The Elon Musk WLF tokens giveaway scam is designed to look like a major, time-sensitive event, not a random promotion. It often appears as an “X crypto giveaway” announcement and drives people to a polished landing page claiming that $250,000,000,000 worth of WLF tokens are being distributed through World Liberty Financial.
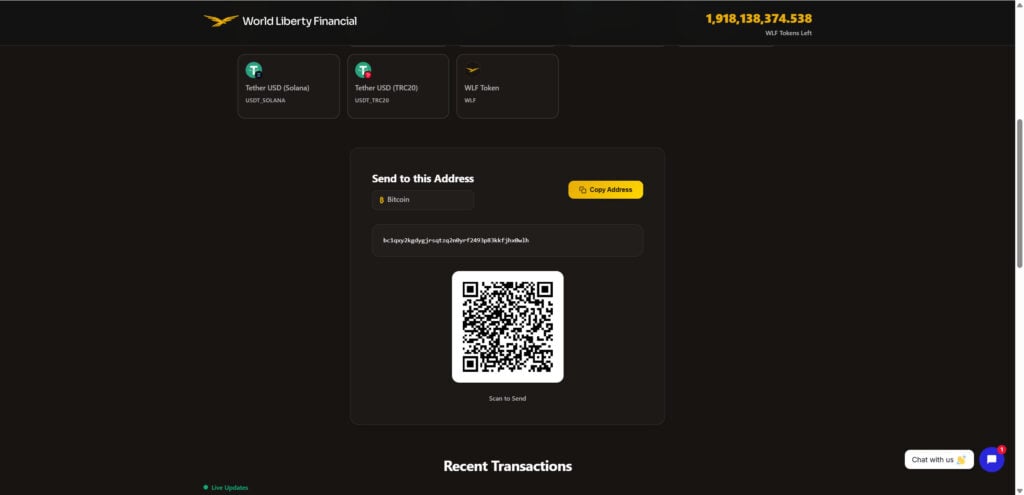
The site presents a simple promise: choose a cryptocurrency, send a “desired amount” to a displayed wallet address, and receive 2x back in WLF tokens “instantly.” To reduce hesitation, it adds a “tokens left” counter, a live-looking “recent transactions” feed, and comments that imply other users are already receiving payouts.
This guide breaks down what the site is really doing, why it convinces people so quickly, and the specific steps to take if you have already sent funds or interacted with the scam page.

Scam Overview
The Elon Musk WLF tokens giveaway scam is built around one of the oldest tricks in crypto: the “send crypto, get more back” lie. It keeps working because it exploits two hard truths at the same time:
- People want simple opportunities that feel like insider access.
- Crypto transactions are irreversible once they leave your wallet.
The page shown in your screenshots presents itself as a large-scale WLF token giveaway hosted by World Liberty Financial. The headline is deliberately extreme: “$250,000,000,000 Worth of WLF Tokens to be given away.” Under that, it gives a short instruction that is the entire scam in one sentence:
Send a desired amount of your chosen cryptocurrency to a wallet address and you will receive double back in WLF tokens, “instantly.”
That is the core con. There is no real giveaway mechanic here. There is no legitimate distribution. There is no automated doubling system. What happens in reality is simple: once victims send crypto, the scammers keep it.
What the page is doing to look legitimate
This scam does not rely on a messy, broken website. It relies on a site that looks confident and “official.” The visual design matters because it reduces hesitation long enough for a victim to take the one action the scammers need: sending funds.
In the screenshots, several elements are used to create that feeling of legitimacy:
- A professional header with the “World Liberty Financial” branding and logo.
- A “tokens left” counter shown at the top right (for example, 1,918,138,374.538), which suggests a live, tracked giveaway pool.
- A big promise headline using a huge dollar amount, which signals “major event” and “big sponsor.”
- A three-step panel that makes the scam feel like a normal process:
- “Send desired amount” with a stated minimum and maximum (minimum 0.001, maximum 10).
- “Get 2x back.”
- “Instant transfer.”
- A crypto selection section that lets you pick what to send, including Bitcoin, Ethereum, Dogecoin, and multiple USDT networks (ERC20, Polygon, Solana, TRC20).
- A “copy address” button and QR code, designed to remove friction so you send quickly.
- A “Recent Transactions” box showing wallet-to-wallet activity and “WLF” amounts credited, which suggests other people are successfully receiving tokens.
- A “Register for Airdrop” form, which adds a fake extra layer of “official” participation and tracking.
None of these elements prove anything. They are presentation choices, and presentation is cheap. The only thing that matters is what happens on-chain, and in scams like this, the chain activity usually shows funds flowing one way only: into wallets controlled by the scammers.
The biggest red flag: real giveaways do not require you to send crypto first
Legitimate token airdrops and promotions do not work like this.
A real airdrop might require you to:
- Hold a certain asset at a snapshot time.
- Complete a social task (follow, retweet, join a server).
- Claim tokens through an official project website using a wallet connection.
But a legitimate organization does not say: “Send us Bitcoin and we will send you double back.”
That is not a giveaway. That is a direct request for funds, and it is indistinguishable from theft because it functions exactly like theft. Once you send, the recipient controls the money. If they decide not to send anything back, you have no built-in recovery path.
And scams like this often add psychological pressure:
- “Tokens left” counters and “limited allocation” language to create urgency.
- Minimum and maximum send values to make it feel structured and “real.”
- Claims of instant delivery to reduce the time you spend thinking.
- Celebrity framing to bypass skepticism.
The “Recent Transactions” trap
One of the smartest parts of this scam is the “Recent Transactions” table. It is there for one reason: social proof.
A visitor who is hesitating might think, “If I could just see someone else doing it successfully, I’d feel safe.”
So the page shows a scrolling list of transactions with small snippets of wallet addresses, amounts sent (like 0.01 BTC or 5.0 USDT_TRC20), and a “status” that appears to show WLF tokens credited.
But look closely at what that implies. The page claims you receive double back in WLF tokens, yet the displayed “credits” do not consistently match a doubling concept. For example:
- One row shows 0.01 BTC with a status of +16462 WLF.
- Another shows 5.0 USDT_TRC20 with +77 WLF.
- Another shows 0.01 USDT_SOLANA with +0 WLF.
That inconsistency is a strong signal that this table is not a real accounting system. In many scam pages, the “recent transactions” feed is simply:
- A prefilled list of fake entries.
- Randomly generated strings formatted like addresses.
- A script that refreshes numbers to simulate activity.
- Or a scraped feed from real chain activity, misrepresented as “proof” of their giveaway.
Even when scammers display real-looking hashes or addresses, they can still be lying about what those transactions mean. A real blockchain transaction does not validate a promise. It only proves that a transfer happened, not that a giveaway is real.
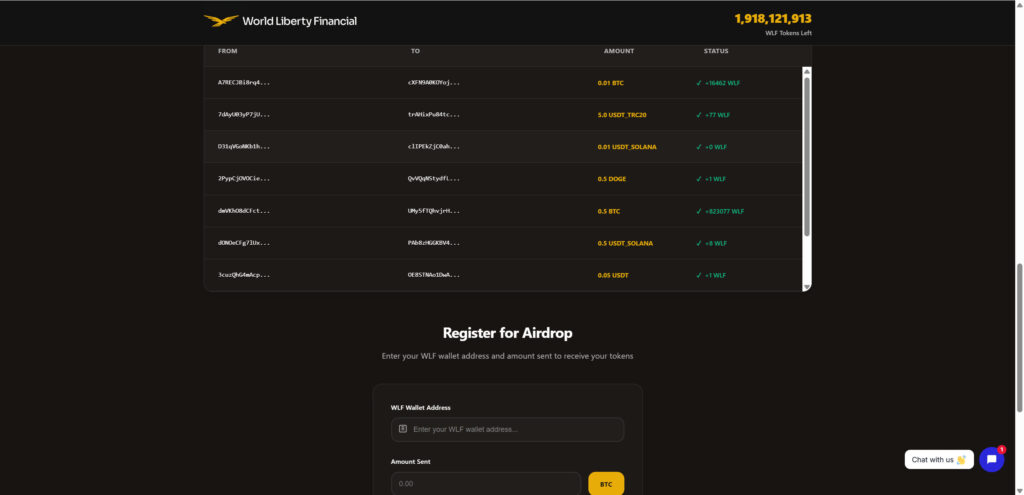
The “airdrop registration” layer is a credibility play, not a safety step
The page includes a “Register for Airdrop” area that asks for:
- A WLF wallet address.
- The amount sent.
This is another psychological trick. It makes the page feel like it has an internal system, a ledger, a support trail.
In reality, this form often exists to:
- Keep victims engaged after they have sent funds.
- Create the impression that tokens are “processing,” so the victim waits instead of acting quickly.
- Collect contact details or wallet identifiers for future targeting.
- Set up the next ask, which is often a second payment.
Many crypto giveaway scams follow a pattern after the first transfer:
- “You need to send a small verification amount.”
- “You need to pay a gas fee.”
- “Your transfer is pending until you upgrade your tier.”
- “We detected unusual activity, send again to confirm.”
The point is not verification. The point is extracting more money while the victim is emotionally committed.
Celebrity branding and fake “news story” framing
Your screenshots also show a blog-style post titled “Elon Musk – X Crypto Giveaway,” presented like a short article with a banner graphic, and text claiming an unprecedented milestone such as a $500 billion net worth and an “exclusive crypto giveaway.”
This is a common scam tactic: wrap the theft mechanism inside a story.
A story gives the link a reason to exist. It creates context that feels shareable. It also gives the scam a surface-level explanation for why the giveaway is so large.
The post format also makes it easier to distribute the scam on social media and through ads, because it looks like content, not a transaction page.
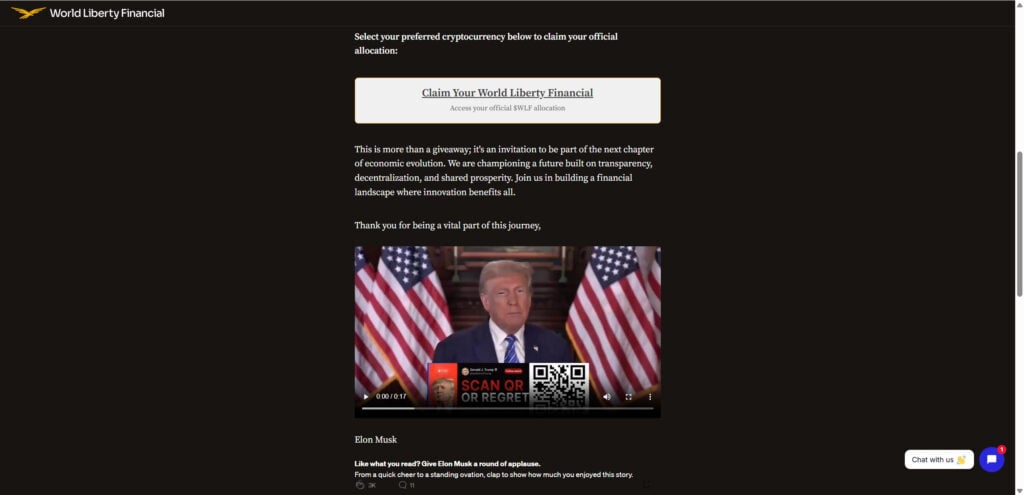
Another screenshot shows a page asking users to “Claim Your World Liberty Financial” and includes an embedded video clip with a QR overlay that says “SCAN OR REGRET.” That kind of language is deliberately aggressive. It tries to push you into acting quickly, and it signals what the scammer wants most: fast clicks and fast transfers.
Why people fall for it, even if they know scams exist
It is easy to say “I would never fall for that,” until you see how many small levers are being pulled at once.
This scam works because it combines:
- Familiar names and platforms, including X style framing.
- A clean interface that feels “official.”
- A simple, step-by-step action flow.
- Social proof through comments and transaction feeds.
- Urgency through scarcity counters and huge giveaway claims.
- The illusion of safety through terms like “verified wallet address.”
Most victims are not fooled because they are careless.
They are fooled because the page is designed to create just enough certainty to get one irreversible transaction.
How The Scam Works
The WLF tokens giveaway scam is basically a funnel. Every part of the experience is built to move you from curiosity to action, with as little time for reflection as possible.
Below is the typical step-by-step flow, matching what is shown in your screenshots and how similar “2x back” crypto scams operate.
Step 1: The hook appears where people already trust the context
Most victims do not start by searching for “WLF token giveaway.”
They encounter it in a place where it feels normal to see promotional announcements:
- A post styled like a celebrity announcement.
- A repost or reply thread that looks busy and active.
- A paid ad disguised as a news update.
- A sponsored-looking graphic with crypto logos.
- A short “article” that reads like a quick update with a call to action.
The scam wants you to feel like you discovered an event in progress, not a random website begging for money.
This is why the page is framed as an “X crypto giveaway,” and why it includes a blog post format with engagement icons and visible comment counts. It is creating the atmosphere of a real social media announcement.
Step 2: The click lands you on a polished “giveaway portal”
Once you land on the site, the first goal is to remove doubt.
The headline uses an eye-catching number: $250,000,000,000 worth of tokens. That amount is intentionally oversized. In scam psychology, huge numbers do not always raise suspicion. They often raise excitement.
Then the page gives you a script:
- Send your desired amount.
- Get 2x back.
- Instant transfer.
This reads like a promotion, not a transaction.
It also adds structure with minimum and maximum values (minimum 0.001, maximum 10), which makes the scam feel like it has “rules,” and rules create false legitimacy.
Step 3: You are asked to choose a cryptocurrency that is easy to send
The “Choose Your Cryptocurrency” section is not there for user convenience. It is there because scammers want the broadest possible victim pool.
By offering multiple coins and multiple USDT networks, the scam captures:
- People who hold Bitcoin.
- People who hold stablecoins.
- People using cheaper networks like TRC20.
- People who do not want to deal with swapping assets.
A real giveaway might distribute tokens on one chain and require a compatible wallet. This scam does not care. It is not distributing anything. It just wants assets it can receive and move.
Step 4: The wallet address and QR code appear, and friction drops to zero
After you select a coin, the page shows:
- “Send to this Address”
- A coin label (for example, Bitcoin)
- A “Copy Address” button
- A wallet address string
- A QR code
This is the moment the scam is built around.
The copy button removes typing errors, which reduces the chance you pause. The QR code makes it easy to send from a phone. The interface is doing the work of pushing you toward completion.
At this point, the victim often thinks the address is “verified” because the page said so.
But there is no such thing as a universally “verified wallet address” on the open internet. Anyone can publish an address and call it verified.
Step 5: The victim sends funds, and the scam quietly succeeds
If the victim sends crypto, the scammers have already won.
Crypto transfers are final. There is no customer service desk for Bitcoin. If you send to a scammer’s address, the network will not reverse it because the transaction was valid.
This is why these scams love the “send first, receive later” model. It relies on irreversible mechanics.
Victims often refresh the page after sending and look for confirmation. The scam anticipates that, which is why it displays:
- “Recent Transactions”
- Green check marks
- “WLF credited” style status entries
- Live-looking updates
This content is not for accounting. It is for emotional management.
It keeps the victim calm and optimistic for a few minutes longer.
Step 6: The site adds a second engagement step to keep you from leaving
After the first send, many victims start looking for what to do next.
The scam provides the next step: “Register for Airdrop.”
This is a smart move because it gives the victim something to do that feels productive, instead of doing the one thing that could help: immediately contacting their exchange, documenting the transaction, and warning others.
The registration form typically asks for:
- Your wallet address.
- The amount you sent.
- Sometimes an email address or a username.
It may also imply that you need to “register” for the system to release your tokens.
In reality, this step is usually one of three things:
- A delay tactic to keep you on the hook.
- A data collection tactic to target you again later.
- A setup for the second payment request.
Step 7: The “processing” excuse appears, followed by the second payment ask
Not every victim will see the same follow-up, but the pattern is extremely common.
After the first payment, the scam may claim:
- The transaction is pending because of network congestion.
- You need to “validate” your wallet with another small send.
- You must pay a “gas fee” to release the tokens.
- Your payment was received, but your “tier” only allows a smaller allocation.
- You were selected for a larger allocation, but you need to confirm eligibility.
This is where victims can lose much more than the first transfer. The scam uses momentum. Once you have already sent money, it is easier to rationalize sending a bit more to “unlock” the promised return.
It is the same psychology as a slot machine. The win feels one step away.
Step 8: Fake comments and testimonials reinforce the illusion
Your screenshots show a comment section filled with messages like:
- “It works! I got 200,000 WLF!!”
- “I got back 1,000,000 WLF in my wallet!!”
- “1,430,000 WLF to my wallet!!”
This content is designed to answer the victim’s internal question: “Has anyone actually received anything?”
Scammers use:
- Bot accounts.
- Recycled usernames.
- Copy-paste testimonial templates.
- Random large token numbers that feel exciting.
They may even include mixed-language names to look international and real.
But none of these comments are verified. They are marketing copy in comment form.
Step 9: The scam disappears, rebrands, or moves domains
These giveaway scams rarely stay in one place for long.
Once a domain is reported or blocked, the same template often reappears under a different name with a different “token” and a different celebrity hook.
That is why it is important to learn the underlying pattern, not just the specific brand name.
If the page is asking you to send crypto first in exchange for a promise of more later, it is a scam pattern, regardless of which logo is at the top.
What To Do If You Have Fallen Victim to This Scam
If you already sent crypto to a WLF giveaway address or interacted with the page, treat it like a time-sensitive incident. The goal is to limit further loss, secure your accounts, and preserve evidence.
- Stop sending funds immediately
- Do not “verify” anything.
- Do not pay a “gas fee.”
- Do not send a second transaction to “unlock” the first.
- Legitimate giveaways do not require repeat payments.
- If you sent from an exchange, contact the exchange support right away
- If you used Coinbase or another exchange, open a support ticket immediately.
- Provide the destination address and the transaction ID (hash).
- Ask whether they can flag the address internally or assist with compliance reporting.
- Recovery is unlikely, but fast reporting can sometimes help if funds hit an exchange that cooperates with law enforcement.
- If you sent from a self-custody wallet, secure the rest of your funds
- If you only sent a transfer (no wallet connection), the scammer cannot automatically drain the rest of your wallet just from receiving funds.
- Still, if you feel uncertain, move remaining funds to a fresh wallet you control, using a device you trust.
- If you connected your wallet or signed anything, assume your wallet may be exposed
- Some scams combine “send” instructions with wallet-draining approvals.
- If you connected a wallet and approved a token allowance, a scammer can sometimes pull tokens later.
- Revoke any suspicious approvals using a reputable permission management tool for the chain you used, then move assets to a new wallet.
- Change passwords and secure your email
- If you entered an email address, password, or reused credentials anywhere related to this scam, change those passwords now.
- Turn on 2FA for your email and exchange accounts.
- Your email is the master key for account recovery, so lock it down first.
- Check your device for risky browser extensions or malware
- These scams are often promoted through compromised ad networks, sketchy redirects, or malicious extensions.
- Review browser extensions and remove anything you do not recognize.
- Run a reputable malware scan on the device you used.
- Document everything while it is still available
- Save screenshots of the page, the wallet address shown, and the “recent transactions” section.
- Save the URL and any redirects.
- Save your transaction hash and the time you sent it.
- If the site disappears later, this documentation can still support a report.
- Report the scam to the right places
- Report the website to your browser’s phishing reporting flow.
- Report the domain to its registrar and hosting provider.
- If you are in the United States, file a report with FBI Internet Crime Complaint Center (IC3).
- If you are elsewhere, report to your national cybercrime unit or consumer protection authority.
- Report the wallet address on chain explorers and abuse databases
- Many explorers and crypto security communities allow address flagging.
- Even if it does not recover your funds, it can protect the next person.
- Watch for “recovery” scammers
- After people post about being scammed, they often get messages from fake “investigators” claiming they can recover funds for a fee.
- They cannot.
- Anyone asking for money to “recover” crypto is usually running the next scam.
- If you sent a large amount, consider filing a police report
- Bring your documentation, transaction hash, and the destination address.
- You may also want to consult an attorney who understands cybercrime reporting in your region.
- Tell others, briefly and clearly
- If you found the link on social media, warn people in the same place you saw it.
- Keep it factual: “This is a send-first crypto giveaway scam. Do not send funds.”
The Bottom Line
The Elon Musk WLF tokens giveaway scam is not complicated once you strip away the design.
It is a dressed-up request for crypto that relies on one irreversible action: you sending money first. The “tokens left” counter, the “recent transactions” feed, the comment section, the “airdrop registration” form, and the confident branding are all there to make that one action feel normal.
A real giveaway does not need your Bitcoin to give you tokens.
If a page promises to double your crypto, asks you to send to a wallet address, and claims you will get paid back instantly, you are not looking at an opportunity. You are looking at a theft mechanism with good web design.
If you already sent funds, focus on damage control: stop sending more, secure your accounts, document the incident, and report it. And if you are still on the fence, treat that hesitation as your best signal. In crypto, the safest giveaways are the ones that do not require you to transfer money to “claim” free money.
FAQ
Is the Elon Musk WLF tokens giveaway real?
No. A legitimate giveaway does not require you to send crypto to a wallet address first in order to receive more back. The “send X and get 2x back instantly” format is a well-known crypto scam pattern.
Does Elon Musk have anything to do with this?
No credible evidence supports that. Scammers frequently use famous names and platform themes (like “X giveaway”) to borrow trust and make a fake promotion feel official.
What is WLF in this scam?
In these campaigns, “WLF” is presented as a token tied to World Liberty Financial. Scammers use token names, logos, and branding to make the page look legitimate, but the token claim itself does not make the giveaway real.
Why does it claim “$250,000,000,000 worth of WLF tokens”?
Huge numbers create urgency and excitement. The goal is to overwhelm your skepticism and push you to act quickly. Extreme giveaway amounts are common in these scams because they are marketing bait, not proof.
The page shows “recent transactions.” Does that prove people are getting paid?
No. Those “recent transactions” feeds are often fake, randomly generated, or manipulated. Even if a real transaction appears on-chain, that only proves money moved, not that a giveaway is legitimate or that people are receiving 2x back.
What does “tokens left” mean?
It is a pressure tactic. Counters like “tokens left” are easy to fake and are used to create scarcity so you do not pause to verify anything.
I sent crypto. Can I get it back?
Usually, no. Crypto transfers are generally irreversible. Your best chance is if you sent funds from an exchange and the exchange can help with reporting or flagging, but recovery is still uncommon.
I sent crypto from an exchange. What should I do right now?
Contact the exchange’s support immediately and provide:
- The destination address shown on the scam page
- Your transaction hash (TXID)
- The amount and time sent
Ask if they can flag the address, assist with compliance reporting, or advise on next steps.
I sent crypto from my own wallet. Am I at risk of losing everything?
If you only sent a transfer to their address, they cannot automatically drain your wallet just from receiving funds.
However, if you connected your wallet to the site or approved anything, your wallet may be at risk. In that case, move remaining assets to a new wallet and revoke any suspicious token approvals.
The site says I need to “register for the airdrop” after sending. Should I do it?
No. That step is typically used to keep you engaged, collect details, and set up additional payment requests. It does not help you receive anything.
They are asking me to send a “verification” payment or a “gas fee.” Is that normal?
No. That is a second-stage scam. Once you send the first amount, scammers often claim you must send more to unlock the payout. Do not send anything else.
What if I entered my email address or personal details on the page?
Assume you may get targeted again. Take these steps:
- Change passwords if you reused them anywhere
- Enable 2FA on your email and exchange accounts
- Watch for phishing emails and “recovery” scam messages
Can I report the wallet address?
Yes. You can report the address to:
- Your exchange (if applicable)
- Chain explorers that allow address reporting
- Scam and abuse databases
Reporting will not usually recover funds, but it can help protect other people.
Are there warning signs that confirm it is a scam?
Common red flags include:
- “Send crypto and get 2x back” promises
- “Verified wallet address” language
- Giant giveaway sums with no verifiable source
- Fake urgency: “tokens left,” countdowns, limited time claims
- A “recent transactions” feed used as social proof
- Comments claiming huge payouts with no proof
- Requests for a second payment (verification, gas, upgrade)
How do real token airdrops work, then?
Real airdrops do not require you to send crypto to receive more back. Legit distributions usually involve eligibility rules, a claim process on official project channels, and clear documentation. The moment you are asked to transfer funds first, treat it as a scam.
What is the most important thing to remember?
If a “giveaway” requires you to send crypto to a wallet address, it is not a giveaway. It is a transfer to someone who controls that wallet, and you are trusting them to send something back. In scams like this, they do not.







