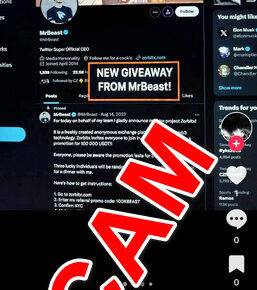
Scams have become increasingly prevalent in the digital age, with cybercriminals constantly devising new methods to deceive unsuspecting individuals. One such scam that has gained significant attention is the Apple ID ‘Violated Policies’ phishing scam. This article aims to provide a comprehensive overview of this scam, including what it is, how it works, what to do if you have fallen victim, technical details, and relevant statistics.
![Apple ID ‘Violated Policies’ Phishing Scam [Explained] 1 Scams](https://malwaretips.com/blogs/wp-content/uploads/2023/07/Scams.jpg)
What is the Apple ID ‘Violated Policies’ Phishing Scam?
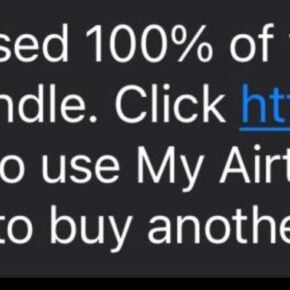
The Apple ID ‘Violated Policies’ phishing scam is a fraudulent scheme that aims to trick Apple users into revealing their personal information, such as their Apple ID credentials, credit card details, and other sensitive data. Cybercriminals typically send out phishing emails or text messages that appear to be from Apple, warning the recipient that their Apple ID has violated certain policies or security measures.
The scam relies on social engineering techniques to create a sense of urgency and panic in the victim, prompting them to take immediate action. The fraudulent message often claims that the user’s Apple ID will be permanently disabled or that unauthorized activity has been detected on their account. To resolve the issue, the victim is instructed to click on a link provided in the email or message.
How Does the Scam Work?
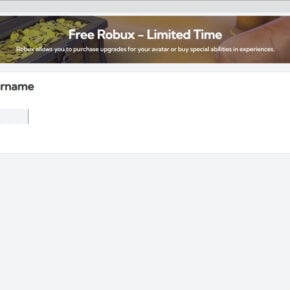
Once the victim clicks on the malicious link, they are directed to a fake website that closely resembles the official Apple website. This website is designed to trick users into entering their Apple ID credentials and other personal information. The scammers may also request credit card details, billing addresses, and other sensitive data under the guise of verifying the user’s account.
Unbeknownst to the victim, the information they enter on the fake website is captured by the cybercriminals, who can then use it for various malicious purposes. This may include identity theft, unauthorized access to the victim’s Apple account, or even financial fraud.
What to Do If You Have Fallen Victim?
If you have fallen victim to the Apple ID ‘Violated Policies’ phishing scam, it is crucial to take immediate action to minimize the potential damage. Here are the steps you should follow:
- Change your Apple ID password: Access your Apple ID account settings and change your password to prevent further unauthorized access.
- Contact Apple Support: Inform Apple about the scam and provide them with any relevant information, such as the phishing email or message you received.
- Monitor your accounts: Keep a close eye on your financial accounts and credit reports for any suspicious activity. If you notice any unauthorized transactions, report them to your bank or credit card provider immediately.
- Scan your device for malware: Run a scan with Malwarebytes Free or another reputable antivirus software to ensure that your device is not infected with malware.
- Enable two-factor authentication: Enable two-factor authentication for your Apple ID to add an extra layer of security to your account.
Technical Details of the Scam
The Apple ID ‘Violated Policies’ phishing scam often utilizes various techniques to deceive users and make the fraudulent messages appear legitimate. Some of the common techniques employed by cybercriminals include:
- Spoofed email addresses: Scammers often use email addresses that closely resemble official Apple email addresses to trick users into believing that the message is genuine.
- URL manipulation: The malicious links in the phishing emails or messages may appear similar to legitimate Apple URLs, but they redirect users to fake websites.
- Website cloning: The fake websites used in the scam are designed to closely mimic the official Apple website, making it difficult for users to distinguish between the two.
- Social engineering tactics: The scammers create a sense of urgency and panic in the victim, compelling them to take immediate action without thoroughly verifying the authenticity of the message.
Statistics on Phishing Scams
Phishing scams, including the Apple ID ‘Violated Policies’ phishing scam, continue to be a significant threat in the digital landscape. Here are some statistics that highlight the prevalence and impact of phishing scams:
- In 2020, the Anti-Phishing Working Group (APWG) reported a total of 241,324 unique phishing attacks worldwide.
- According to a report by Verizon, 22% of data breaches in 2019 involved phishing attacks.
- A study conducted by Google found that phishing attacks are successful 45% of the time.
- In 2020, the FBI’s Internet Crime Complaint Center (IC3) received over 241,000 complaints related to phishing scams, resulting in losses exceeding $54 million.
Summary
The Apple ID ‘Violated Policies’ phishing scam is a deceptive scheme that aims to trick Apple users into revealing their personal information. By understanding how this scam works and taking appropriate precautions, users can protect themselves from falling victim to such fraudulent activities. Remember to always be cautious when receiving unsolicited emails or messages, and never provide personal information unless you are certain of the sender’s authenticity. By staying vigilant and following the recommended steps, users can safeguard their online security and privacy.