A new cryptocurrency scam is exploding across social media, fueled by deepfake videos of Elon Musk and fraudulent websites falsely promising to double your Bitcoin, Ethereum, Dogecoin and Tether. This “Tesla Crypto Giveaway Scam” has already swindled millions from unwary investors lured by the potential for effortless profits. But of course, these astronomical returns don’t actually exist.
Once directed to fake Tesla promotions pages after watching the deceptive videos, victims deposit crypto into scam wallets thinking their funds will be doubled. In reality, these wallets are controlled by anonymous scammers who simply steal the cryptocurrency, never intending to send back any “giveaway” funds. By the time investors realize there will be no payout, it’s too late.
So how does this alarming scam actually work, spreading so rapidly across YouTube, Instagram and more? How can its fake videos and sites seem so convincing, tricking even savvy crypto holders? And most critically – if you already fell victim to this fraud, what should you do next?
This article offers a comprehensive overview of the Tesla Crypto Giveaway Scam, outlining its deceptive tactics, who’s behind it, and how to respond if you unfortunately sent crypto to these criminals. By understanding this scam fully, we can work together to cut off its spread, prevent more victims, and hopefully see justice served. So let’s dive in.
Scam Overview: A Sophisticated Web of Fake Videos and Websites
The Tesla Crypto Giveaway Scam is a complex infrastructure of fraudulent media and websites designed to dupe consumers into relinquishing their cryptocurrencies under false pretenses. Here’s a closer look at how this deception operates at each stage:
Fake Promotional Videos
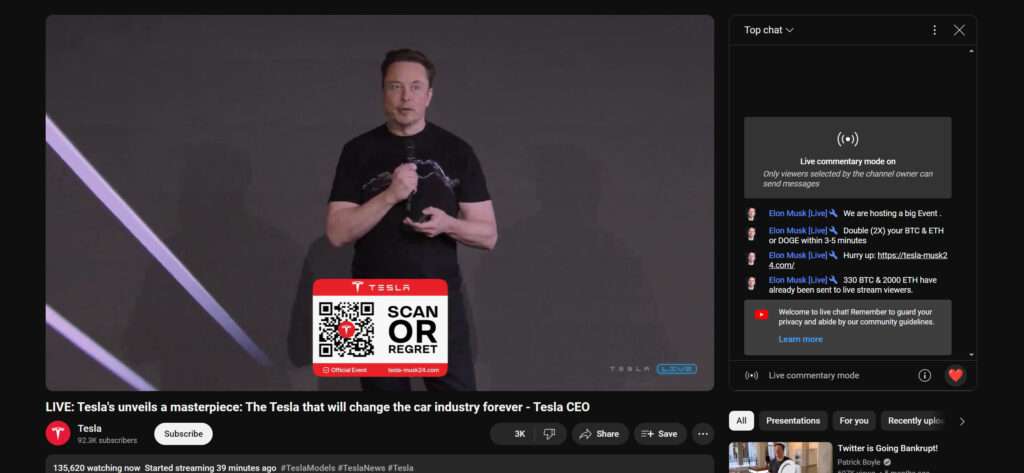
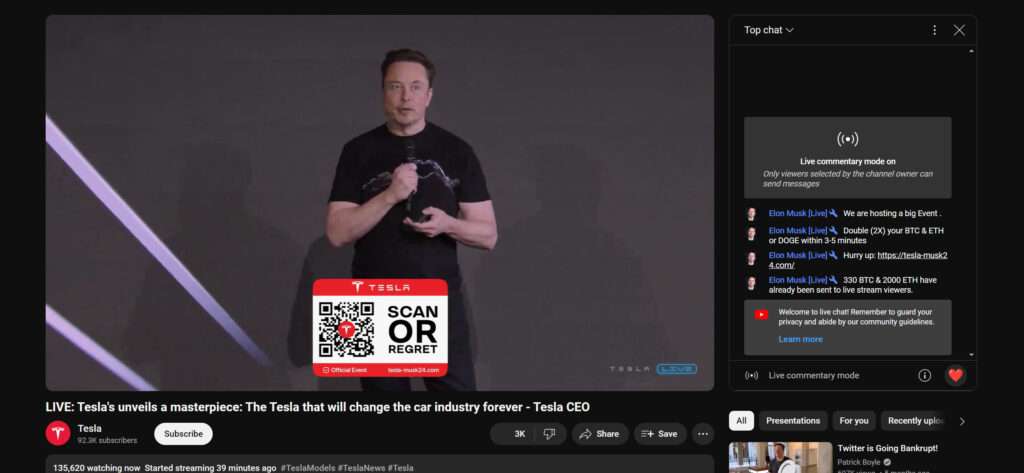
The starting point of this scam is the fake promotional giveaway videos. Hosted on major social media platforms, these videos combine deepfake AI footage of Elon Musk with a voiceover announcing a special Tesla promotion.
The deepfakes portray Musk delivering a speech or presentation, and are manipulated to show him claiming that to support cryptocurrency adoption, Tesla is giving away millions in Bitcoin, Ethereum, Dogecoin, and Tether.
He states that for every amount of these cryptocurrencies sent to a provided wallet address, Tesla will send back double that amount to the sender’s wallet. The deepfakes are now sophisticated enough to look and sound essentially real, convincingly appearing to show Musk himself endorsing this “giveaway.”
Fraudulent Website
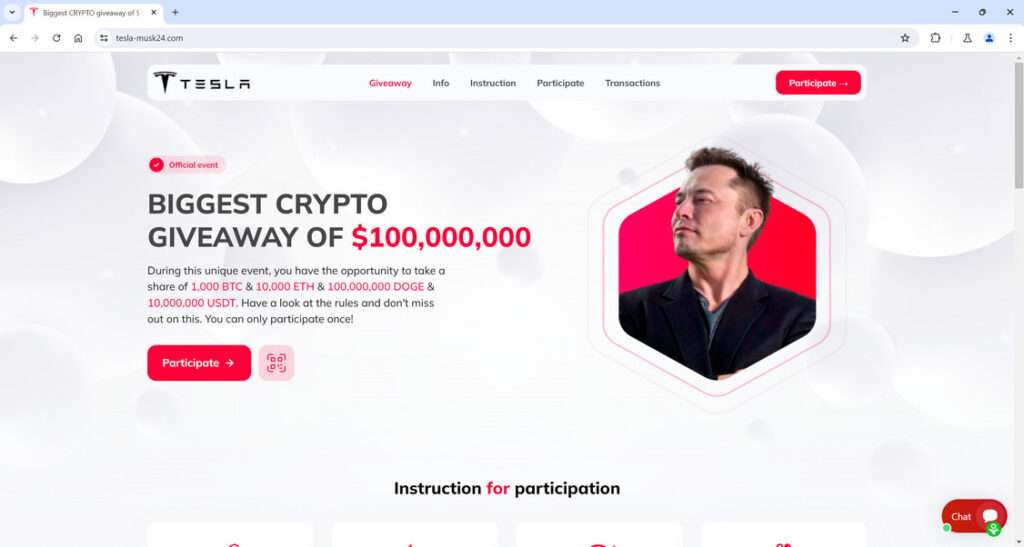
The videos direct viewers to click a link taking them to an official-looking website, prominently featuring the Tesla logo. However, this site is entirely fraudulent. Hosted outside of Tesla’s domains, it is designed expressly to further dupe victims into handing over crypto funds.
This fake site reiterates the supposed giveaway offer, stating in more detail that by sending any amount from 0.1 to 15 BTC, 1 to 200 ETH, 20,000 to 5,000,000 DOGE, or 1,000 to 500,000 USDT to a provided wallet address, Tesla will supposedly send back double those funds.
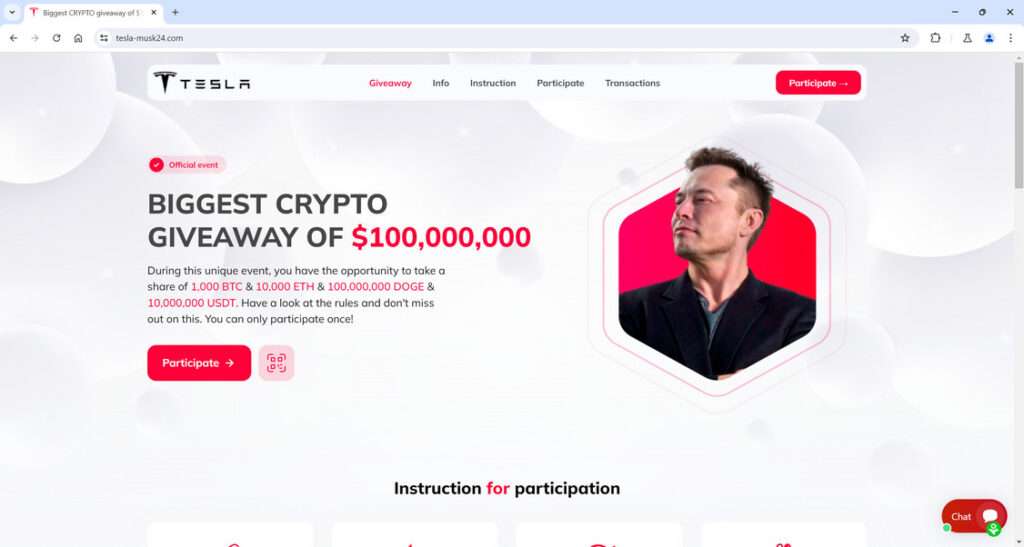
Here is what the scam websites will say:
“BIGGEST CRYPTO GIVEAWAY OF $100,000,000
During this unique event, you have the opportunity to take a share of 1,000 BTC & 10,000 ETH & 100,000,000 DOGE & 10,000,000 USDT. Have a look at the rules and don’t miss out on this. You can only participate once!
To participate, you can do the transaction using any wallet or exchange! Send the desired number of coins to the special address below. Once we receive your transaction, the doubled amount will be sent back to you immediately. You can only take part in our giveaway once, hurry up!”
Scam Wallets
Each scam website displays cryptocurrency wallet addresses, often multiple, for victims to send their Bitcoin, Ethereum, Dogecoin, or Tether to. If funds are deposited to these wallets, they are harvested by the scammers with no intent to return any doubled amount.

T
racking Dashboards
For extra deception, scam sites have a tracking section that appears to show the giveaway progress. Counters claim to track total participants, money sent, and money paid out, as if assets are being doubled and returned. In reality, this entire dashboard is fabricated. No money is ever “paid out”, only stolen.
By combining these elements – the fake videos, the fraudulent websites, the scam wallets, and rigged trackers – this scam forms an alarmingly convincing facade that has defrauded many victims already.
How the Tesla Crypto Giveaway Scam Actually Works
The Tesla Crypto Giveaway Scam ensnares victims through a sinister sequence of deceptions. Here is a step-by-step walkthrough of how this fraud operates, from initial contact to the scammers ultimately stealing funds.
Step 1: Malicious Videos Spread Across Social Media
The starting point is typically fake promotional videos spread across YouTube, Facebook, Instagram and TikTok through paid ads or posts. These videos have increased exponentially in recent months.
The videos seem to show Elon Musk delivering a speech or presentation. Through deceptive deepfake AI technology, the videos are manipulated to depict Musk announcing a major Tesla cryptocurrency giveaway event.
He claims that to support wider crypto adoption, Tesla will double any amount of Bitcoin, Ethereum, Dogecoin or Tether sent to specified wallet addresses. The deepfakes are now sophisticated enough to appear nearly indistinguishable from real events.
Step 2: Scam Links Direct to Fraudulent Websites
The videos prominently feature links in the video description or comments. These links direct viewers to an official-looking website carrying Tesla branding.
However, this website is entirely fraudulent. Hosted outside of Tesla’s official domains, its sole purpose is furthering the crypto giveaway deception.
Step 3: Fake Sites Reiterate the Scam Offer
The fraudulent site reiteratively lays out the giveaway offer described in the videos. It states that by sending any amount from 0.1 to 15 BTC, 1 to 200 ETH, 20,000 to 5,000,000 DOGE, or 1,000 to 500,000 USDT, Tesla will send back double.
These promised astronomical returns are the bait encouraging victims to send funds. The site falsely claims to support crypto mass adoption through this “giveaway”.
Step 4: Scam Wallets Are Provided
The fake Tesla page lists various cryptocurrency wallet addresses, often multiple for each currency. Victims are instructed to send funds to these wallets to participate in the bogus giveaway.
If deposits are made, the scammers immediately harvest them. Their only intention is stealing money, not giving any away. The listed “official” Tesla wallets are entirely controlled by the fraudsters.
Step 5: Fake Statistics Add Validity
For added deception, the website often tracks false statistics like total giveaway participants, amount deposited, and amount supposedly paid out. This data makes the scam look fully legitimate and in progress.
In reality, these figures are wholly falsified. No payouts are occurring, only victim deposits flowing to the scammers. But victims trust the site at face value.
Step 6: Victims Initiate Transfers to Scam Wallets
Believing Elon Musk and Tesla are genuinely running a cryptocurrency giveaway promotion, the victim sends funds to the listed wallet addresses per the site’s instructions.
They transfer amounts of Bitcoin, Ethereum, Dogecoin and/or Tether, expecting Tesla to send back double as promised. But the truth is devastatingly different.
Step 7: Scammers Steal Deposits
Instead of Tesla sending back doubled cryptocurrency, the scammers simply steal whatever assets victims deposit into the fake wallet addresses.
With no intent of paying out, they rapidly withdraw funds from the scam wallets into accounts they control. Victims watch helplessly as their balance drops to zero.
Step 8: Scammers Often Pressure for More
In some cases, scammers will reach out to victims who already sent crypto, pressuring them to deposit more in order to ultimately receive the full “promised giveaway amount.” This salts the wound, further manipulating those already defrauded.
Step 9: Scammers Cash Out and Disappear
Once satisfied with their scam bounty size, the fraudsters cash out their stolen cryptocurrency into fiat currency, routed through mixers and exchanges to cover their trail. They then disappear permanently, leaving victims empty-handed.
By following these steps in sequence, this scam has been extremely effective at extorting money from unwitting crypto investors who believe the false promises. But what if you already fell victim?
What To Do If You Sent Crypto to the Tesla Giveaway Scam
If you deposited any amount of Bitcoin, Ethereum, Dogecoin or Tether to a wallet associated with this scam, here are the important next steps to take:
1. Report the Scam
Report the scam videos, websites and social media pages immediately. Contact the hosting platforms, register complaints and urge them to remove the fraudulent content to prevent further victims.
2. Contact Local Authorities
File reports about the scam and your situation with your local police department, FBI office, or cybercrime agency. Provide all relevant details and make clear you are seeking help recovering stolen cryptocurrency funds.
3. Inform Your Wallet and Exchange Providers
If using an exchange like Coinbase, alert them to the fraudulent transfer. Similarly, inform any hosted wallet services. Ask them to attempt blocking further withdrawals where possible.
4. Monitor the Scam Wallets
Carefully monitor the wallet addresses you sent crypto to. Follow any outgoing transfers the scammers make in hopes of tracing movement of the funds.
5. Retain Any Evidence
Keep recordings of scam videos, screenshots of websites, wallet addresses, and transaction records. This evidence trail is crucial for demonstrating the scam took place.
6. Consult Recovery Experts
To aid tracing and recovering stolen crypto assets, consult professional cryptocurrency recovery firms. They may have resources and blockchain analysis tools law enforcement lack.
7. Warn Others
Spread awareness of this scam publicly to prevent others from being victimized. Share posts, details, wallet addresses, and resources online to maximize the scam’s exposure.
While recouping losses is extremely difficult, following these steps provides the best chance. And moving forward, remember that legitimate giveaways will never ask you to send crypto to participate – that is always the hallmark of a scam.
How to Identify This Scam on Social Media and Websites
While the Tesla Crypto Giveaway Scam has become sophisticated, there are key indicators to help spot it across social platforms and fraudulent sites. Here is what to watch for:
On Social Media
- Videos focused on Elon Musk and Tesla announcing a major crypto giveaway promotion. For example, a deepfake TikTok video showing Musk proclaiming “BIGGEST CRYPTO GIVEAWAY OF $100,000,000 During this unique event, you have the opportunity to take a share of 1,000 BTC & 10,000 ETH & 100,000,000 DOGE & 10,000,000 USDT. Have a look at the rules and don’t miss out on this. You can only participate once!”
- Check if the video is an obvious deepfake. Pause and look for strange artifacts, lip sync issues, blurriness or other signs of AI manipulation.
- Account posting it has zero other content or was just created. Scam accounts often have no posting history.
- Link in video description or comments routes to an unofficial domain. Legitimate promotions would link to Tesla’s site.
- Comment section is disabled to suppress warnings. Scam videos block comments to hide users exposing the fraud.
Importantly, remember Tesla and Elon Musk have never conducted cryptocurrency giveaways before. So any promotions of this type are guaranteed to be fraudulent.
On Websites
- Domain name is NOT an official tesla.com page, but mimics it closely. Check the URL carefully.
- Page layout, fonts and branding copied from Tesla to appear legitimate. Scammers mimic the look.
- Promises a giveaway of “free” or “passive” crypto just for sending to their wallet. Classic red flag.
- Shows fabricated stats on total participants, deposits and withdrawals to look real. Verify figures directly with Tesla.
- Lists multiple cryptocurrency wallet addresses totally unrelated to Tesla. Tesla would never provide these.
- Contains grammatical errors, typos, inconsistencies or other sloppy signs of a scam operation.
Again, remember neither Tesla nor Elon Musk has ever conducted a cryptocurrency giveaway promotion requiring sending assets to provided wallet addresses. Any site or social media page promoting such an offering is 100% fraudulent.
Stay vigilant for these indicators on social media and sites. Spreading awareness of these scam warning signs is crucial to stay safe.
Frequently Asked Questions About The Tesla Crypto Giveaway Scam
1. What exactly is the Tesla Crypto Giveaway Scam?
The Tesla Crypto Giveaway Scam is a fraudulent scheme spreading primarily through social media ads and videos. By using deepfake AI footage of Elon Musk, scammers create fake promotional videos portraying Musk announcing a major Tesla cryptocurrency giveaway event.
The videos direct victims to fake Tesla promotions websites that promise to immediately send back double any amount of Bitcoin, Ethereum, Dogecoin or Tether deposited into provided wallet addresses. However, these are scam wallets controlled by fraudsters who simply steal any funds sent.
2. How do the fraudulent videos work?
The videos combine deepfake AI-manipulated footage of Elon Musk with a voiceover of him announcing Tesla is running a crypto giveaway. The deepfakes portray Musk giving speeches or presentations and are faked to appear real and credible. They spread through YouTube, Facebook, Instagram and TikTok ads and posts.
3. What happens when victims click the link in the videos?
The videos prominently feature links in the description or comments leading to fake, but professional-looking Tesla promotions websites. These fraudulent sites reinforce the giveaway message, promising to instantly send back double any crypto deposited. In reality, they are scam pages designed to further trick victims.
4. How do the fraudulent websites work?
The fake Tesla crypto giveaway websites list wallet addresses and instruct users to send crypto to participate in the bogus promotion. They falsely promise to send back doubled funds. In truth, the provided wallets are controlled by scammers who steal deposits. The websites also use fake trackers and stats to appear legitimate.
5. What cryptocurrencies are targeted?
The scam targets Bitcoin, Ethereum, Dogecoin and Tether specifically. The fake websites list wallet addresses for each currency, enticing victims to send funds expecting their coins to be doubled. However, their deposits are stolen.
6. How much have victims lost to this scam so far?
Total losses are still being tabulated, but likely amount to many millions in stolen cryptocurrency. The scam has expanded rapidly through broad social media exposure and increasingly convincing deepfake videos. Police urge anyone victimized by this fraud to immediately file reports.
7. How can I spot this scam on social media and websites?
Be skeptical of giveaway promotions involving Tesla or Elon Musk sending back doubled crypto funds. Look for deepfake signs in videos. Check links go to real Tesla domains. Beware fake statistics on sites. Avoid any site asking for crypto payments.
8. What should I do if I sent crypto to this scam?
If you deposited funds, immediately report it to authorities, contact wallet/exchange providers to potentially block withdrawals, monitor the scam wallet addresses, and retain evidence like wallet IDs and transaction records. Also seek professional crypto recovery help and legal support.
9. How can I avoid cryptocurrency giveaway scams in general?
Be wary of any giveaways requiring you to send crypto first. Only trust promotions directly hosted on official company sites – not social media videos or outside links. Verify legitimacy before participating. And remember – if it seems too good to be true, it nearly always is.
10. How can I report this scam or get more help?
Report scam social media posts, videos and websites immediately to get them taken down. File complaints with the FTC, CFTC, your local FBI office, or cybercrime agencies about this fraud and your situation. You can also consult a lawyer or professional crypto recovery company for further assistance and support.
The Bottom Line
The Tesla Crypto Giveaway Scam demonstrates that for all their potential, cryptocurrencies remain prime targets for fraud given their pseudonymous nature. By exploiting convincing deepfakes and fraudulent websites, this scam has cost victims millions by duping them into relinquishing their coins and tokens to anonymous thieves.
If you encounter any giveaway promotion involving sending crypto, exercise extreme caution. Do not trust any videos, sites, or materials around such offers, no matter how credible they appear. Verify directly with Tesla or any company involved before engaging.
With crypto scams only growing in sophistication, it is crucial investors implement robust security practices, educate themselves on fraud typologies, and remain deeply skeptical of anything resembling “free money”. Because as the Tesla scam proves, when it seems too good to be true in crypto, it almost certainly is.







