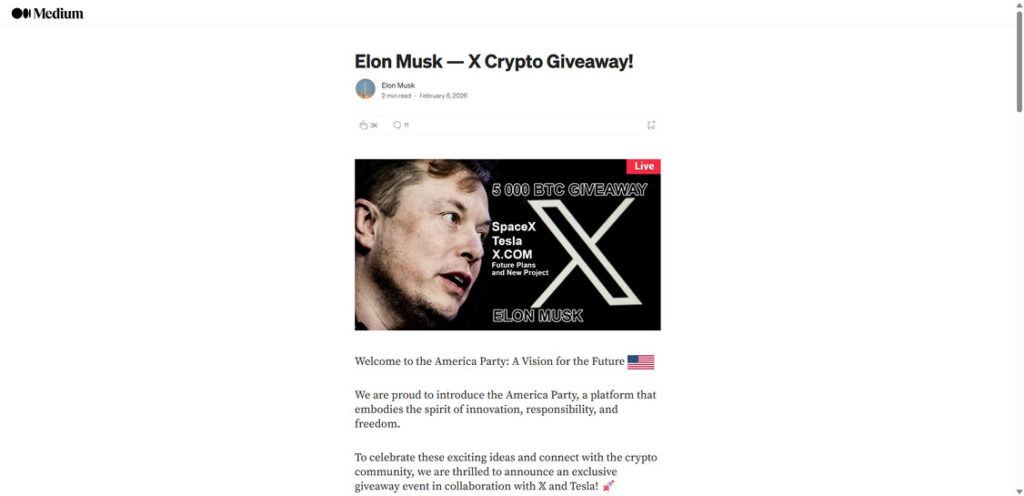
If you have been around crypto long enough, you have probably seen at least one “celebrity giveaway” link that looks surprisingly polished. This one is making the rounds again with a very specific hook: an Elon Musk themed “X Crypto Giveaway” claiming a 5,000 BTC giveaway is live right now.
The pitch is built to feel effortless. A page styled like a quick article, a big banner image, and a few bold lines that make it sound like an official event. Then you hit the call to action and land on a portal with a QR code, a wallet address, and a promise that sounds almost too clean: send Bitcoin to “verify” your address and you will get x2 back immediately.
That is the moment where people lose money, because the page is not trying to “verify” anything. It is trying to get you to send crypto first, before you pause long enough to ask the only question that matters: why would a real giveaway ever need your Bitcoin upfront?
Scam Overview
The Elon Musk 5,000 BTC giveaway scam is a classic crypto theft scheme packaged in a modern, high-converting design. It uses the most effective ingredients scammers have in this space: a famous name, a massive number, and a simple “send first, receive more back” promise that preys on urgency and excitement.
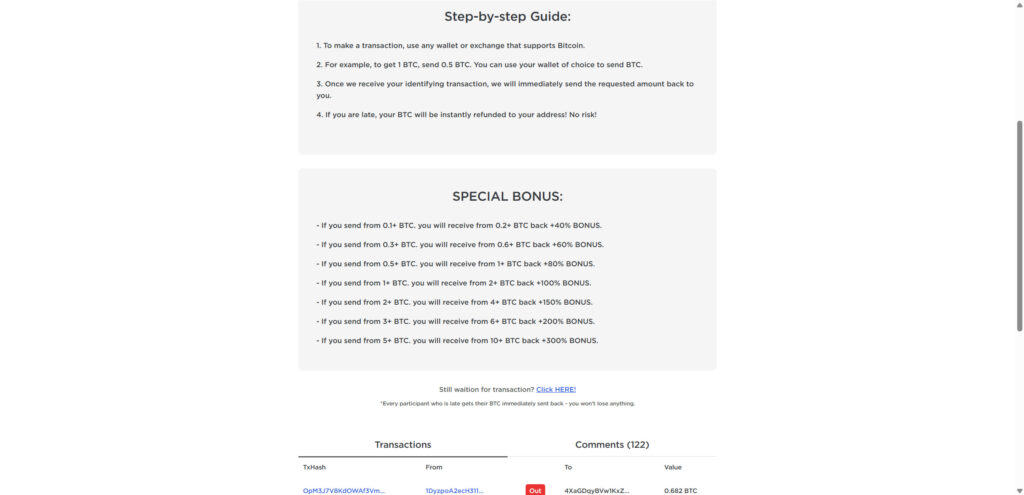
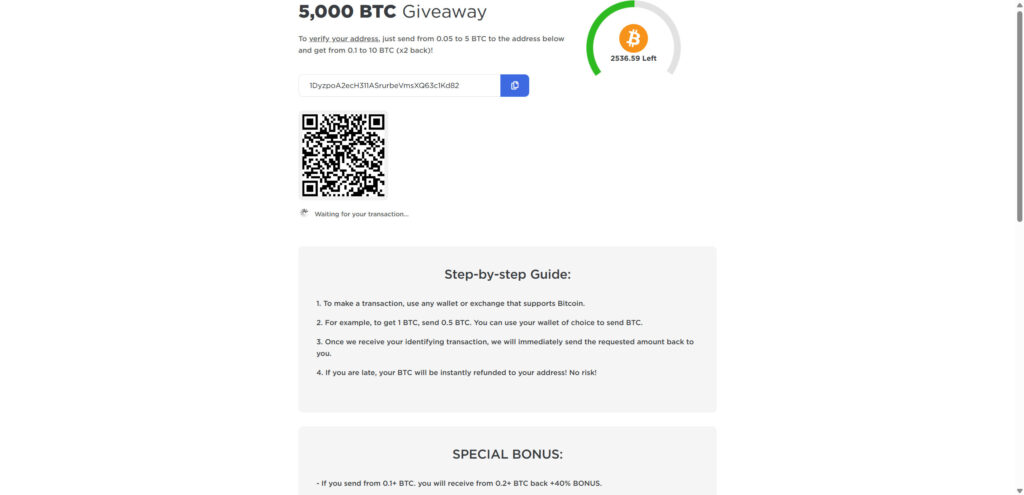
What makes this version stand out is how carefully it stages the story. The scam sites are presented like a short post titled “Elon Musk – X Crypto Giveaway!” with a banner that implies a live event and a limited supply. It then funnels victims into a dedicated “5,000 BTC Giveaway” page that looks like a real campaign site, complete with:
- A large headline announcing the giveaway
- A “left” counter (for example, thousands of BTC “remaining”)
- A wallet address field with a copy icon
- A QR code for fast mobile payments
- A “waiting for your transaction” status message
- A step-by-step guide that explains exactly how to send
- “Special bonus” tiers that promise higher returns at higher deposit amounts
- A transaction table labeled with “In” and “Out” entries
- A comment counter that suggests hundreds of people are participating
None of this is evidence of legitimacy. It is a conversion funnel.
The core lie: “Send crypto to get more back”
At the center of the scam is a claim that never changes across versions:
You send Bitcoin first, and you receive more Bitcoin back.
Sometimes it is framed as “x2 back.” Sometimes it is framed as “verify your address.” Sometimes it is wrapped in “bonus tiers” and “limited allocation” language. The mechanics are always the same: you transfer real crypto into a wallet controlled by the scammer, and you receive nothing in return.
The scam sites explicitly instructs visitors to send from 0.05 to 5 BTC and promises from 0.1 to 10 BTC back (x2 back). This is the most important detail, because it confirms the scam pattern beyond any debate. A legitimate giveaway does not require participants to send funds first, and it definitely does not promise to double deposits on demand.
Why the “5,000 BTC” number is bait
The 5,000 BTC headline is not there to be realistic. It is there to create a sense of scale and urgency.
A huge number does three things for scammers:
- It makes the event feel “global” and important.
- It encourages victims to rationalize risk: “If this is that big, it must be real.”
- It distracts from the one detail that should stop you cold: the upfront payment request.
They often pair the number with scarcity cues, like a progress ring showing how much is “left,” or a note implying the giveaway ends soon. That scarcity pressure is one of the strongest drivers of impulsive sending.
The scam borrows trust from real brands and platforms
This scam heavily leans on the public familiarity of:
- X branding and language
- Tesla and the idea of “official” giveaways
- SpaceX associations that make the theme feel plausible
- Medium style formatting, which makes it look like an article, not a scam page
The scam sites post even claims a grand prize and “collaboration” vibe, then tries to push users to click “official” links for BTC, ETH, and DOGE.
This is a credibility trick. The scammer knows most people will not verify partnerships. They just need the page to feel believable for 20 seconds.
Fake “official” links and a fake contact email
The scam sites include a set of links like:
- “Click this official link to get BTC”
- “Click this official link to get ETH”
- “Click this official link to get DOGE”
It then claims that if you send 1 BTC, 50 ETH, or 500,000 DOGE, you will receive bonus crypto plus a grand prize vehicle. It even instructs victims to email a supposed “official” address like giveaway@tesla.com with a screenshot of the transaction.
This is not how real companies operate. A legitimate brand does not run a promotion where you send funds to a random address, then email a screenshot to coordinate a prize. That is a scammer’s fantasy version of “customer support,” designed to keep you engaged and potentially extract more money later.
The “step-by-step guide” is engineered for one purpose: reduce hesitation
The “Step-by-step Guide” on the giveaway page is especially revealing because it is written like a set of simple instructions for a normal process:
- Use any wallet or exchange that supports Bitcoin.
- Example: to get 1 BTC, send 0.5 BTC.
- Once your identifying transaction is received, funds will be sent back immediately.
- If you are late, your BTC will be refunded instantly. “No risk.”
Each line is crafted to remove a specific fear:
- “Any wallet works” removes friction.
- “Example amounts” makes the scam feel routine.
- “Identifying transaction” adds technical-sounding legitimacy.
- “Refunded instantly, no risk” tries to neutralize the biggest emotional barrier.
But the blockchain does not work on promises. Once you send Bitcoin to a scammer’s address, they control it. There is no forced refund mechanism.
The “special bonus” tiers are designed to pull larger deposits
The “Special Bonus” section is another high-pressure tactic. It offers escalating returns as the deposit amount increases. For example, it promises higher bonus percentages at higher deposit tiers, going all the way up to extremely large “bonus” claims.
This is not random. Many victims might consider testing with a small amount. The bonus ladder attempts to push them into sending more by making the “small test” feel like a wasted opportunity.
This is also why scammers often set minimums like 0.05 BTC. They want the initial loss to be large enough to matter.
The fake transaction table and fake comments are social proof tools
On the giveaway page, the “Transactions” section shows what looks like real activity:
- TxHash links
- “From” and “To” fields
- “In” and “Out” markers
- BTC values
It may even show a mix of inbound and outbound activity to suggest payouts are happening.
This is a common deception technique. The table can be:
- Completely fabricated data displayed as if it is live
- Random hashes and addresses pulled from elsewhere and repurposed
- Real deposits into the scam wallet, misrepresented as “proof” that the giveaway pays out
- A mix of deposits and the scammer’s own wallet shuffling, staged to look like payouts
The comment section does the same thing in plain language. It creates the impression that regular people are receiving BTC and thanking “Elon,” which nudges hesitant visitors toward sending.
“Elon Musk has nothing to do with this” is not just a disclaimer, it is the key fact
This part matters because scammers build these pages to make you feel like you are interacting with an official campaign. You are not.
Elon Musk is not running a 5,000 BTC giveaway, and he is not asking people to send Bitcoin to receive double back. Real giveaways do not operate through random domains like elonxprize.com and clones that appear and disappear.
This scam is a theft operation. Victims send crypto. Victims receive nothing. The branding is just bait.
How The Scam Works
Although the design can vary, the Elon Musk 5,000 BTC giveaway scam follows a predictable playbook. Understanding the flow is useful because it helps you recognize the next version, even if the domain name and layout change.
Step 1: You encounter the bait where trust already exists
Most people do not search for “5,000 BTC giveaway scam” first.
They see something that looks like an announcement:
- A post styled like a short article
- A graphic that says “LIVE” and “5,000 BTC Giveaway”
- A headline that references X, Tesla, SpaceX, or “official” language
- A link that claims you can choose BTC, ETH, or DOGE
The scam relies on quick pattern recognition. You recognize the name, you recognize the brand vibe, and you assume there is at least a chance it is real.
Step 2: The scam adds a story to lower your defenses
The campaign is framed like a “Medium-style” post. That matters because it changes how your brain reads the page.
A clean article layout feels informational. It does not feel like a transaction page. The story also adds emotional context, like “building the future,” “community,” and “limited-time celebration.”
This is not about informing you. It is about getting you to click the next link without doing a verification check.
Step 3: The “official link” buttons push you into the funnel
The post includes obvious calls to action that look safe:
- “Click this official link to get BTC”
- “Click this official link to get ETH”
- “Click this official link to get DOGE”
These links are the funnel entry points. They route you to the scam portal where the wallet address and QR code appear.
Once you are there, the scammer is no longer selling you an idea. They are trying to make you send.
Step 4: The giveaway portal presents a simple, structured process
When victims land on the portal, the scam is framed as a predictable sequence:
- Verify your address by sending BTC
- Receive x2 back immediately
- Enjoy a limited-time allocation
- Watch “live” transactions proving it works
This is why the page includes a “Step-by-step Guide.” It reads like customer onboarding.
The page is engineered for low-friction execution. You do not have to sign up, read terms, or connect anything. You just copy an address and send.
That simplicity is not generosity. It is optimization.
Step 5: The QR code and copy button remove the last moment of hesitation
Many victims hesitate because entering a wallet address manually is scary. Scammers know that.
So they provide:
- A “copy address” icon
- A large QR code
- A “waiting for your transaction” status line that makes it feel like the system is ready
This is the moment where people convince themselves it is safe, because it feels so operational.
But operational does not mean legitimate. A scam can be extremely well built.
Step 6: The “verify your address” wording gives the scam a fake reason to exist
The phrase “verify your address” is doing heavy lifting.
It implies a technical necessity. It makes it sound like the deposit is not really a payment, more like a temporary handshake. Then it promises that once your “identifying transaction” is received, you get the requested amount back.
That is not how verification works in crypto.
Verification is usually done by:
- Signing a message
- Proving wallet ownership through a signature
- Connecting to an official claim portal
You do not verify ownership by giving away Bitcoin.
Step 7: Bonus ladders push higher deposits and larger losses
The “Special Bonus” ladder is not a bonus. It is a upsell.
Here is the psychological effect it creates:
- If a victim sends a small amount, they fear missing out on the bigger return.
- If they already want to test, they might jump straight to a higher tier to “make it worth it.”
- The ladder also normalizes larger deposits by presenting them as common.
That is why these pages often show numbers that feel routine, like 0.5 BTC or 1 BTC, as if that is a normal giveaway participation amount.
Step 8: The transaction table is meant to answer one question: “Is this working for others?”
When a page asks you to send money, your brain naturally looks for proof.
So the scam provides “proof,” typically in two forms:
- A live-looking transactions list
- Comments from “participants” claiming they received payouts
Even if the transactions list contains real deposits, it does not prove anyone received x2 back. It only proves money went in.
This is a subtle but critical distinction.
A legitimate giveaway would have transparent rules, verifiable official channels, and a claim process. This scam has a wallet address and a promise.
Step 9: Victims receive nothing, then get pulled into follow-up traps
After sending BTC, victims usually see one of these outcomes:
- Nothing happens, and the page keeps showing “waiting”
- The page claims congestion and asks the victim to wait
- The victim is prompted to “click here” if still waiting, leading to another page
- A “support” contact appears, encouraging the victim to email or message with proof
- The scam asks for a second payment to “unlock” the payout
That second payment request is extremely common. It might be framed as:
- A “verification fee”
- A “gas fee”
- A “refundable deposit”
- An “activation” requirement
It is never legitimate. It is just the scam trying to extract more money from someone who already sent once.
Step 10: The domain changes, the template survives
Even if one domain gets reported or removed, the scam typically reappears under another lookalike domain, with the same structure:
- Famous name
- Massive giveaway number
- x2 back promise
- QR code and copy button
- Fake proof sections
That is why you should treat domains like elonxprize.com as one example, not the whole threat. The real danger is the pattern.
What To Do If You Have Fallen Victim to This Scam
If you sent crypto to a “5,000 BTC giveaway” address or interacted with the scam site, move quickly and focus on practical containment. You may not be able to reverse the transfer, but you can prevent further losses and improve your chances of meaningful reporting.
- Stop sending funds immediately
- Do not send another deposit for “verification.”
- Do not pay a “fee” to release the payout.
- Do not chase bonuses or tier upgrades.
- This is the most common way victims lose more after the first transfer.
- Save the evidence before the page disappears
- Screenshot the giveaway page, including the wallet address area (do not share it publicly if possible).
- Save the domain name and any redirect chain you can see.
- Save any email addresses, “support” handles, or contact forms shown.
- Save the transaction hash (TXID) for your transfer.
- If you sent from an exchange, contact the exchange immediately
- Open a support ticket and include:
- The TXID
- The destination address
- The amount sent
- The date and time
- The domain you used
- Ask whether they can flag the address internally and assist with reporting.
- Recovery is not common, but fast action is still worth it.
- Open a support ticket and include:
- If you sent from a personal wallet, assume the transfer is permanent
- Bitcoin transactions are generally irreversible.
- Do not waste time believing the site will “refund” you.
- Shift your effort to preventing follow-on theft and documenting the incident.
- Figure out whether you only sent BTC or also connected a wallet
- If you only sent BTC, the scammer typically cannot drain the rest of your wallet automatically.
- If you connected a wallet, signed anything, or approved token permissions on another chain, treat it as higher risk.
- If you connected a wallet or approved permissions, move remaining funds
- Move assets to a new wallet you control.
- Use a clean device if possible.
- Then revoke any suspicious approvals using a reputable approval management tool for the chain involved.
- Secure your email and exchange logins
- Change passwords for your email, exchange accounts, and any account that shares the same password.
- Enable 2FA wherever possible.
- Email is critical because it controls password resets.
- Check your device and browser for unwanted software
- Review installed browser extensions and remove anything you do not recognize.
- Run a reputable malware scan.
- If you reached the scam through pop-ups or redirects, be extra cautious about adware and unwanted extensions.
- Watch for “recovery” scams
- After victims post online, scammers often message them claiming they can recover stolen crypto.
- They usually demand an upfront “service fee.”
- This is almost always a second scam targeting people who are already stressed.
- Report the scam domain and wallet address
- Report the domain to its registrar and hosting provider.
- Report the scam page through your browser’s phishing reporting tool.
- If you are in the United States, file a report with FBI Internet Crime Complaint Center (IC3).
- Report the address on chain explorers and scam databases if they provide a reporting option.
- If you lost a significant amount, consider a police report
- Bring:
- Screenshots
- TXID
- Destination address
- Domain name
- Timeline of events
- Even if recovery does not happen, a formal record can help with broader investigations.
- Warn others where you saw it
- If the scam came through social media, reply with a short factual warning:
- “This is a send-first giveaway scam. Do not send crypto.”
- You do not need to argue with the scammers. Your goal is to slow down the next victim.
The Bottom Line
The Elon Musk 5,000 BTC giveaway scam is not a real giveaway and it is not connected to Elon Musk, X, Tesla, or SpaceX. It is a polished theft page built around a single irreversible action: getting you to send crypto first in exchange for a promise of more later.
The design elements are there to push you past hesitation: the QR code, the “left” counter, the step-by-step guide, the bonus tiers, and the transactions table that looks like proof. But none of those features change the underlying reality.
If you already sent funds, do not send anything else. Document what happened, secure your accounts and devices, and report the domain and transaction details. The best protection going forward is simple and consistent: any “giveaway” that requires you to send crypto first is not a giveaway. It is the scam.
FAQ
Is the “Elon Musk 5,000 BTC giveaway” real?
No. This is a send-first crypto scam. The page is designed to get you to transfer Bitcoin to the scammer’s wallet by promising you will receive 2x back.
Does Elon Musk have anything to do with this giveaway?
No. Scammers use famous names to borrow credibility and reduce skepticism. The branding is bait, not proof.
Why do these pages say “verify your address” by sending BTC?
Because it sounds technical and harmless, like a temporary check. In reality, it is simply an upfront payment request. Sending BTC does not “verify” anything for a giveaway.
How does the “2x back” promise actually work?
It does not. The scam relies on the fact that Bitcoin transfers are generally irreversible. Once you send BTC, the scammer can keep it and move it quickly.
The site shows transactions and “In/Out” activity. Does that prove it is paying people?
No. Those transaction tables are commonly faked, staged, or misleading. Even if you see real deposits going into the wallet, that does not prove anyone is receiving payouts.
Why is the giveaway amount so huge, like 5,000 BTC?
A big number creates urgency and makes the offer feel “major.” It also helps victims rationalize risk: “If it’s this large, it must be real.” That reaction is exactly what the scam is trying to trigger.
What is the purpose of the QR code and the copy address button?
Speed. The faster you can send, the less time you have to second-guess it. QR codes also make it easy to pay from a phone, which increases conversion for scammers.
What does “Waiting for your transaction” mean?
Usually, nothing. It is a psychological hook that keeps you on the page after you send BTC, so you hesitate less if they push you toward another step or another payment.
Why do they offer “special bonus” tiers for bigger deposits?
To encourage larger losses. Bonus ladders are a pressure tactic that makes a small test payment feel like you are missing out, nudging people into sending more than they planned.
I sent Bitcoin. Can I get it back?
In most cases, no. Bitcoin transactions are typically irreversible. If you sent from an exchange, contact the exchange immediately and provide the transaction hash and destination address. Recovery is still uncommon, but fast reporting matters.
If I sent BTC from my own wallet, can they drain the rest of my wallet?
If you only sent BTC to their address, they usually cannot drain your wallet just from that transfer.
However, if you connected a wallet, approved permissions, or signed anything on a related site, assume higher risk and move remaining funds to a new wallet.
They asked me to send a second payment to “unlock” the payout. Should I?
No. That is a common second-stage move. “Verification,” “release,” “activation,” or “fee” payments are designed to pull more money from victims who already sent once.
The scam site lists Tesla and SpaceX. Does that make it legitimate?
No. Scammers frequently reference Tesla and SpaceX to make the story feel believable. Name-dropping is not verification.
Why does it look like a Medium post or a real article?
Because a familiar article format lowers your defenses. Pages styled like Medium content feel informational, so users click through more readily.
What are the clearest red flags that confirm it’s a scam?
Common signs include:
- Any promise of “send BTC and get more back”
- “Verify your address” wording that requires a deposit
- A huge “5,000 BTC” claim paired with scarcity counters
- Bonus tiers pushing higher amounts
- A QR code and copy button front and center
- “Recent transactions” and comments used as social proof
How do I report this scam?
Report the domain to its registrar and hosting provider, report the page as phishing in your browser, and file a complaint with FBI Internet Crime Complaint Center (IC3) if you are in the United States. If you used an exchange, also report the destination address to the exchange support team.
If you want, I can also generate 3 post highlights and a tagline for this 5,000 BTC version, tailored to make readers click without giving away the whole article.







