Scams and phishing attempts have become increasingly common in the digital age, targeting unsuspecting individuals and organizations. One such scam that has gained attention recently is the Apple ‘Last Alert From Us’ phishing scam email. This article aims to provide a detailed overview of this scam, including what it is, how it works, what to do if you have fallen victim, and other relevant information.
![Apple ‘Last Alert From Us’ Phishing Scam Email [Explained] 1 Scams](https://malwaretips.com/blogs/wp-content/uploads/2023/07/Scams.jpg)
What is the Apple ‘Last Alert From Us’ Phishing Scam Email?
The Apple ‘Last Alert From Us’ phishing scam email is a fraudulent email that impersonates Apple, a well-known technology company. The email is designed to trick recipients into believing that their Apple ID has been compromised or that there is an issue with their account. The scammers use various tactics to create a sense of urgency and panic, prompting recipients to take immediate action.
How Does the Scam Work?
The Apple ‘Last Alert From Us’ phishing scam email typically follows a similar pattern. Here is a step-by-step breakdown of how the scam works:
- The scammer sends an email that appears to be from Apple, using a spoofed email address that may look legitimate.
- The email usually contains Apple’s logo and branding to make it appear authentic.
- The subject line often includes phrases like “Last Alert From Us” or “Account Security Notice” to grab the recipient’s attention.
- The body of the email contains a message stating that the recipient’s Apple ID has been compromised or that there is an issue with their account.
- The email urges the recipient to click on a link or download an attachment to resolve the issue.
- If the recipient falls for the scam and clicks on the link or downloads the attachment, they are directed to a fake website that looks like Apple’s official website.
- The fake website prompts the recipient to enter their Apple ID and password, which the scammers then capture.
- Once the scammers have obtained the victim’s Apple ID and password, they can use it to gain unauthorized access to the victim’s account or commit identity theft.
What to Do If You Have Fallen Victim?
If you have fallen victim to the Apple ‘Last Alert From Us’ phishing scam email, it is important to take immediate action to protect your account and personal information. Here are the steps you should follow:
- Change your Apple ID password: Go to the official Apple website and change your password immediately. Make sure to choose a strong, unique password that is not used for any other accounts.
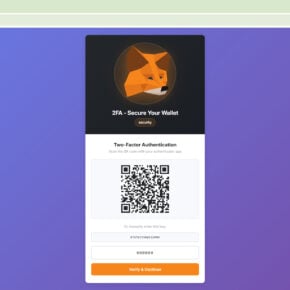
- Enable two-factor authentication: Two-factor authentication adds an extra layer of security to your Apple ID. Enable this feature to prevent unauthorized access to your account.
- Scan your device for malware: Run a scan with Malwarebytes Free or any reputable antivirus software to check for any malware or viruses that may have been installed on your device.
- Monitor your accounts: Keep a close eye on your financial accounts, credit reports, and any other accounts linked to your Apple ID. Report any suspicious activity to the respective institutions.
- Report the scam: Forward the phishing email to Apple’s official phishing email address (reportphishing@apple.com) and to your email provider’s abuse department.
How to Spot a Phishing Scam Email?
It is essential to be able to identify phishing scam emails to protect yourself from falling victim. Here are some signs that can help you spot a phishing scam email:
- Generic greetings: Phishing emails often use generic greetings like “Dear Customer” instead of addressing you by name.
- Urgency and threats: Scammers create a sense of urgency and may threaten to suspend your account or impose penalties if you do not take immediate action.
- Misspellings and grammatical errors: Phishing emails often contain spelling mistakes, grammatical errors, or awkward phrasing.
- Unusual sender email address: Check the sender’s email address carefully. Phishing emails often use email addresses that are similar to, but not exactly the same as, the legitimate company’s email address.
- Request for personal information: Legitimate companies will never ask you to provide personal information, such as passwords or social security numbers, via email.
Summary
The Apple ‘Last Alert From Us’ phishing scam email is a deceptive attempt to trick individuals into revealing their Apple ID credentials. By impersonating Apple and creating a sense of urgency, scammers aim to obtain personal information and gain unauthorized access to accounts. To protect yourself, it is crucial to be vigilant and cautious when dealing with emails, especially those requesting personal information. If you have fallen victim to this scam, take immediate action by changing your password, enabling two-factor authentication, and reporting the incident to Apple. Remember to regularly scan your devices for malware and stay informed about the latest phishing scams to ensure your online safety.

![Remove Iptil.adsstreamline.top Pop-ups [Virus Removal Guide] 3 McAfee scam 4](https://malwaretips.com/blogs/wp-content/uploads/2023/08/McAfee-scam-4-290x290.jpg)