LoadTubes is a potentially unwanted program, which will display advertisements, pop-up ads and sponsored links on Youtube and other websites that you are visiting.
LoadTubes is a browser plugin for Internet Explorer that is typically added when you install another free software (video recording/streaming, download-managers or PDF creators) that had bundled into their installation this adware program. When you install these free programs, they will also install LoadTubes as well. Some of the programs that are known to bundle LoadTubes include 1ClickDownload, Yontoo and FBPhotoZoom.
Once installed, whenever you will watch a video on Youtube, LoadTubes will display a “Song Download” button, which will allow you to download into a mp3 format.
LoadTubes is an ad-supported software, so this program will also display targeted advertisements and pop-ups within the web pages you are viewing. Because of this, Loadtubes is classified as an adware program, and will install various BHOs (Browser Helper Objects) in Internet Explorer.
Loadtubes is seen by many security vendors as a malicious program, and generally classified as adware:
- Avira – Adware / BHO.S
- Avast – Win32: Adware-gen [Adw]
- BitDefender – Trojan.Agent.AWUR
- Emsisoft – Adware.Win32.BHO (A)
- F-Secure – Adware.Generic
- Kaspersky – AdWare.Win32.BHO
- Malwarebytes Anti-Malware – PUP.Loadtubes
You should always pay attention when installing software because often, a software installer includes optional installs, such as this LoadTubes adware. Be very careful what you agree to install.
Always opt for the custom installation and deselect anything that is not familiar, especially optional software that you never wanted to download and install in the first place. It goes without saying that you should not install software that you don’t trust.
PUP.LoadTubes – Virus Removal Instructions
STEP 1 : Uninstall LoadTubes from your computer
- To uninstall LoadTubes from your computer, click the Start button, then select Control Panel, and click on Uninstall a program.
If you are a Windows 8 user, you can right-click on a bottom left hot corner (formerly known as the Start button) and select Control panel from there, then select Uninstall a program.
- When the Add/Remove Programs or the Uninstall a Program screen is displayed, scroll through the list of currently installed programs and remove LoadTbs from your computer.
STEP 2 : Remove the LoadTubes plugin from Internet Explorer
- Open Internet Explorer,then click on the gear icon
(Tools for Windows XP users) at the top (far right), then select Manage add-ons.
- From the Toolbars and Extensions tab, select LoadTubes plugin, and click on Disable.
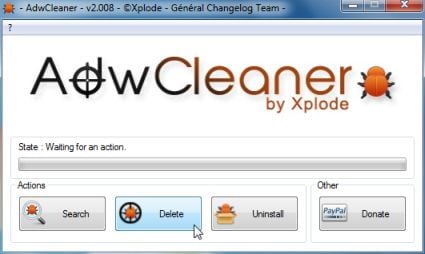
STEP 3: Remove LoadTubes registry keys with Adwcleaner
- You can download AdwCleaner from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting this utility,close all open programs and internet browsers.
- Double click on adwcleaner.exe to run the tool.
- Click on Delete,then confirm each time with Ok.
- Your computer will be rebooted automatically. A text file will open after the restart.
- NEXT,double click on adwcleaner.exe to run the tool.
- Click on Uninstall,then confirm with yes to remove this utility from your computer.
STEP 4: Scan your computer for malware
Run a computer scan with Malwarebytes Anti-Malware
- You can download Malwarebytes Anti-Malware Free from the below link,then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
DO NOT make any changes to default settings and when the program has finished installing, make sure you leave both the Update Malwarebytes’ Anti-Malware and Launch Malwarebytes’ Anti-Malware checked,then click on the Finish button.
- On the Scanner tab,select Perform quick scan and then click on the Scan button to start scanning your computer.
- Malwarebytes’ Anti-Malware will now start scanning your computer as shown below.
- When the Malwarebytes scan will be completed,click on Show Result.
- You will now be presented with a screen showing you the malware infections that Malwarebytes’ Anti-Malware has detected.Please note that the infections found may be different than what is shown in the image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
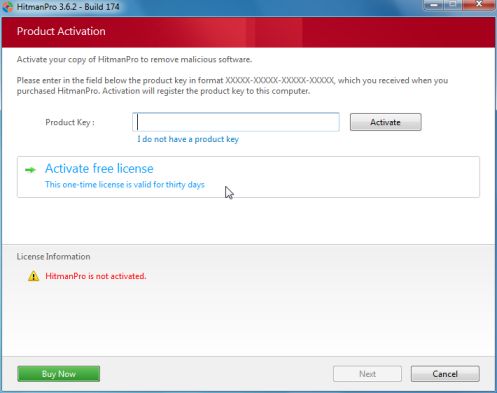
Run a computer scan with HitmanPro
- You can download HitmanPro from the below link, then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.
- HitmanPro will start scanning your computer for malware, as seen in the image below.
- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove these malicious files.
- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
![LoadTubes adware [Image: PUP.LoadTubes]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/loadtubes-virus.jpg)
![Click on Uninstall a program [Image: Uninstall a program]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/uninstall-a-program-windows.jpg)
![Uninstall LoadTubes program [Image: Uninstall PUP.LoadTubes program]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/loadtubes-uninstall.jpg)
![Select Manage Add-ons in Internet Explorer [Image: Manage Add-ons in Internet Explorer]](http://malwaretips.com/blogs/wp-content/uploads/2013/03/Internet-Explorer-Manage-Add-ons.jpg)
![LoadTubes Internet Explorer plugin [Image: LoadTubes Internet Explorer plugin]](http://malwaretips.com/blogs/wp-content/uploads/2013/05/loadtubes-Interent-Explorer-extension.jpg)
![Malwarebytes Anti-Malware final installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
![Malwarebytes Anti-Malware scanning for LoadTubes virus [Image: Malwarebytes Anti-Malware scanning for malware]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of malware [Image:Malwarebytes removing malware]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)