Search.Whitesmoke.com is a browser hijacker, which is promoted via other free downloads, and once installed it will change your browser homepage and default search engine to search.whitesmoke.com, and install the WhiteSmoke toolbar.
Search.Whitesmoke.com will display advertisements and sponsored links in your search results, and may collect search terms from your search queries. The Search.Whitesmoke.com hijack is used to boost advertising revenue, as in the use of blackhat SEO, to inflate a site’s page ranking in search results.
Search.Whitesmoke.com it’s technically not a virus, but it does exhibit plenty of malicious traits, such as rootkit capabilities to hook deep into the operating system, browser hijacking, and in general just interfering with the user experience. The industry generally refers to it as a “PUP,” or potentially unwanted program.
Search.Whitesmoke.com is an ad-supported (users may see additional banner, search, pop-up, pop-under, interstitial and in-text link advertisements) cross web browser plugin for Internet Explorer (BHO) and Firefox/Chrome (plugin) and distributed through various monetization platforms during installation. The browser extension includes various features that will modify the default or custom settings of the browser including the home page, search settings and in some cases will modify Internet Explorer’s load time threshold, place a lock file within Firefox to prevent competing software from changing its settings as well as disable the browser’s Content Security Policy in order to allow for cross site scripting of the plugin.
Search.Whitesmoke.com is typically added when you install another free software (video recording/streaming, download-managers or PDF creators) that had bundled into their installation this browser hijacker. Very often users have no idea where did it come from, so it’s not surprising at all that most of them assume that Search.Whitesmoke.com is a virus. This program is also bundled within the custom installer on many reputable download sites (eg: CNET, Softonic), so if you have downloaded a software from these websites, chances are that Search.Whitesmoke.com was installed during the software setup process
For example, when you install VPlay, you will also agree to change your browser homepage and default search engine to search.whitesmoke.com, and install the WhiteSmoke toolbar.
However when you uninstall VPlay from your computer, your web browser’s default settings will not be restored. This means that you’ll have to remove Search.Whitesmoke.com and Local Moxie search from your favorite web browser manually.
You should always pay attention when installing software because often, a software installer includes optional installs, such as this Search.Whitesmoke.com browser hijacker. Be very careful what you agree to install.
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
How to remove Search.Whitesmoke.com browser hijacker – Virus Removal Guide
This page is a comprehensive guide, which will remove Search.Whitesmoke.com from your Internet Explorer, Firefox and Google Chrome.
Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Remove Search.Whitesmoke.com browser hijacker from your computer with AdwCleaner
STEP 2: Remove Search.Whitesmoke.com from Internet Explore, Firefox and Google Chrome with Junkware Removal Tool
STEP 3: Remove Search.Whitesmoke.com malicious files with Malwarebytes Anti-Malware Free
STEP 4: Double-check for the Search.Whitesmoke.com infection with HitmanPro
STEP 1: Remove Search.Whitesmoke.com browser hijacker with AdwCleaner
The AdwCleaner utility will scan your computer for Search.Whitesmoke.com malicious files that may have been installed on your computer without your knowledge.
- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Scan button as shown below.
AdwCleaner will now start to search for Search.Whitesmoke.com malicious files that may be installed on your computer. - To remove the Search.Whitesmoke.com malicious files that were detected in the previous step, please click on the Clean button.
AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK button.
STEP 2: Remove Search.Whitesmoke.com from Internet Explore, Firefox and Google Chrome with Junkware Removal Tool
Junkware Removal Tool is a powerful utility, which will remove Search.Whitesmoke.com extensions from Internet Explorer, Firefox and Google Chrome.
- You can download the Junkware Removal Tool utility from the below link:
JUNKWARE REMOVAL TOOL DOWNLOAD LINK (This link will automatically download the Junkware Removal Tool utility on your computer) - Once Junkware Removal Tool has finished downloading, please double-click on the JRT.exe icon as seen below.
If Windows prompts you as to whether or not you wish to run Junkware Removal Tool, please allow it to run. - Junkware Removal Tool will now start, and at the Command Prompt, you’ll need to press any key to perform a scan for the Search.Whitesmoke.com virus.
Please be patient as this can take a while to complete (up to 10 minutes) depending on your system’s specifications. - When the scan Junkware Removal Tool will be completed, this utility will display a log with the malicious files and registry keys that were removed from your computer.
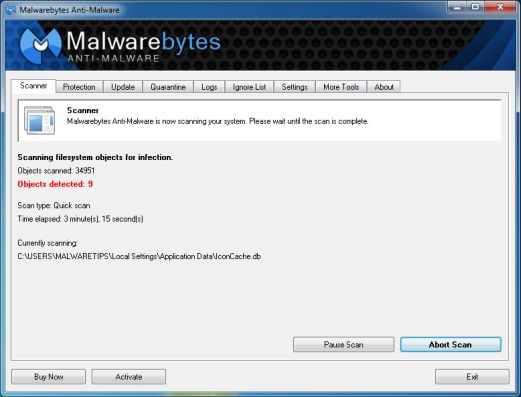
STEP 3: Remove Search.Whitesmoke.com malicious files from your computer with Malwarebytes Anti-Malware Free
Malwarebytes Anti-Malware Free utilizes Malwarebytes powerful technology to detect and remove all traces of malware including worms, trojans, rootkits, rogues, dialers, spyware and more.
- You can download Malwarebytes Anti-Malware Free from the below link,then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
Do not make any changes to default settings and when the program has finished installing, click on the Finish button.
- On the Scanner tab, select Perform quick scan and then click on the Scan button to start scanning your computer.
- Malwarebytes’ Anti-Malware will now start scanning your computer as shown below.
- When the Malwarebytes scan will be completed,click on Show Result.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
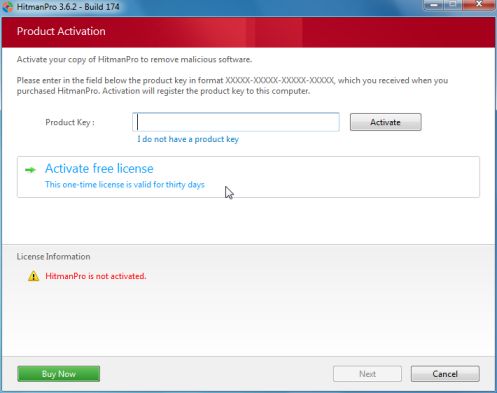
STEP 4: Double check for the Search.Whitesmoke.com infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti virus software, firewalls, etc.).
- You can download HitmanPro from the below link, then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for malware, as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove these malicious files.
- Click Activate free licenseto start the free 30 days trial and remove all the malicious files from your computer.
Your computer should now be free of the Search.Whitesmoke.com infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future.
If you are still experiencing problems while trying to remove Search.Whitesmoke.com hijacker from your machine, please start a new thread in our Malware Removal Assistance forum.
![Search.Whitesmoke.com homepage [Image: Search.Whitesmoke.com virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/10/search-Whitesmoke-com-virus.jpg)
![Search.Whitesmoke.com redirect [Image: Search.Whitesmoke.com redirect]](http://malwaretips.com/blogs/wp-content/uploads/2013/10/search-Whitesmoke-com-redirect.jpg)
![Click on Scan button to search for Search.Whitesmoke.com infection [Image: Adwcleaner Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-scan.jpg)
![Click on the Clean button to remove Search.Whitesmoke.com virus [Image: AdwCleaner removing infections]](http://malwaretips.com/blogs/wp-content/uploads/2013/08/adwcleaner-cleanup.jpg)
![Junkware Removal Tool scanning for Search.Whitesmoke.com virus [Image: Junkware Removal Tool scanning for Search.Whitesmoke.com homepage]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)
![Malwarebytes Anti-Malware final installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of malware [Image:Malwarebytes removing malware]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)