When shopping online, it’s critical to thoroughly research unfamiliar e-commerce sites before making purchases. Professional scammers easily create convincing fake storefronts to defraud customers. This article examines the concerning signs found on Kljhltd.com as a case study for vetting unknown retailers.
Warning Signs on Kljhltd.com Warrant Caution for Shoppers
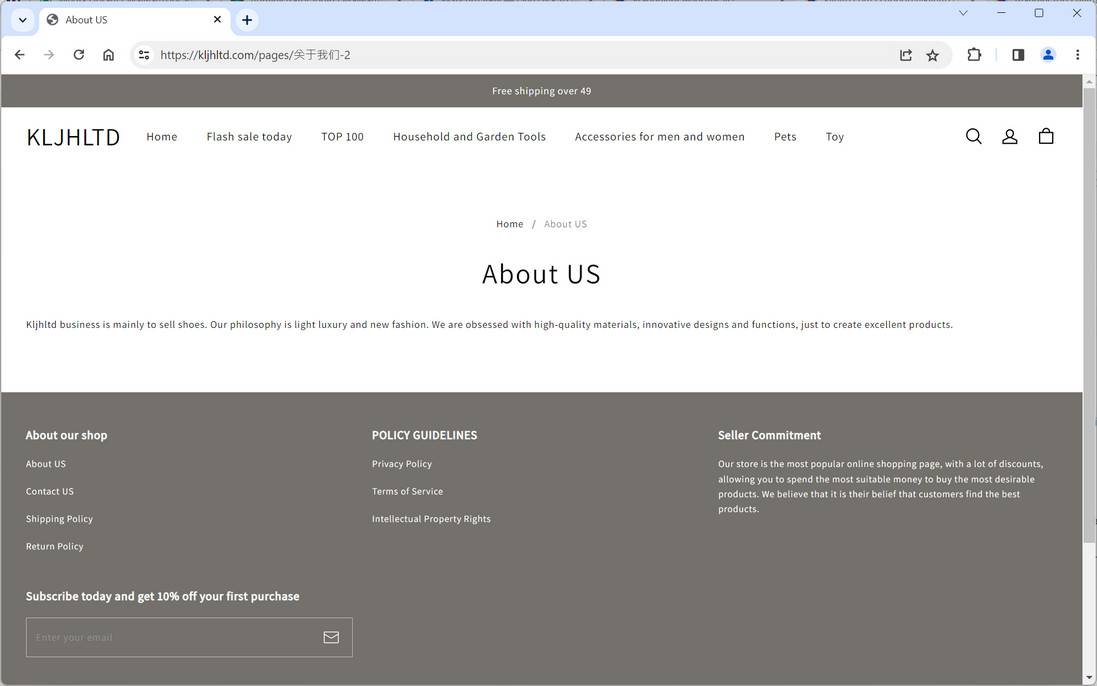
While Kljhltd.com looks professional at first glance, several red flags emerge upon closer examination:
Missing Company Transparency
Reputable retailers provide background like years in business, location addresses, leadership team details, and customer service options. Kljhltd.com shares none of this standard company information, eroding trustworthiness.
Recently Registered Domain
A Whois domain lookup shows Devcarry.com was recently registered, indicating the site is likely not an authentic long-standing business.
Stolen Product Images
Reverse image searches reveal Kljhltd.com’s product photos are copied from overseas wholesalers. This indicates the inventory may be fabricated, not real items they can ship.
Plagiarized Website Content
Large sections of Kljhltd.com’s shipping, returns, and privacy policies are stolen from unrelated sites. The lack of original content demonstrates low effort invested.
No Social Media Presence
Legitimate e-commerce brands maintain social media accounts for customer engagement. But Kljhltd.com has no external social profiles, preventing vetting through other channels.
No Customer Reviews
All major retailers accumulate at least some independent customer reviews over time. The total lack of reviews for Kljhltd.com aligns with a fraudulent new business.
Exercise Abundant Caution Before Ordering
While not definitive proof of ill intent, these multiple credibility gaps provide reasonable grounds for consumer skepticism. Shoppers should exercise extreme caution sharing payment or personal information with Kljhltd.com until legitimacy can be verified. Monitor bank accounts closely if you’ve already ordered for unauthorized charges. Also prepare for potentially undelivered, late, or misrepresented products.
Vetting Online Retailers Protects Consumers
To avoid scams, consumers should thoroughly research unknown e-commerce sites before buying. Search for reviews, complaints, transparency, social proof, and other indicators of authenticity. Prioritize retailers that have consistently demonstrated ethical business practices and satisfied customers over many years. If your instincts warn that a site seems suspicious, listen and scrutinize further or avoid ordering altogether. Paying attention to warning signs can help internet shoppers safely access expanded options while avoiding deceitful merchants. Scrutinize before you buy.
Summary: Verify Before Engaging with Unfamiliar Sites
Kljhltd.com cannot be definitively classified as illegitimate with limited information. However, prudent shoppers should still approach with ample skepticism until transparency and customer satisfaction are proven over time. Insufficient evidence exists to recommend trusting them with payments or personal data. Consumers carry all risks when engaging with unverified websites.
Instead, seek out established e-commerce businesses with long histories of customer service and satisfaction readily confirmed through research. Protect yourself by verifying legitimacy before providing money or information to unfamiliar online retailers. Exercise wise caution to shop safely.