A troubling new scam involving fraudulent McAfee PayPal invoices aims to trick unsuspecting victims into handing over their hard-earned money. This scam starts with an email pretending to come from McAfee, the well-known cybersecurity company.
The fake email includes an official-looking PayPal invoice claiming you purchased or renewed McAfee software and owe payment. If you call the phone number provided, scammers posing as McAfee support agents answer and aim to steal your money through sly manipulation tactics.
This scam is often a precursor to remote access tech support scams, where criminals gain control of your computer under the guise of refunding the charges. From there, victims get pressured into paying the fake fees via unrecoverable methods benefitting only the scammers.
By learning how to detect telltale signs these messages are phishing attempts, you can avoid losing money to this insidious scam. Keep reading to understand how the McAfee PayPal invoice scam works, what to watch out for, and steps to take if you fell victim already.
Overview of the McAfee PayPal Invoice Scam
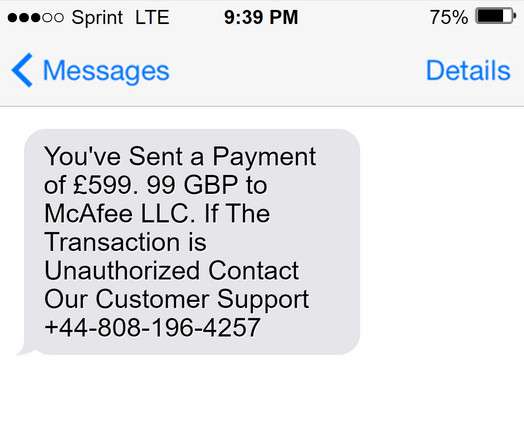
This scam typically starts when potential victims receive an unsolicited email or text message crafted to appear to be from PayPal.
The sender name, email address, and messaging are spoofed to impersonate PayPal’s branding and communication style. The subject line usually says something like “Your McAfee Order Receipt” or “Unauthorized Transaction from McAfee.”
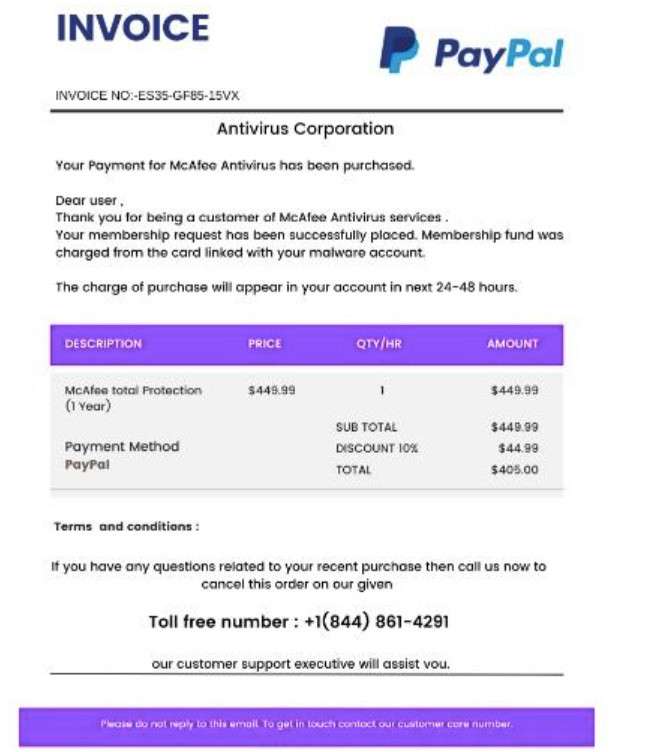
The body of the email or text is formatted to mimic a PayPal invoice receipt, including:
- Fake PayPal letterhead and logos
- A phony order or transaction number
- The victim’s name and partial billing address
- An item such as “McAfee Total Protection Subscription”
- A 1 or 2-year subscription term
- The amount owed, usually $300 to $500
The message states that this unauthorized payment was processed through the recipient’s PayPal account for a service they did not request.
It provides a customer support phone number to call to dispute the unauthorized charge and potentially receive a refund. However, this phone number actually routes to a fraudulent overseas call center.
By initially impersonating PayPal through clever spoofing techniques, the scammers aim to convince victims that unauthorized payments were made through their real PayPal account. This tricks them into calling the number assuming they will reach PayPal’s customer support team, when in reality they will be connected to criminal scammers intending to steal their money.
How the McAfee PayPal Invoice Scam Unfolds Step-by-Step
Let’s walk through how scammers leverage this scam stage-by-stage to ultimately steal funds from unsuspecting victims:
Step 1: Victims Receive the Phishing Email or text message
The scam starts with victims receiving an unsolicited email or text message crafted to mimic a receipt from McAfee. The sender name, subject line, and formatting make the email appear credible on first glance.
Common phishing techniques like slight variations in the sender address or typos can reveal it’s fraudulent upon closer inspection. But most busy recipients glance quickly and assume the email is legitimate.
Step 2: Victims View the Fake PayPal Invoice
When victims click the “View Invoice” link, it takes them to a spoofed PayPal billing page replicating the same fake order details. This adds further legitimacy and urgency since it seems to confirm charges were made via PayPal.
In reality, the scammers created the phony PayPal invoice using the company’s branding without their consent. But it appears real enough to deceive victims.
Step 3: Victims Call the Scam Support Number
The fake invoice displays a customer support phone number to inquire about the charges or request a refund. This tricks victims into calling the number assuming it reaches real McAfee representatives.
However, the phone number routes to a fraudulent overseas call center staffed by skilled scammers impersonating McAfee tech support agents. Their only goal is to steal money from callers.
Step 4: Scammers Gain the Victim’s Trust
When victims call the scam number, the criminal pretenders initially pose as helpful McAfee reps. They play along expressing concern about the charges, promising to request a refund from PayPal.
This builds trust and makes victims think the scammers are on their side, when in reality they are plotting to scam them using psychological tricks.
Step 5: Scammers Infiltrate the Victim’s Computer
Once they gain the victim’s confidence, the scammers shift the call saying they also need to access the victim’s computer to process the refund and investigate how the fake transaction occurred.
The criminals convince victims to download screensharing apps like AnyDesk that grant the scammer full remote control over the victim’s computer, networks, files, and more.
Step 6: Scammers Manipulate the Victim’s Screens
Now able to manipulate everything the victim sees on their screen, the criminals open other applications and change elements using inspect tools.
For example, they can display fake error messages and warnings about hackers in the system. Or they alter banking screens to show unauthorized transfers made to themselves that they can reverse for an fee.
Step 7: Victims Pay the Criminals
Between the fake invoice and altered banking screens, the criminals now have multiple ways to convince victims to willingly pay them. They pose as McAfee techs and claim the only way to fix the issues and refund the scam charges is for the victim to pay them or purchase gift cards.
Sadly, many victims are manipulated into wiring sums of money or revealing gift card numbers that the scammers quickly steal. Victims think they are getting refunds, when in reality they are paying criminals.
How to Spot the Scam Emails and Texts
It’s crucial to know how to recognize the phishing emails and texts used to deceive victims in this scam. Here are tips to identify the warning signs:
Inspect the Sender’s Email Address and Name
Carefully check that the email address appears exactly as “service@paypal.com” or another official PayPal domain. Scammers often use slight misspellings or extra characters to spoof it.
Also ensure the sender name matches “PayPal” or a verified PayPal entity. hover over any links to check where they really direct to.
Verify the PayPal Logos and Branding
Closely examine the logo images and overall branding in the email or text. Fraudsters often use low-quality versions of logos and fonts. Make sure colors, fonts, and images match PayPal’s professional branding.
Watch for Poor Grammar and Spelling
Phishing scams often contain typos, grammatical mistakes, and other writing errors because they are from foreign scammers. The texts may read unprofessionally compared to PayPal’s legitimate customer service messages.
Scrutinize the Message Formatting
While scammers try to mimic PayPal’s formatting, subtle details like font choices and text placement may differ from real messages. Compare to verified emails from PayPal to detect discrepancies.
Check the Urgency Level
Scams create false urgency to get victims to act fast without thinking. Phrases like “urgent action required” or “call immediately” indicate a likely scam attempt. PayPal provides time to resolve issues.
Look for Strange Attachments
Do not open attachments in unsolicited emails, as they can release malware. PayPal does not send emails with random attachments you need to open.
Verify it Elsewhere
Don’t trust the email or text alone. Log in directly to your PayPal account to check recent activity for any unauthorized transactions before believing the messages.
With close inspection and awareness of common phishing techniques, you can hopefully identify scam PayPal emails and texts before being deceived. Reach out directly to PayPal if you have any uncertainties.
What to Do if You Already Fell Victim to This Scam
If you already got deceived by this scam, stay calm and take these steps right away:
- Contact your bank immediately: Notify your bank you authorized payments to scammers by mistake. Disputed fraudulent transfers and freeze your account if needed.
- Call gift card companies: If you revealed gift card numbers, call the retailer and request they immediately cancel the codes before the criminals can redeem them.
- Report it to authorities: File a report about the fraud with the FTC, FBI, state authorities, and local law enforcement. Provide all details to aid investigations.
- Alert companies impersonated: Contact McAfee and PayPal to make them aware their name is being used to defraud people. They may help get fake sites and numbers shut down.
- Monitor your credit and accounts: Check for any further misuse of your personal information now that scammers had access. Enable extra security like multifactor authentication wherever possible.
Avoiding the McAfee PayPal Invoice Scam
Here are smart precautions to avoid falling for this scam:
- Be wary of unexpected emails about software renewals or charges. Verify by logging into your accounts.
- Check sender email addresses for spoofing. Ensure it comes from an official McAfee domain.
- Inspect URLs before clicking. Hovers to reveal the actual destination.
- Call official customer support numbers listed on real McAfee sites if you have billing issues. Avoid numbers in emails.
- Never let strangers remotely access your computer, even if they claim to be helping you. Refuse demands to install sketchy software.
- Use strong passwords and change them routinely. Enable two-factor authentication where possible.
- Keep software updated and use comprehensive antivirus protection to stop malware infections.
Frequently Asked Questions About the Fake McAfee PayPal Invoice Scam
What is the McAfee PayPal invoice scam?
This is a fraudulent scam where scammers send phishing emails pretending to be PayPal invoices from McAfee for a software subscription you didn’t purchase. The emails include a customer support number to call about the charge, but it routes to criminal call centers intent on stealing your money.
How does the scam email or text look?
The phishing messages are disguised as invoices from PayPal showing an order from McAfee that you never placed. They use logos and branding from both companies and have details like a fake order number, billing address, subscription term, and amount owed.
Does the message actually come from PayPal or McAfee?
No, the sender just spoofs PayPal and McAfee’s information to make it seem real. Scammers fake the “From” email address, phone numbers, and branding without permission from either company.
What happens if I call the customer support number?
The number goes to an overseas scam call center instead of PayPal or McAfee support. Criminals impersonating tech support agents answer and pretend to help dispute the charges while actually gaining remote access to steal your personal information and money.
How do the criminals gain remote access?
The fake support agent claims they need to initiate a remote session to process your refund and investigate the issue. They guide you through downloading screensharing apps like AnyDesk that let them control your computer, masking it as part of the process.
What do the scammers do with remote access?
Having control of your screen allows the criminals to manipulate what you see and do on your device. They can steal data, install malware, display fake error messages, and alter banking screens to show unauthorized transfers out of your account to pressure you to pay.
How can I avoid this scam?
Be wary of surprise billing emails. Verify senders are real PayPal domains. Never call numbers in suspicious emails. Check your PayPal account directly. Don’t allow remote access to callers. Use strong unique passwords and update software. Know the warning signs of phishing scams.
The Bottom Line
The fake McAfee PayPal invoice scam preys on unsuspecting victims by posing as trusted companies charging money. But awareness of the manipulative red flags and deceptive techniques can help you avoid being swindled. Legitimate firms don’t send unsolicited billing emails out of the blue. Report phishing scams if you come across them and warn others about this fraud. Spreading awareness is key to protecting more people and putting these scammers out of business.







