PrimeAurora is a potentially unwanted program that injects advertisements into websites you visit and changes your browser’s default search engine and homepage. PrimeAurora is commonly bundled with other programs that you download from the Internet.

What is PrimeAurora?
PrimeAurora is a malicious program that hijacks your browser homepage and search engine and displays unwanted advertisements not originating from the sites you are browsing. To do this, PrimeAurora uses a browser extension or program.
When installed on a computer, the PrimeAurora browser hijacker will redirect your browser search queries through PrimeAurora Search, which will redirect to search result pages from search.yahoo.com. This is most likely done to generate advertising revenue by using Yahoo Search for its search results.
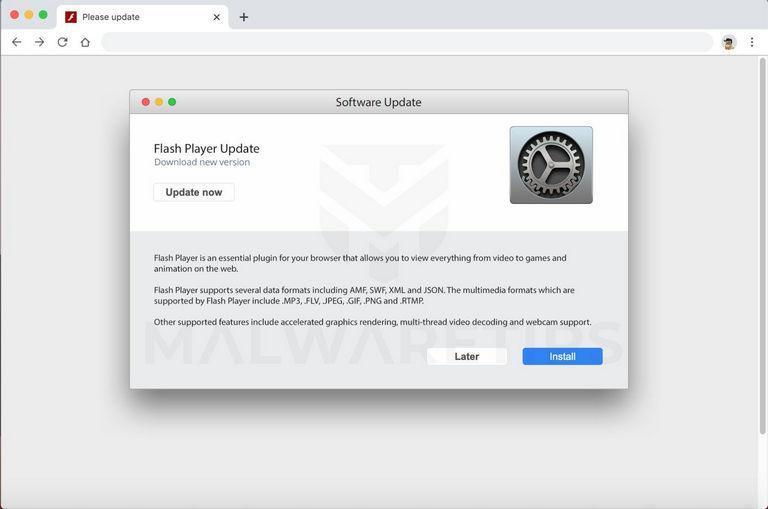
PrimeAurora will also open new tabs in the browser that display advertisements trying to sell software, push fake software updates, and tech support scams.
When the PrimeAurora browser hijacker is installed on a computer, common symptoms include:
- Your web browser’s default search engine is PrimeAurora Search
- Your browser’s search queries are redirected through PrimeAurora Search
- The “PrimeAurora” browser extension or program is installed on your Mac
How was PrimeAurora installed on my computer?
PrimeAurora is installed by the users, whether that is knowingly or not. Often, this type of program is offered through advertisements or bundled with other software, leaving the user puzzled about where this software came from.
Unfortunately, some free downloads do not adequately disclose that other software will also be installed and you may find that you have installed PrimeAurora without your knowledge.
If you do not know how PrimeAurora was installed or are concerned other extensions or unwanted programs may be installed on your Mac, you can use the removal guide below.
Removal instructions for PrimeAurora browser hijacker
Please perform all the steps in the correct order. If you have any questions or doubts at any point, stop and ask for our assistance.
- STEP 1: Remove malicious Profiles from your Mac
- STEP 2: Remove PrimeAurora from Mac
- STEP 3: Use Malwarebytes for Mac to remove PrimeAurora and other malware
- STEP 4: Remove PrimeAurora from Safari, Chrome, or Firefox
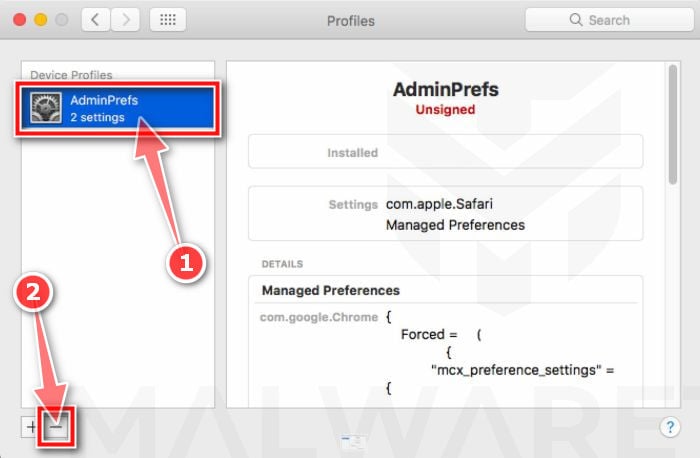
STEP 1: Remove malicious Profiles from your Mac
Profiles are used by IT admins in businesses to control the behavior of their Macs. These profiles can configure a Mac to do many different things, some of which are not otherwise possible.
When it comes to home users, adware and browser hijackers are using the configuration profile to prevent users from removing malicious programs from the computer. This also prevents the user from changing that behavior in the browser’s settings.
In this first step, we will check your computer to see if any configuration profiles are installed. To do this, follow the below steps:
-
Open “System Preferences”
From the Apple menu, select System Preferences.
-
Search for “Profiles”
When the System Preferences window opens, search for the Profiles icon.
If there isn’t a Profiles icon, you don’t have any profiles installed, which is normal and you can continue with the next steps. -
Remove the malicious profiles
If there’s a Profile icon, click on it and select any suspicious profile that you want to remove, and then press the – (minus) button. Click Remove to remove the profile.
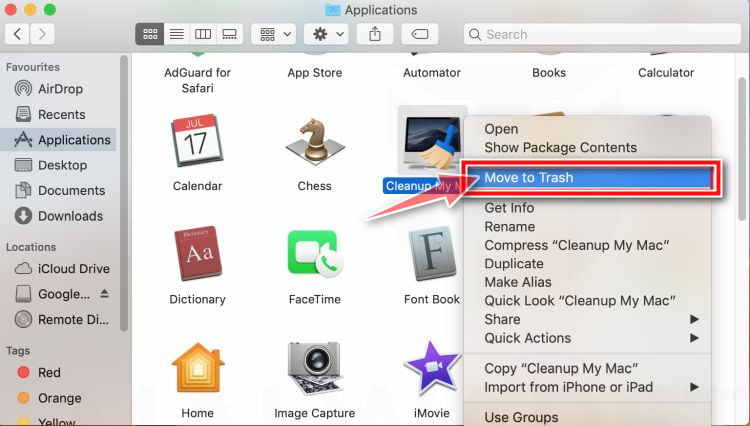
STEP 2: Remove PrimeAurora from Mac
In this next step, we will uninstall PrimeAurora and remove its files from your computer. Sometimes the PrimeAurora browser hijacker can have a usable Uninstall entry that can be used to remove it.
-
Quit “PrimeAurora”
On the Apple menu bar, in the top-right corner, if you see the PrimeAurora icon, click on it and then select Quit.
-
Open “Finder”
Click the Finder application on your dock.
-
Click on “Applications”
In the Finder left pane, click on “Applications“.
-
Find and remove PrimeAurora.
The “Applications” screen will be displayed with a list of all the apps installed on your device. Scroll through the list until you find PrimeAurora, right-click it, and then click “Move to Trash”.
There may be other malicious programs installed on your Mac. Look out for any suspicious program that could be behind all the drama – anything you don’t remember downloading or that doesn’t sound like a genuine program.
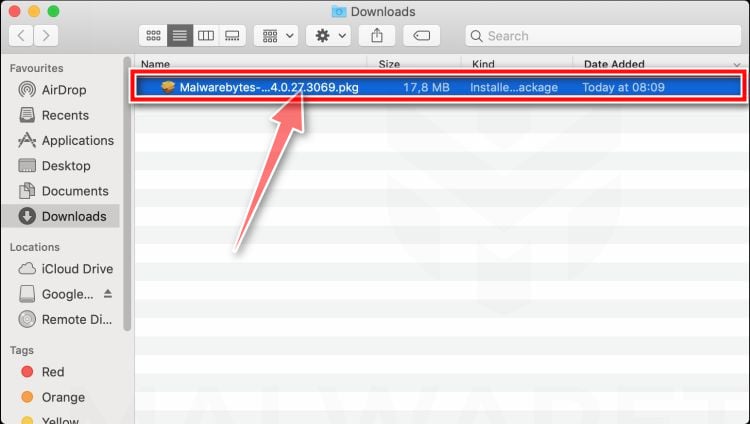
STEP 3: Use Malwarebytes for Mac to remove PrimeAurora and other malware
In this third step, we will download, install and run a scan with Malwarebytes for Mac to remove PrimeAurora and other malware from your Mac.
Malwarebytes for Mac is an on-demand scanner that takes out malware, adware, spyware, and other threats before they can infect your machine and ruin your day.
-
Download Malwarebytes for Mac.
You can download Malwarebytes for Mac by clicking the link below.
MALWAREBYTES FOR MAC DOWNLOAD LINK
(The above link will open a new page from where you can download Malwarebytes for Mac) -
Double-click on the Malwarebytes setup file.
When Malwarebytes has finished downloading, double-click on the setup file to install Malwarebytes on your computer. In most cases, downloaded files are saved to the Downloads folder.
-
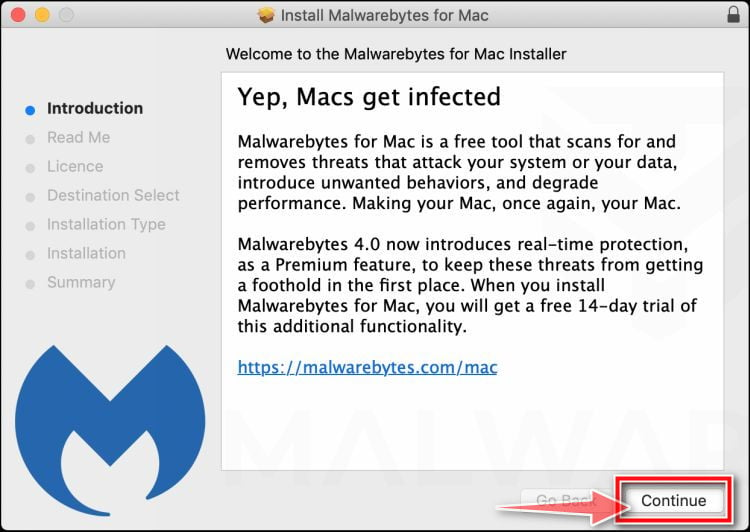
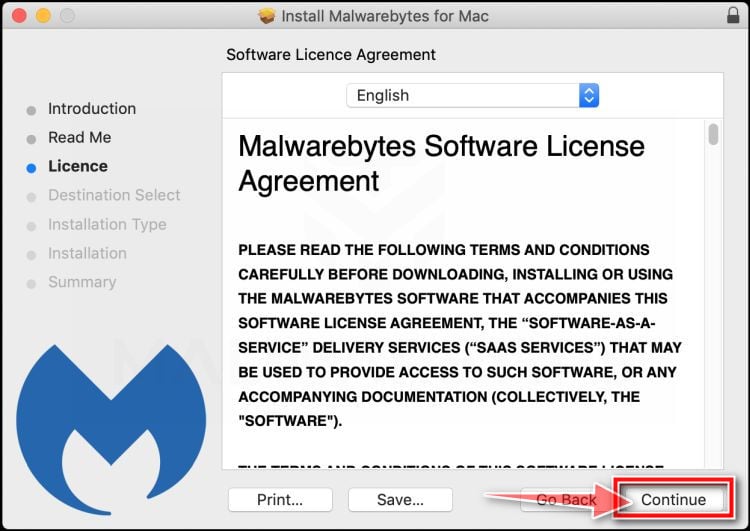
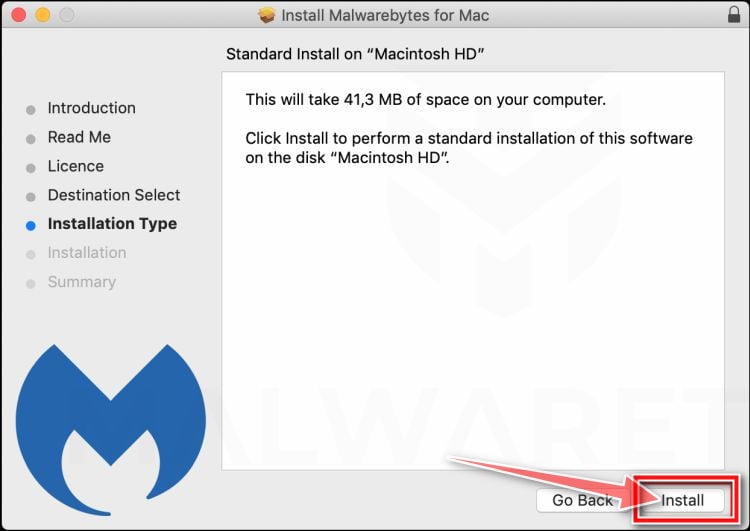
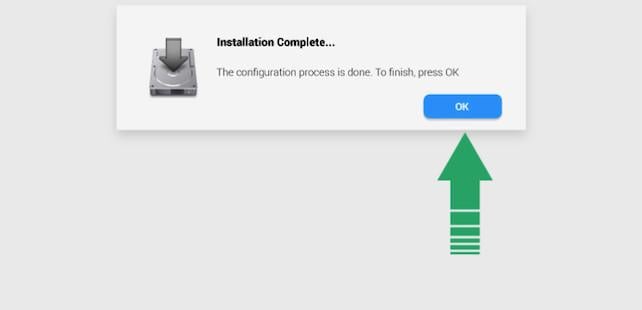
Follow the on-screen prompts to install Malwarebytes.
When the Malwarebytes installation begins, you will see the Malwarebytes for Mac Installer which will guide you through the installation process. Click “Continue“, then keep following the prompts to continue with the installation process.
When your Malwarebytes installation completes, the program opens to the Welcome to Malwarebytes screen. Click the “Get started” button.
-
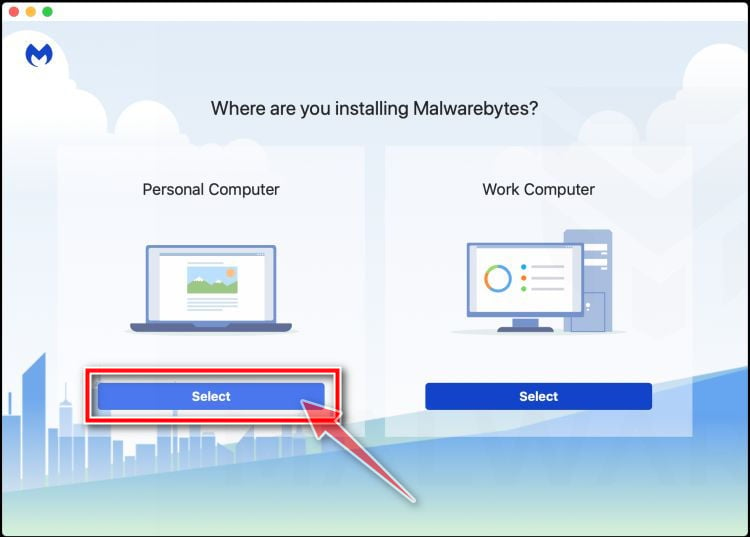
Select “Personal Computer” or “Work Computer”.
The Malwarebytes Welcome screen will first ask you what type of computer are you installing this program, click either Personal Computer or Work Computer.
-
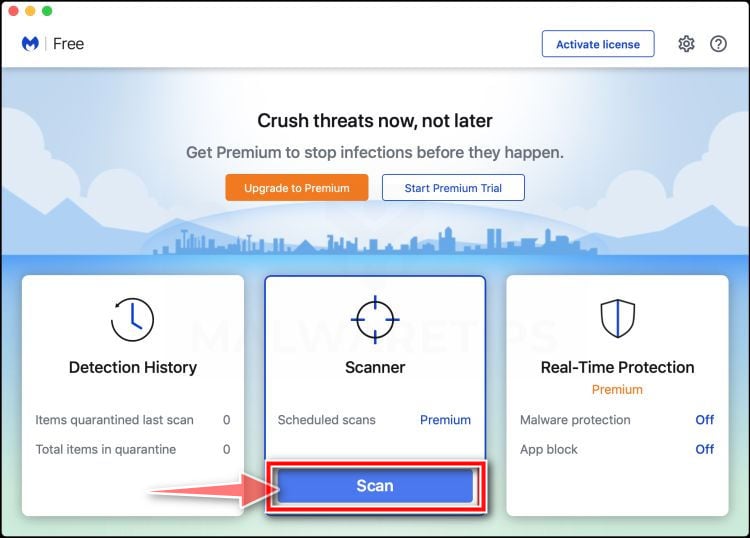
Click on “Scan”.
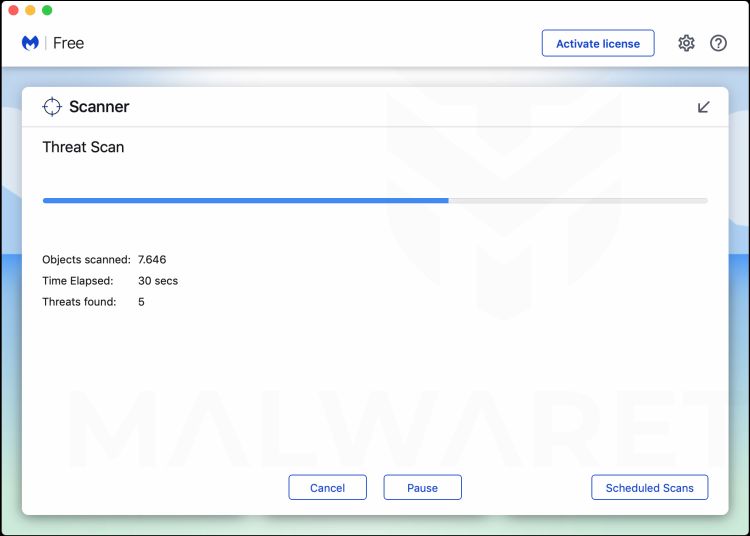
To scan your computer with Malwarebytes, click on the “Scan” button. Malwarebytes will automatically update the antivirus database and start scanning your computer for the PrimeAurora malware.
-
Wait for the Malwarebytes scan to complete.
Malwarebytes will scan your computer for PrimeAurora and other malicious programs. This process can take a few minutes, so we suggest you do something else and periodically check on the status of the scan to see when it is finished.
-
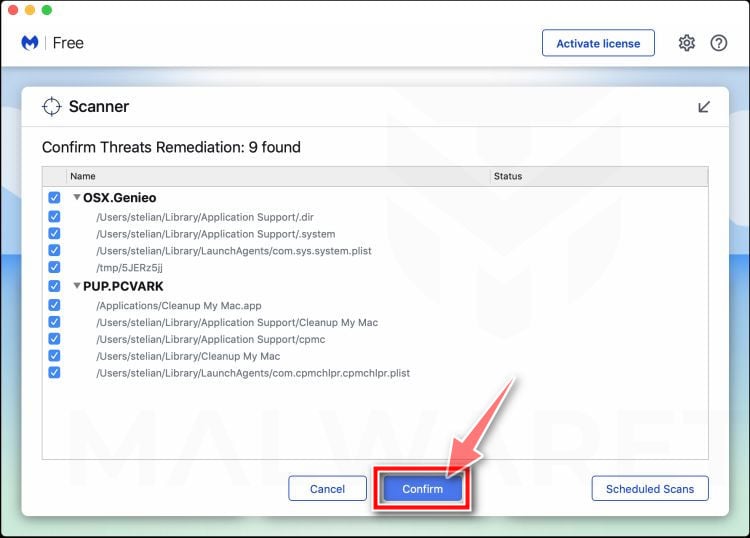
Click on “Quarantine”.
When the scan has been completed, you will be presented with a screen showing the malware infections that Malwarebytes has detected. To remove PrimeAurora and other malicious programs that Malwarebytes has found, click on the “Quarantine” button.
-
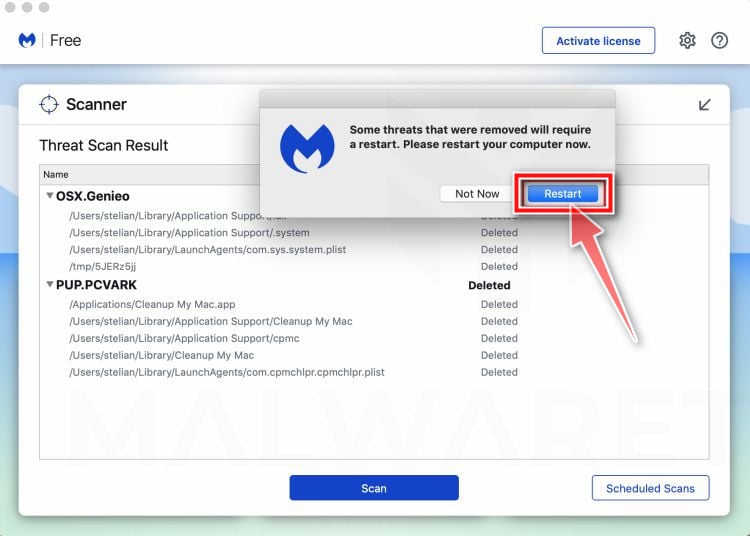
Restart computer.
Malwarebytes will now remove PrimeAurora and other malicious files that it has found. To complete the malware removal process, Malwarebytes may ask you to restart your computer.
When the malware removal process is complete, you can close Malwarebytes and continue with the rest of the instructions.
STEP 4: Remove PrimeAurora from Safari, Chrome, or Firefox
In this final step, we will remove the PrimeAurora browser extension, its search engine, and any spam browser notifications.
Remove PrimeAurora browser hijacker from Safari
To remove the PrimeAurora browser hijacker from Safari we will check if there are any malicious extensions installeded on your browser and what settings have been changed by this malicious program.
-
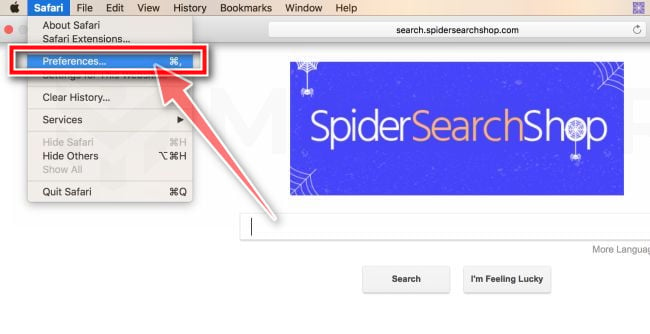
Go to Safari’s “Preferences”.
On the menu bar, click the “Safari” menu and select “Preferences”.
-
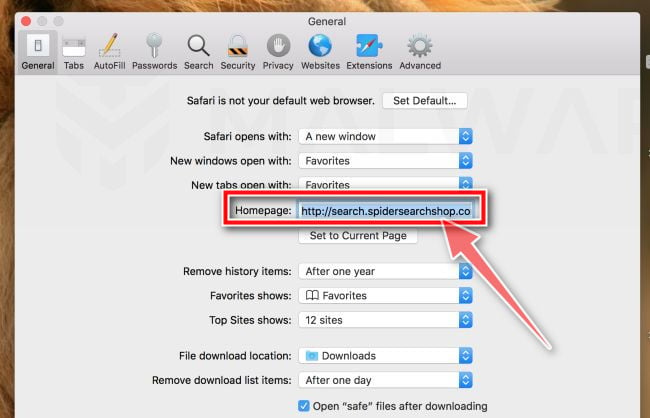
Check Homepage.
This will open a new window with your Safari preferences, opened to the “General” tab. Some browser hijackers may change your default homepage, so in the Homepage field make sure it’s a web page you want to use as your start-up page.
-
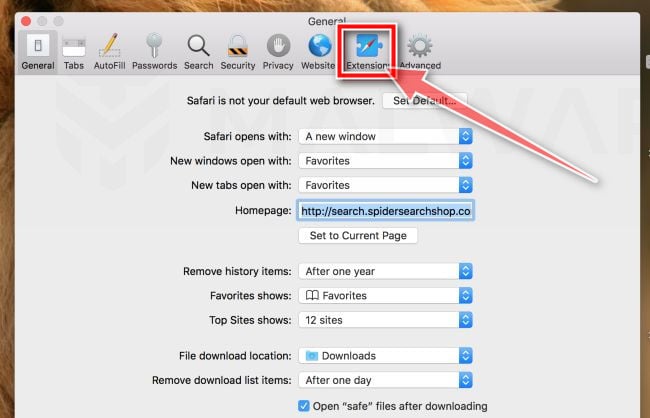
Click “Extensions”
Next, click on the “Extensions” tab.
-
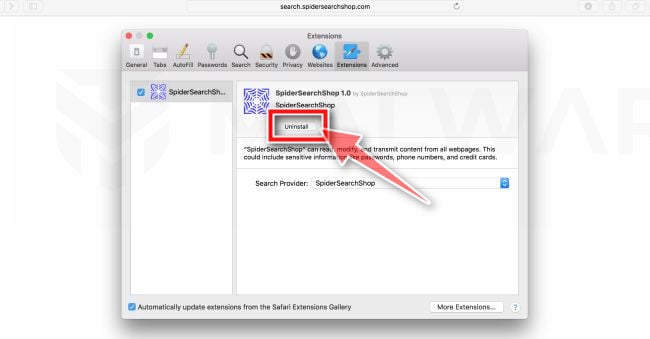
Find and uninstall PrimeAurora.
The “Extensions” screen will be displayed with a list of all the extensions installed on Safari. Scroll through the list until you find the PrimeAurora extension, and then click on “Uninstall” to remove it.
There may be other malicious extensions installed. Look out for any suspicious browser extension that could be behind all the drama – anything you don’t remember downloading or that doesn’t sound like a genuine extension. By default, there are no extensions installed on Safari so it’s safe to remove any extension. -
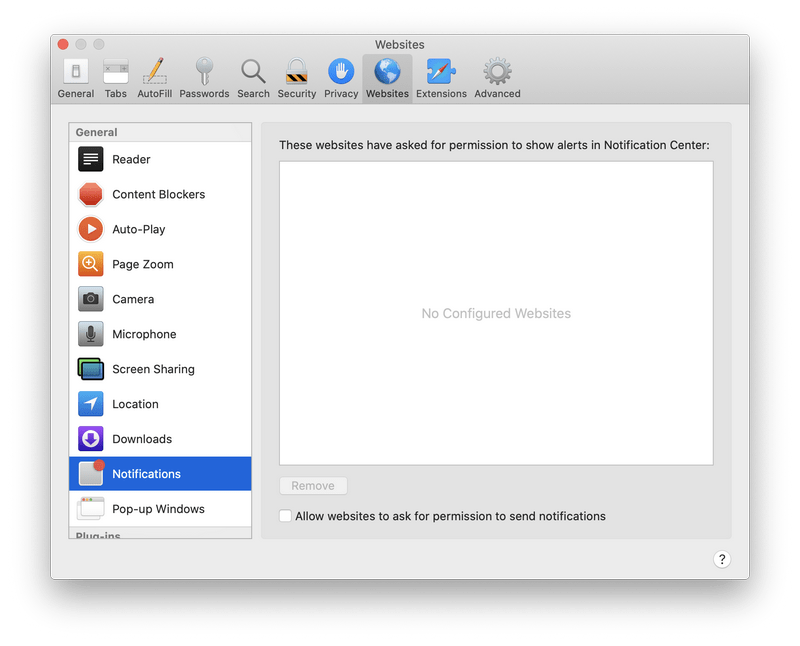
Remove spam notifications ads
Click Preferences, click Websites, then click Notifications. Deselect “Allow websites to ask for permission to send push notifications”.
If the above steps didn’t help you remove the PrimeAurora browser hijacker from Safari, you can follow the below steps:
-
Workaround for greyed out Safari’s homepage
In some cases, after being changed by browser hijackers or malware, Safari’s home page can become stuck (greyed out). You will be able to edit the Homepage field in Safari’s preferences, but the change will not stick. This appears to be a bug, and there is an odd workaround. Try this:- In Safari, choose Preferences from the Safari menu.
- In the window that opens, click the General icon (if necessary)
- Enter your desired home page in the “Homepage” field, but DO NOT press return!
- At the top of the window, click any of the other icons (eg, Tabs, AutoFill, etc).
- You may see a prompt asking for confirmation for changing the home page. If so, confirm.
- Switch back to the General page and check to make sure the home page has been changed.
-
Delete Safari’s preferences file to remove malicious changes
Some malicious programs are known to install managed preferences to set the homepage and search engine settings in Safari. If the above options didn’t help you remove the malicious redirects, we’ll need to delete Safari’s preferences. To do this, follow the below steps:- Quit Safari
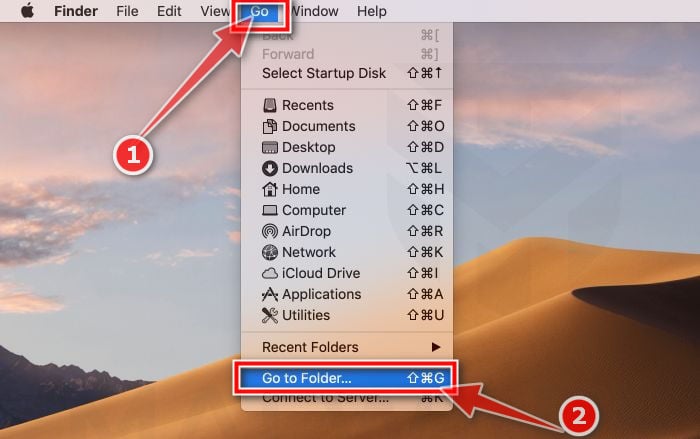
- Click the desktop to make sure you’re in the Finder, choose “Go” then click on “Go to Folder“.
- Type or copy/paste the following path into the window that opens, then click Go: ~/Library/Preferences/com.apple.Safari.plist
- If the file is found, delete it, then re-open Safari
Remove PrimeAurora browser hijacker from Chrome for Mac
To remove the PrimeAurora browser hijacker from Chrome for Mac we will reset the browser settings to its default. Resetting your browser settings will reset the unwanted changes caused by installing other programs. However, your saved bookmarks and passwords will not be cleared or changed.
-
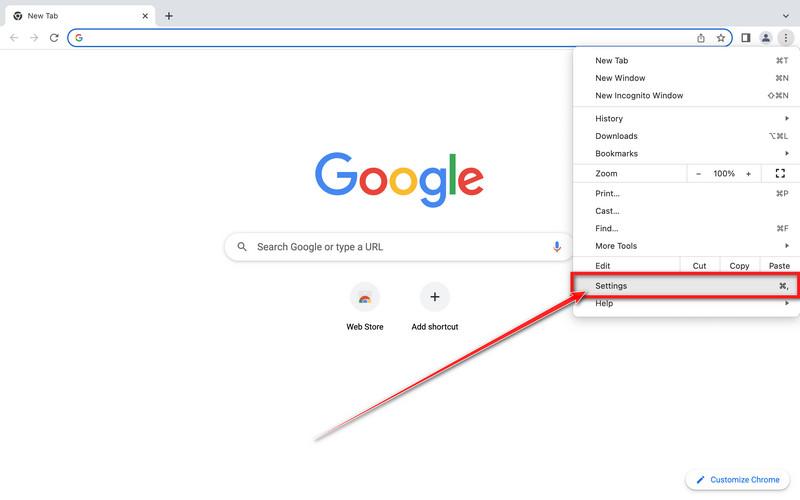
Click on the three dots at the top right and click “Settings”.
Click on Chrome’s main menu button, represented by three dots at the top right corner. Now click on the menu option labeled Settings as shown by the arrow in the picture below, which will open the basic settings screen.
-
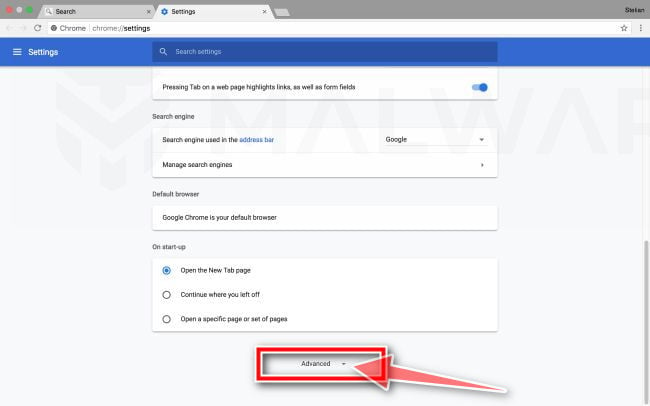
At the bottom, click “Advanced”.
Chrome’s “Settings” should now be displayed in a new tab or window, depending on your configuration. Next, scroll to the bottom of the page and click on the “Advanced” link (as seen in the below example).
-
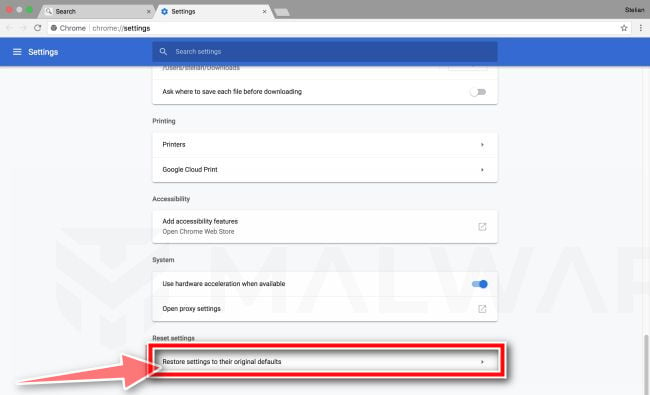
Under the section “Reset,” click “Reset”.
Chrome’s advanced settings should now be displayed. Scroll down until the “Reset and clean up” section is visible, as shown in the example below. Next, click on the “Reset settings to their original defaults” button.
-
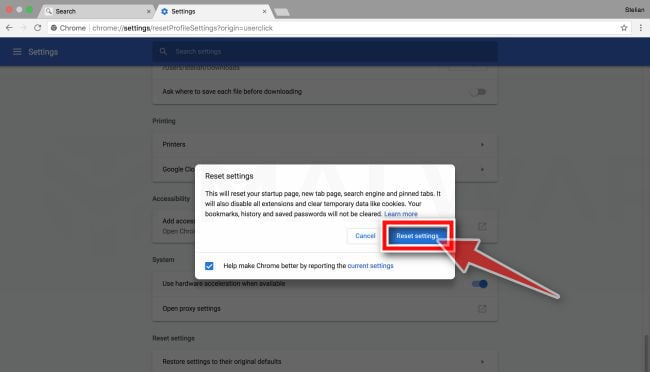
Confirm by clicking “Reset”.
A confirmation dialog should now be displayed, detailing the components that will be restored to their default state should you continue with the reset process. To complete the restoration process, click on the “Reset Settings” button.
If the above steps didn’t help you remove the PrimeAurora browser hijacker from Chrome, you can follow the below steps:
-
Remove the unwanted policies created by malware from Chrome
In many cases, changes to Chrome may not be fixed with a simple browser reset. In such a case, a malicious program may have created unwanted policies on your browser. You can check if any unwanted policies are loaded into the browser by typing chrome://policy into the URL bar.
To reset these policies, follow these steps:- Open a new Terminal window. To do this, go to Finder > Go > Utilities > Terminal
- Enter the following commands, pressing enter after each line:
- defaults write com.google.Chrome HomepageIsNewTabPage -bool false
- defaults write com.google.Chrome NewTabPageLocation -string “https://www.google.com/”
- defaults write com.google.Chrome HomepageLocation -string “https://www.google.com/”
- defaults delete com.google.Chrome DefaultSearchProviderSearchURL
- defaults delete com.google.Chrome DefaultSearchProviderNewTabURL
- defaults delete com.google.Chrome DefaultSearchProviderName
- defaults delete com.google.Chrome ExtensionInstallSources
- After running these commands, quit Chrome if you haven’t already done so, then launch it again and check chrome://policy to see if the same keys are still present (you may need to click the “Reload policies” button for changes to show up). If they’re gone, you should be able to change your search engine and home page back to your preferred defaults in Chrome’s settings.
-
Remove the “Managed by your organization” policy from Chrome
Some malicious programs are known to install managed preferences to set the home page and search engine settings in Chrome. To check for these, do the following:- Quit Chrome
- Click the desktop to make sure you’re in the Finder, choose “Go” then click on “Go to Folder“.
- Type or copy/paste the following path into the window that opens, then click Go: /Library/Managed Preferences/
- Paste the below path into the window that opens, then click Go:
Look for the following files, where [username] is your username:- com.google.Chrome.plist
- [username]/com.google.Chrome.plist
- [username]/complete.plist
These may be legitimate, so open these files with TextEdit and see if they have links to the troublesome site in them. If they do, delete them and restart Chrome.
-
Uninstall Google Chrome from your computer
If the above options didn’t help you remove the malicious redirects, it is easier to completely remove Chrome and all data, then reinstall the browser. To do this, click the Finder icon, from the menu bar. Choose Go, and click Go to Folder, then paste one of the below paths into the window that opens.
You will need to delete all of the below items, but before doing this be aware that this will delete all data for all Google apps you have installed, such as your bookmarks, so you will need to export them before doing this.- /Applications/Chrome.app
- /Library/Application Support/Google/
- /Library/Google/
- ~/Library/Application Support/Google/
- ~/Library/Google/
- ~/Library/Preferences/com.google.Chrome.plist
Note: The “~” indicates that it’s the current user’s Library which is often invisible in recent versions of macOS. To get to it you must hold down the Option (sometimes labeled Alt) key and select Library from the Finder’s Go menu.
After deleting all of the above files, restart your device. You can now download and re-install Google Chrome on your device. You will need to import any exported bookmarks or other data and may need to reinstall any other Google apps that you use.
Remove PrimeAurora browser hijacker from Firefox for Mac
To remove the PrimeAurora browser hijacker from Firefox for Mac we will reset the browser settings to its default. The reset feature fixes many issues by restoring Firefox to its factory default state while saving your essential information like bookmarks, passwords, web form auto-fill information, browsing history, and open tabs.
-
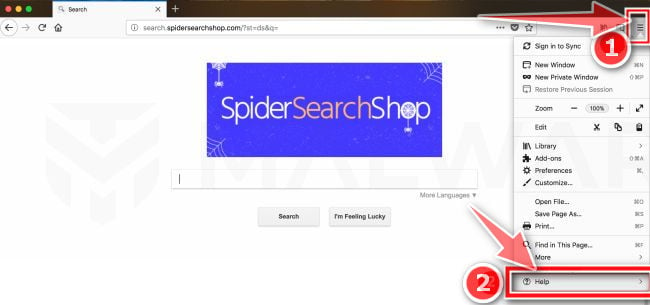
Go to the “Help” menu.
Click on Firefox’s main menu button, represented by three horizontal lines. When the drop-down menu appears, select the option labeled “Help“.
-
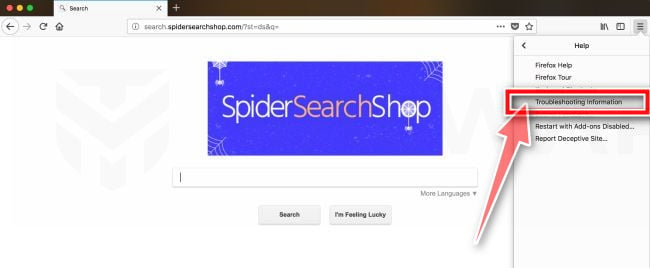
Click “Troubleshooting Information”.
From the Help menu, click on “Troubleshooting Information“.
If you’re unable to access the “Help” menu, type about:support in your address bar to bring up the Troubleshooting information page. -
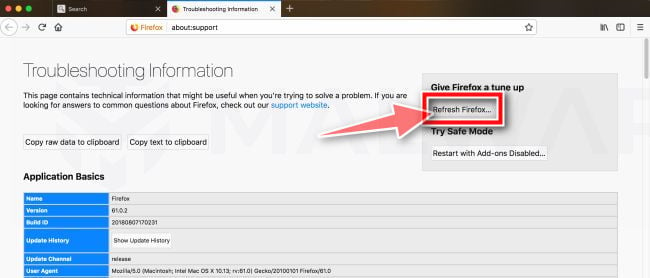
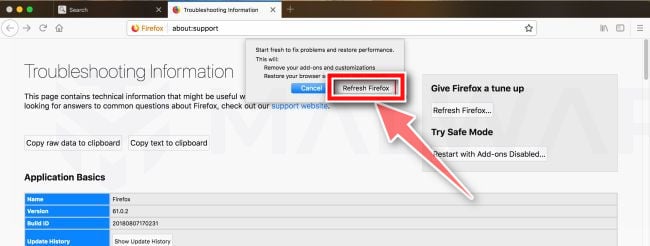
Click on “Refresh Firefox”
Click the “Refresh Firefox” button in the upper-right corner of the “Troubleshooting Information” page.
-
Confirm.
To continue, click on the “Refresh Firefox” button in the new confirmation window that opens.
-
Click on “Finish”.
Firefox will close itself and will revert to its default settings. When it’s done, a window will list the information that was imported. Click on the “Finish“.
If you are still experiencing problems while trying to remove a malicious program from your computer, please ask for help in our Mac Malware Removal Help & Support forum.