When it comes to computer security, it’s important to be aware of the various processes and files that run on your system. One such file that you may come across is sdclt.exe. In this article, we will explore what sdclt.exe is, its purpose, and whether or not you should remove it from your system.

What is sdclt.exe?
Sdclt.exe is an executable file that is associated with the Windows Backup and Restore utility. It stands for “Windows Backup and Restore Control Panel.” This file is responsible for launching the Backup and Restore utility when you access it through the Control Panel or by using the “sdclt” command in the Run dialog box.
When you run the Backup and Restore utility, sdclt.exe is executed to handle the backup and restore operations. It allows you to create backups of your important files and restore them in case of data loss or system failure.
Is sdclt.exe a legitimate file?
Yes, sdclt.exe is a legitimate file that is included with the Windows operating system. It is located in the System32 folder, which is a common location for system files. However, like any other file, it is possible for malware to disguise itself as sdclt.exe in order to avoid detection.
If you suspect that sdclt.exe on your system may be malicious, it is important to scan your computer for viruses and malware. We recommend using Malwarebytes Free, a reputable antivirus and anti-malware software, to perform a thorough scan of your system.
Should I remove sdclt.exe?
In most cases, you should not remove sdclt.exe from your system. It is a critical component of the Windows Backup and Restore utility, and removing it may prevent you from being able to perform backups or restore your files.
However, if you are certain that sdclt.exe on your system is malicious, you should take immediate action to remove it. Again, we recommend using Malwarebytes Free to scan your system and remove any threats.
How to verify the legitimacy of sdclt.exe?
If you want to verify the legitimacy of sdclt.exe on your system, you can follow these steps:
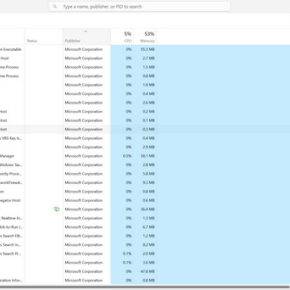
- Open the Task Manager by pressing Ctrl + Shift + Esc or by right-clicking on the taskbar and selecting “Task Manager.”
- Go to the “Processes” or “Details” tab, depending on your version of Windows.
- Locate sdclt.exe in the list of processes.
- Right-click on sdclt.exe and select “Open File Location.”
- If the file location is C:\Windows\System32\sdclt.exe, it is likely a legitimate file. However, if it is located in a different folder or has a different name, it may be malicious.
If you are still unsure about the legitimacy of sdclt.exe on your system, it is best to consult with a computer security professional or seek assistance from a reputable antivirus software provider.
Conclusion
Sdclt.exe is a legitimate file that is associated with the Windows Backup and Restore utility. It is responsible for launching the utility and handling backup and restore operations. While it is possible for malware to disguise itself as sdclt.exe, in most cases, you should not remove it from your system.
If you suspect that sdclt.exe on your system is malicious, it is important to scan your computer for viruses and malware. We recommend using Malwarebytes Free to perform a thorough scan and remove any threats.
Remember to always exercise caution when dealing with unfamiliar files and processes on your computer. Regularly updating your antivirus software and practicing safe browsing habits can help protect your system from potential threats.