A common tech support scam is circulating fake pop-up alerts about supposed “Pornographic Spyware” detections in order to trick users into calling fraudulent phone numbers. The pop-ups pretend to be urgent security warnings from Microsoft about inappropriate content resulting in malware infections.
This comprehensive guide will dive into how this “Pornographic Spyware Alert” scam works, examples of the deceptive pop-ups, and most importantly, tips to help you avoid becoming victimized by this cyber threat. Arm yourself with knowledge and protect your devices.
Overview of the Fake Pornographic Spyware Alert Scam
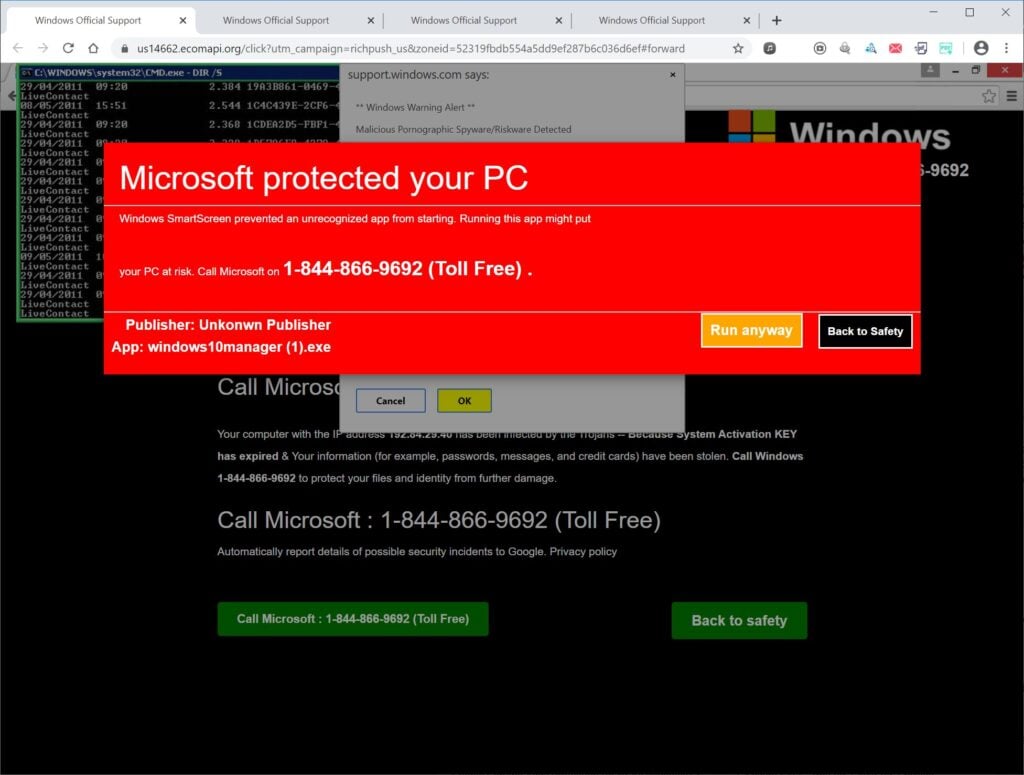
The Pornographic Spyware Alert scam starts by displaying fake pop-up warnings pretending to be from Microsoft, accusing the user of accessing illicit adult content leading to pornography malware infections.
The pop-ups claim the user’s personal data is at risk and that Microsoft Support must be contacted immediately via a highlighted phone number to remove the pornographic spyware threat.
However, the pop-ups are completely fabricated and the numbers actually route to overseas cybercriminal call centers.
Once users call the number, scammers trick victims into providing remote access to their computers. This grants the criminals ability to covertly steal personal information, install viruses, encrypt files for ransom, or fraudulently charge for bogus tech support services.
This is simply a common tech support scam variation exploiting fear and urgency around inappropriate content and data privacy. The fake spyware alerts aim to pressure users into urgently calling the number without critical evaluation. But the pop-ups have nothing to do with real Microsoft alerts and are only aimed at gaining remote system access.
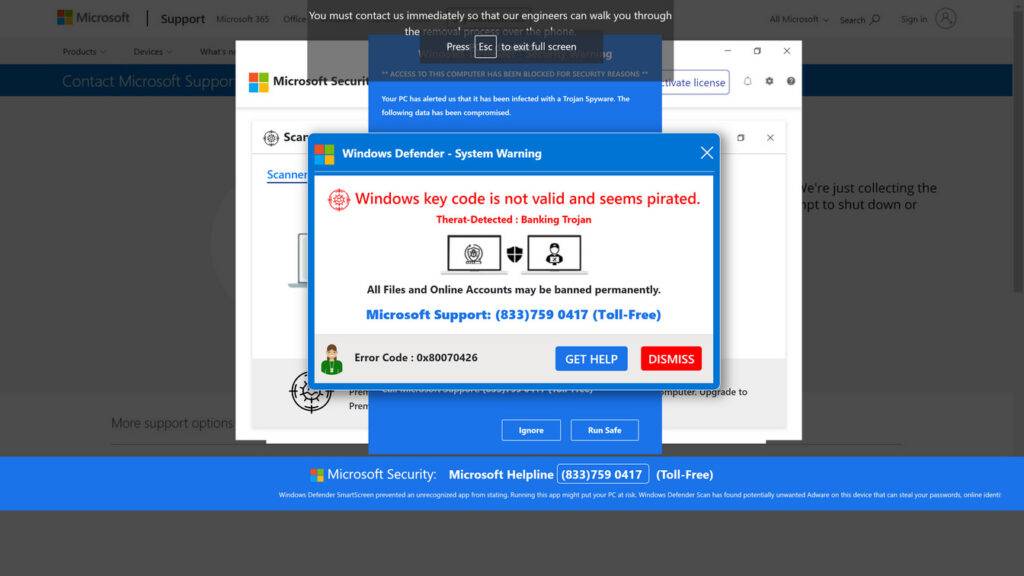
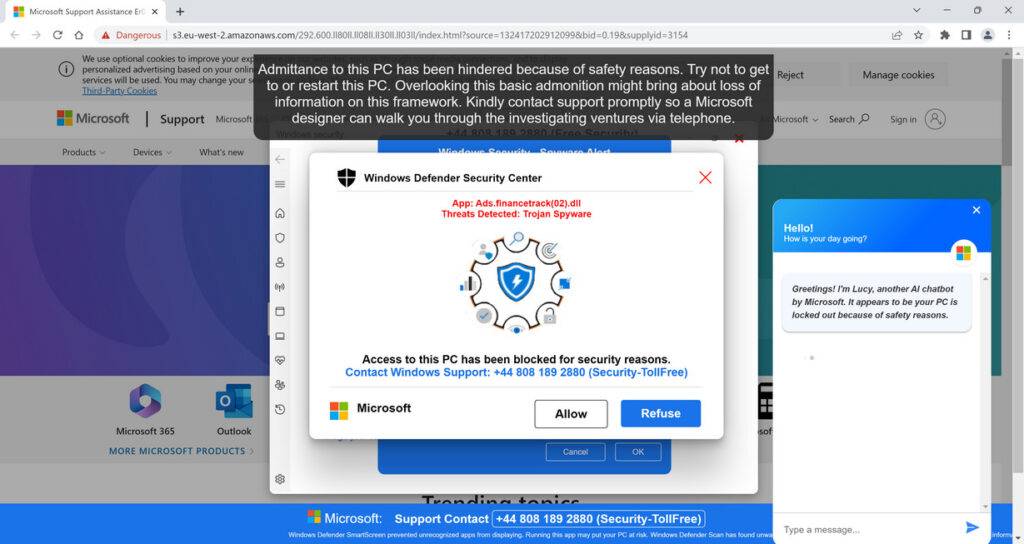
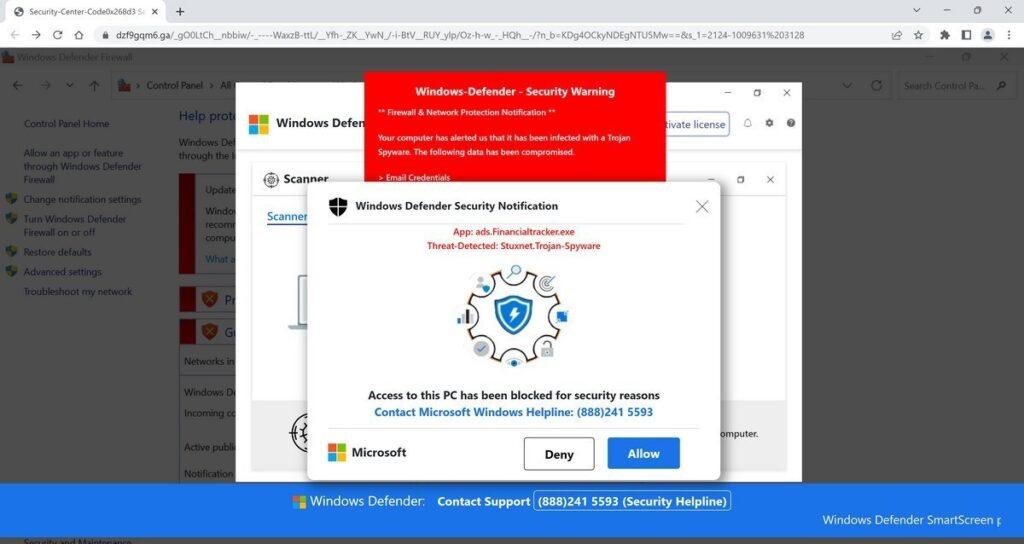
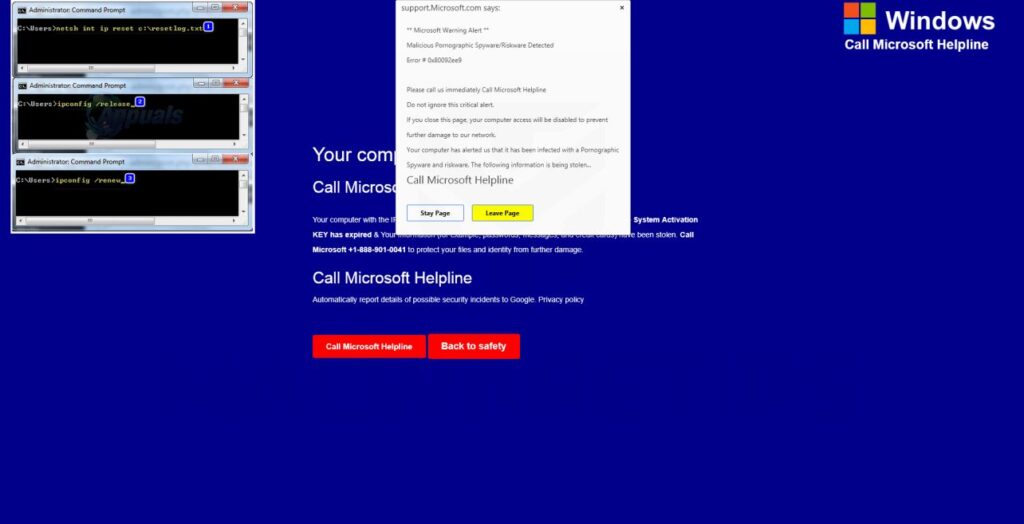
Examples of the Fake Pornographic Spyware Alerts
Here are some examples of the fraudulent Pornographic Spyware Alert pop-up content:
- “Microsoft Alert – Pornographic spyware detected resulting in identity theft! Call 888-123-4567 immediately to remove viruses and protect your personal data.”
- “URGENT Warning from Microsoft – Pornographic malware has been downloading explicit images and videos! Contact 833-555-1212 immediately to deactivate spyware before more content is accessed.”
- “Microsoft Firewall Alert – Pornographic viruses detected from visiting illicit adult websites! Call 844-777-8888 now to speak with security experts to remove malware and secure your data.”
- “Pornographic Spyware Alert – Your personal data is at risk from inappropriate content malware. Call 833-222-2444 immediately to prevent identity theft and financial loss!”
As you can see, threats about inappropriate content, malware, and data privacy risks aim to overwhelm critical thinking and pressure urgent calling of the highlighted number.
How the Pornographic Spyware Alert Scam Works
Cybercriminals are using devious psychological tactics to perpetrate this scam. Here’s an in-depth look at how it typically operates:
Step 1: Victim Lands on a Malicious Website
It starts with the user visiting a compromised website harboring redirects to the fake pop-ups. Dangerous sites include:
- Adult websites and pornography
- Torrent platforms with pirated videos and software
- Offshore gambling sites
- Hacker tool databases
These malicious sites trigger redirects to the scam pop-ups.
Step 2: The Fake Alert Appears
Once redirected, the fraudulent pop-up appears with the fake warnings about pornographic spyware threats and personal data risks.
The pop-ups use Microsoft logos and imagery to appear legitimate.
Step 3: User Calls the Phone Number
Alarmed about inappropriate content malware and data theft, the user calls the tech support number in the pop-up for help.
But in reality, the number routes internationally to a fraudulent call center completely unaffiliated with Microsoft.
Step 4: Scammer “Confirms” the Pornography Spyware
The overseas scammer claims specialized software detected illegal pornographic activity resulting in spyware installation compromising personal data.
The scammer insists remote access is required to “locate the viruses” and remove the inappropriate content properly.
Step 5: Remote Access Software is Installed
Following the scammer’s instructions, the user installs remote access software like AnyDesk and provides the scammer an access code granting full control.
Step 6: Scammer Steals Data and Money
With remote access, the scammer can now:
- Install additional malware, viruses, ransomware and keyloggers
- Access and steal personal documents, images, videos and account info
- Take over financial accounts and make unauthorized transactions
- Encrypt files on the computer and hold them ransom
- Force victims to purchase bogus anti-virus software and fake cleanings
The pop-ups are only meant to trick users into surrendering remote access to their systems, allowing the criminals to steal personal and financial data.
What to Do If You Get This Pop-Up
If one of these fraudulent pop-ups appears, here are the steps to take:
- Close out the pop-up immediately and do not call the phone number. The alerts are fake.
- Disconnect your computer from the internet to terminate any connections.
- Run full system scans with reputable antivirus software and malware removal tools to eliminate any existing infections.
- Change passwords on all accounts accessed on that device, focusing on those with financial data and payment info. Enable two-factor authentication where possible.
- Contact your bank and credit cards to monitor closely for fraudulent transactions and report any detected.
- Avoid visiting illicit adult sites where tech support scam pop-ups are highly prevalent. Use ad-blockers.
The main priorities are closing the pop-up connection, running malware scans, and resetting account credentials as a precaution.
What to Do If You Already Called the Scammers
If you contacted the scammers before realizing the pop-up was fraudulent, quickly take these steps:
- End the remote session if the scammer still has access to your computer – immediately terminate the connection.
- Run comprehensive antivirus scans and delete anything suspicious found, including remote access tools.
- Change any account passwords that were accessed during the scam call and enable two-factor authentication. Monitor accounts closely.
- Contact your bank and credit cards about any fraudulent transactions on accounts. Dispute all unauthorized charges.
- Place fraud alerts on your credit files and check credit reports for identity theft indicators.
- File detailed scam reports with the FTC, FBI, BBB, and local law enforcement. Provide pop-up specifics.
Although being deceived is extremely unfortunate, acting swiftly to secure systems and accounts can help minimize damages from fraud or identity theft.
How to Avoid Pornographic Spyware Alert Pop-Up Scams
Here are some tips to protect yourself from this scam type:
- Never call unsolicited pop-up numbers about inappropriate content malware. Microsoft will not contact you this way.
- Be very wary of any robocalls insisting pornography was detected on your computer. Hang up immediately.
- Avoid visiting illicit adult sites where tech support scam pop-ups are highly prevalent.
- Use ad-blocking and anti-malware tools to prevent landing on pages with fake security alerts.
- Verify pop-ups through Microsoft.com or other official sources before calling numbers listed.
- Never provide personal or financial details to any unsolicited callers claiming security issues. No legitimate tech support will request this over the phone.
- Never allow remote access from pop-ups or cold calls unless you initiated contact directly with a verified computer security firm.
Stay vigilant for phony alerts, use security tools to block malicious pages, and only contact legitimate computer security firms directly – never use numbers listed on pop-ups.
Frequently Asked Questions About the Fake Pornographic Spyware Alerts
The Pornographic Spyware Alert scam uses fake pop-ups about inappropriate content and malware to trick users into calling scammers. Below we answer common questions about identifying and avoiding this prevalent tech support phishing scam.
What are the fake Pornographic Spyware Alert pop-ups?
These are fraudulent pop-up messages that suddenly appear on Windows PCs with titles like “Pornographic Spyware Alert” or “Microsoft Firewall Alert”. They accuse you of accessing inappropriate adult content resulting in spyware installations compromising your personal data.
What is the goal of the fake alerts?
The goal is to overwhelm critical thinking and scare users into calling the phone number listed in the pop-up window by making alarming claims about pornography viruses, identity theft, and explicit content spyware.
Do the pop-ups really come from Microsoft?
No, Microsoft does not send unsolicited pop-up warnings about detection of inappropriate content leading to spyware installations. The Pornographic Spyware Alert pop-ups have nothing to do with Microsoft and are totally fake, created only by scammers to deceive you.
What happens if I call the number on the pop-up?
If you call the number, scammers will pretend to be Microsoft support and claim they detected illegal porn activity that installed spyware on your system. They’ll insist on remotely accessing your computer to “remove the threats”, allowing them to steal your data.
Should I provide remote access to address the spyware?
No, you should never allow remote access from any pop-up making claims about pornography spyware. Microsoft would never contact you this way or demand remote access without verifying your identity first. The callers are scammers.
Can the pop-ups themselves infect my device?
The fake alerts cannot directly install malware just by appearing on your screen. However, providing the scammers remote access allows them to actively download trojans, keyloggers, ransomware and other malware.
How do I remove the spyware if I did call them?
If you provided remote access, immediately disconnect your PC from the internet and run full scans with your antivirus software and malware removal tools. Wipe your system fully using recovery options if infections are found. Also change all account passwords that were accessed during the scam call.
What should I do if one of these pop-ups appears?
If you see a Pornographic Spyware Alert, close it right away without calling the number. Disconnect from the internet, run security scans, and change your passwords. The pop-ups are always fake and designed to trick you.
How can I avoid the Pornographic Spyware Alert scam?
Use ad-blocking and antivirus software to prevent landing on pages with fake pop-ups. Avoid visiting shady adult sites frequently tied to this scam campaign. And remember, Microsoft will never send alerts like this.
Hopefully this gives you a better understanding of the fake Pornographic Spyware Alert pop-up scam so you can remain vigilant and protect yourself.
The Bottom Line
The fake Pornographic Spyware Alert pop-up scam uses social engineering about inappropriate content and malware to trick users into surrendering remote access to overseas cybercriminals posing as tech support.
If one appears on your computer, close the pop-up immediately without calling the number. Disconnect from the internet and run trusted antivirus scans, not any programs the scammers request. Reset all account passwords as a precaution too.
Avoid visiting the dangerous adult sites where tech support scam redirects are highly prevalent. Use security tools like ad-blockers and anti-malware to enhance protection.
Lastly, remember Microsoft will never send unsolicited alerts about detection of pornography or inappropriate content resulting in malware. Use extreme caution when evaluating any pop-up making such claims. Do not call the numbers listed or provide access to your device.







