Exploit:Win32/Pdfjsc.AFU is a malicious PDF file that exploits a vulnerability in Adobe Acrobat and Adobe Reader.
Your computer has been infected with Exploit:JS/Cooexp.A, after you have visited a malicious or compromised webpage containing a malicious script, which exploited known vulnerabilities in Adobe Acrobat, and Adobe Reader.The following versions of Adobe Acrobat and Adobe Reader are vulnerable to this exploit:
Adobe Acrobat and Adobe Reader earlier than 8.2.1
Adobe Acrobat and Adobe Reader earlier than 9.3.1
The PDF file contains a malicious JavaScript that exploits a vulnerability, discussed in CVE-2010-0188.If Exploit:Win32/Pdfjsc.AFU successfully exploits a vulnerable computer, it attempts to download and install arbitrary files which may be detected as malware.
This malicious program is also known as:
EXP/Pidief.dqz.1.B (Avira)
Exploit.PDF (Ikarus)
Exploit.PDF.3178 (Dr.Web)
JS/ShellCode.A (Command)
PDF:Exploit.PDF-JS.SU (BitDefender)
Troj/PDFJs-ACY (Sophos)
TROJ_PIDIEF.ENR (Trend Micro)
If you received a pop-up warning for Exploit:Win32/Pdfjsc.AFU while you were surfing a website, chances are that the threat was blocked and there’s nothing to remove, however if you suspect that a malicious file has been downloaded to your computer, we strongly recommend taht you perform the following removal guide.
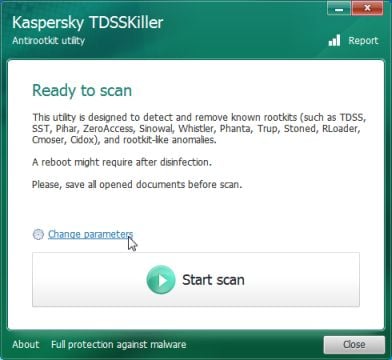
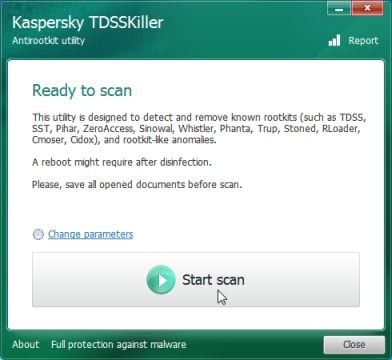
STEP 1: Remove Exploit:Win32/Pdfjsc.AFU infection with Kaspersky TDSSKiller
As part of its self defense mechanism, Exploit:Win32/Pdfjsc.AFU will install a rootkit on the infected computer.In this first step, we will run a system scan with Kaspersky TDSSKiller to remove this rookit.
- Please download the latest official version of Kaspersky TDSSKiller.
KASPERSKY TDSSKILLER DOWNLOAD LINK(This link will automatically download Kaspersky TDSSKiller on your computer.) - Before you can run Kaspersky TDSSKiller, you first need to rename it so that
you can get it to run. To do this, right-click on the TDSSKiller.exe icon and select Rename.
Edit the name of the file from TDSSKiller.exe to iexplore.exe, and then double-click on it to launch. - Kaspersky TDSSKiller will now start and display the welcome screen and we will need to click on Change Parameters.
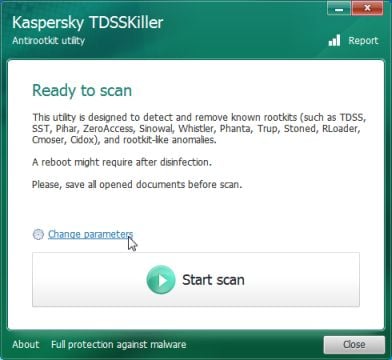
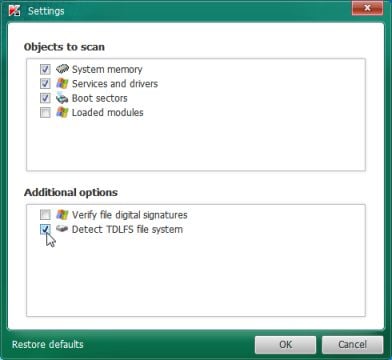
- In the new open window,we will need to enable Detect TDLFS file system, then click on OK.
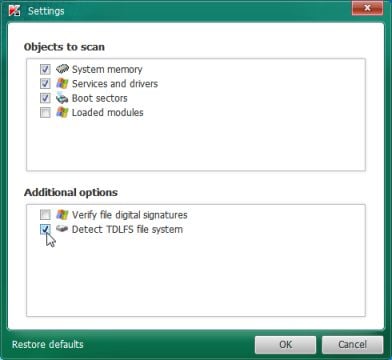
- Next,we will need to start a scan with Kaspersky, so you’ll need to press the Start Scan button.
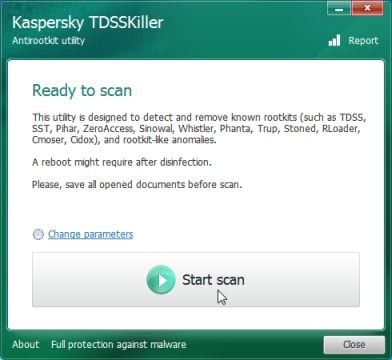
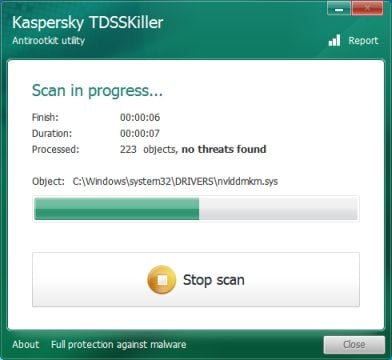
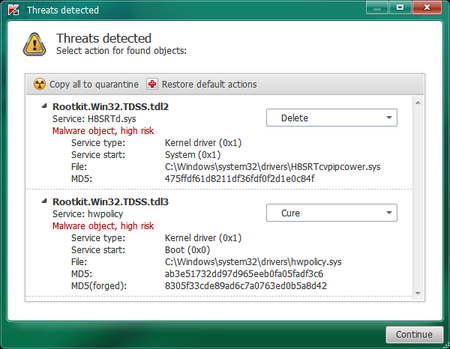
- Kaspersky TDSSKiller will now scan your computer for Exploit:Win32/Pdfjsc.AFU infection.
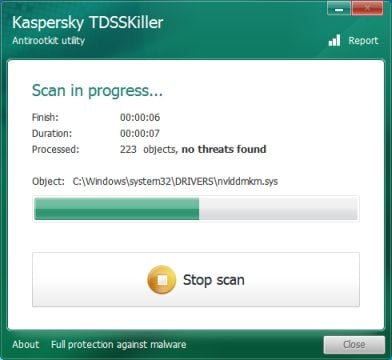
- When the scan has finished it will display a result screen stating whether or not the infection was found on your computer. If it was found it will display a screen similar to the one below.
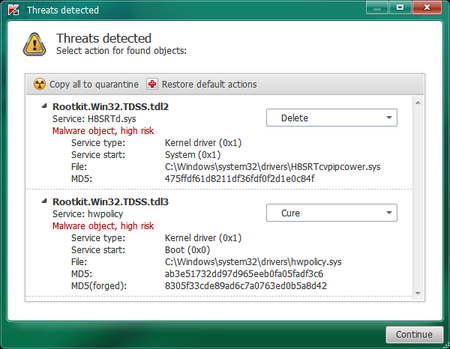
- To remove the infection simply click on the Continue button and TDSSKiller will attempt to clean the infection.A reboot will be require to completely remove any infection from your system.
STEP 2: Remove Exploit:Win32/Pdfjsc.AFU malicious files with Malwarebytes Anti-Malware
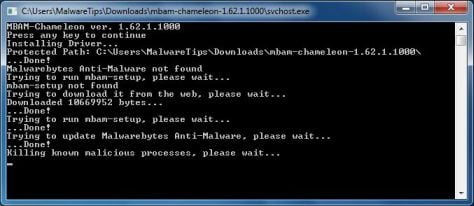
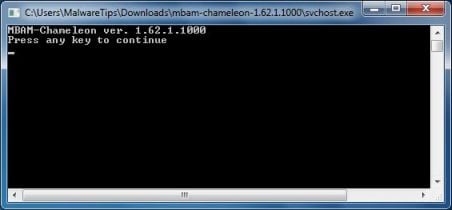
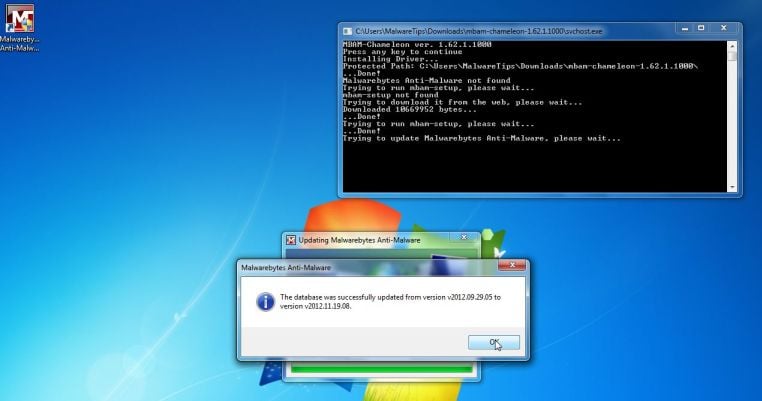
Malwarebytes Chameleon technologies will allow us to install and run a Malwarebytes Anti-Malware scan without being blocked by Trojan:Win32/QHosts and Trojan:W32/Qhost.
- Download Malwarebytes Chameleon from the below link and extract it to a folder in a convenient location.
MALWAREBYTES CHAMELEON DOWNLOAD LINK (This link will open a new web page from where you can download Malwarebytes Chameleon) - Make certain that your infected computer is connected to the internet and then open the Malwarebytes Chameleon folder and double-click on svchost.exe.

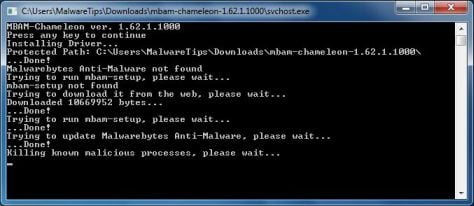
IF Malwarebytes Chameleon will not open, double-click on the other renamed files until you find one will work, which will be indicated by a black DOS/command prompt window. - Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
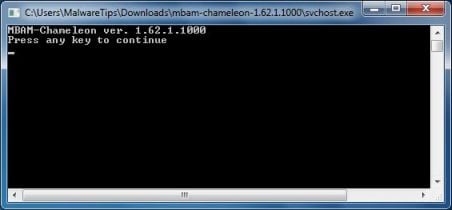
- Once it has done this, it will update Malwarebytes Anti-Malware, and you’ll need to click OK when it says that the database was updated successfully.
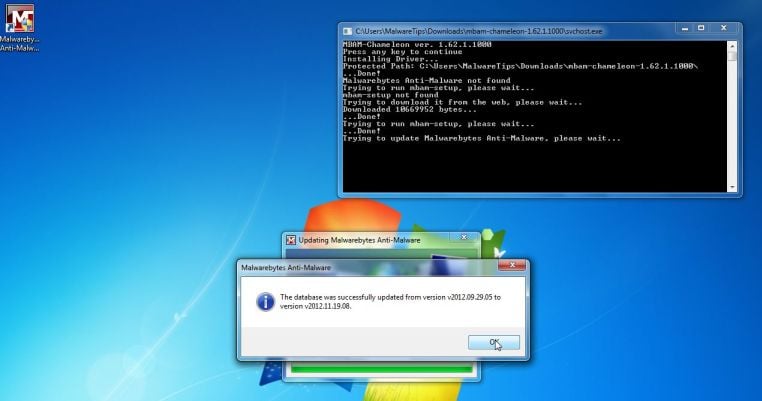
- Malwarebytes Anti-Malware will now attempt to kill all the malicious process associated with Trojan:Win32/QHosts and Trojan:W32/Qhost.Please be aware that this process can take up to 10 minutes, so please be patient.
- Next, Malwarebytes Anti-Malware will automatically open and perform a Quick scan for Exploit:Win32/Pdfjsc.AFU malicious files as shown below.
![Malwarebytes Anti-Malware scanning for Trojan:Win32/QHosts and Trojan:W32/Qhost [Image: Malwarebytes Anti-Malware scanning for Trojan:Win32/QHosts and Trojan:W32/Qhost]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
- Upon completion of the scan, click on Show Result
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
- You will now be presented with a screen showing you the malware infections that Malwarebytes Anti-Malware has detected.
Make sure that everything is Checked (ticked),then click on the Remove Selected button.
![Click on Remove Selected to get rid of Trojan:Win32/QHosts and Trojan:W32/Qhost [Image:Malwarebytes removing virus]](//malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
- After your computer restarts, open Malwarebytes Anti-Malware and perform a Full System scan to verify that there are no remaining threats
STEP 3 : Remove the malicious registry keys added by the Trojan:Win32/QHosts and Trojan:W32/Qhost
Trojan:Win32/QHosts and Trojan:W32/Qhost has added some malicious registry keys to your Windows installation,to remove them we will need to perform a scan with RogueKiller.
- You can download RogueKiller from the below link.
ROGUEKILLER DOWNLOAD LINK (This link will automatically download RogueKiller on your computer) - Double click on RogueKiller.exe to start this utility and then wait for the Prescan to complete.This should take only a few seconds and then you can click the Start button to perform a system scan.
![Click on the Start button to perform a system scan [Image: RogueKiller while scanning]](//malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-1.png)
- After the scan has completed, press the Delete button to remove any malicious registry keys.
![Press Delete to remove the malicious registry keys [Image: RogueKiller removing Trojan:Win32/QHosts and Trojan:W32/Qhost]](//malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-2.png)
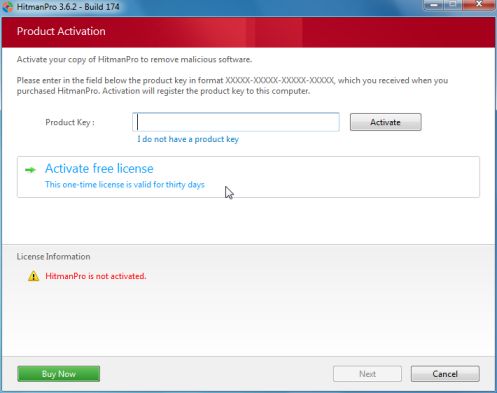
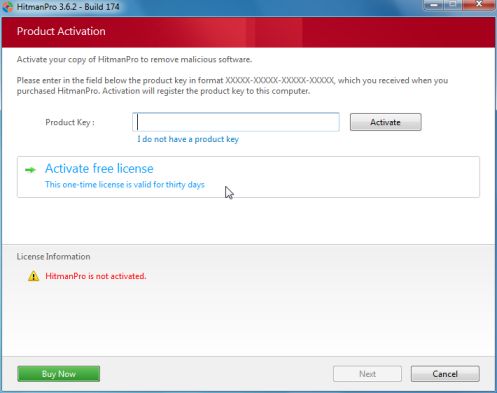
STEP 4: Remove Exploit:Win32/Pdfjsc.AFU rootkit with HitmanPro
- you can download HitmanPro from the below link,then double click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro)
IF you are experiencing problems while trying to start HitmanPro, you can use the Force Breach mode.To start HitmanPro in Force Breach mode, hold down the left CTRL-key when you start HitmanPro and all non-essential processes are terminated, including the malware process. (How to start HitmanPro in Force Breach mode – Video) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.


- HitmanPro will start scanning your computer for Exploit:Win32/Pdfjsc.AFU malicious files as seen in the image below.

- Once the scan is complete,you’ll see a screen which will display all the infected files that this utility has detected, and you’ll need to click on Next to remove this malicious files.

- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
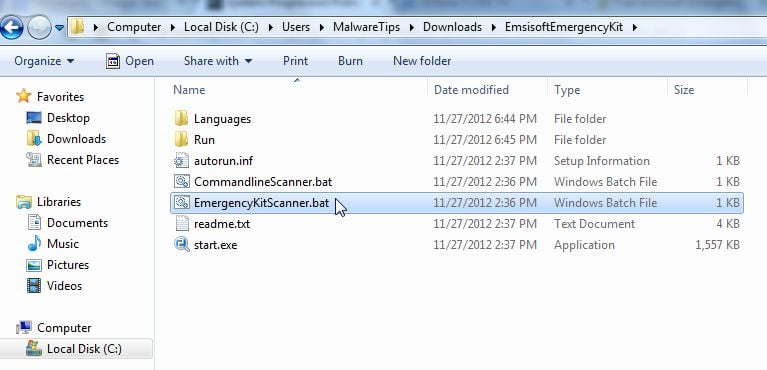
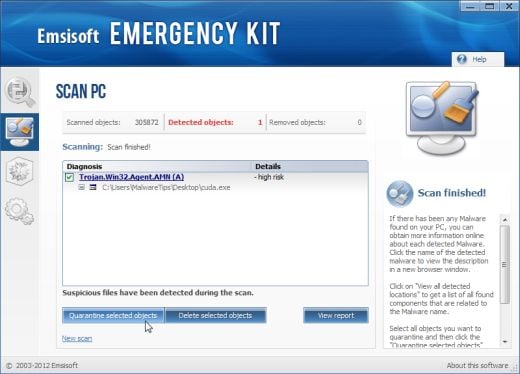
STEP 5: Double check for any left over infections with Emsisoft Emergency Kit
- You can download Emsisoft Emergency Kit from the below link,then extract it to a folder in a convenient location.
EMSISOFT EMERGENCY KIT DOWNLOAD LINK ((This link will open a new web page from where you can download Emsisoft Emergency Kit) - Open the Emsisoft Emergency Kit folder and double click EmergencyKitScanner.bat, then allow this program to update itself.
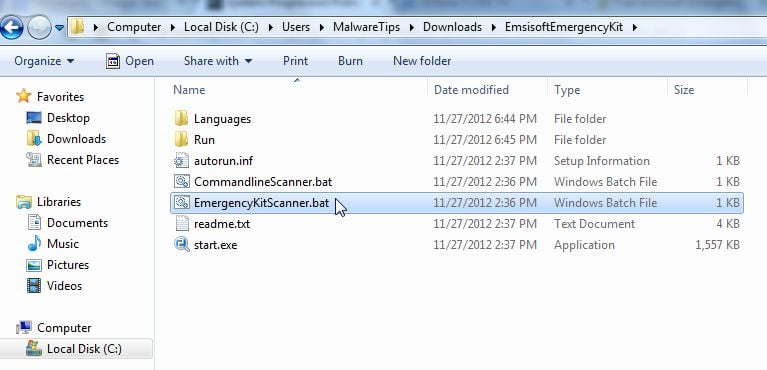
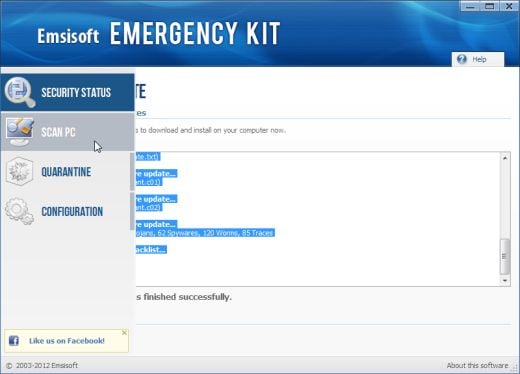
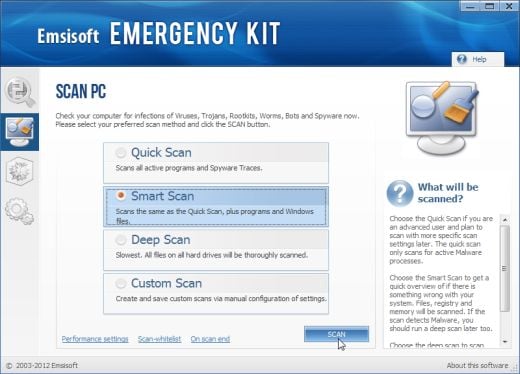
- After the Emsisoft Emergency Kit has update has completed,click on the Menu tab,then select Scan PC.
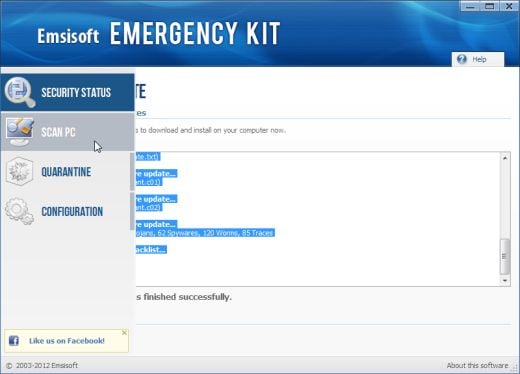
- Select Smart scan and click on the SCAN button to search for Exploit:Win32/Pdfjsc.AFU malicious files.
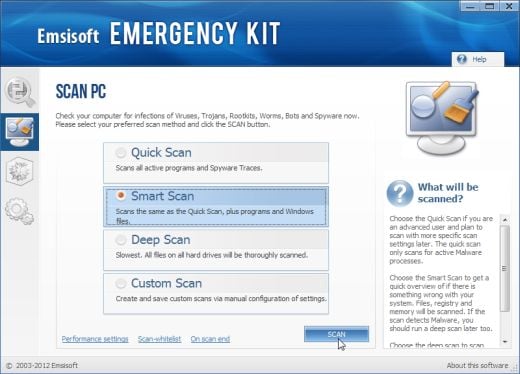
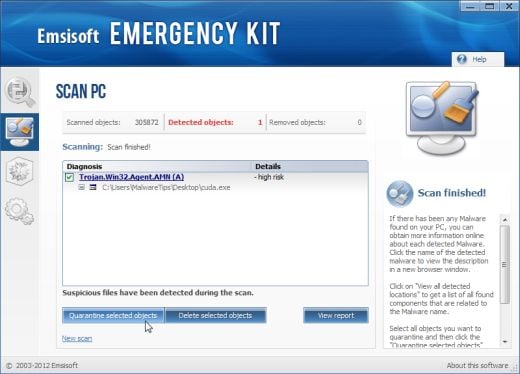
- When the scan will be completed,you will be presented with a screen reporting which malicious files has Emsisoft detected on your computer, and you’ll need to click on Quarantine selected objects to remove them.
Next,we will remove the tools that we’ve used in our malware removal process.
Kaspersky TDSSKiller and RogueKiller can be removed by deleting the utilities.
We strongly recommend that you keep Malwarebytes Anti-Malware and HitmanPro installed on your machine and run regular scans with this tools.If you however,wish to remove them,you can go into the Add or Remove programs and uninstall this two on-demand scanners.
If you are still experiencing problems while trying to remove Exploit:Win32/Pdfjsc.AFU from your machine, please start a new thread in our Malware Removal Assistance forum.


![Malwarebytes Anti-Malware scanning for Trojan:Win32/QHosts and Trojan:W32/Qhost [Image: Malwarebytes Anti-Malware scanning for Trojan:Win32/QHosts and Trojan:W32/Qhost]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan.jpg)
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
![Click on Remove Selected to get rid of Trojan:Win32/QHosts and Trojan:W32/Qhost [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
![Click on the Start button to perform a system scan [Image: RogueKiller while scanning]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-1.png)
![Press Delete to remove the malicious registry keys [Image: RogueKiller removing Trojan:Win32/QHosts and Trojan:W32/Qhost]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-2.png)