Trojans
How to Remove KMSPico Malware [Virus Removal Guide]
Many users—especially those looking for free access to premium software—eventually come across KMSPico. It’s one of the most widely used hack tools for activating Microsoft…

Help Bust Scammers
Your report helps us connect the dots across domains, ads, and messages so the next person doesn’t get tricked.
Protect Your Accounts
Avoid Irreversible Payments
If someone demands payment by gift card, crypto, wire, or “friends and family,” assume it’s a scam. Those methods are popular because they’re hard to reverse and easy to disappear with.
Scams End Here
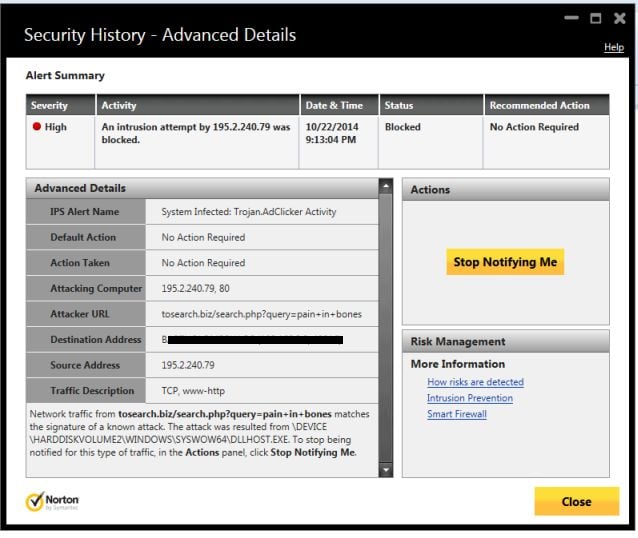
How to remove Trojan.Adclicker virus (Removal Guide)
Trojan.Adclicker is a detection name used by Norton Antivirus to identify malicious programs that share the primary functionality of artificially…
How to remove Trojan.Poweliks virus (Removal Guide)
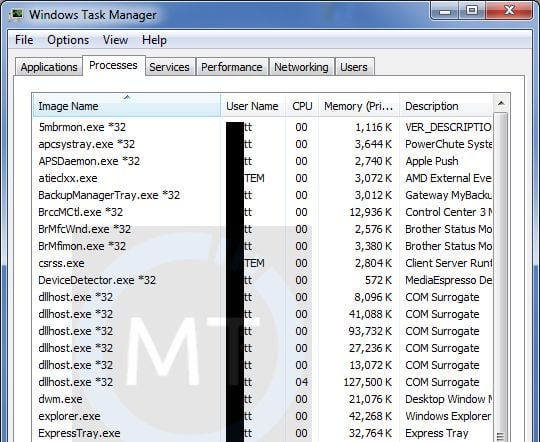
Poweliks is not a regular piece of malware because it resides in the memory of the system and stores absolutely…
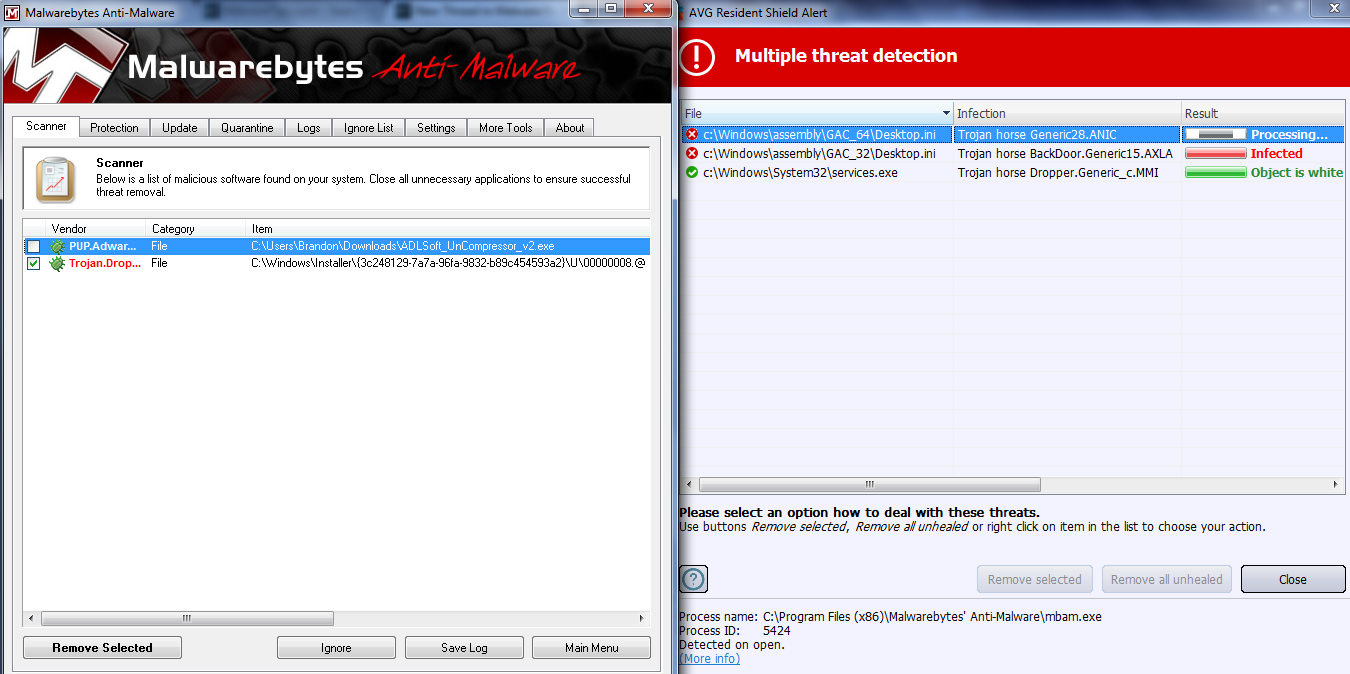
Remove Trojan.Dropper.BCMiner (Virus Removal Guide)
Trojan.Dropper.BCMiner is a Trojan Horse that uses the infected computer's resources to mine Bitcoin without user permission. Trojan.Dropper.BCMiner Trojans will…
How to easily remove ZeroAccess rootkit (Virus Removal Instructions)
The ZeroAccess rootkit also known as Sirefef, is a malicious program that has as a primary motivation of to make…

Scam Hunter Mode
Submit the evidence and we’ll verify what we can, then turn it into a practical alert others can act on.


![How to Remove KMSPico Malware [Virus Removal Guide] 6 kmspico malware](https://malwaretips.com/blogs/wp-content/uploads/2023/01/kmspico-malware.jpg)