Online shopping has become extremely popular in recent years due to its convenience and variety of products available. However, the rise of e-commerce has also led to an increase in online shopping scams designed to trick unsuspecting customers. One such prevalent scam involves fake shopping websites using the email address Reneeomano@hotmail.com.
Scam Overview
Reneeomano@hotmail.com is an email address that has been associated with numerous scam shopping websites. These fraudulent sites typically sell apparel, shoes, jewelry, and electronics at unbelievably huge discounts of up to 90% off.
They rely heavily on Facebook and Instagram ads to drive traffic to their sites. The ads showcase high-quality products like electric bikes, branded clothing and shoes at incredibly low prices to lure customers.
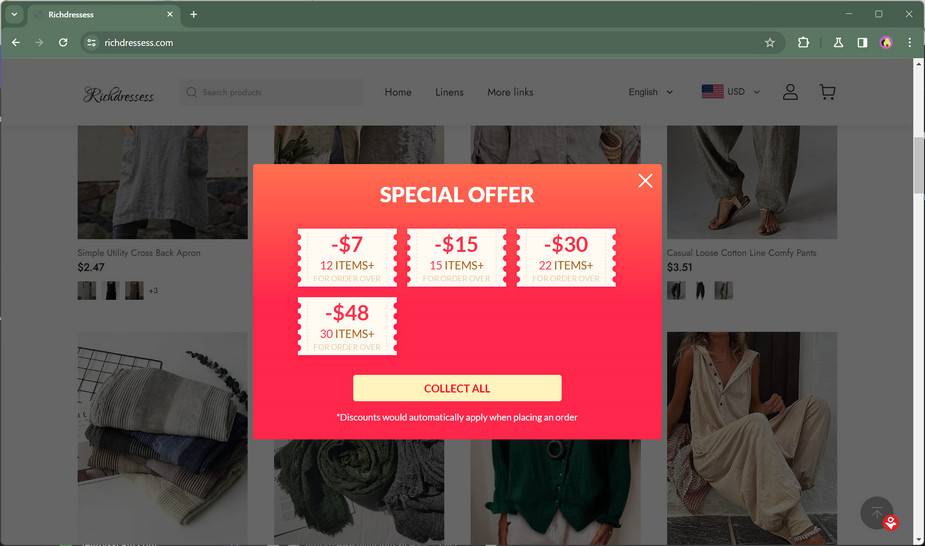
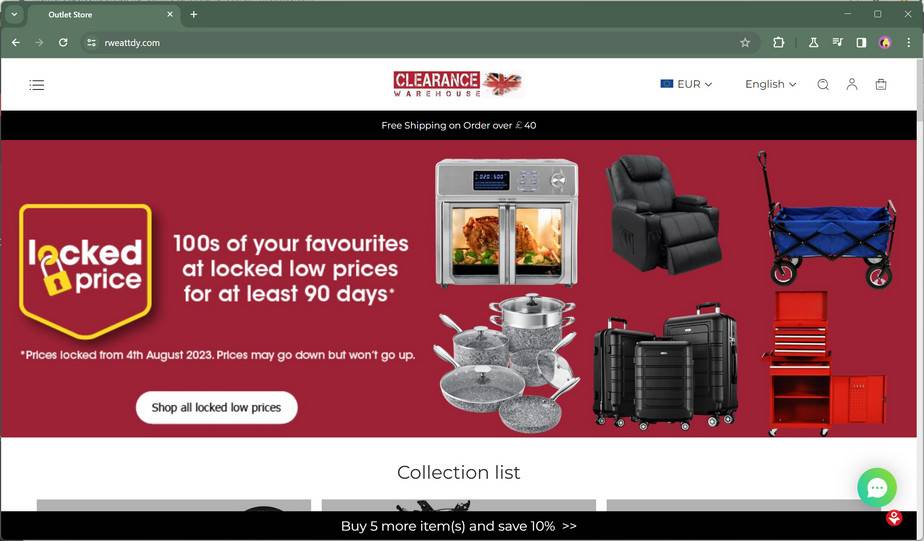
Once visitors arrive at the site, they soon realize it’s a scam. The website has a template design, no contact details apart from a suspicious email, unrealistic prices, and limited stock to create a false sense of urgency.
In this detailed article, we will uncover everything you need to know about this notorious online shopping scam and how to protect yourself.
The online shopping scam involving Reneeomano@hotmail.com operates in the following manner:
- Fake shopping websites are quickly set up featuring the email address Reneeomano@hotmail.com as the only contact detail. These sites use generic templates and stock content.
- Ads on social media like Facebook and Instagram heavily promote the scam shopping sites. The ads showcase expensive products like electric scooters and graphic tees at unbelievably low prices starting from $10.
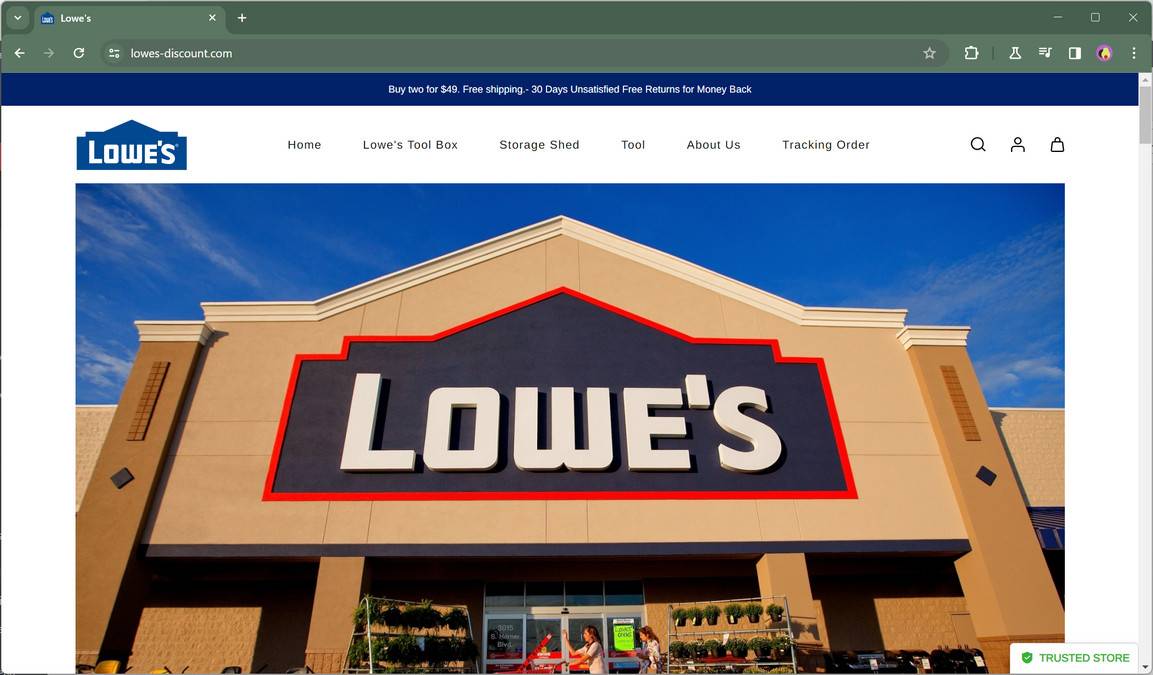
- When people click on the ads, they are directed to the scam sites with content and images likely stolen from legitimate businesses.
- The scam websites also create a false sense of urgency with claims like “Limited Time Sale!” and “Free Shipping”.
- After customers place orders, either the products never arrive or customers receive low-quality items very different from the advertisements.
- Customers who try to contact the company receive no response since Reneeomano@hotmail.com is fake.
- Within days, the scam sites disappear after defrauding many customers. The scam repeats with new domain names and ads.
This type of shopping scam is rampant and has robbed thousands of online shoppers who fell for improbable deals. Losses can range from a few dollars to hundreds based on the products ordered.
Next, let’s explore in-depth how this sneaky scam works to better understand the red flags and tricks used by scammers.
How the Scam Works
The Reneeomano@hotmail.com shopping scam is orchestrated in a strategic manner at every stage to maximize profits and avoid detection.
Stage 1 – Setting Up Fraudulent Sites
The first step for scammers is to quickly create fake e-commerce sites. Some common methods used are:
- Registering new domains: The scam sites use new domain names that are very different from reputable businesses. Examples include acpttdem.com, efdau.com, and ihualians.com.
- Using site templates: To speed up the process, ready-made website templates are used which only require some basic customization. The sites appear well-designed but lack unique content.
- Stealing content: Images, product descriptions, and other content are stolen from legitimate websites to appear credible. Reverse image search reveals the original sources.
- Providing limited contact details: Email addresses like Reneeomano@hotmail.com are mentioned but no physical address or working contact number.
Once the sites are ready, the next stage involves spreading awareness about the fake deals.
Stage 2 – Promotions on Social Media
Scammers leverage the power of social media ads to target and lure their victims. Some ways they promote the scam sites include:
- Facebook and Instagram ads: Eye-catching ads showcasing unbelievable discounts on electric bikes, clothing, jewelry, and other expensive products.
- FOMO messaging: Phrases like “Seize the deals before they are gone!” create a fear of missing out on the limited-time offers.
- Boosted posts: Paying for boosted social media posts ensures the ads are seen by more people for higher traffic.
- Clickbait: Posts like “GenesysGo X Electric Bike available for $17 only!” entice people to click on the links.
- Targeting: Scammers analyze user demographics and interests to show relevant ads to the right victims.
The goal is to direct as many people as possible to the scam sites by showing absurd discounts on products they may be interested in buying.
Stage 3 – Hooking Victims
When social media users click on the ads, they are taken to the scam websites. The sites utilize various tricks to convert visitors into making a purchase:
- Falsified reviews and trust badges: Fake 5-star reviews and trust seals like Norton and TrustedSite create legitimacy.
- Countdown timer: A sense of urgency and scarcity is created by showing extremely limited stock and a ticking timer.
- Upsells during checkout: Additional products and bundles are displayed at discounted prices to increase order value.
- Discount codes: New visitors are offered special percentage discounts by signing up which are applied during checkout.
- No customer service number: Removing ways to contact them directly makes it riskier for victims to request refunds later.
These sly tactics prevent visitors from examining the site in detail and drive impulse buying behavior.
Stage 4 – Collecting Payments
Since the scam sites do not have any real inventory, they rely on dishonest payment processors and methods to collect funds.
- Prepaid gift cards: Asking customers to pay using untraceable gift cards like iTunes and Amazon gift cards.
- Wire transfers: Requesting direct wire transfers to anonymous bank accounts which cannot be reversed.
- Fake payment pages: Some sites have bogus payment pages that collect credit card details but do not charge anything.
- Third-party processors: Services like backendpayment.com which help process payments involving scams and money laundering.
Payment options that offer zero buyer protection are accepted to avoid refunds and maximize profits.
Stage 5 – Vanishing Act
After accumulating substantial revenue from orders, the scammers vanish without delivering any products:
- Site shutdown: Within days, the scam sites are taken down and all history erased.
- Contact email stops working: Emails sent to Reneeomano@hotmail.com start bouncing since the mailbox is disabled.
- Social media ads paused: All promotions on Facebook/Instagram are halted once enough money is swindled.
- Phishing attempts: Any remaining victims may receive phishing emails requesting additional sensitive information like SSN, bank details etc.
Before customers realize they have been duped, the scammers disappear with the money. Rinse and repeat with brand new websites.
This methodical scam process enriches fraudsters while leaving customers frustrated without products they paid for or redressal. But there are ways to spot the red flags early and avoid getting scammed.
What to do if you Have Fallen Victim
If you unfortunately placed an order on a website using Reneeomano@hotmail.com and suspect it was a scam, you can attempt the following steps to mitigate losses:
Step 1: Stop Communications
Immediately cease all contact with the scammers regarding your order or payment. Do not reply to any texts, emails, or calls received as it will confirm you as a potential target for further scams or phishing attempts.
Step 2: Report the Scam
Notify relevant authorities about being defrauded:
- Report the website, social media accounts, and payment processor to the FTC at ReportFraud.ftc.gov.
- File complaints with the IC3 (Internet Crime Complaint Center) and BBB (Better Business Bureau) about the scam.
- Report fake social media ads and posts to get them taken down faster and prevent others from falling prey.
Reporting helps track scammer activities and potentially prevent more victims.
Step 3: Review Payment Options
Check what payment method was used to make the purchase. Depending on the option, you may be able to get your money back:
- For credit card payments, immediately notify your bank and dispute the charges as fraudulent.
- If paid with services like PayPal or Apple Pay, report unauthorized transactions to reverse the charges.
- wired transfers are tough to recover. However, contacting the recipient bank to report fraud may help recover funds.
- Prepaid gift cards and Bitcoin payments are virtually untraceable and cannot be canceled.
Step 4: Gather Evidence
Collect all evidence related to your order to strengthen your fraud claims. Keep copies of:
- Social media ads leading to the site
- Website screenshots
- All email communications
- Payment receipts or confirmation numbers
- Records of reporting the fraud
Evidence proves your money was stolen versus an order gone wrong.
Step 5: Be Vigilant
Going forward, exercise caution to avoid being scammed again:
- Avoid deals that seem too good to be true even if promoted by celebrities. Verify sponsored posts.
- Research unfamiliar websites and read reviews before purchasing.
- Stick to trusted brands and reputable platforms like Amazon.
- Use credit cards for added protection against fraud. Avoid untraceable payment methods.
- Do not trust social media ads blindly. Confirm legitimacy before clicking.
Staying vigilant is key to identify and steer clear of online shopping scams.
How to Spot and Avoid the Reneeomano@hotmail.com Scam
While this notorious scam ensnares many unsuspecting victims, there are several red flags you can watch out for to identify and steer clear of it:
Warning Signs of the Scam
- Unbelievable discounts like a $2000 electric bike available for $100.
- Website domain registered very recently like a month ago.
- No physical address or working customer service number listed.
- Reviews seem fake or copied from other sites.
- Limited stock badges and countdown timers creating false scarcity.
- Payment only via untraceable methods like wire transfer or gift cards.
Steps to Avoid the Scam
- Verify unfamiliar websites through online reviews and scam warnings.
- Research the domain name through WHOIS database to check registration date.
- Reverse image search product photos which are often stolen from other sites.
- Avoid making quick impulse purchases and take time to assess legitimacy.
- Use protected purchase methods like credit cards which allow disputing fraudulent charges.
- Report suspicious shopping websites and social media ads to relevant authorities.
- Read sponsored posts carefully and look up promoters before trusting.
Staying vigilant and checking for these signs can help you spot and steer clear of the Reneeomano@hotmail.com scam. Trust your instincts – if an offer seems unrealistic, it most likely is.
Frequently Asked Questions
What is the Reneeomano@hotmail.com scam?
This scam involves fake shopping websites that use the email address Reneeomano@hotmail.com to dupe customers into buying products at unbelievable discounts. Customers either receive low quality or no products after payment.
What products are sold on these scam sites?
The scam sites typically sell expensive items like electric bikes, jewelry, branded shoes and apparel at 90% off retail prices to attract victims.
How do they promote the scam sites?
Scammers run Facebook and Instagram ads showcasing huge discounts on popular products. The ads direct users to the fake sites through clickbait headlines and urgency messaging.
What payment methods do they accept?
Untraceable methods like gift cards, wire transfers, and crypto payments are accepted to avoid refunds. Credit cards may be collected but not actually charged.
What happens after I place an order?
In most cases, no product will be shipped at all. If you do receive a delivery, it will be a low-quality item very different from the advertisement.
How can I get my money back?
Unfortunately, payments via gift cards, wire transfer or crypto are virtually impossible to recover. For credit cards, immediately inform your bank about the fraud.
What precautions can I take to avoid this scam?
Beware of deals that seem too good be true, even if promoted by celebrities. Only shop on trusted sites, read reviews, avoid sketchy payment methods and confirm sponsored posts.
What should I do if I am a victim?
Report the scam to authorities like the FTC and IC3 immediately. Collect evidence like ads and screenshots. Dispute credit card payments as fraudulent with your bank.
Conclusion
The notorious Reneeomano@hotmail.com scam stands as a stark reminder that if a deal appears unrealistic, it most likely is. These fraudulent sites prey on the bargain hunting nature of online shoppers to deprive them of money and leave them without any recourse.
Thankfully, this guide has outlined all the vital red flags and devious tricks used in this scam. We explored how the scam sites are quickly set up, promoted on social media, aimed at creating a false sense of urgency, use shady payment methods before inevitably disappearing.
By reporting such fraud, using protected payment options, and exercising caution, we can work collectively to reduce the success of these scams. The old adage stands true – if something is too good to be true, it probably isn’t true. So stay safe during online shopping by doing proper due diligence.