Scammers are constantly finding new ways to deceive unsuspecting individuals and steal their personal information. One of the latest tactics used by cybercriminals is the ‘3 Broken Emails’ spam, which involves fake Google notification messages. These emails appear to be legitimate, but they are designed to trick users into revealing sensitive information or downloading malicious software.

What is the ‘3 Broken Emails’ Spam?
The ‘3 Broken Emails’ spam is a type of phishing scam that targets Google users. It involves sending fake notification emails that appear to come from Google, alerting the recipient about three undelivered emails. The emails claim that the recipient’s account has been compromised and that action is required to secure it.
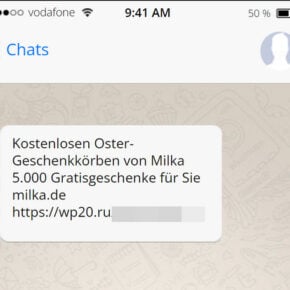
These emails often include official-looking logos, email addresses, and other elements that make them appear genuine. They may also use scare tactics to create a sense of urgency, urging the recipient to take immediate action to prevent further damage.
How the Scam Works
The ‘3 Broken Emails’ scam works by exploiting the trust users have in Google and their desire to protect their accounts. Here is a step-by-step breakdown of how the scam typically unfolds:
- The victim receives an email that appears to be from Google, informing them about three undelivered emails.
- The email claims that the recipient’s account has been compromised and that action is required to secure it.
- The email instructs the recipient to click on a link or download an attachment to resolve the issue.
- If the recipient falls for the scam and clicks on the link or downloads the attachment, they may be directed to a fake website that looks like a Google login page.
- The victim is prompted to enter their Google username and password on the fake login page.
- Once the victim enters their credentials, the scammers gain access to their Google account and can use it for malicious purposes.
It is important to note that the ‘3 Broken Emails’ spam can also be used to distribute malware. In some cases, clicking on the link or downloading the attachment may result in the installation of malicious software on the victim’s device.
What to Do If You Have Fallen Victim
If you have fallen victim to the ‘3 Broken Emails’ spam or any other phishing scam, it is crucial to take immediate action to protect your accounts and personal information. Here are the steps you should follow:
- Change your passwords: Start by changing the password for the compromised account. Make sure to choose a strong, unique password that is not easily guessable.
- Enable two-factor authentication: Set up two-factor authentication for your Google account and any other accounts that offer this security feature. This adds an extra layer of protection by requiring a verification code in addition to your password.
- Scan for viruses and malware: Run a scan with a reliable antivirus program, such as Malwarebytes Free, to check for any malicious software that may have been installed on your device.
- Monitor your accounts: Keep a close eye on your accounts for any suspicious activity. Report any unauthorized transactions or changes to the respective service providers.
- Be cautious of future emails: Be extra vigilant when receiving emails, especially those requesting personal information or urging immediate action. Verify the legitimacy of the email by contacting the official support channels of the service provider.
Technical Details
The ‘3 Broken Emails’ spam relies on social engineering techniques to deceive users. The scammers carefully craft the emails to appear legitimate and exploit the trust users have in Google. They may use tactics such as:
- Using official-looking logos and email addresses to make the emails appear genuine.
- Creating a sense of urgency to pressure users into taking immediate action.
- Using scare tactics, such as claiming that the recipient’s account has been compromised, to manipulate users into revealing their personal information.
Additionally, the scammers may use various techniques to distribute malware, such as:
- Embedding malicious links or attachments in the emails.
- Redirecting users to fake websites that mimic legitimate login pages.
- Exploiting vulnerabilities in software or operating systems to install malware on the victim’s device.
Statistics on Phishing Scams
Phishing scams, including the ‘3 Broken Emails’ spam, continue to be a significant threat to individuals and organizations. Here are some statistics that highlight the prevalence and impact of phishing scams:
- According to the Anti-Phishing Working Group (APWG), there were over 241,324 unique phishing attacks reported in the first quarter of 2023.
- Phishing attacks cost businesses an estimated $1.8 billion in losses in 2022, according to the FBI’s Internet Crime Complaint Center (IC3).
- A study by Verizon found that 30% of phishing emails are opened by targeted users, and 12% of those users click on the malicious attachment or link.
- Google reported blocking over 100 million phishing emails every day in 2022.
Summary
The ‘3 Broken Emails’ spam is a deceptive phishing scam that targets Google users. It involves sending fake notification emails that appear to come from Google, tricking recipients into revealing their personal information or downloading malware. If you have fallen victim to this scam, it is crucial to take immediate action by changing your passwords, enabling two-factor authentication, scanning for viruses and malware, monitoring your accounts, and being cautious of future emails.
Phishing scams, including the ‘3 Broken Emails’ spam, are a significant threat, costing businesses billions of dollars and compromising the security of individuals worldwide. It is essential to stay vigilant, educate yourself about these scams, and take proactive measures to protect your personal information and accounts.