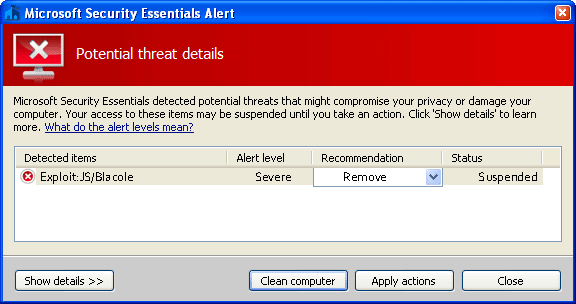
JS/Exploit-Blacole (Exploit:JS/Blacole) is malicious Java code that exploits a vulnerability in the Java Runtime Environment component of Oracle Java SE and Java for Business that allows the execution of arbitrary code.
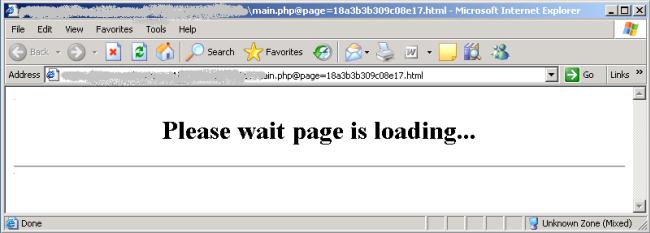
JS/Exploit-Blacole was developed in Russia and is used by hackers to infect computers with old versions of Java via malicious scripts planted on compromised websites. When the page is visited by a user running vulnerable versions of Java, the malicious Java class runs and allows the execution of arbitrary code.
In the wild, this exploit was observed to be distributed within a Java archive file named “g43kb6j34kblq6jh34kb6j3kl4.jar” and within a collection of other Java class malware, as in the following example list of files:
- ExtResolution.class [Detected as Exploit-Blacole]
- Image.class [Detected as Exploit-Blacole]
- Mover.class [Detected as Exploit-Blacole]
- TContainer.class [Detected as Exploit-Blacole]
- Zoom.class [Detected as Generic Exploit!c2w]
If your computer is infected with JS/Exploit-Blacole,you must assume that your passwords (for email, banking, or other online accounts) have been stolen, that any credit card details you have given in online transactions have been copied, that your bank account details (if you do online banking) have been stolen. You may have been used to send spam, your machine may be under the control of a botnet herder, you could still have malware running on your machine.
While most antivirus products will detect using their heuristic engine JS/Exploit-Blacole,some security products may have some issues while trying to remove this infection.
JS/Exploit-Blacole – Virus Removal Guide
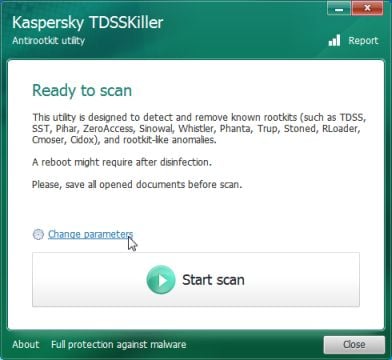
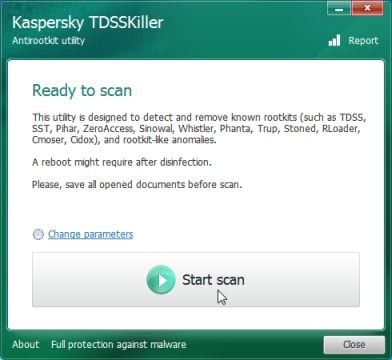
STEP 1: Remove JS/Exploit-Blacole bootkit with Kaspersky TDSSKiller
JS/Exploit-Blacole has installed a bootkit, which has infected your Master Boot Record and it’s causing browser redirects.To remove this infection, we need to run a system scan with Kaspersky TDSSKiller.
- Please download the latest official version of Kaspersky TDSSKiller.
KASPERSKY TDSSKILLER DOWNLOAD LINK(This link will automatically download Kaspersky TDSSKiller on your computer.) - Before you can run Kaspersky TDSSKiller, you first need to rename it so that
you can get it to run. To do this, right-click on the TDSSKiller.exe icon and select Rename.
Edit the name of the file from TDSSKiller.exe to iexplore.exe, and then double-click on it to launch. - Kaspersky TDSSKiller will now start and display the welcome screen and we will need to click on Change Parameters.
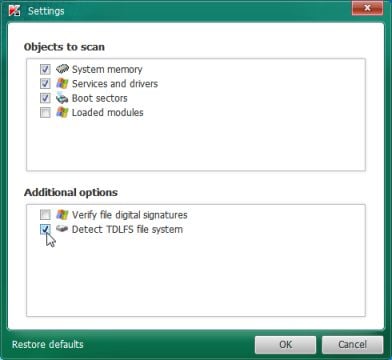
- In the new open window,we will need to enable Detect TDLFS file system, then click on OK.
- Next,we will need to start a scan so you’ll need to press the Start Scan button.
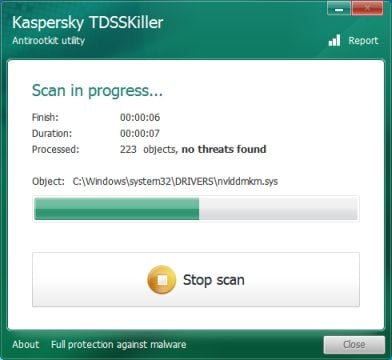
- Kaspersky TDSSKiller will now scan your computer for any bootkits infection.
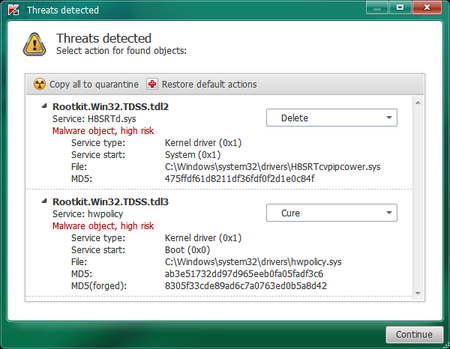
- When the scan has finished it will display a result screen stating whether or not the infection was found on your computer. If it was found it will display a screen similar to the one below.
- To remove the infection simply click on the Continue button and TDSSKiller will attempt to clean the infection.A reboot will be require to completely remove any infection from your system.
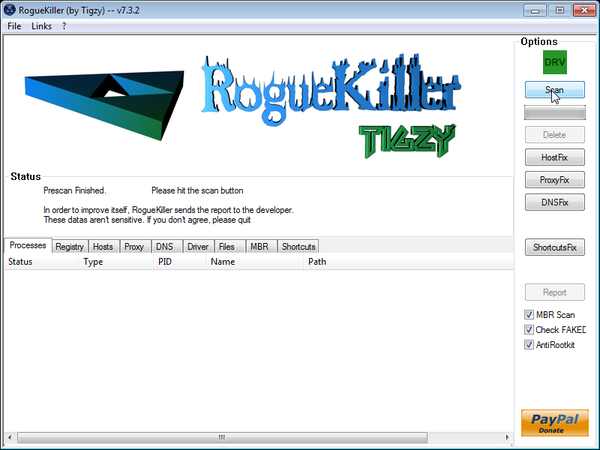
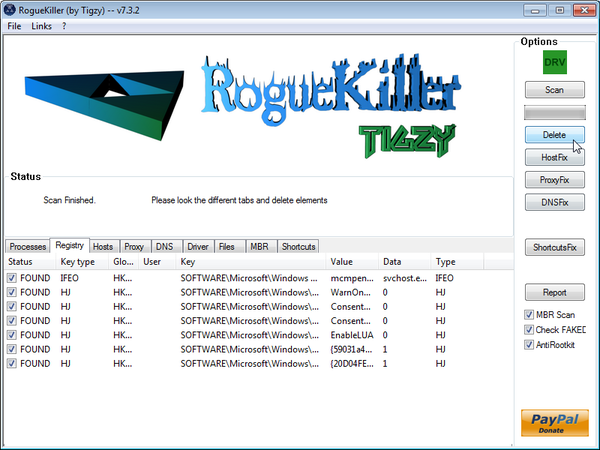
STEP 2 : Remove JS/Exploit-Blacole malicious registry keys with RogueKiller
- Please download the latest official version of RogueKiller.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Start button to perform a system scan.
- After the scan has completed, press the Delete button to remove any malicious registry keys.
STEP 3: Remove JS/Exploit-Blacole malicious files with Malwarebytes Anti-Malware FREE
Malwarebytes Anti-Malware is a powerfull on-demand scanner which will remove malware malicious files from your computer.
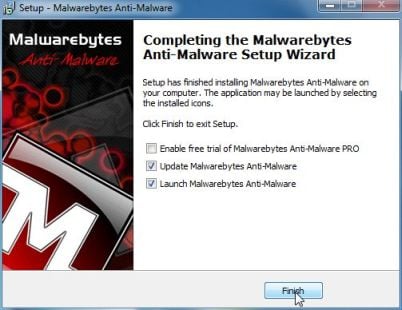
- You can download Malwarebytes Anti-Malware Free from the below link,then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK(This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
DO NOT make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked,then click on the Finish button.
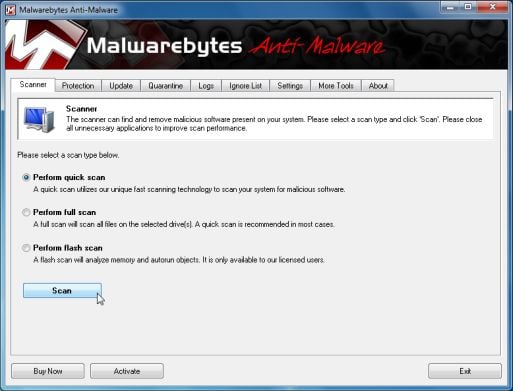
- On the Scanner tab,select Perform quick scan and then click on the Scan button to start scanning your computer.
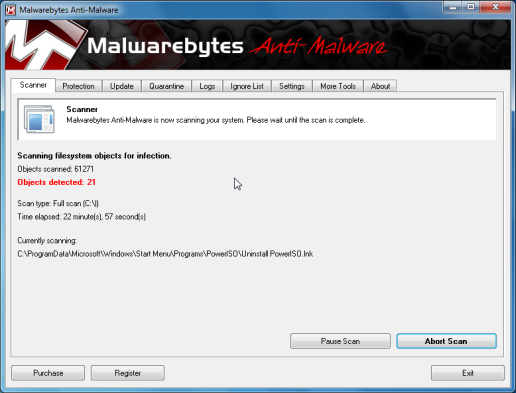
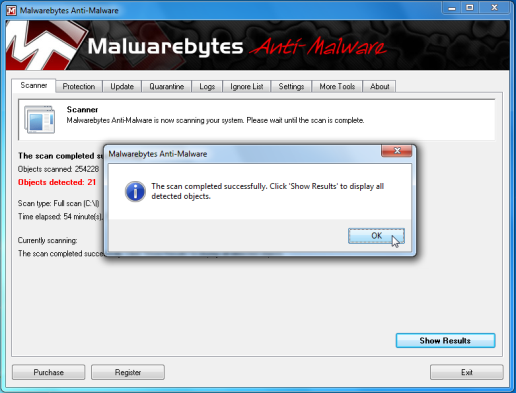
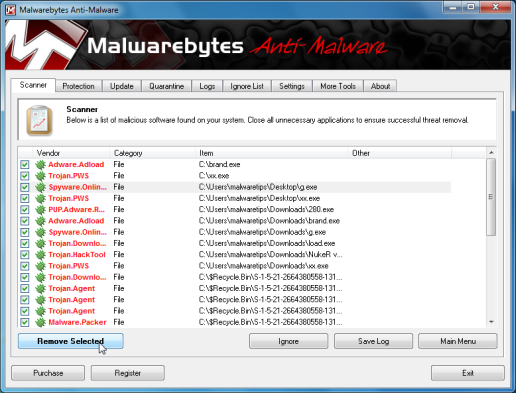
- Malwarebytes’ Anti-Malware will now start scanning your computer for JS/Exploit-Blacole malicious files as shown below.
- When the Malwarebytes scan will be completed,click on Show Result.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
- After your computer will restart in Normal mode, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
STEP 4: Remove JS/Exploit-Blacole rootkit with HitmanPro
In some cases,JS/Exploit-Blacole will install a rootkit on victims computer which will cause browser redirects,to remove this infection we will use HitmanPro.
- Download HitmanPro from the below link,then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for JS/Exploit-Blacole malicious files as seen in the image below.
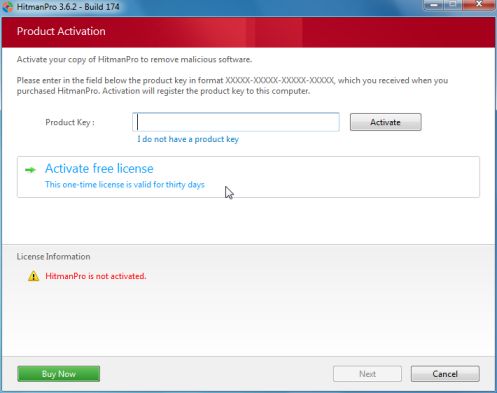
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.
- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
STEP 5: Double check for any left over infections on your computer
If want to make another check for any left over malicious files,you can run a scan with the following tools:
STEP A: Run a scan with Eset Online Scanner.
- Download ESET Online Scanner utility.
ESET Online Scanner Download Link (This link will automatically download ESET Online Scanner on your computer.) - Double click on the Eset installer program (esetsmartinstaller_enu.exe).
- Check Yes, I accept the Terms of Use
- Click the Start button.
- Check Scan archives
- Push the Start button.
- ESET will then download updates for itself, install itself, and begin scanning your computer. Please be patient as this can take some time.
- When the scan completes, push Finish
STEP B: Run a scan with Emsisoft Emergency Kit.
- Please download the latest official version of Emsisoft Emergency Kit.
EMSISOFT EMERGENCY KIT DOWNLOAD LINK (This link will open a download page in a new window from where you can download Emsisoft Emergency Kit) - After the download process will finish , you’ll need to unpack EmsisoftEmergencyKit.zip and then double click on EmergencyKitScanner.bat
- A pop-up will prompt you to update Emsisoft Emergency Kit , please click the “Yes” button.After the Update process has completed , put the mouse cursor over the “Menu” tab on the left and click-on “Scan PC“.
- Select “Smart scan” and click-on the below “SCAN” button.When the scan will be completed , you will be presented with a screen showing you the malware infections that Emsisoft Emergency Kit has detected.Make sure that everything is Checked (ticked) and click on the ‘Quarantine selected objects‘ button.
Kaspersky TDSSKiller and RogueKiller can be removed by deleting the utilities.
We strongly recommend that you keep Malwarebytes Anti-Malware and HitmanPro installed on your machine and run regular scans with this tools.If you however,wish to remove them, you can go into the Add or Remove programs and uninstall these two on-demand scanners.
Because JS/Exploit-Blacole is designed to steal your personal information, we recommend that you change your passwords for your online accounts and if you have used your credit card while this trojan was on your computer, contact the bank and let them know that you might be be victim of a phishing attack.












Thanks a ton guys. keep up the great work!
After days of frustration this site has me back on the net
with thanks
Darryl
Hi,
We are greatly thanksfull for this page and work you’ve done.
It was helpfull and we managed to clean deeply our computer.
We were first attacked by un UKash virus.
After we could restore from a former system save point, we scanned and found three malware : exploit:Java/-blacole.ga, CVE-2012-1723.gen!A and virtool:win32\ceeinject.
We found this page and followed the indications and still found other 4 viruses wich we could delete.
Thanks a lot again.
Stephane & Marie