If your computer is locked, and you are seeing an “This user is disabled due to some malicious files found in system” notification asking you to call a support phone number, then your machine is infected with a piece of malware known as Rogue.Tech-Support.

This ransomware program displays an “This user is disabled due to some malicious files found in system” lock screen when you start Windows that attempts to scare users into calling a remote tech support number (1-914-465-0012).
These alerts are shown in such a way as to trick the user into thinking their computer has crashed or that a virus has been detected on the computer. It does this to try and scare the infected user into calling one of the listed numbers in order to receive support. In reality, though, they will only be greeted with people who are trying to sell them unneeded support contracts and services.
When you call the number listed in the “This user is disabled due to some malicious files found in system” lock screen , you will be told that your Windows product key is invalid and that you will need to pay $99.99 USD for a new one.
When the “This user is disabled due to some malicious files found in system” malicious program is installed it will also change a variety of Windows settings. This allows it to display the fake “This user is disabled due to some malicious files found in system” lock screen, which overlaps your entire screen, without fear that you can terminate it.
The text of the “This user is disabled due to some malicious files found in system” lock screen is:
This user is disabled due to some malicious files found in system, ensure you have complete protection. Call Technician Now 1-914-465-0012
Your system is lock due to unauthorized activity on your computer. Need any help Call Technician Now at 1-914-465-0012 (Toll-free). unauthorized lock
How to remove “This user is disabled due to some malicious files found in system” lock screen (Removal Guide)
-
To remove the “This user is disabled” lock screen, follow these steps:
- STEP 1: Remove the “This user is disabled due to some malicious files found in system” lock screen
- STEP 2: Scan your computer with Malwarebytes Anti-Malware
- STEP 3: Scan your computer with HitmanPro
STEP 1 : Remove the “This user is disabled due to some malicious files found in system” lock screen
In this first step we will remove the “This user is disabled due to some malicious files found in system” lock screen from Windows.
Because there are many versions of this malware, which behave differently, we have provided multiple options to remove the malicious lock screen.
OPTTION 1: Remove “This user is disabled due to some malicious files found in system” lock screen using task manager
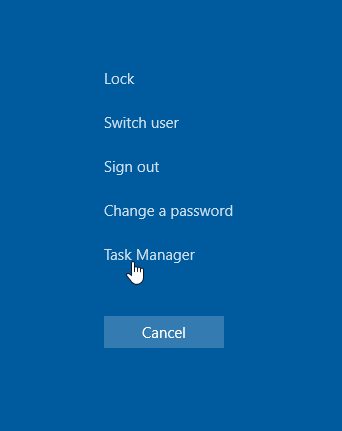
- Open Task Manager by holding down simultaneously the CTRL + ALT + DEL keys on your keyboard.
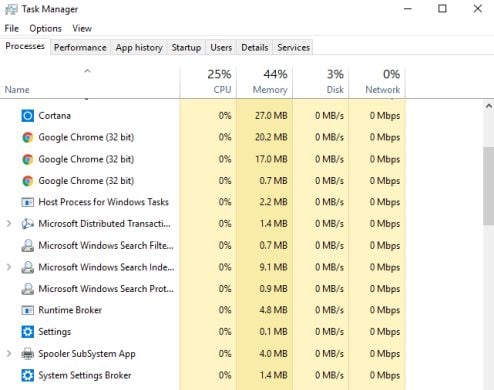
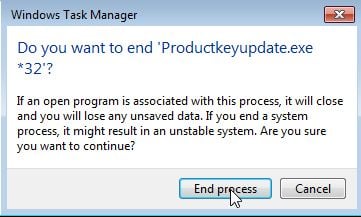
- Scroll through the list till you see the Productkeyupdate.exe or fatalerror.exe process and left-click on it once so it becomes highlighted. Once you have selected the browser’s process, click on the End Task button as show in the picture below.
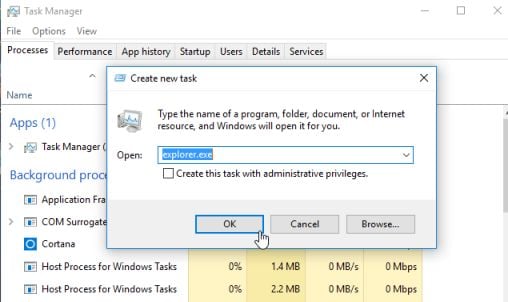
If you are using Windows 10 or Windows 8, you will need to click on the More Details button to see all the process. The malicious process may have a different name on your computer. - The Windows desktop should be visible, but if not, we will start the desktop from the Task Manager. To do this, in the Task Manager window, click on the “File” button then select “Run new task“. When the “Run new task” windows opens, type in “explorer.exe” to start the desktop.
When the process is complete, you can close the Windows Task Manager and continue with the rest of the instructions.
OPTTION 2: Remove “This user is disabled due to some malicious files found in system” lock screen using Command Prompt
- In the “This user is disabled due to some malicious files found in system” lock screen screen click on the “CMD” button which will open a command prompt.
- In the command prompt type “taskmgr” and press “Enter“.
- In the list of processes select “fatalerror.exe” or “ProductKey.exe” and click on “End Process”. The malicious process may have a different name on your computer.
- Close Taskmanager and in the command prompt type “explorer” and press “Enter”.
OPTION 3: Remove the malicious lock screen with HitmanPro.Kickstart
HitmanPro.Kickstart is the solution against ransomware and other persistent malware that has taken your computer hostage or prevents normal computer use.
Because this infection has locked you out of your computer, we will need to create a bootable USB drive that contains the HitmanPro.Kickstart program. We will then boot the infected machine with the HitmanPro.Kickstart USB drive, and use the program to clean the infection.
- Using a “clean” (non-infected) computer, please download HitmanPro from the below link.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Once HitmanPro has been downloaded on the clean machine, insert an USB flash drive and double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows).
To create a bootable HitmanPro USB drive, please follow the instructions from this video:
- Once you have created the bootable HitmanPro.Kickstart USB drive, insert the USB into the computer infected with the “This user is disabled” lock screen.
- After you have inserted the HitmanPro Kickstart USB drive, boot your machine from the HitmanPro.Kickstart USB as seen in the below video.
- The malicious lock screen should be removed from your machine. It’s recommended that you perform a system scan with Malwarebytes and HitmanPro as see in the below steps.
OPTION 4: Start your computer in Safe Mode with Networking
If the above options did not work for your machine, then we will need to start the computer in Safe Mode with Networking to bypass the lock screen.
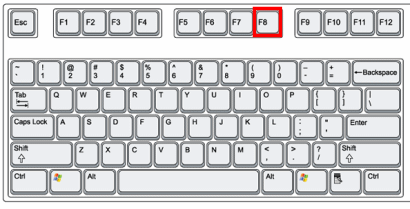
- Immediately after the computer is powered on or restarted (usually after you hear your computer beep), tap the F8 key in 1 second intervals.
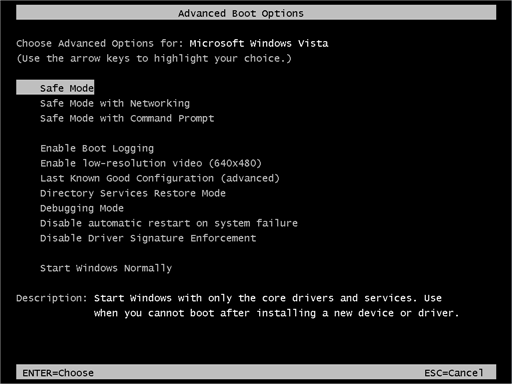
- After your computer displays hardware information and runs a memory test, the Advanced Boot Options menu will appear.
- Use the arrow keys to select Safe Mode with Networking and press ENTER.
- After you have started your machine in Safe Mode with Networking, run a system scan with Malwarebytes Anti-Malware as seen in the below step.
STEP 2: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which should remove the This user is disabled due to some malicious files found in system ransomware. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
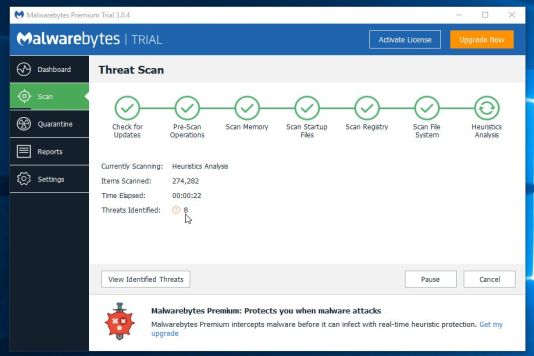
- Once installed, Malwarebytes Anti-Malware will automatically start and will update the antivirus database. To start a system scan you can click on the “Scan Now” button.
- Malwarebytes Anti-Malware will now start scanning your computer for malware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
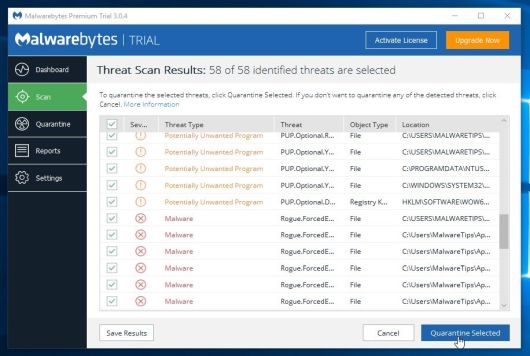
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
STEP 3: Double-check for malware with HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows).
Click on the “Next” button, to install HitmanPro on your computer.
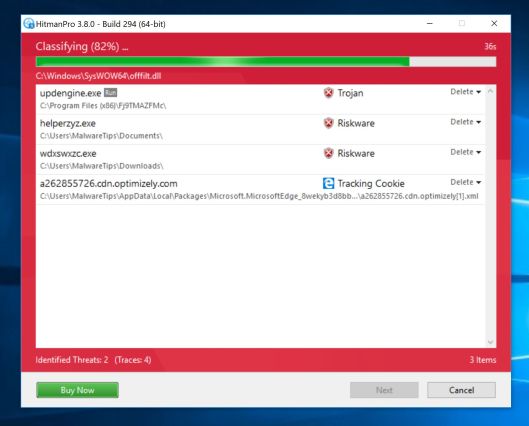
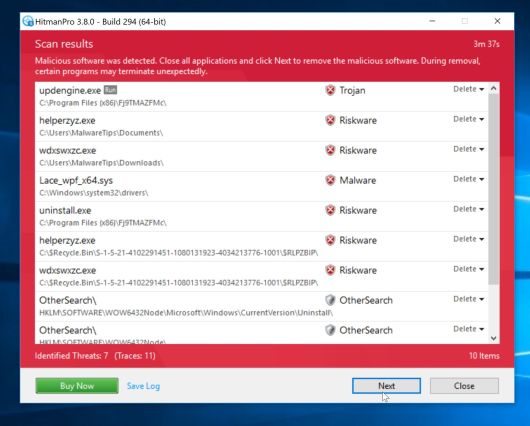
- HitmanPro will now begin to scan your computer for malware.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
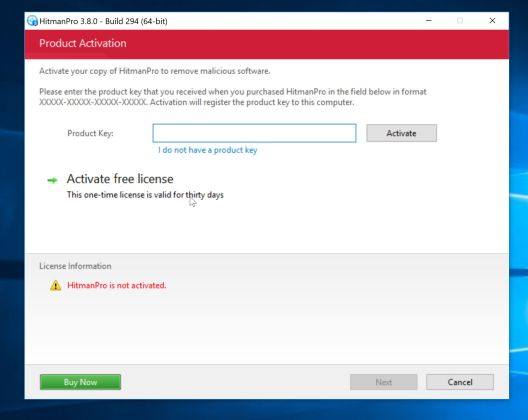
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
If you are still experiencing problems while trying to remove This user is disabled due to some malicious files found in system virus from your machine, you can ask for help in our Malware Removal Assistance forum.