Live Security Platinum is a computer virus which will display fake security alerts,reporting that malware has been detected on your computer.This alerts are professional looking pop-ups and when you click on them, you are advised to buy Live Security Platinum in order to remove the detected threats.
In reality, none of the reported issues are real, and are only used to scare you into buying Live Security Platinum and stealing your personal financial information.
Apart from the bogus alerts,as part of its self-defense mechanism,Live Security Platinum has disabled the Windows system utilities, including the Windows Task Manager and Registry Editor,and will block you from running certain programs that could lead to its removal.
Further more,this rogue antivirus has modified your Windows files associations so now you can’t run files that end in a .exe extension.
If your computer is infected with Live Security Platinum,then you are seeing this images:
Registration codes for Live Security Platinum
As an optional step,you can use the following license key to register Live Security Platinum and stop the fake alerts.
Live Security Platinum license key: AA39754E-715219CE
Please keep in mind that entering the above registration code will NOT remove Live Security Platinum from your computer , instead it will just stop the fake alerts so that you’ll be able to complete our removal guide more easily.
Live Security Platinum Removal Guide
STEP 1 : Start your computer in Safe Mode with Networking
- Remove all floppy disks, CDs, and DVDs from your computer, and then restart your computer.
- Press and hold the F8 key as your computer restarts.Please keep in mind that you need to press the F8 key before the Windows start-up logo appears.
Note: With some computers, if you press and hold a key as the computer is booting you will get a stuck key message. If this occurs, instead of pressing and holding the “F8 key”, tap the “F8 key” continuously until you get the Advanced Boot Options screen. - On the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
STEP 2: Remove Live Security Platinum malicious proxy server
Live Security Platinum may add a proxy server which prevents the user from accessing the internet,follow the below instructions to remove the proxy.
- Start the Internet Explorer browser and if you are using Internet Explorer 9 ,click on the gear icon
(Tools for Internet Explorer 8 users) ,then select Internet Options.
- Go to the tab Connections.At the bottom, click on LAN settings.
- Uncheck the option Use a proxy server for your LAN. This should remove the malicious proxy server and allow you to use the internet again.
If you are a Firefox users, go to Firefox(upper left corner) → Options → Advanced tab → Network → Settings → Select No Proxy
STEP 3: Repair your Windows Registry from Live Security Platinum malicious changes.
Smart Fortress 2012 has changed your Windows registry settings so that when you try to run a executable file (ending with .exe ) , it will instead launch the infection rather than the desired program.
- Download the registryfix.reg file to fix the malicious registry changes from Live Security Platinum.
REGISTRYFIX.REG DOWNLOAD LINK (This link will automatically download the registry fix called registryfix.reg) - Double-click on registryfix.reg file to run it. Click “Yes” for Registry Editor prompt window,then click OK.
STEP 4: Run RKill to terminate known malware processes associated with Live Security Platinum.
RKill is a program that will attempt to terminate all malicious processes associated with Live Security Platinum,so that we will be able to perform the next step without being interrupted by this malicious software.
Because this utility will only stop Live Security Platinum running process, and does not delete any files, after running it you should not reboot your computer as any malware processes that are configured to start automatically will just be started again.
- While your computer is in Safe Mode with Networking ,please download the latest official version of RKill.Please note that we will use a renamed version of RKILL so that Live Security Platinum won’t block this utility from running.
RKILL DOWNLOAD LINK (This link will automatically download RKILL renamed as iExplore.exe) - Double-click on the iExplore.exe icon in order to automatically attempt to stop any processes associated with Live Security Platinum.
- RKill will now start working in the background, please be patient while the program looks for various malware programs and tries to terminate them.
IF you are having problems starting or running RKill, you can download any other renamed versions of RKill from here. - When Rkill has completed its task, it will generate a log. You can then proceed with the rest of the guide.
WARNING: Do not reboot your computer after running RKill as the malware process will start again , preventing you from properly performing the next step.
STEP 5: Remove Live Security Platinum malicious files with Malwarebytes Anti-Malware FREE
- Download the latest official version of Malwarebytes Anti-Malware FREE.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - Start the Malwarebytes’ Anti-Malware installation process by double clicking on mbam-setup file.
- When the installation begins, keep following the prompts in order to continue with the setup process. Do not make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked. Then click on the Finish button. If Malwarebytes’ prompts you to reboot, please do not do so.
- Malwarebytes Anti-Malware will now start and you’ll be prompted to start a trial period , please select ‘Decline‘ as we just want to use the on-demand scanner.
- On the Scanner tab,select Perform full scan and then click on the Scanbutton to start scanning your computer.
- Malwarebytes’ Anti-Malware will now start scanning your computer for Live Security Platinum malicious files as shown below.
- When the scan is finished a message box will appear, click OK to continue.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
- Malwarebytes’ Anti-Malware will now start removing the malicious files.After completing this task it will display a message stating that it needs to reboot,please allow this request and then let your PC boot in Normal mode.
STEP 6: Double check your system for any left over infections with HitmanPro
- This step can be performed in Normal Mode ,so please download the latest official version of HitmanPro.
HITMANPRO DOWNLOAD LINK (This link will open a download page in a new window from where you can download HitmanPro) - Double click on the previously downloaded fileto start the HitmanPro installation.
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - Click on Next to install HitmanPro on your system.
- The setup screen is displayed, from which you can decide whether you wish to install HitmanPro on your machine or just perform a one-time scan, select a option then click on Next to start a system scan.
- HitmanPro will start scanning your system for malicious files as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the malicious files that the program has found.Click on Next to remove this malicious files.
- Click Activate free license to start the free 30 days trial and remove the malicious files.
- HitmanPro will now start removing the infected objects.If this program will ask you to restart your computer,please allow this request.
STEP 7: Remove the left over malicious registry keys and files
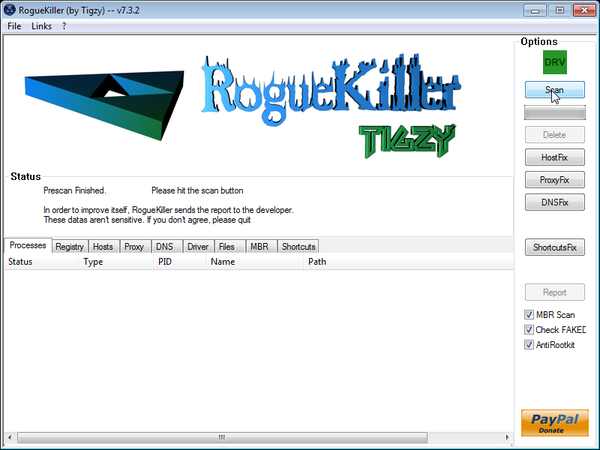
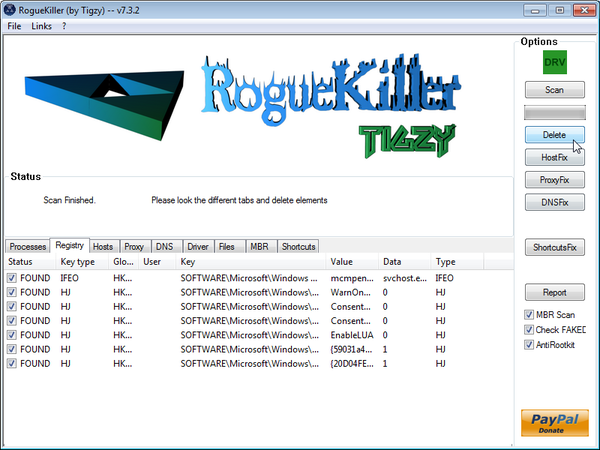
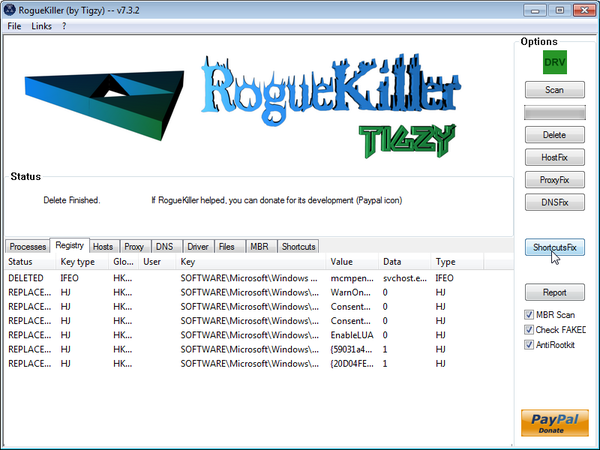
Live Security Platinum has sadded some malicious registry keys to your Windows installation , to remove this malicious changes we need to run a scan with RogueKiller.
- Please download the latest official version of RogueKiller.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Start button to perform a system scan.
- After the scan has completed, press the Delete button to remove any malicious registry keys.
- Next we will need to restore your shortcuts, so click on the ShortcutsFix button and allow the program to run.
![Live Security Platinum virus [Image: Live Security Platinum virus]](http://malwaretips.com/blogs/wp-content/uploads/2012/06/Live-Security-Platinum-2.png)
![Live Security Platinum fake alert [Image: Live Security Platinum Alert]](http://malwaretips.com/blogs/wp-content/uploads/2012/06/Live-Security-Platinum-4.png)
![Live Security Platinum activation [Image: Live Security Platinum Activation request]](http://malwaretips.com/blogs/wp-content/uploads/2012/06/Live-Security-Platinum-3.png)
![Live Security Platinum fake warning [Image: Live Security Platinum Warning]](http://malwaretips.com/blogs/wp-content/uploads/2012/06/Live-Security-Platinum-1.png)
![Safe Mode with Networking screen [Image: Safemode.jpg]](http://malwaretips.com/images/removalguide/safemode.jpg)
![Internet Options in IE [Image: Internet-options-IE.png]](http://malwaretips.com/images/removalguide/ie1.png)
![Connections tab in Internet Explorer [Image: Remove-proxy-server2.png]](http://malwaretips.com/images/removalguide/ie2.png)
![Uncheck the option Use a proxy server for your LAN [Image: Remove-proxy-server3.png]](http://malwaretips.com/images/removalguide/ie3.png)
![Live Security Platinum - Virus Removal Guide 1 [Image: fix registry]](http://malwaretips.com/blogs/wp-content/uploads/2011/12/registry.png)
![RKILL ICON [Image: run-rkill-1.png]](http://malwaretips.com/images/removalguide/rkill1.png)
![RKILL Command prompt [Image: run-rkill-2.png]](http://malwaretips.com/images/removalguide/rkill2.png)
![RKILL LOG [Image: Live Security Platinum rkill3.jpg]](http://malwaretips.com/images/removalguide/rkill3.png)
![Malwarebytes Anti-Malware Installer [Image: Malwarebytes Installer]](http://malwaretips.com/images/removalguide/malwarebytes-setup.png)
![Malwarebytes last setup screen [Image: Finishing Malwarebytes installation]](http://malwaretips.com/images/removalguide/update-malwarebytes.png)
![Decline trial period in Malwarebytes Anti-Malware [Image: Decline Malwarebytes trial]](http://malwaretips.com/images/removalguide/malwarebytes-trial.png)
![Perform a Full System Scan with Malwarebytes Anti-Malware [Image: Starting a full system sca]](http://malwaretips.com/images/removalguide/start-scan-malwarebytes.png)
![Malwarebytes Anti-Malware scanning for Live Security Platinum [Image: Malwarebytes scanning for malicious files]](http://malwaretips.com/images/removalguide/scan-malwarebytes.png)
![Malwarebytes when the system scan has finished [Image: Malwarebytes scan results]](http://malwaretips.com/images/removalguide/results-malwarebytes.png)
![Removing the infections found by Malwarebytes [Image: Infections found by Malwarebytes]](http://malwaretips.com/images/removalguide/detection-malwarebytes.png)
![HitmanPro Installer [Image: HitmanPro Icon]](http://malwaretips.com/images/removalguide/hpro1.png)
![HitmanPro installation process [Image: Starting HitmanPro]](http://malwaretips.com/images/removalguide/hitmanpro36-start.png)
![HitmanPro setup options [Image: HitmanPro installation screen]](http://malwaretips.com/images/removalguide/hitmanpro36-installation.png)
![HitmanPro while scanning for Live Security Platinum virus [Image: HitmanPron scanning for Live Security Platinum]](http://malwaretips.com/images/removalguide/hitmanpro36-scan.png)
![HitmanPro displaying scan results [Image: HitmanPro scan results]](http://malwaretips.com/images/removalguide/hitmanpro36-results.png)
![Activate the HitmanPro free 30 days trial to remove any detected infections [Image: Activate HitmanPro license]](http://malwaretips.com/images/removalguide/hitmanpro36-activation.png)








Sir, I was so impresses by your clarity & generosity that I read back to Sept. 1, to see if my problem was already addressed. My Lenovo x300 was infected yesterday (Firefox) and froze. I restarted in safe mode, but can not connect to the Internet because I rely solely on an imbedded Sierra 1x-EV-DO network adapter for broadband connection with Verizon. The device manager tells me it can not start (code 10) and Verizon’s Access Connections is locked to “other” not broadband. Are these problems potentially related to this virus or do I first need a new adapter to clean up?
You really and truly are a hero
I discovered Windows prevents me from connecting in safe mode
Hello Peter,
Yes,this behavior is related to malware.Lets try to fix it.Did you try to use the activation code provided in this guide (AA39754E-715219CE)…If,please try to use this code as it could make the removal process much more easy.
NEXT,download TDSSKiller.zip
Next,can you please run a scan with Combofix and Complete Internet Repair utility, and post the logs here so that I can get an idea on what’s going on:
STEP 1 : Run a scan with Combofix
Download ComboFix from the below link:
COMBOFIX DOWNLOAD LINK (This link will automatically download Combofix on your computer)
VERY IMPORTANT !!! Save as Combo-Fix.exe during the download.ComboFix must be renamed before you download to your Desktop
Notes:
STEP 2: Run a scan with Complete Internet Repair utility
Many many thanks. You are a star!
Hello Stelian!And Thank you so much!
Thanks
IE9
Windows Vista 64-bit
Hi Stelian,
This solution got rid of the virus, very helpful and clear, thank-you!
However, now my Internet Explorer is running very, very slow. It takes a long time to load each page. This did not happen before I followed your steps to get rid of the virus – I am wondering if there is a relation and have you seen this before? Do you have a way to fix the slow IE9?
Steps I followed:
1. safe mode with networking
2. registry fix
3. Rkill
4. Malwarebytes
5. HitmanPro
6. Rogue Killer
7. Kaspersky
8. Eset online scan
Thanks,
Andrew
Hello,
Can you reset Internet Explorer to its default settings and see how that it works: http://windows.microsoft.com/en-US/windows7/Reset-Internet-Explorer-settings-in-Internet-Explorer-9
Thank you Stelian!
Thank you for all your help and support
You, my friend, are a lifesaver! THANK YOU! :-)
Perfect! You are a lifesaver.
Count me in with a big :THANK YOU!
Excellent step by step guide, sorted the issue completely.
Thanks Stelian, you are a true star !! :)
Thanks!
Thankyou so much!! this is the second time ive had this virus and i think its because i did not remove it as thoroughly as was done under your guidance. THANKYOU COMPUTER ANGEL!
Thank you so much! You are a life saver!
Fk… you are the best bro. Thanks for the help. I fkin love you!
Thanx a lot for this wonderful guide. A friend of mine has this issue and we succeed to manage it.
Thanks for the guide!
I have a problem though… When I start in safe mode it just keeps restarting, it won’t ever load windows, just restarts and says that Windows didn’t shut down correctly, and do I want to start in safe mode, but again, selecting it here causes a reboot, so it just loops. I can start in normal mode.
In normal mode I used FixExec to stop the virus and allow me to run MalwareBytes. I ran a quick scan, and deleted all of the selected issues. I allowed it to reboot, but I was immediately met with the same Live Security Platinum screen and the fake scan that it does.
I have just started a full scan using the method I described above. What else should I do to get rid of the virus? Should I run your other suggestions straight after the malwarebytes scan and fix, without allowing it to restart? It seems like the virus will only start over again if I restart at that point.
Any advice would be greatly appreciated as I have very limited time to get this fixed!
Hello ,
Lets try to fix your computer,please run the below tools while in Normal Mode;
STEP 1: Run a scan with Malwarebytes Anti-Malware in Chameleon Mode in Norman mode:
STEP 2: Run a scan with RogueKiller
RogueKiller Download Link (This link will automatically download RogueKiller on your computer)
STEP 3 Please perform a scan with HitmanPro as seen on the guide.
If you are having problems starting this program please use the ForceBreach mode as described in the guide.
STEP 4: Run a scan with ESET Online Scanner:
ESET Online Scanner Download Link (This link will automatically download ESET Online Scanner on your computer.)
Waiting for your reply to tell me how everything is running!
Good luck…
THANK YOU SO MUCH!!!! I am beyond words in expressing my heartfelt gratitude towards you! I would have lost all my work on the computer without you!! Thanks a million billion trillion!
This was so amazingly helpful. I was in the middle of research for class with typefaces when this happened and completely ruined my whole night. I started spazing and everything. I really appreciate the fact that you have this up for people to use. Greatly appreciate it.