Poweliks is not a regular piece of malware because it resides in the memory of the system and stores absolutely no file on the disk, making it more difficult to detect.
After compromising the computer, the malware creates registry entries with commands that verify for the presence of PowerShell or .NET Framework and for executing the payload.
Once the file is launched, the cybercriminals turn on the persistency feature of the malware by creating an encoded autostart key in the registry.
It seems that the encoding technique used by the malware was originally created by Microsoft to safeguard their source code from being altered.In order to avoid detection by system tools, the registry key is hidden by providing a name in non-ASCII characters, which makes it unavailable to the Registry Editor (regedit.exe) in Windows.
By creating the auto-start key, the attackers make sure that a reboot of the system does not remove it from the computer.
By decoding the key, Symantec observed two sets of code: one that verified if the affected machine had Windows PowerShell installed, and another one, a Base64-encoded PowerShell script, for calling and executing the shellcode.
According to the Symantec researchers, the shellcode executes the payload, which attempts to connect to a remote command and control (C&C) server for receiving instructions. There are multiple IP addresses for C&C servers, all hard-coded.
The peculiarity of this malware is that it does not create any file on the disk, making it more difficult to be detected through classic protection mechanisms.
What the Trojan.Poweliks malware usually does?
If your computer is infected with the Trojan.Poweliks virus, this infection may contact a remote host for the following purposes:
- To report a new infection to its author
- To receive configuration or other data
- To download and execute arbitrary files (including updates or additional malware)
- To receive instruction from a remote attacker
- To upload data taken from the affected computer
How do I know if Trojan.Poweliks malware or not?
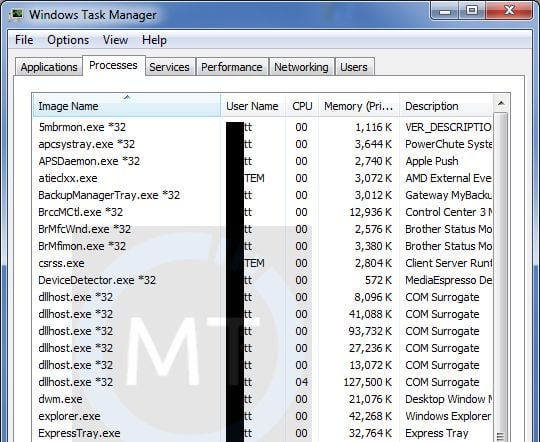
If your machine is infected with the Trojan.Poweliks you will see very high CPU usage, and multiple “dllhost.exe *32” process running in Windows Task Manager. While these symptoms may be caused by other factors, we strongly suggest to check you computer for malware if you notice them.
How to remove Trojan.Poweliks virus (Removal Guide)
This page is a comprehensive guide, which will remove the Trojan.Poweliks infection from your computer. Please perform all the steps in the correct order. If you have any questions or doubt at any point, STOP and ask for our assistance.
STEP 1: Remove Trojan.Poweliks with ESET Poweliks Cleaner
STEP 2: Remove Trojan.Poweliks virus with Malwarebytes Anti-Malware Free
STEP 3: Remove Trojan.Poweliks infection with HitmanPro
STEP 4: Double check for any left over infections with Emsisoft Emergency Kit
STEP 1: Remove Trojan.Poweliks with ESET Poweliks Cleaner
In this first step, we will run a system scan with ESET Poweliks Cleaner to remove Trojan.Poweliks that might be installed on your system.
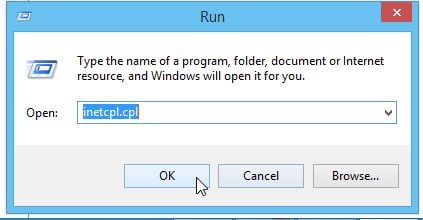
- Poweliks will change your Internet Explorer security settings so that you are unable to download files with it. To fix this, press the Windows key (Windows Key) on your keyboard, and while holding it down, also press the R key on your keyboard. This will open the Run dialog box as shown below.
Next, we will need to type inetcpl.cpl in the “Run” box to open the Internet Explorer settings. - In Internet Explorer, click on the “Security” tab, then on “Reset all zones to default level” button. Click on “Apply” and “OK” to save these settings.
- Next, we will need to download ESET Poweliks Cleaner from the below link:
ESET POWELINKS CLEANER DOWNLOAD LINK (This link will download ESET Poweliks Cleaner on your computer) - Once the ESET Poweliks Cleaner tool has been downloaded, look for the file called ESETPoweliksCleaner.exe on your desktop and double-click it.
- You will now be shown the main screen for the ESET Poweliks Cleaner and it will begin to search for the infection. If the tool detects Poweliks, it will state that it found it and then ask if you wish to remove it.
If Poweliks is detected, then press the Y button on your keyboard. ESET Poweliks Cleaner will now remove the Poweliks trojan from your computer.
STEP 2: Remove Trojan.Poweliks virus with Malwarebytes Anti-Malware Free
Malwarebytes Anti-Malware Free uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.
It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Anti-Malware Free) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup-consumer-2.00.xx” to start the installation of Malwarebytes Anti-Malware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.
To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the “Fix Now” button.
Alternatively, you can click on the “Scan” tab and select “Threat Scan“, then click on the “Scan Now” button.
- Malwarebytes Anti-Malware will now check for updates, and if there are any, you will need to click on the “Update Now” button.
- Malwarebytes Anti-Malware will now start scanning your computer for the Trojan.Poweliks virus. When Malwarebytes Anti-Malware is scanning it will look like the image below.
- When the scan has completed, you will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Quarantine All” button, and then click on the “Apply Now” button.
Please note that the infections found may be different than what is shown in the image. - Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another “Threat Scan” scan to verify that there are no remaining threats
STEP 3: Remove Trojan.Poweliks infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti-virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows). When the program starts you will be presented with the start screen as shown below.
Click on the “Next” button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for Trojan.Poweliks malicious files.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove Trojan.Poweliks virus.
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
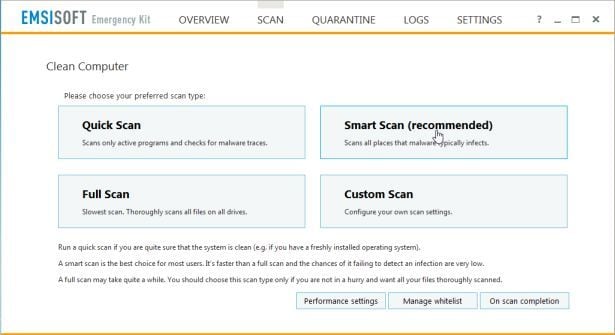
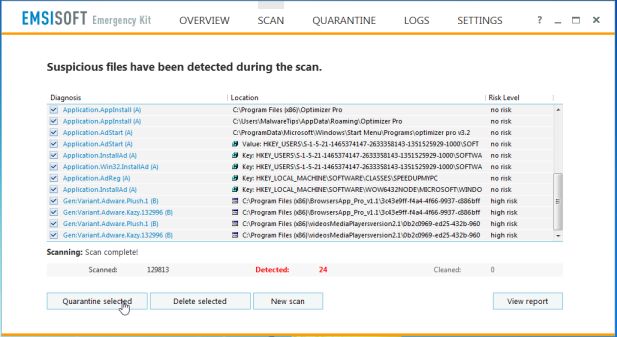
STEP 4: Double check for any left over infections with Emsisoft Emergency Kit
The Emsisoft Emergency Kit Scanner includes the powerful Emsisoft Scanner complete with graphical user interface. Scan the infected PC for Viruses, Trojans, Spyware, Adware, Worms, Dialers, Keyloggers and other malicious programs.
- You can download Emsisoft Emergency Kit from the below link.
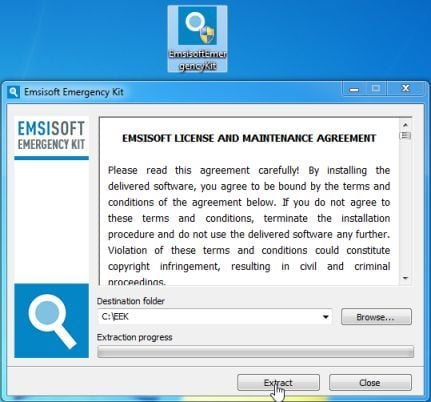
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - Double-click on the “EmsisoftEmergencyKit” icon, then click on the “Extract” button.
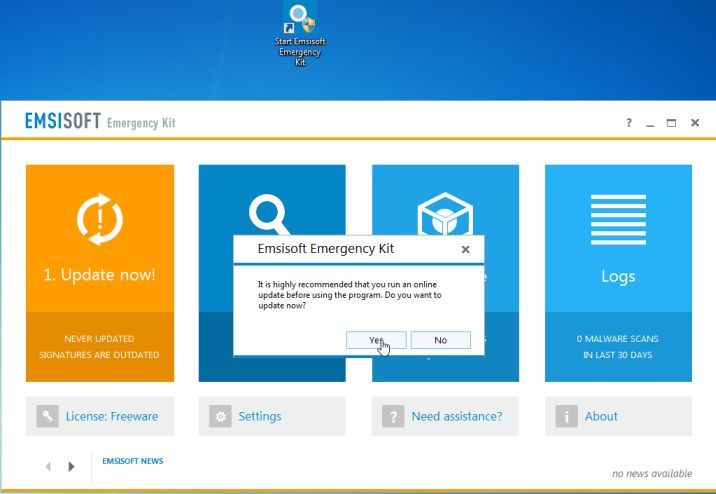
- On your desktop you should now have a “Start Extract Emsisoft Emergency Kit” icon, double-click on it, then when the program will start allow it to update its database.
- Once the Emsisoft Emergency Kit has update has completed,click on the “Scan” tab, and perform a “Smart Scan“.
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.


![Malwarebytes Anti-Malware setup program [Image: Malwarebytes Anti-Malware setup program]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/Malwarebytes-Anti-Malware-Setup.jpg)
![Malwarebytes Anti-Malware Setup Wizard [Image: Malwarebytes Anti-Malware Setup Wizard]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-installation.jpg)
![Malwarebytes Anti-Malware Final Setup Screen [Image: Malwarebytes Anti-Malware Final Setup Screen]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-final-screen.jpg)
![How to remove Trojan.Poweliks virus (Removal Guide) 2 [Image: Click on the Fix Now button to start a scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-fix-now.jpg)
![Malwarebytes Anti-Malware Threat Scan [Image: Malwarebytes Anti-Malware Threat Scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-threat-scan-option.jpg)
![Click on Update Now to update Malwarebytes Anti-Malware [Image: Click on Update Now to update Malwarebytes Anti-Malware]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-2-0-update-now.jpg)
![Malwarebytes Anti-Malware while performing a scan [Image: Malwarebytes Anti-Malware while performing a scan]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-scan.jpg)
![Remove the malware that Malwarebytes Anti-Malware has detected [Image: Remove the malware that Malwarebytes Anti-Malware has found]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-potential-threat-detected.jpg)
![Malwarebytes Anti-Malware asking to reboot your computer [Image: Malwarebytes Anti-Malware while removing viruses]](http://malwaretips.com/blogs/wp-content/uploads/2014/02/malwarebytes-anti-malware-remove-virus.jpg)
![HitmanPro startup screen (Click Next) [Image: HitmanPro start-up screen]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-install.jpg)
![HitmanPro installation options (Click Next) [Image: HitmanPro setup options]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmapro-start-scan.jpg)
![HitmanPro scanning for Trojan.Poweliks [Image: HitmanPro scanning for malware]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scanning.jpg)
![HitmanPro scan results (Click Next) [Image: HitmanPro scan results]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-scan-results.jpg)
![Click on the Activate free license button [Image: HitmanPro Activate Free License]](http://malwaretips.com/blogs/wp-content/uploads/2014/03/hitmanpro-activation.jpg)








thank you for the help
Awesome. It worked for me!! Thank you Stelian!!