The CIA Special Agent 767 is a Trojan Horse that locks your Windows desktop, and states that the files on the computer have been encrypted and you need to pay $100 (in bitcoins) to recover them.
The CIA Special Agent 767 is distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission of knowledge.
The CIA Special Agent 767 may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software. The CIA Special Agent 767 is also prevalent on peer-to-peer file sharing websites and is often packaged with pirated or illegally acquired software.
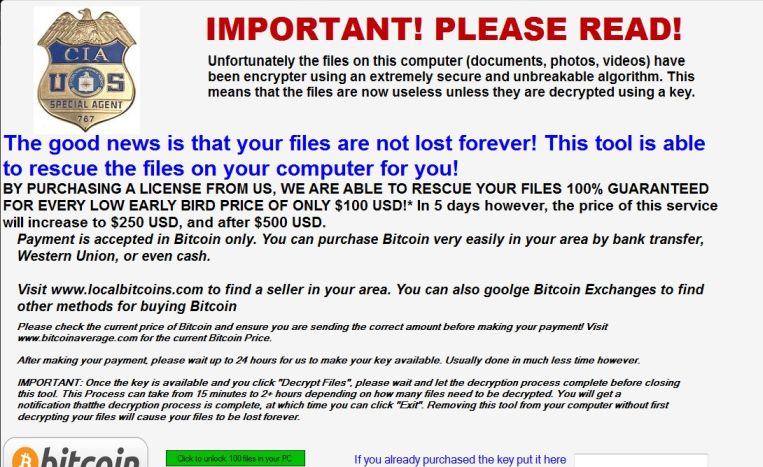
When a computer is infected, the CIA Special Agent 767 malware displays a screen that pretends to be form the CIA that is designed to scare you into paying for a fake tool. This screen will overlay the desktop and state that your files have been encrypted and you have 5 days to pay $100 in bitcoins to recover your documents.
The CIA Special Agent 767 malware state that once they verify the payment the computer will automatically be unlocked and you will be able to access your Windows desktop again.
While the text in these messages can be scary, the good news is that the CIA Special Agent 767 malware will not delete or encrypt any files, and can be removed without paying the ransomware.
The text of the CIA Special Agent 767 screen locker is:
IMPORTANT! PLEASE READ! Unfortunately the files on this computer (documents, photos, videos) have been encrypter using an extremely secure and unbreakable algorithm.
This means that the files are now useless unless they are decrypted using a key.
The good news is that your files are not lost forever! This tool is able to rescue the files on your computer for you!BY PURCHASING A LICENSE FROM US, WE ARE ABLE TO RESCUE YOUR FILES 100% GUARANTEED FOR EVERY LOW EARLY BIRD PRICE OF ONLY $100 USD!*
In 5 days however, the price of this service will increase to $250 USD, and after $500 USD. Payment is accepted in Bitcoin only. You can purchase Bitcoin very easily in your area by bank transfer, Western Union, or even cash. Visit www.localbitcoins.com to find a seller in your area. You can also goolge Bitcoin Exchanges to find other methods for buying Bitcoin Please check the current price of Bitcoin and ensure you are sending the correct amount before making your payment!
Visit www.bitcoinaverage.com for the current Bitcoin Price. After making your payment, please wait up to 24 hours for us to make your key available. Usually done in much less time however. IMPORTANT: Once the key is available and you click \”Decrypt Files\”, please wait and let the decryption process complete before closing this tool. This Process can take from 15 minutes to 2+ hours depending on how many files need to be decrypted. You will get a notification thatthe decryption process is complete, at which time you can click \”Exit\”. Removing this tool from your computer without first decrypting your files will cause your files to be lost forever. Bitcoin Address: (edited)*Please note that early bird qualification is determined from the date that this tool was first run as recorded on our servers.
How to remove “CIA Special Agent 767” lock screen (Removal Guide)
-
To remove the “This user is disabled” lock screen, follow these steps:
- STEP 1: Remove the CIA Special Agent 767 lock screen
- STEP 2: Use Malwarebytes Anti-Malware to remove CIA Special Agent 767 malware
- STEP 3: Double-check for malware with HitmanPro
STEP 1 : Remove the CIA Special Agent 767 lock screen
In this first step we will remove the “CIA Special Agent 767” lock screen from Windows.
Because there are many versions of this malware, which behave differently, we have provided multiple options to remove the malicious lock screen.
OPTION 1: Remove the malicious lock screen with HitmanPro.Kickstart
HitmanPro.Kickstart is the solution against ransomware and other persistent malware that has taken your computer hostage or prevents normal computer use.
Because this infection has locked you out of your computer, we will need to create a bootable USB drive that contains the HitmanPro.Kickstart program. We will then boot the infected machine with the HitmanPro.Kickstart USB drive, and use the program to clean the infection.
- Using a “clean” (non-infected) computer, please download HitmanPro from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Once HitmanPro has been downloaded on the clean machine, insert an USB flash drive and double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows).
To create a bootable HitmanPro USB drive, please follow the instructions from this video:
- Once you have created the bootable HitmanPro.Kickstart USB drive, insert the USB into the computer infected with the “This user is disabled” lock screen.
- After you have inserted the HitmanPro Kickstart USB drive, boot your machine from the HitmanPro.Kickstart USB as seen in the below video.
- The malicious lock screen should be removed from your machine. It’s recommended that you perform a system scan with Malwarebytes and HitmanPro as see in the below steps.
OPTION 2: Start your computer in Safe Mode with Networking
If the above options did not work for your machine, then we will need to start the computer in Safe Mode with Networking to bypass the lock screen.
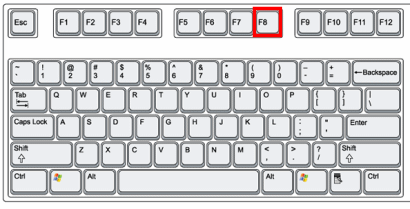
- Immediately after the computer is powered on or restarted (usually after you hear your computer beep), tap the F8 key in 1 second intervals.
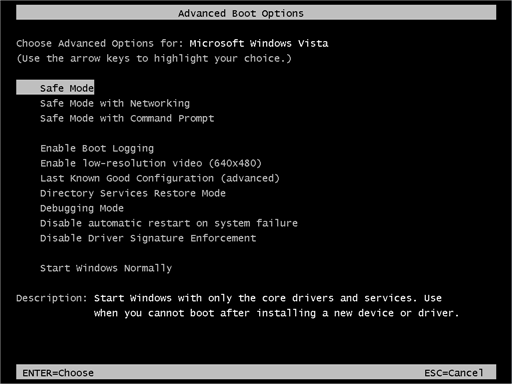
- After your computer displays hardware information and runs a memory test, the Advanced Boot Options menu will appear.
- Use the arrow keys to select Safe Mode with Networking and press ENTER.
- After you have started your machine in Safe Mode with Networking, run a system scan with Malwarebytes Anti-Malware as seen in the below step.
STEP 2: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which should remove the CIA Special Agent 767 virus from your computer. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
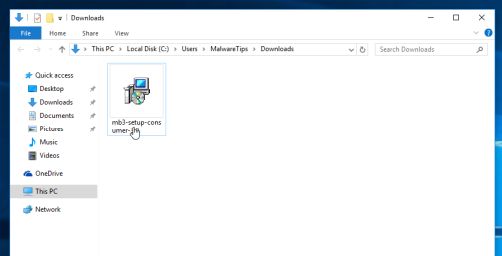
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link open a new page from where you can download “Malwarebytes Anti-Malware”) - When Malwarebytes has finished downloading, double-click on the “mb3-setup-consumer” file to install Malwarebytes Anti-Malware on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow Malwarebytes to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
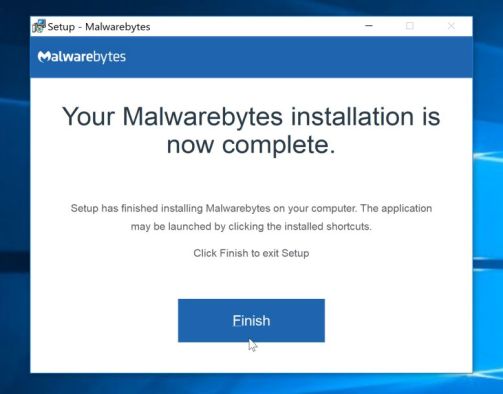
- When the Malwarebytes installation begins, you will see the Malwarebytes Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
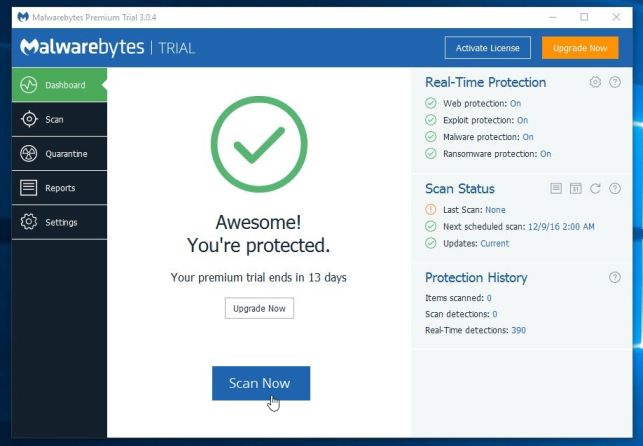
- Once installed, Malwarebytes will automatically start and update the antivirus database. To start a system scan you can click on the “Scan Now” button.
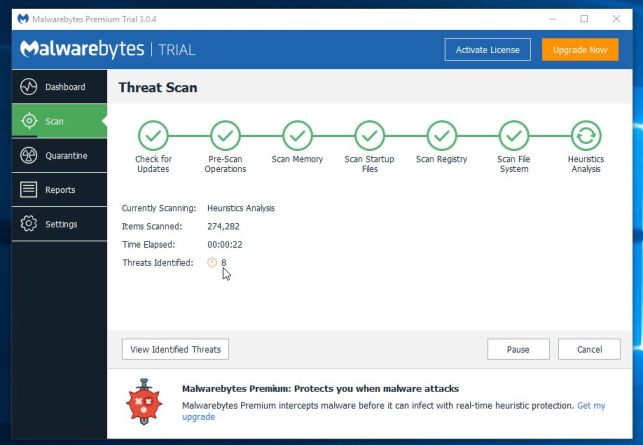
- Malwarebytes Anti-Malware will now start scanning your computer for malicious programs.
This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
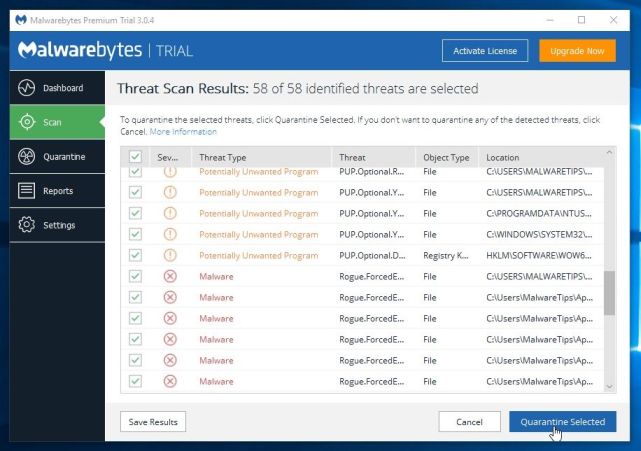
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected.
To remove the malicious programs that Malwarebytes has found, click on the “Quarantine Selected” button.
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found.
To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes Anti-Malware and continue with the rest of the instructions.
STEP 3: Double-check for malware with HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
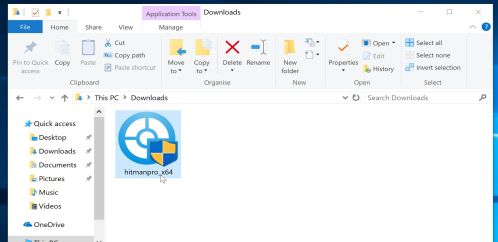
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - When HitmanPro has finished downloading, double-click on the “hitmanpro” file to install this program on your computer.
You may be presented with an User Account Control pop-up asking if you want to allow HitmanPro to make changes to your device. If this happens, you should click “Yes” to continue with the installation.
- When the program starts you will be presented with the start screen as shown below. Now click on the Next button to continue with the scan process.
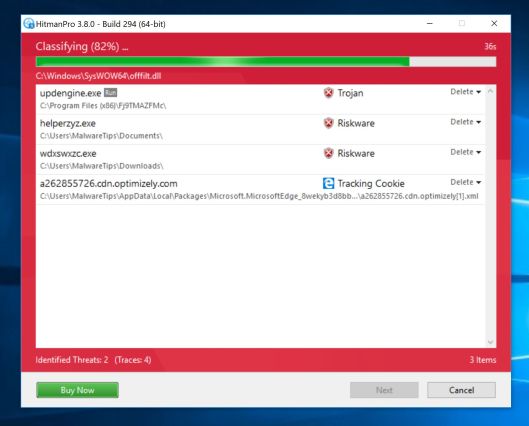
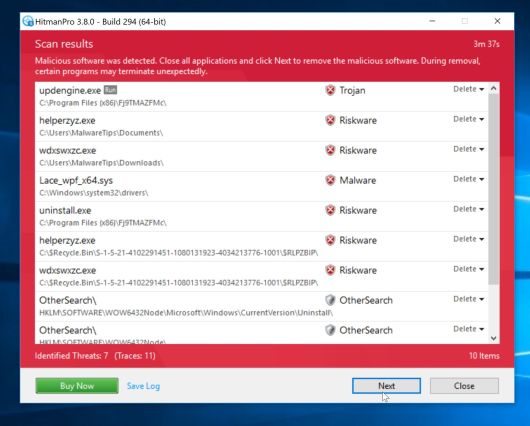
- HitmanPro will now begin to scan your computer for malware.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
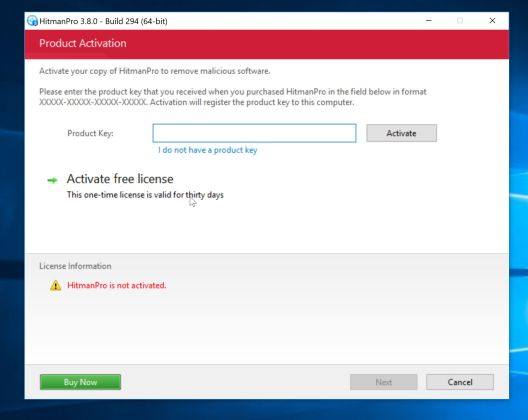
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
If you are still experiencing problems while trying to remove CIA Special Agent 767 screen locker from your computer, please do one of the following:
- Run a system scan with Zemana AntiMalware
- Ask for free help in our Malware Removal Assistance forum.