have, you can should request a refund, stating that you are the victim of a computer virus and scam.
“El ordenador se ha bloqueado y todos sus datos se cifran” lock screen – Virus Removal Guide
STEP 1: Remove “El ordenador se ha bloqueado y todos sus datos se cifran” lock screen from your computer
“El ordenador se ha bloqueado y todos sus datos se cifran” virus has modified your Windows registry and added its malicious files to run at start-up, so whenever you’re trying to boot your computer it will launch instead its bogus notification.To remove these malicious changes, we can use any of the below methods :
Method 1: Start your computer in Safe Mode with Networking and scan for malware
Some variants of “El ordenador se ha bloqueado y todos sus datos se cifran” virus will allow the users to start the infected computer in Safe Mode with Networking without displaying the bogus lock screen. In this first method, we will try to start the computer in Safe Mode with Networking and then scan for malware to remove the malicious files.
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
- Press and hold the F8 key as your computer restarts.Please keep in mind that you need to press the F8 key before the Windows start-up logo appears.
Note: With some computers, if you press and hold a key as the computer is booting you will get a stuck key message. If this occurs, instead of pressing and holding the “F8 key”, tap the “F8 key” continuously until you get the Advanced Boot Options screen. - On the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
- If your computer has started in Safe Mode with Networking, you’ll need to perform a system scan (as seen on STEP 2) with Malwarebytes Anti-Malware and HitmanPro to remove the malicious files from your machine.
IF the “El ordenador se ha bloqueado y todos sus datos se cifran” virus didn’t allow you to start the computer in Safe Mode with Networking,you’ll need to follow Method 2 to get rid of its lock screen.
Method 2: Restore Windows to a previous state using System Restore
System Restore can return your computer system files and programs to a time when everything was working fine, so we will try to use this Windows feature to get rid of “El ordenador se ha bloqueado y todos sus datos se cifran” lock screen.
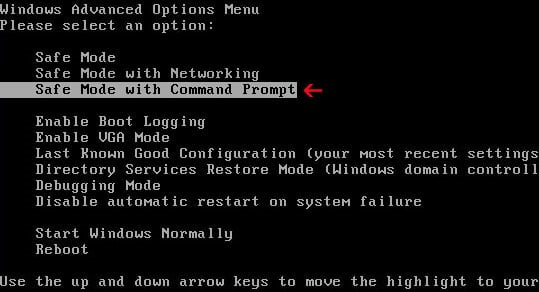
- Restart your computer, and then press and hold F8 during the initial startup to start your computer in safe mode with a Command prompt.
Note: With some computers, if you press and hold a key as the computer is booting you will get a stuck key message. If this occurs, instead of pressing and holding the “F8 key”, tap the “F8 key” continuously until you get the Advanced Boot Options screen. - Use the arrow keys to select the Safe mode with a Command prompt option.
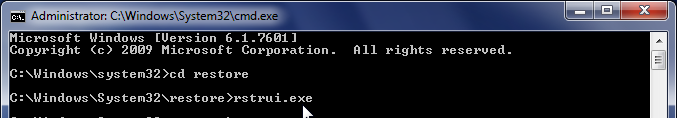
- At the command prompt, type cd restore, and then press ENTER.
Next,we will type rstrui.exe , and then press ENTER.Alternatively, if you are using Windows Vista, 7 and 8, you can just type : C:\windows\system32\rstrui.exe , and press ENTER.
If you are using Windows XP, you will need to type C:\windows\system32\restore\rstrui.exe, and then press ENTER.
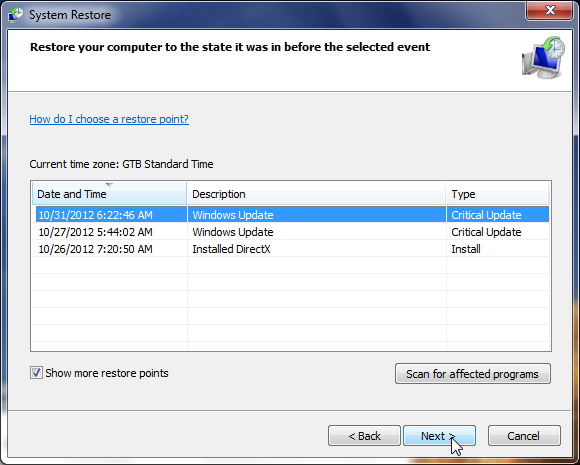
- The System Restore utility will start, and you’ll need to select a restore point previous to this infection.
- After System Restore has completed its task, you should be able to boot in Windows normal mode, and perform a system scan (as seen on STEP 2) with Malwarebytes Anti-Malware and HitmanPro to remove the malicious files from your machine.
IF the “El ordenador se ha bloqueado y todos sus datos se cifran” virus didn’t allow you to restore your computer to a previous point, you’ll need to follow Method 3 to get rid of its screen lock.
Method 3: Remove “El ordenador se ha bloqueado y todos sus datos se cifran” virus with HitmanPro Kickstart
IF you couldn’t boot into Safe Mode with Command Prompt or didn’t have a System Restore point on your machine, we can use HitmanPro Kickstart to bypass this infection, and access your computer to scan it for malware.
- We will need to create a HitmanPro Kickstart USB flash drive,so while you are using a “clean” (non-infected) computer, download HitmanPro from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a download page in a new window from where you can download HitmanPro) - Insert your USB flash drive into your computer and follow the instructions from the below video:
- After you have create the HitmanPro Kickstart USB flash drive, you can insert this USB drive into the infected machine and start your computer.
- Once the computer starts, repeatedly tap the F11 key (on some machines its F10 or F2),which should bring up the Boot Menu, from there you can select to boot from your USB.
Next,you’ll need to perform a system scan with HitmanPro as see in the below video:
- After HitmanPro Kickstart has completed its task,you should be able to boot in Windows normal mode,from there you’ll need to perform a system scan (as seen on STEP 2) with Malwarebytes Anti-Malware and HitmanPro to remove the malicious files from your machine.
STEP 2: Remove “El ordenador se ha bloqueado y todos sus datos se cifran” malicious files from your computer
Run a computer scan with Malwarebytes Anti-Malware Free
- You can download Malwarebytes Anti-Malware Free from the below link,then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
DO NOT make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked,then click on the Finish button.
- On the Scanner tab,select Perform quick scan and then click on the Scan button to start scanning your computer.
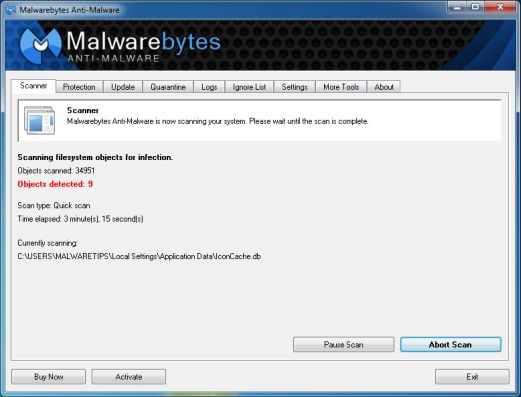
- Malwarebytes’ Anti-Malware will now start scanning your computer for “El ordenador se ha bloqueado y todos sus datos se cifran” virus as shown below.
- When the Malwarebytes scan will be completed,click on Show Result.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
- After your computer will restart in Normal mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
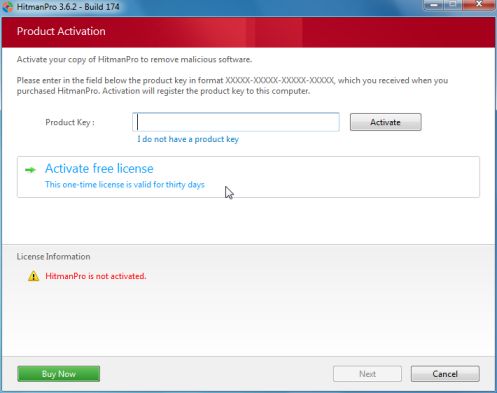
Run a computer scan with HitmanPro
- Download HitmanPro from the below link,then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for “El ordenador se ha bloqueado y todos sus datos se cifran” malicious files as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove these malicious files.
- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.

![Remove "El ordenador se ha bloqueado y todos sus datos se cifran" virus 1 [Image: Safe Mode with Networking]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/safemode.jpg)
![Malwarebytes Anti-Malware final installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)